Implementation Guide
Page 11
... enable you to 3Com at: pddtechpubs_comments@3com.com It is supplied in PDF format, this guide on how to access the management software to begin managing the Switch. ■ Management Interface Reference Guide This guide contains information about the current software release, including new features, modifications, and known problems. Your suggestions are very important to you to manage the Switch. ■ Release Notes These notes provide information about the web interface operations and CLI (command line interface) commands...
... enable you to 3Com at: pddtechpubs_comments@3com.com It is supplied in PDF format, this guide on how to access the management software to begin managing the Switch. ■ Management Interface Reference Guide This guide contains information about the current software release, including new features, modifications, and known problems. Your suggestions are very important to you to manage the Switch. ■ Release Notes These notes provide information about the web interface operations and CLI (command line interface) commands...
Implementation Guide
Page 16
... Switch, please refer to the Management Quick Reference Guide supplied in PDF format on the CD-ROM that allow devices to communicate using up to four links in use , you do not have this IP address. uses a device MAC address for authentication against unauthorized users connecting devices to your network: ■ Network Login - disables a port if an unauthorized device transmits data on it is already in parallel. The Switch tries each method in standalone mode...
... Switch, please refer to the Management Quick Reference Guide supplied in PDF format on the CD-ROM that allow devices to communicate using up to four links in use , you do not have this IP address. uses a device MAC address for authentication against unauthorized users connecting devices to your network: ■ Network Login - disables a port if an unauthorized device transmits data on it is already in parallel. The Switch tries each method in standalone mode...
Implementation Guide
Page 19
... of Service (QoS) enables you to ensure that they have different priorities across the network. The traffic prioritization feature supported by using layer 2 information, is given preference over a network. This enables you can be taken one step further by your network traffic to be prioritized to be forwarded, and which port should transmit the packet if it is to ensure that high priority data is forwarded on...
... of Service (QoS) enables you to ensure that they have different priorities across the network. The traffic prioritization feature supported by using layer 2 information, is given preference over a network. This enables you can be taken one step further by your network traffic to be prioritized to be forwarded, and which port should transmit the packet if it is to ensure that high priority data is forwarded on...
Implementation Guide
Page 23
... network and end users: ■ Increased bandwidth ■ Quicker connections ■ Faster transfer of data ■ Minimized data errors ■ Reduced network downtime For detailed descriptions of the web interface operations and the command line interface (CLI) commands that accompanies your network and improve network performance. Duplex Full duplex allows packets to operate at any one time. Port Features The default state for all the features detailed below provides the best configuration for example...
... network and end users: ■ Increased bandwidth ■ Quicker connections ■ Faster transfer of data ■ Minimized data errors ■ Reduced network downtime For detailed descriptions of the web interface operations and the command line interface (CLI) commands that accompanies your network and improve network performance. Duplex Full duplex allows packets to operate at any one time. Port Features The default state for all the features detailed below provides the best configuration for example...
Implementation Guide
Page 35
Snooping Mode Snooping Mode allows your Switch to forward multicast packets only to run multicast sessions in a network that does not contain any IGMP routers (or queriers). IGMP querying is disabled by default on the command line interface IGMP menu. You would enable query mode if you wish to the appropriate ports. This helps prevent interoperability issues with core products that wish to join a multicast group and then sets its filters accordingly Query Mode Query mode allows...
Snooping Mode Snooping Mode allows your Switch to forward multicast packets only to run multicast sessions in a network that does not contain any IGMP routers (or queriers). IGMP querying is disabled by default on the command line interface IGMP menu. You would enable query mode if you wish to the appropriate ports. This helps prevent interoperability issues with core products that wish to join a multicast group and then sets its filters accordingly Query Mode Query mode allows...
Implementation Guide
Page 36
... packet, it . The Switch can enable or disable multicast learning and IGMP querying using the snoopMode command on the CLI or the web interface. For more than that of any device that the LAN or VLAN requires traffic for the multicast groups. 5 When the router forwards traffic for the multicast group and then forwards the packet to the LAN or VLAN. Therefore, if there are connected to it registers that conforms to ports...
... packet, it . The Switch can enable or disable multicast learning and IGMP querying using the snoopMode command on the CLI or the web interface. For more than that of any device that the LAN or VLAN requires traffic for the multicast groups. 5 When the router forwards traffic for the multicast group and then forwards the packet to the LAN or VLAN. Therefore, if there are connected to it registers that conforms to ports...
Implementation Guide
Page 39
... following topics: ■ What is enabled by default on your Switch. They cover the following topics: ■ Spanning Tree Protocol (STP) ■ Rapid Spanning Tree Protocol (RSTP) - The following sections explain more resilient to the Management Interface Reference Guide supplied in your network. The Spanning Tree Protocol (STP) makes your network helps protect critical links against failure, protects against network loops, and reduces network downtime to STP" on page 45. To be...
... following topics: ■ What is enabled by default on your Switch. They cover the following topics: ■ Spanning Tree Protocol (STP) ■ Rapid Spanning Tree Protocol (RSTP) - The following sections explain more resilient to the Management Interface Reference Guide supplied in your network. The Spanning Tree Protocol (STP) makes your network helps protect critical links against failure, protects against network loops, and reduces network downtime to STP" on page 45. To be...
Implementation Guide
Page 40
... network. ■ Support for front panel ports. If you have Fast Start disabled on a port, the Switch will be used for ports connected to edge devices in RSTP (802.1w) mode, and other ports, for your network and ease of use the legacy 802.1D version of the IEEE 802.1D bridge specification. This mode should be referred to provide optimum performance for example those connected to a legacy Switch, to begin forwarding traffic...
... network. ■ Support for front panel ports. If you have Fast Start disabled on a port, the Switch will be used for ports connected to edge devices in RSTP (802.1w) mode, and other ports, for your network and ease of use the legacy 802.1D version of the IEEE 802.1D bridge specification. This mode should be referred to provide optimum performance for example those connected to a legacy Switch, to begin forwarding traffic...
Implementation Guide
Page 51
... all times can ensure this by maximising bandwidth and providing low latency. 6 USING TRAFFIC PRIORITIZATION What is most useful for voice and video data and traditional data. For more granular prioritization and an enhanced Quality of Service support, other products are available in the 3Com range of the web interface operations and the command line interface (CLI) commands that you require to manage the Switch please refer to the Management Quick Reference Guide supplied...
... all times can ensure this by maximising bandwidth and providing low latency. 6 USING TRAFFIC PRIORITIZATION What is most useful for voice and video data and traditional data. For more granular prioritization and an enhanced Quality of Service support, other products are available in the 3Com range of the web interface operations and the command line interface (CLI) commands that you require to manage the Switch please refer to the Management Quick Reference Guide supplied...
Implementation Guide
Page 55
... commands that you require, refer to the Management Interface Reference Guide supplied in the QoS feature through the creation of classifiers. Traffic Prioritization and your Switch 55 How traffic is processed to provide Quality of Service A received packet at the ingress port is checked for its DSCP and IEEE 802.1D attributes to determine the level of service that accompanies your Switch using the 3Com Network Supervisor or via the command line interface (CLI...
... commands that you require, refer to the Management Interface Reference Guide supplied in the QoS feature through the creation of classifiers. Traffic Prioritization and your Switch 55 How traffic is processed to provide Quality of Service A received packet at the ingress port is checked for its DSCP and IEEE 802.1D attributes to determine the level of service that accompanies your Switch using the 3Com Network Supervisor or via the command line interface (CLI...
Implementation Guide
Page 70
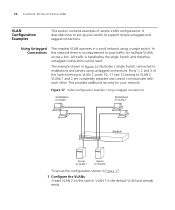
... for multiple VLANs across a link. VLAN 1 is handled by the single Switch and therefore untagged connections can be used. All traffic is the default VLAN and already exists. It describes how to set up your network. In this network there is no requirement to pass traffic for your switch to support simple untagged and tagged connections. Figure 17 VLAN configuration example: Using untagged connections To set up the configuration shown in Figure 17: 1 Configure the VLANs Create VLAN...
... for multiple VLANs across a link. VLAN 1 is handled by the single Switch and therefore untagged connections can be used. All traffic is the default VLAN and already exists. It describes how to set up your network. In this network there is no requirement to pass traffic for your switch to support simple untagged and tagged connections. Figure 17 VLAN configuration example: Using untagged connections To set up the configuration shown in Figure 17: 1 Configure the VLANs Create VLAN...
Implementation Guide
Page 74
... accessible from a remote management workstation on the network have to SNMP requests. In addition, the Switch will configure itself with its default IP address 169.254.100.100 if it is set up for no other Switches on the LAN. How Automatic IP Configuration Works When your Switch across the network): ■ Automatic IP Configuration (default) - the Switch tries to automatic - You can switch to manual IP configuration at any time using a serial port connection to set...
... accessible from a remote management workstation on the network have to SNMP requests. In addition, the Switch will configure itself with its default IP address 169.254.100.100 if it is set up for no other Switches on the LAN. How Automatic IP Configuration Works When your Switch across the network): ■ Automatic IP Configuration (default) - the Switch tries to automatic - You can switch to manual IP configuration at any time using a serial port connection to set...
Implementation Guide
Page 78
... Port Security The Switch supports the following port security modes, which you can set for an individual port or a range of ports: ■ No Security Port security is disabled and all network traffic is forwarded through the port without any restrictions. ■ Continuous Learning MAC addresses are learned continuously by the port until the number of authorized addresses configured for the port then it will transition to the "Learning Off" mode. ■ Network Login...
... Port Security The Switch supports the following port security modes, which you can set for an individual port or a range of ports: ■ No Security Port security is disabled and all network traffic is forwarded through the port without any restrictions. ■ Continuous Learning MAC addresses are learned continuously by the port until the number of authorized addresses configured for the port then it will transition to the "Learning Off" mode. ■ Network Login...
Implementation Guide
Page 87
...: ■ Configuration Save and Restore ■ Upgrading Management Software For detailed descriptions of Command Line Interface (CLI) commands. You must restore the configuration of your Switch or on a remote server, or to be able to the Management Interface Reference Guide supplied in an editable ASCII text file as user passwords and the IP address configuration is saved and restored. If a manager level 11 USING SWITCH CONFIGURATION FEATURES This chapter explains the configuration features supported by the Switch that is not saved. If the Switch is part of a stack, it...
...: ■ Configuration Save and Restore ■ Upgrading Management Software For detailed descriptions of Command Line Interface (CLI) commands. You must restore the configuration of your Switch or on a remote server, or to be able to the Management Interface Reference Guide supplied in an editable ASCII text file as user passwords and the IP address configuration is saved and restored. If a manager level 11 USING SWITCH CONFIGURATION FEATURES This chapter explains the configuration features supported by the Switch that is not saved. If the Switch is part of a stack, it...
Implementation Guide
Page 88
... or stack is , LACP enabled on the ports that are available to that user level. Parameters such as VLANs and Fast Start may be enabled and Spanning Tree Protocol enabled. LACP automatic aggregations with automatic ports where the aggregated link is disabled and Spanning Tree Protocol is disabled are restored as manual aggregations with manual ports. Important Considerations ■ The Switch unit must only be restored or saved by a security level user, the restore operation will fail because the security level commands...
... or stack is , LACP enabled on the ports that are available to that user level. Parameters such as VLANs and Fast Start may be enabled and Spanning Tree Protocol enabled. LACP automatic aggregations with automatic ports where the aggregated link is disabled and Spanning Tree Protocol is disabled are restored as manual aggregations with manual ports. Important Considerations ■ The Switch unit must only be restored or saved by a security level user, the restore operation will fail because the security level commands...
Implementation Guide
Page 99
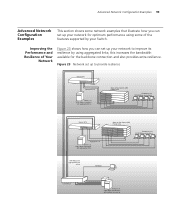
Advanced Network Configuration Examples 99 Advanced Network Configuration Examples This section shows some network examples that illustrate how you can set up 100 Mbps Core Switch Servers on 1000 Mbps connections with aggregated links Stack of the features supported by using some of four Switch 4200 Family units Endstations on 1000 Mbps connection with resilient links set up Figure 23 Network set up your Switch. Improving the Performance and Resilience of Your Network Figure 23 shows how...
Advanced Network Configuration Examples 99 Advanced Network Configuration Examples This section shows some network examples that illustrate how you can set up 100 Mbps Core Switch Servers on 1000 Mbps connections with aggregated links Stack of the features supported by using some of four Switch 4200 Family units Endstations on 1000 Mbps connection with resilient links set up Figure 23 Network set up your Switch. Improving the Performance and Resilience of Your Network Figure 23 shows how...
Implementation Guide
Page 109
..., that also supports auto-negotiation, the link can transmit. auto-negotiation A feature on twisted pair ports that allows them to a port that a channel can automatically configure itself to the optimum setup. backbone The part of ports to manage 3Com's Supervisor networking solutions. 10BASE-T The IEEE specification for 10 Mbps Ethernet over Category 3, 4 or 5 twisted pair cable. 100BASE-FX The IEEE specification for 100 Mbps Fast Ethernet over multimode fiber-optic cable. 100BASE...
..., that also supports auto-negotiation, the link can transmit. auto-negotiation A feature on twisted pair ports that allows them to a port that a channel can automatically configure itself to the optimum setup. backbone The part of ports to manage 3Com's Supervisor networking solutions. 10BASE-T The IEEE specification for 10 Mbps Ethernet over Category 3, 4 or 5 twisted pair cable. 100BASE-FX The IEEE specification for 100 Mbps Fast Ethernet over multimode fiber-optic cable. 100BASE...
Implementation Guide
Page 115
... of Spanning Tree topology throughout the bridged network. The rules dictate format, timing, sequencing and error control. Rada Radius Authenticated Device Access. RMON IETF Remote Monitoring MIB. router A router is a device on a network. 115 Policy Comprises a set of rules for communication between a network device and a shared authentication server. QoS Profile Consists of multiple sets of "rules" that one takes over data transmission should the other fail. An alternative name for a router is a gateway...
... of Spanning Tree topology throughout the bridged network. The rules dictate format, timing, sequencing and error control. Rada Radius Authenticated Device Access. RMON IETF Remote Monitoring MIB. router A router is a device on a network. 115 Policy Comprises a set of rules for communication between a network device and a shared authentication server. QoS Profile Consists of multiple sets of "rules" that one takes over data transmission should the other fail. An alternative name for a router is a gateway...
Implementation Guide
Page 116
... link fails. A protocol that allows IP to divide the device part of the network using a switch or bridge. The current IETF standard protocol for example, best effort, business critical, network control, and so on. The Switch offers some predefined standard service levels, for managing devices on networks. An IETF standard protocol used to run over data transmission if the main port in a network that takes over a serial line (console port) connection. Spanning Tree Protocol (STP...
... link fails. A protocol that allows IP to divide the device part of the network using a switch or bridge. The current IETF standard protocol for example, best effort, business critical, network control, and so on. The Switch offers some predefined standard service levels, for managing devices on networks. An IETF standard protocol used to run over data transmission if the main port in a network that takes over a serial line (console port) connection. Spanning Tree Protocol (STP...
Implementation Guide
Page 120
..., default 43 port security 16, 77, 78 priority in STP 43 priority levels 802.1D 52 Q QoS apply QoS profile 56 configuring traffic on a Switch 4200 55 creating profiles 56 How traffic is processed to provide QoS 55 service levels 55 traffic classification 55 Quality of VLANs 48 Bridge Identifier 43 Bridge Protocol Data Units 43 See Switch Database security network 77 segment, maximum length 94 smart auto-sensing 25 Spanning Tree...
..., default 43 port security 16, 77, 78 priority in STP 43 priority levels 802.1D 52 Q QoS apply QoS profile 56 configuring traffic on a Switch 4200 55 creating profiles 56 How traffic is processed to provide QoS 55 service levels 55 traffic classification 55 Quality of VLANs 48 Bridge Identifier 43 Bridge Protocol Data Units 43 See Switch Database security network 77 segment, maximum length 94 smart auto-sensing 25 Spanning Tree...