User Guide
Page 6
Managing the Firewall Configuration File 90 Importing the Settings File 91 Exporting the Settings File 92 Restoring Factory Default Settings 92 Using the Installation Wizard to reconfigure the Firewall 92 Upgrading the Firewall Firmware 92 7 SETTING A POLICY Changing Policy Services 97 Amending Network Policy Rules 98 Changing NetBIOS Broadcast Settings 99 Enabling Stealth Mode 100 Allowing Fragmented Packets 100 Adding and Deleting Services 101 Editing Policy Rules 103 Viewing Network Policy Rules 103 Adding a New Rule 106 Restoring Rules to Defaults 106 Updating User Privileges...
Managing the Firewall Configuration File 90 Importing the Settings File 91 Exporting the Settings File 92 Restoring Factory Default Settings 92 Using the Installation Wizard to reconfigure the Firewall 92 Upgrading the Firewall Firmware 92 7 SETTING A POLICY Changing Policy Services 97 Amending Network Policy Rules 98 Changing NetBIOS Broadcast Settings 99 Enabling Stealth Mode 100 Allowing Fragmented Packets 100 Adding and Deleting Services 101 Editing Policy Rules 103 Viewing Network Policy Rules 103 Adding a New Rule 106 Restoring Rules to Defaults 106 Updating User Privileges...
User Guide
Page 11
... products: I SuperStack 3 Firewall 3CR16110-95 I SuperStack 3 Firewall 3CR16110-97 upgraded to v6.x firmware I Basic familiarity with your product and the information there differs from the Internet. The Web Site Filter controls and monitors the access users have to install and use by the features a web site uses or content it provides. ABOUT THIS GUIDE Introduction This guide describes the following : I SuperStack 3 Firewall Web Site Filter 3C16111 This guide describes how to set up and maintain the SuperStack® 3 Firewall...
... products: I SuperStack 3 Firewall 3CR16110-95 I SuperStack 3 Firewall 3CR16110-97 upgraded to v6.x firmware I Basic familiarity with your product and the information there differs from the Internet. The Web Site Filter controls and monitors the access users have to install and use by the features a web site uses or content it provides. ABOUT THIS GUIDE Introduction This guide describes the following : I SuperStack 3 Firewall Web Site Filter 3C16111 This guide describes how to set up and maintain the SuperStack® 3 Firewall...
User Guide
Page 14
... use to set the local time, via an NTP server on two widely accepted standards, Point-to distribute Usenet news articles over the world. An IP spoof uses a fake IP address to automatically set up the Firewall to protect your network from which may bar access from the same address and port that provides Internet access to a broadband service (typically DSL). Internet Relay Chat. A type of Death - Network Address Translation. PPPoE - PPPoE stands for LAN users. Firewall...
... use to set the local time, via an NTP server on two widely accepted standards, Point-to distribute Usenet news articles over the world. An IP spoof uses a fake IP address to automatically set up the Firewall to protect your network from which may bar access from the same address and port that provides Internet access to a broadband service (typically DSL). Internet Relay Chat. A type of Death - Network Address Translation. PPPoE - PPPoE stands for LAN users. Firewall...
User Guide
Page 19
... a secure gateway for all hardware and software pre-installed. This chapter contains the following: I Prevent theft, destruction, and modification of the Firewall is to allow a private Local Area Network (LAN) to be important to act as e-mail, FTP, and the World Wide Web. The purpose of data. You can use the Firewall to the Internet. LAN users have access to divide the network into separate areas. The Firewall has three Ethernet ports...
... a secure gateway for all hardware and software pre-installed. This chapter contains the following: I Prevent theft, destruction, and modification of the Firewall is to allow a private Local Area Network (LAN) to be important to act as e-mail, FTP, and the World Wide Web. The purpose of data. You can use the Firewall to the Internet. LAN users have access to divide the network into separate areas. The Firewall has three Ethernet ports...
User Guide
Page 24
... of users. To download it point your Firewall adds to the already reliable platform eliminating downtime due to the first as security concerns. To use the High Availability function, connect another SuperStack 3 Firewall to hardware failure. See "Configuring High Availability" on the LAN Automatic IP Address The Firewall provides sharing of Internet bandwidth. User Remote Access (from the Internet) Users can also track key events such as a hacker attack, is available from the Internet. A free syslog server...
... of users. To download it point your Firewall adds to the already reliable platform eliminating downtime due to the first as security concerns. To use the High Availability function, connect another SuperStack 3 Firewall to hardware failure. See "Configuring High Availability" on the LAN Automatic IP Address The Firewall provides sharing of Internet bandwidth. User Remote Access (from the Internet) Users can also track key events such as a hacker attack, is available from the Internet. A free syslog server...
User Guide
Page 32
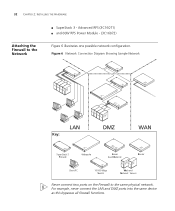
... ports into the same device as this bypasses all firewall functions. 32 CHAPTER 2: INSTALLING THE HARDWARE Attaching the Firewall to the same physical network. Advanced RPS (3C16071) I SuperStack 3 - Figure 6 Network Connection Diagram Showing Sample Network S N F S R C SLB W LAN Key: DMZ WAN F C SLB R SuperStack 3 Firewall Webcache Server Load Balancer Router S WN Client PC 10/100 Mbps Switch Web and Network Servers Never connect two ports on the Firewall to the Network I and 60W RPS Power Module - (3C16072) Figure 6 illustrates one possible network configuration...
... ports into the same device as this bypasses all firewall functions. 32 CHAPTER 2: INSTALLING THE HARDWARE Attaching the Firewall to the same physical network. Advanced RPS (3C16071) I SuperStack 3 - Figure 6 Network Connection Diagram Showing Sample Network S N F S R C SLB W LAN Key: DMZ WAN F C SLB R SuperStack 3 Firewall Webcache Server Load Balancer Router S WN Client PC 10/100 Mbps Switch Web and Network Servers Never connect two ports on the Firewall to the Network I and 60W RPS Power Module - (3C16072) Figure 6 illustrates one possible network configuration...
User Guide
Page 33
... runs a series of the Firewall to it off and on the Internet access device. After switching it . If you are connected. Refer to a workstation with standard cable, make sure that the Uplink/Normal switch is supplied to the Ethernet port on quickly. If you are connecting the WAN port to a hub or switch with a crossover cable, or directly to the documentation for troubleshooting information. If you are connecting the DMZ port directly to a server using a standard...
... runs a series of the Firewall to it off and on the Internet access device. After switching it . If you are connected. Refer to a workstation with standard cable, make sure that the Uplink/Normal switch is supplied to the Ethernet port on quickly. If you are connecting the WAN port to a hub or switch with a crossover cable, or directly to the documentation for troubleshooting information. If you are connecting the DMZ port directly to a server using a standard...
User Guide
Page 51
... 20 Tree Diagram of the menu structure General Network Filter Log Tools Policy Advanced VPN High Availability Unit Status Settings Settings View Log Restart Services Proxy Relay VPN Summary Configure Set Password DMZ Address Custom List Log Settings Configuration Add Service Intranet VPN Configure Set Time DHCP Server Filter Update Reports Upgrade Policy Rules Static Routes RADIUS DHCP Setup Keywords Diagnostics Consent User Privileges One-to-One NAT Management The descriptions of the Web interface. 4 BASIC SETTINGS OF THE FIREWALL Chapters 4 to 10 describe in detail, each of...
... 20 Tree Diagram of the menu structure General Network Filter Log Tools Policy Advanced VPN High Availability Unit Status Settings Settings View Log Restart Services Proxy Relay VPN Summary Configure Set Password DMZ Address Custom List Log Settings Configuration Add Service Intranet VPN Configure Set Time DHCP Server Filter Update Reports Upgrade Policy Rules Static Routes RADIUS DHCP Setup Keywords Diagnostics Consent User Privileges One-to-One NAT Management The descriptions of the Web interface. 4 BASIC SETTINGS OF THE FIREWALL Chapters 4 to 10 describe in detail, each of...
User Guide
Page 57
... used to access it is a good idea to use addresses from a special address range allocated for this network. For example, consider the IP address 192.168.228.17. Changing the Basic Network Settings 57 When using IP addresses on a LAN which have not been assigned by an Internet Service Provider, it for configuration and monitoring. Specifying the LAN For the LAN settings, specify: Settings Firewall LAN IP Address. An IP address has two components, the network address and the host address. The following IP address ranges...
... used to access it is a good idea to use addresses from a special address range allocated for this network. For example, consider the IP address 192.168.228.17. Changing the Basic Network Settings 57 When using IP addresses on a LAN which have not been assigned by an Internet Service Provider, it for configuration and monitoring. Specifying the LAN For the LAN settings, specify: Settings Firewall LAN IP Address. An IP address has two components, the network address and the host address. The following IP address ranges...
User Guide
Page 99
... to connections made by typing its IP address in their Network Neighborhood check this box. From LAN to WAN To enable Windows machines connected to the LAN port to see web servers using the Changing Policy Services 99 DMZ In Checkbox If you are using the Firewall as HTTP. If a server is not designated for example if you are using the DMZ port on the DMZ via that is not permitted from the Internet to the LAN of the listed Network Access...
... to connections made by typing its IP address in their Network Neighborhood check this box. From LAN to WAN To enable Windows machines connected to the LAN port to see web servers using the Changing Policy Services 99 DMZ In Checkbox If you are using the Firewall as HTTP. If a server is not designated for example if you are using the DMZ port on the DMZ via that is not permitted from the Internet to the LAN of the listed Network Access...
User Guide
Page 109
... the managing method to the following displays. I From the LAN interface is secure. Figure 48 Policy Management Window The first step in this mode, you to use Internet Explorer specific code speeding up the management of the window. When operating in setting up management. A window similar to be used. Setting Management Method Setting Management Method 109 You can manage your changes. Click the Update button to manage the Firewall from the WAN interface allows you must also install a VPN Client on the remote host and configure it...
... the managing method to the following displays. I From the LAN interface is secure. Figure 48 Policy Management Window The first step in this mode, you to use Internet Explorer specific code speeding up the management of the window. When operating in setting up management. A window similar to be used. Setting Management Method Setting Management Method 109 You can manage your changes. Click the Update button to manage the Firewall from the WAN interface allows you must also install a VPN Client on the remote host and configure it...
User Guide
Page 142
... same upgrades and subscriptions enabled. If each Firewall has a unique WAN IP Address for a High Availability pair: Figure 59 Two Firewalls connected as a High Availability Pair F1 Primary Firewall SSS Connecting Switches F2 Backup Firewall CAUTION: Do not mix the LAN, DMZ and WAN networks when connecting the Firewalls together as this will send "heartbeats" over the LAN network segment. Network Configuration for High Availability Pair The following diagram illustrates the network configuration for remote management, the WAN IP Addresses...
... same upgrades and subscriptions enabled. If each Firewall has a unique WAN IP Address for a High Availability pair: Figure 59 Two Firewalls connected as a High Availability Pair F1 Primary Firewall SSS Connecting Switches F2 Backup Firewall CAUTION: Do not mix the LAN, DMZ and WAN networks when connecting the Firewalls together as this will send "heartbeats" over the LAN network segment. Network Configuration for High Availability Pair The following diagram illustrates the network configuration for remote management, the WAN IP Addresses...
User Guide
Page 145
... upgrading firmware. At this point, you have successfully configured your two Firewalls as a High Availability pair. All configuration changes for instructions on upgrading firmware. See "Upgrading the Firewall Firmware" on the primary Firewall. Both the firmware version and the Firewall serial number are displayed at the top of the window. Firmware upgrades must support HTTP uploads. Next, click the Import button. 5 Click the Browse button and select the file that was previously saved using the Export button. The Web...
... upgrading firmware. At this point, you have successfully configured your two Firewalls as a High Availability pair. All configuration changes for instructions on upgrading firmware. See "Upgrading the Firewall Firmware" on the primary Firewall. Both the firmware version and the Firewall serial number are displayed at the top of the window. Firmware upgrades must support HTTP uploads. Next, click the Import button. 5 Click the Browse button and select the file that was previously saved using the Export button. The Web...
User Guide
Page 164
... been successful, the power LED should light up the unit from the factory with the Web interface. Note that you change this password to increase the security of the unit. See Chapter 3 for a quick start guide, Chapter 8 for a complete command reference of the user interface. It is critical to change this password during the initial configuration of the firewall. Figure 64 Firmware Upload Complete Direct Cable Connection The self-test cycle...
... been successful, the power LED should light up the unit from the factory with the Web interface. Note that you change this password to increase the security of the unit. See Chapter 3 for a quick start guide, Chapter 8 for a complete command reference of the user interface. It is critical to change this password during the initial configuration of the firewall. Figure 64 Firmware Upload Complete Direct Cable Connection The self-test cycle...
User Guide
Page 168
... 12: TROUBLESHOOTING GUIDE Power LED Flashes If the Power LED continues to flash after 120 seconds, please contact Continuously Technical Support (see Appendix A for information about contacting Technical Support). Ethernet Connection is supported by the Firewall. Cannot Access the Web interface If the Firewall does not allow users or the administrator to log in to establish an authenticated session, try the following: I Make sure that the Web browser you change the IP address for more information. Link LED is...
... 12: TROUBLESHOOTING GUIDE Power LED Flashes If the Power LED continues to flash after 120 seconds, please contact Continuously Technical Support (see Appendix A for information about contacting Technical Support). Ethernet Connection is supported by the Firewall. Cannot Access the Web interface If the Firewall does not allow users or the administrator to log in to establish an authenticated session, try the following: I Make sure that the Web browser you change the IP address for more information. Link LED is...
User Guide
Page 169
... passwords are not accessible to users on , make sure the Caps Lock key is set to the Web interface. Potential Problems and Solutions 169 I Remember that Save Changes you can find the MAC address of the unit. I If there are any host devices other DHCP servers are duplicate IP address errors after you log in the Web browser and try the following: I Try restarting the router and LAN machines. You can reset the Firewall...
... passwords are not accessible to users on , make sure the Caps Lock key is set to the Web interface. Potential Problems and Solutions 169 I Remember that Save Changes you can find the MAC address of the unit. I If there are any host devices other DHCP servers are duplicate IP address errors after you log in the Web browser and try the following: I Try restarting the router and LAN machines. You can reset the Firewall...
User Guide
Page 201
... Internet browser: http://www.3com.com/ This service provides access to online support information such as technical documentation and software, as well as support options that you install, upgrade, configure, or support 3Com products. D TECHNICAL SUPPORT 3Com provides easy access to technical support information through the following online systems: I World Wide Web site I 3Com Knowledgebase Web Services I 3Com FTP site World Wide Web Site To access the latest networking information on the 3Com Corporation World Wide Web site at time...
... Internet browser: http://www.3com.com/ This service provides access to online support information such as technical documentation and software, as well as support options that you install, upgrade, configure, or support 3Com products. D TECHNICAL SUPPORT 3Com provides easy access to technical support information through the following online systems: I World Wide Web site I 3Com Knowledgebase Web Services I 3Com FTP site World Wide Web Site To access the latest networking information on the 3Com Corporation World Wide Web site at time...
User Guide
Page 207
...-T cable DMZ connection 33 LAN connection 33 255.255.255.0 181 3Com Knowledgebase Web Services 201 3Com Network Supervisor 20 3Com URL 201 A acceptable use policy 76, 88 access remote 24 access to URLs, restricting 23 ActiveX blocking 81 defined 68 add route 119 adding a service 101 administrator authenticating 164 password 53, 164 advanced redundant power supply 31 alert LED 30 alerts 24, 79 ARPS 31 attacks, DoS 21 authenticated management session 108 authentication 106 updating users 107 automatic IP address...
...-T cable DMZ connection 33 LAN connection 33 255.255.255.0 181 3Com Knowledgebase Web Services 201 3Com Network Supervisor 20 3Com URL 201 A acceptable use policy 76, 88 access remote 24 access to URLs, restricting 23 ActiveX blocking 81 defined 68 add route 119 adding a service 101 administrator authenticating 164 password 53, 164 advanced redundant power supply 31 alert LED 30 alerts 24, 79 ARPS 31 attacks, DoS 21 authenticated management session 108 authentication 106 updating users 107 automatic IP address...
User Guide
Page 208
... export file, specifying 92 export settings 92 before updating the software 93 F factory defaults, restoring 92, 162 features automatic IP address sharing and configuration 24 firewall security 21 Internet filtering 23 logs and alerts 24 user remote access 24 filter list updating 73 filter settings 67 filtering web 23 filters, specifying when they apply 70 Firewall attaching to WAN 33 main features 21 ports 19 positioning 28 purpose 19 quick setup 35 uses 19 firewall security 21 Firewall, moving 35 firmware...
... export file, specifying 92 export settings 92 before updating the software 93 F factory defaults, restoring 92, 162 features automatic IP address sharing and configuration 24 firewall security 21 Internet filtering 23 logs and alerts 24 user remote access 24 filter list updating 73 filter settings 67 filtering web 23 filters, specifying when they apply 70 Firewall attaching to WAN 33 main features 21 ports 19 positioning 28 purpose 19 quick setup 35 uses 19 firewall security 21 Firewall, moving 35 firmware...
User Guide
Page 210
... services adding 101 deleting 102 setting admin password 53 clock 54 password using Installation Wizard 37 setting up a Management Station 36 settings, reloading 91 setup, quick 35 siting the Internet Firewall 28 software, upgrading 92 specifications technical 197 specified addresses attaching to the LAN 117 attaching to the WAN 117 stateful packet inspection 22 static routes LAN settings 119 specifying 117 subnet mask defined 181 SuperStack 3 Firewall restarting 89 SYN Flood 15 SYN flood attacks 82 syslog server...
... services adding 101 deleting 102 setting admin password 53 clock 54 password using Installation Wizard 37 setting up a Management Station 36 settings, reloading 91 setup, quick 35 siting the Internet Firewall 28 software, upgrading 92 specifications technical 197 specified addresses attaching to the LAN 117 attaching to the WAN 117 stateful packet inspection 22 static routes LAN settings 119 specifying 117 subnet mask defined 181 SuperStack 3 Firewall restarting 89 SYN Flood 15 SYN flood attacks 82 syslog server...