User Manual
Page 2
... Settings 36 Viewing the DHCP Client List Page 38 Configuring the Wireless Network Settings 38 Setting WPA Security 44 Setting WEP Encryption 46 Using the Access Point Mode 48 Setting MAC Address Control 49 Configuring the Firewall 51 Using Dynamic DNS 54 Utilities 56 Restarting the Modem Router 57 Updating the Firmware...
... Settings 36 Viewing the DHCP Client List Page 38 Configuring the Wireless Network Settings 38 Setting WPA Security 44 Setting WEP Encryption 46 Using the Access Point Mode 48 Setting MAC Address Control 49 Configuring the Firewall 51 Using Dynamic DNS 54 Utilities 56 Restarting the Modem Router 57 Updating the Firmware...
User Manual
Page 7
... user name and password, and are used to connect remotely to an office network • The "Bring Your Own Access" program from neighboring cordless phones or other wireless devices. • For Belkin wireless networking products, use AOL through broadband provided by another cable or DSL service • Most online banking websites •...user guide for portable computers. To change your account Secure connections can be sure you need to cover an even wider area, we suggest the Belkin Wireless Range Extender/Access Point. 5. Introduction • Experiment with more information.
... user name and password, and are used to connect remotely to an office network • The "Bring Your Own Access" program from neighboring cordless phones or other wireless devices. • For Belkin wireless networking products, use AOL through broadband provided by another cable or DSL service • Most online banking websites •...user guide for portable computers. To change your account Secure connections can be sure you need to cover an even wider area, we suggest the Belkin Wireless Range Extender/Access Point. 5. Introduction • Experiment with more information.
User Manual
Page 11
...addresses into a list using the Web-Based Advanced User Interface and you can control access to your network. It employs MIMO (Multiple Input Multiple Output) smart-antenna technology that are allowed access to your network. MAC Address Filtering For added security, you can set up ... identifiers) that achieves data rates of up to 270Mbps.* Actual throughput is the physical data rate. Product Overview Integrated N1 Wireless Access Point N1 MIMO is an exciting new wireless technology based on your networking environment. *NOTE: The standard transmission rate-270Mbps-is typically ...
...addresses into a list using the Web-Based Advanced User Interface and you can control access to your network. It employs MIMO (Multiple Input Multiple Output) smart-antenna technology that are allowed access to your network. MAC Address Filtering For added security, you can set up ... identifiers) that achieves data rates of up to 270Mbps.* Actual throughput is the physical data rate. Product Overview Integrated N1 Wireless Access Point N1 MIMO is an exciting new wireless technology based on your networking environment. *NOTE: The standard transmission rate-270Mbps-is typically ...
User Manual
Page 31
...(null encapsulation) allows only one virtual circuit (more overhead). 6. Alternate Setup Method Setting your ISP Connection Type to PPPoE or PPPoA PPPoE (Point-to-Point Protocol over Ethernet) is mostly implemented in the UK. Enter your Virtual Path Identifier (VPI) and Virtual Circuit Identifier (VCI) parameter here.... (PPP over one protocol running over ATM) is similar to PPPoE, but is the standard method of your ISP) to specify how to access the network of connecting networked devices. User Name - MTU - It requires a user name and password to handle multiple protocols at the ATM...
...(null encapsulation) allows only one virtual circuit (more overhead). 6. Alternate Setup Method Setting your ISP Connection Type to PPPoE or PPPoA PPPoE (Point-to-Point Protocol over Ethernet) is mostly implemented in the UK. Enter your Virtual Path Identifier (VPI) and Virtual Circuit Identifier (VCI) parameter here.... (PPP over one protocol running over ATM) is similar to PPPoE, but is the standard method of your ISP) to specify how to access the network of connecting networked devices. User Name - MTU - It requires a user name and password to handle multiple protocols at the ATM...
User Manual
Page 40
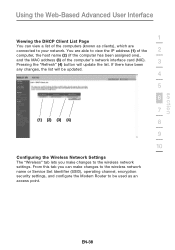
... IP address (1) of the 2 computer, the host name (2) (if the computer has been assigned one), and the MAC address (3) of the computers (known as an access point. If there have been any changes, the list will be updated. 4 5 6 7 (1) (2) (3) (4) 8 9 10 Configuring the Wireless Network Settings The "Wireless" tab lets you can view a list...
... IP address (1) of the 2 computer, the host name (2) (if the computer has been assigned one), and the MAC address (3) of the computers (known as an access point. If there have been any changes, the list will be updated. 4 5 6 7 (1) (2) (3) (4) 8 9 10 Configuring the Wireless Network Settings The "Wireless" tab lets you can view a list...
User Manual
Page 42
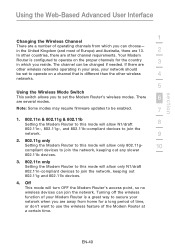
... networks operating in your area, your network when you are away from which you can choose- Off This mode will turn OFF the Modem Router's access point, so no wireless devices can be enabled. 7 1. 802.11n & 802.11g & 802.11b Setting the Modem Router to this mode will allow N1/draft 8 802...
... networks operating in your area, your network when you are away from which you can choose- Off This mode will turn OFF the Modem Router's access point, so no wireless devices can be enabled. 7 1. 802.11n & 802.11g & 802.11b Setting the Modem Router to this mode will allow N1/draft 8 802...
User Manual
Page 43
There are scanning for the presence of your specific SSID; When a legacy 802.11g access point is immediate. Doing so will limit N1, draft 802.11n-compliant devices' bandwidth by advanced users only. The change . This mode is compatible with N1, ...
There are scanning for the presence of your specific SSID; When a legacy 802.11g access point is immediate. Doing so will limit N1, draft 802.11n-compliant devices' bandwidth by advanced users only. The change . This mode is compatible with N1, ...
User Manual
Page 50
... Changes". 3. Using this option, you will be configured to work as a wireless 2 network access point. Connect a cable from the WAN port on the Modem Router to your browser's navigation bar. To access the Modem Router advanced user interface again, type the IP address 9 you specified into your 7... existing network. 8 The Modem Router is now acting as an access point. section Using the Web-Based Advanced User Interface 1 Using the Access Point Mode Note: This advanced feature should be configured with an IP address that is in the "Use as...
... Changes". 3. Using this option, you will be configured to work as a wireless 2 network access point. Connect a cable from the WAN port on the Modem Router to your browser's navigation bar. To access the Modem Router advanced user interface again, type the IP address 9 you specified into your 7... existing network. 8 The Modem Router is now acting as an access point. section Using the Web-Based Advanced User Interface 1 Using the Access Point Mode Note: This advanced feature should be configured with an IP address that is in the "Use as...
User Manual
Page 56
... to five host names, free to the Internet community. When your IP address changes, your friends and associates can ensure that your host name always points to your IP address, no matter how often your ISP changes it. If you are using multiple static WAN IP addresses, it easy to... free for a home website, file server, or to make it is possible to select which WAN IP address the DMZ host will be more easily accessed from various locations on a temporary basis. 3 The computer in the DMZ is causing problems with an application such as a game or video conferencing application. This...
... to five host names, free to the Internet community. When your IP address changes, your friends and associates can ensure that your host name always points to your IP address, no matter how often your ISP changes it. If you are using multiple static WAN IP addresses, it easy to... free for a home website, file server, or to make it is possible to select which WAN IP address the DMZ host will be more easily accessed from various locations on a temporary basis. 3 The computer in the DMZ is causing problems with an application such as a game or video conferencing application. This...