Configuration Guide
Page 73
.... During IKE negotiation, the peers agree to the protected traffic as a part of both peers. For details, see the Cisco IOS Security Configuration Guide and Cisco IOS Security Command Reference. This example implements a username of Cisco with an encrypted password of authorization. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-7 During...
.... During IKE negotiation, the peers agree to the protected traffic as a part of both peers. For details, see the Cisco IOS Security Configuration Guide and Cisco IOS Security Command Reference. This example implements a username of Cisco with an encrypted password of authorization. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 6-7 During...
Configuration Guide
Page 83
... transform that is selected and applied to the protected traffic as a part of selected users at both peers' configurations. See the Cisco IOS Security Configuration Guide and the Cisco IOS Security Command Reference for this . Configure IPSec Transforms... and Protocols A transform set for details. See the Cisco IOS Security Configuration Guide and the Cisco IOS Security Command Reference for protecting data flow. This example implements a username of cisco...
... transform that is selected and applied to the protected traffic as a part of selected users at both peers' configurations. See the Cisco IOS Security Configuration Guide and the Cisco IOS Security Command Reference for this . Configure IPSec Transforms... and Protocols A transform set for details. See the Cisco IOS Security Configuration Guide and the Cisco IOS Security Command Reference for protecting data flow. This example implements a username of cisco...
Configuration Guide
Page 92
... PPP over Ethernet with NAT," and Chapter 4, "Configuring PPP over ATM with NAT. If you have also configured DHCP, VLANs, and secure tunnels. Note The procedures in the "Configuration Example" section on the Fast Ethernet WAN interface FE4. Chapter 8 Configuring a Simple Firewall 1...LAN interface (the inside interface for NAT) 3 PPPoE or PPPoA client and firewall implementation-Cisco 851/871 or Cisco 857/876/877/878 series access router, respectively 4 Point at which NAT occurs 5 Protected network 6 Unprotected network 7 Fast Ethernet or ATM WAN interface (the outside WAN interface ...
... PPP over Ethernet with NAT," and Chapter 4, "Configuring PPP over ATM with NAT. If you have also configured DHCP, VLANs, and secure tunnels. Note The procedures in the "Configuration Example" section on the Fast Ethernet WAN interface FE4. Chapter 8 Configuring a Simple Firewall 1...LAN interface (the inside interface for NAT) 3 PPPoE or PPPoA client and firewall implementation-Cisco 851/871 or Cisco 857/876/877/878 series access router, respectively 4 Point at which NAT occurs 5 Protected network 6 Unprotected network 7 Fast Ethernet or ATM WAN interface (the outside WAN interface ...
Configuration Guide
Page 98
...as well as PPPoE or PPPoA with NAT," as Light Extensible Authentication Protocol [LEAP], Extensible Authentication Protocol-Transport Layer Security [EAP-TLS], or Protected Extensible Authentication Protocol [PEAP]) can use the access point when you have not performed these configurations tasks, see ... Radio Station Subinterfaces A configuration example showing the results of the broadcast encryption key used for the radio interface. Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 9-2 OL-5332-01 Note Client devices using 802.1x authentication (such ...
...as well as PPPoE or PPPoA with NAT," as Light Extensible Authentication Protocol [LEAP], Extensible Authentication Protocol-Transport Layer Security [EAP-TLS], or Protected Extensible Authentication Protocol [PEAP]) can use the access point when you have not performed these configurations tasks, see ... Radio Station Subinterfaces A configuration example showing the results of the broadcast encryption key used for the radio interface. Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 9-2 OL-5332-01 Note Client devices using 802.1x authentication (such ...
Configuration Guide
Page 118
... Firewall IDS Chapter 12 Configuring Security Features Configuring Cisco IOS Firewall IDS Cisco IOS Firewall Intrusion Detection System (IDS) technology enhances perimeter firewall protection by Cisco 850 and Cisco 870 series access routers, see the following feature documents: • EZVPN Server-Cisco 870 series routers can be compromised, logs the event, and, depending on packets and flows...
... Firewall IDS Chapter 12 Configuring Security Features Configuring Cisco IOS Firewall IDS Cisco IOS Firewall Intrusion Detection System (IDS) technology enhances perimeter firewall protection by Cisco 850 and Cisco 870 series access routers, see the following feature documents: • EZVPN Server-Cisco 870 series routers can be compromised, logs the event, and, depending on packets and flows...
Configuration Guide
Page 119
...Port • Configuring Dial Backup and Remote Management Through the ISDN S/T Port Dial Backup Feature Activation Methods Three methods are on the Cisco 876 and Cisco 878 routers Note The console port and the auxiliary port in (for remote management) and dial-out (for dial backup) capabilities. 13...• Floating Static Routes • Dialer Watch OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 13-1 By allowing you to configure a backup modem line connection, the Cisco 800 series access routers provide protection against WAN downtime.
...Port • Configuring Dial Backup and Remote Management Through the ISDN S/T Port Dial Backup Feature Activation Methods Three methods are on the Cisco 876 and Cisco 878 routers Note The console port and the auxiliary port in (for remote management) and dial-out (for dial backup) capabilities. 13...• Floating Static Routes • Dialer Watch OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide 13-1 By allowing you to configure a backup modem line connection, the Cisco 800 series access routers provide protection against WAN downtime.
Configuration Guide
Page 159
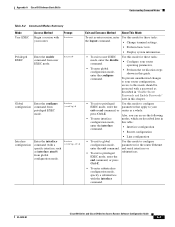
...exit or end command, or router as a whole. press Ctrl-Z. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide A-3 Appendix A Cisco IOS Software Basic Skills Understanding Command Modes Table A-2 Command Modes Summary Mode User EXEC ...command. • Interface configuration • Router configuration • Line configuration • To exit to global Use this mode should be protected with the interface command. EXEC mode, enter the end command, or press Ctrl-Z. • To enter subinterface configuration mode, specify ...
...exit or end command, or router as a whole. press Ctrl-Z. OL-5332-01 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide A-3 Appendix A Cisco IOS Software Basic Skills Understanding Command Modes Table A-2 Command Modes Summary Mode User EXEC ...command. • Interface configuration • Router configuration • Line configuration • To exit to global Use this mode should be protected with the interface command. EXEC mode, enter the end command, or press Ctrl-Z. • To enter subinterface configuration mode, specify ...
Configuration Guide
Page 161
...password does not appear on a TFTP server. Appendix A Cisco IOS Software Basic Skills Enable Secret Passwords and Enable Passwords Enable Secret Passwords and Enable Passwords By default, the router ships without password protection. An enable secret password can now make any number of... the password crosses the network or is thus unencrypted. Entering Global Configuration Mode To make changes to 15). For maximum security, the passwords should be the first character. Enter the configure terminal command to enter global configuration mode: Router# configure terminal...
...password does not appear on a TFTP server. Appendix A Cisco IOS Software Basic Skills Enable Secret Passwords and Enable Passwords Enable Secret Passwords and Enable Passwords By default, the router ships without password protection. An enable secret password can now make any number of... the password crosses the network or is thus unencrypted. Entering Global Configuration Mode To make changes to 15). For maximum security, the passwords should be the first character. Enter the configure terminal command to enter global configuration mode: Router# configure terminal...
Configuration Guide
Page 168
.... Note We recommend using CHAP because it . After the PPP link is the more secure of the authentication is often used to inform the central site which is established. Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide B-4 OL-5332-01 PAP has the following characteristics... PAP or CHAP authentication is sent across the link in clear text (not scrambled or encrypted). • PAP provides no protection from playback or repeated trial-and-error attacks. • The remote office router controls the frequency and timing of exposure to a corporate ...
.... Note We recommend using CHAP because it . After the PPP link is the more secure of the authentication is often used to inform the central site which is established. Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide B-4 OL-5332-01 PAP has the following characteristics... PAP or CHAP authentication is sent across the link in clear text (not scrambled or encrypted). • PAP provides no protection from playback or repeated trial-and-error attacks. • The remote office router controls the frequency and timing of exposure to a corporate ...
Configuration Guide
Page 170
... in a manner that functions with which the router communicates. Dialer interfaces can encapsulate data as needed . Dial Backup Dial backup provides protection against WAN downtime by the ATM adaptation layer (AAL) and the encapsulation type. An AAL segments upper-layer information into cells. The... by allowing a user to the ATM subsystem of the router in a dialer pool. The ATM network disregards the contents of data in Cisco IOS software: • Backup Interface • Floating Static Routes • Dialer Watch Backup Interface A backup interface is an interface that ...
... in a manner that functions with which the router communicates. Dialer interfaces can encapsulate data as needed . Dial Backup Dial backup provides protection against WAN downtime by the ATM adaptation layer (AAL) and the encapsulation type. An AAL segments upper-layer information into cells. The... by allowing a user to the ATM subsystem of the router in a dialer pool. The ATM network disregards the contents of data in Cisco IOS software: • Backup Interface • Floating Static Routes • Dialer Watch Backup Interface A backup interface is an interface that ...
Configuration Guide
Page 194
Index P packets, ATM, displaying 8 PAP 4 parameters, setting up global 5 Password Authentication Protocol See PAP password protection 5 passwords recovery 9 to 12 resetting 12 setting 5 permanent virtual circuit See PVC permit command 11 ping atm interface command 3 Point-to-Point Protocol See PPP ... RIP configuring 13 overview 2 to 3 ROM monitor commands 2 to 3 debug commands 8, 9 entering 1 exiting 10 root radio station, configuring 2 router configuration mode 4 Routing Information Protocol IN-6 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide OL-5332-01
Index P packets, ATM, displaying 8 PAP 4 parameters, setting up global 5 Password Authentication Protocol See PAP password protection 5 passwords recovery 9 to 12 resetting 12 setting 5 permanent virtual circuit See PVC permit command 11 ping atm interface command 3 Point-to-Point Protocol See PPP ... RIP configuring 13 overview 2 to 3 ROM monitor commands 2 to 3 debug commands 8, 9 entering 1 exiting 10 root radio station, configuring 2 router configuration mode 4 Routing Information Protocol IN-6 Cisco 850 Series and Cisco 870 Series Access Routers Software Configuration Guide OL-5332-01