Security Target
Page 4
... 68 6.2 Security Assurance Requirements 68 6.3 Security Requirements Rationale 69 6.3.1 Tracing ...69 6.3.2 Justification of Traceability 71 6.3.3 Dependency Analysis 77 6.3.4 Security Assurance Requirements Rationale 79 7 TOE Summary Specification 80 7.1 Audit Function ...80 7.2 Identification and Authentication Function 82 Copyright (c) 2011...
... 68 6.2 Security Assurance Requirements 68 6.3 Security Requirements Rationale 69 6.3.1 Tracing ...69 6.3.2 Justification of Traceability 71 6.3.3 Dependency Analysis 77 6.3.4 Security Assurance Requirements Rationale 79 7 TOE Summary Specification 80 7.1 Audit Function ...80 7.2 Identification and Authentication Function 82 Copyright (c) 2011...
Security Target
Page 6
...of Administrative Roles...19 Table 8 : Definition of User Data ...26 Table 9 : Definition of TSF Data ...27 Table 10 : Specific Terms Related to This ST 27 Table 11 : Rationale for Security Objectives 42 Table 12 : List of Auditable Events ...49 Table...Roles Allowed to Override Default Values 64 Table 29 : List of TSF Data ...65 Table 30 : List of Specification of Management Functions 66 Table 31 : TOE Security Assurance Requirements (EAL3+ALC_FLR.2 69 Table 32 : Relationship between Security... 35 : List of Audit Log Items ...81 Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
...of Administrative Roles...19 Table 8 : Definition of User Data ...26 Table 9 : Definition of TSF Data ...27 Table 10 : Specific Terms Related to This ST 27 Table 11 : Rationale for Security Objectives 42 Table 12 : List of Auditable Events ...49 Table...Roles Allowed to Override Default Values 64 Table 29 : List of TSF Data ...65 Table 30 : List of Specification of Management Functions 66 Table 31 : TOE Security Assurance Requirements (EAL3+ALC_FLR.2 69 Table 32 : Relationship between Security... 35 : List of Audit Log Items ...81 Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
Security Target
Page 27
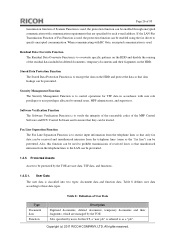
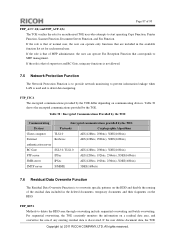
... Residual Data Overwrite Function is to control operations for each e-mail address. Security Management Function The Security Management Function is to overwrite specific patterns on the HDD and disable the reusing of the residual data included in accordance with RC Gate, encrypted communication is used.... are managed by users. User Data The user data is used to as the "fax line") can be prevented. Copyright (c) 2011 RICOH COMPANY, LTD. If the LAN-Fax Transmission Function of the MFP Control Software and FCU Control Software and to ensure that unauthorised intrusion...
... Residual Data Overwrite Function is to control operations for each e-mail address. Security Management Function The Security Management Function is to overwrite specific patterns on the HDD and disable the reusing of the residual data included in accordance with RC Gate, encrypted communication is used.... are managed by users. User Data The user data is used to as the "fax line") can be prevented. Copyright (c) 2011 RICOH COMPANY, LTD. If the LAN-Fax Transmission Function of the MFP Control Software and FCU Control Software and to ensure that unauthorised intrusion...
Security Target
Page 28
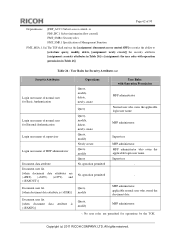
...data". The components that are for management of the document data of user data are classified as "TSF confidential data". Copyright (c) 2011 RICOH COMPANY, LTD. Login password, audit log, and HDD cryptographic key. 1.4.5.3. Functions The MFP applications (Copy Function, Document Server Function, .... Login user name, Number of Attempts before Lockout, settings for This ST For clear understanding of specific terms. Terms MFP Control Software Table 10 : Specific Terms Related to the public. This data must be protected from changes by users without viewing permissions....
...data". The components that are for management of the document data of user data are classified as "TSF confidential data". Copyright (c) 2011 RICOH COMPANY, LTD. Login password, audit log, and HDD cryptographic key. 1.4.5.3. Functions The MFP applications (Copy Function, Document Server Function, .... Login user name, Number of Attempts before Lockout, settings for This ST For clear understanding of specific terms. Terms MFP Control Software Table 10 : Specific Terms Related to the public. This data must be protected from changes by users without viewing permissions....
Security Target
Page 48
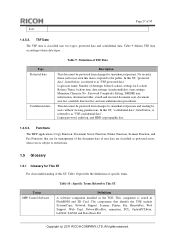
... external interfaces before these data are intended to require TSF controlled processing of functionality. Many products receive information on specific external interfaces and are sent out on another external interface. Component levelling: FPT_FDI_EXP: Restricted forwarding of data to external...an administrative role c) Revocation of data from one requires explicit allowance by an authorized administrative role. Examples Copyright (c) 2011 RICOH COMPANY, LTD. Rationale: Quite often, a TOE is supposed to perform the management activities b) Management of the conditions under...
... external interfaces before these data are intended to require TSF controlled processing of functionality. Many products receive information on specific external interfaces and are sent out on another external interface. Component levelling: FPT_FDI_EXP: Restricted forwarding of data to external...an administrative role c) Revocation of data from one requires explicit allowance by an authorized administrative role. Examples Copyright (c) 2011 RICOH COMPANY, LTD. Rationale: Quite often, a TOE is supposed to perform the management activities b) Management of the conditions under...
Security Target
Page 49
... this . However, in either the FDP or the FPT class. Copyright (c) 2011 RICOH COMPANY, LTD. The Common Criteria defines attribute-based control of the existing families in either too implementation-specific for a Protection Profile or too unwieldy for the incoming data before it could therefore... for this functionality. It has been viewed as useful to have this functionality as useful to : No other components Dependencies: FMT_SMF.1 Specification of 93 are firewall systems but also other systems that -if allowed at all-can be transferred. Therefore, the authors decided to...
... this . However, in either the FDP or the FPT class. Copyright (c) 2011 RICOH COMPANY, LTD. The Common Criteria defines attribute-based control of the existing families in either too implementation-specific for a Protection Profile or too unwieldy for the incoming data before it could therefore... for this functionality. It has been viewed as useful to have this functionality as useful to : No other components Dependencies: FMT_SMF.1 Specification of 93 are firewall systems but also other systems that -if allowed at all-can be transferred. Therefore, the authors decided to...
Security Target
Page 51
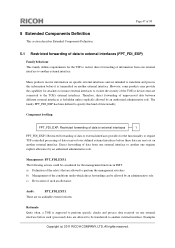
... the user. Start and end operation of downloading document data. - a) Minimal: Unsuccessful use of the authentication mechanism; c) Detailed: The specific security attributes used in making an access check. Start and end operation of deleting document data. All rights reserved. b) Basic: All use...failure of login operation b) Basic: Success and failure of the authentication mechanism; b) Basic: All use of Copyright (c) 2011 RICOH COMPANY, LTD. Page 50 of 93 FDP_ACF.1(b) FIA_UAU.1(a) FIA_UAU.1(b) FIA_UAU.2 perform an operation on an object covered by the SFP.
... the user. Start and end operation of downloading document data. - a) Minimal: Unsuccessful use of the authentication mechanism; c) Detailed: The specific security attributes used in making an access check. Start and end operation of deleting document data. All rights reserved. b) Basic: All use...failure of login operation b) Basic: Success and failure of the authentication mechanism; b) Basic: All use of Copyright (c) 2011 RICOH COMPANY, LTD. Page 50 of 93 FDP_ACF.1(b) FIA_UAU.1(a) FIA_UAU.1(b) FIA_UAU.2 perform an operation on an object covered by the SFP.
Security Target
Page 63
Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. Table 26 : User Roles for Security Attributes (a) Security Attributes Login user name of normal user for Basic Authentication Login user ... the applicable login user name Supervisor - Page 62 of 93 Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of MFP administrator Document data attribute Document user list [when document data attributes are permitted for operations by the TOE.
Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. Table 26 : User Roles for Security Attributes (a) Security Attributes Login user name of normal user for Basic Authentication Login user ... the applicable login user name Supervisor - Page 62 of 93 Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of MFP administrator Document data attribute Document user list [when document data attributes are permitted for operations by the TOE.
Security Target
Page 64
FMT_MSA.3(a)Static attribute initialisation Hierarchical to : No other components. All rights reserved. Copyright (c) 2011 RICOH COMPANY, LTD. Page 63 of 93 FMT_MSA.1(b)Management of security attributes FMT_SMR.1 Security roles FMT_MSA.3.1(a) The TSF ...for operations by the TOE. Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of External Authentication) No operation permitted No operation permitted User Roles with operation permission in Table 27] to [assignment: the user roles with...
FMT_MSA.3(a)Static attribute initialisation Hierarchical to : No other components. All rights reserved. Copyright (c) 2011 RICOH COMPANY, LTD. Page 63 of 93 FMT_MSA.1(b)Management of security attributes FMT_SMR.1 Security roles FMT_MSA.3.1(a) The TSF ...for operations by the TOE. Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of External Authentication) No operation permitted No operation permitted User Roles with operation permission in Table 27] to [assignment: the user roles with...
Security Target
Page 65
... 28] to specify alternative initial values to override the default values when an object or information is created. Dependencies: FMT_SMR.1 Security roles FMT_SMF.1 Specification of 93 FMT_MSA.3.2(a) The TSF shall allow the [assignment: MFP administrator for the available function list, no authorised identified roles for the function type...No authorised identified roles FMT_MSA.3(b) Static attribute initialisation Hierarchical to : No other components. All rights reserved. Page 64 of Management Functions Copyright (c) 2011 RICOH COMPANY, LTD. No authorised identified roles -
... 28] to specify alternative initial values to override the default values when an object or information is created. Dependencies: FMT_SMR.1 Security roles FMT_SMF.1 Specification of 93 FMT_MSA.3.2(a) The TSF shall allow the [assignment: MFP administrator for the available function list, no authorised identified roles for the function type...No authorised identified roles FMT_MSA.3(b) Static attribute initialisation Hierarchical to : No other components. All rights reserved. Page 64 of Management Functions Copyright (c) 2011 RICOH COMPANY, LTD. No authorised identified roles -
Security Target
Page 67
... and received documents User authentication method Operations Query, modify Query User Roles MFP administrator MFP administrator FMT_SMF.1 Specification of performing the following management functions: [assignment: management functions shown in Table 30]. Table 30 : List of Specification of Management Functions Management Functions New creation, query, modification, and deletion of the login user name...modification of available function list by MFP administrator Query of own available function list by normal user when the Basic Authentication is used Copyright (c) 2011 RICOH COMPANY, LTD.
... and received documents User authentication method Operations Query, modify Query User Roles MFP administrator MFP administrator FMT_SMF.1 Specification of performing the following management functions: [assignment: management functions shown in Table 30]. Table 30 : List of Specification of Management Functions Management Functions New creation, query, modification, and deletion of the login user name...modification of available function list by MFP administrator Query of own available function list by normal user when the Basic Authentication is used Copyright (c) 2011 RICOH COMPANY, LTD.
Security Target
Page 69
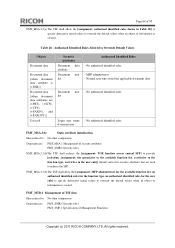
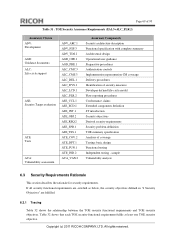
... FTP_ITC.1.2 The TSF shall permit [selection: the TSF, another trusted IT product that is EAL3+ALC_FLR.2. Copyright (c) 2011 RICOH COMPANY, LTD. Dependencies: No dependencies. FTP_ITC.1.1 The TSF shall provide a communication channel between itself and another trusted IT ...channel. Table 31 lists the assurance components of the TOE. All rights reserved. Dependencies: No dependencies. Dependencies: FMT_SMF.1 Specification of Management Functions FMT_SMR.1 Security roles FPT_FDI_EXP.1.1 The TSF shall provide the capability to : No other components. ALC_FLR.2 ...
... FTP_ITC.1.2 The TSF shall permit [selection: the TSF, another trusted IT product that is EAL3+ALC_FLR.2. Copyright (c) 2011 RICOH COMPANY, LTD. Dependencies: No dependencies. FTP_ITC.1.1 The TSF shall provide a communication channel between itself and another trusted IT ...channel. Table 31 lists the assurance components of the TOE. All rights reserved. Dependencies: No dependencies. Dependencies: FMT_SMF.1 Specification of Management Functions FMT_SMR.1 Security roles FPT_FDI_EXP.1.1 The TSF shall provide the capability to : No other components. ALC_FLR.2 ...
Security Target
Page 70
....2 ASE_REQ.2 ASE_SPD.1 ASE_TSS.1 ATE_COV.2 ATE_DPT.1 ATE_FUN.1 ATE_IND.2 AVA_VAN.2 Assurance Components Security architecture description Functional specification with complete summary Architectural design Operational user guidance Preparative procedures Authorisation controls Implementation representation CM coverage Delivery procedures Identification... components definition ST introduction Security objectives Derived security requirements Security problem definition TOE summary specification Analysis of coverage Testing: basic design Functional testing Independent testing - Table 32 shows...
....2 ASE_REQ.2 ASE_SPD.1 ASE_TSS.1 ATE_COV.2 ATE_DPT.1 ATE_FUN.1 ATE_IND.2 AVA_VAN.2 Assurance Components Security architecture description Functional specification with complete summary Architectural design Operational user guidance Preparative procedures Authorisation controls Implementation representation CM coverage Delivery procedures Identification... components definition ST introduction Security objectives Derived security requirements Security problem definition TOE summary specification Analysis of coverage Testing: basic design Functional testing Independent testing - Table 32 shows...
Security Target
Page 74
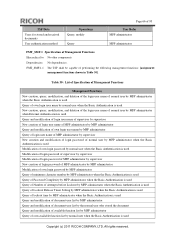
...fulfilled. By satisfying FMT_MTD.1, FMT_SMF.1, FMT_SMR.1 and FTP_ITC.1, which are the security functional requirements for Security Function. (3) Specification of supervisor. A supervisor is the security objective to allow only users who can maintain the security to alter the TSF... for sending or receiving TSF confidential data. Copyright (c) 2011 RICOH COMPANY, LTD. FMT_SMR.1 maintains the users who have the privileges. (4) Use trusted channels for stored and received documents. (2) Specification of administrator. By FMT_MTD.1, only the MFP administrator is required...
...fulfilled. By satisfying FMT_MTD.1, FMT_SMF.1, FMT_SMR.1 and FTP_ITC.1, which are the security functional requirements for Security Function. (3) Specification of supervisor. A supervisor is the security objective to allow only users who can maintain the security to alter the TSF... for sending or receiving TSF confidential data. Copyright (c) 2011 RICOH COMPANY, LTD. FMT_SMR.1 maintains the users who have the privileges. (4) Use trusted channels for stored and received documents. (2) Specification of administrator. By FMT_MTD.1, only the MFP administrator is required...
Security Target
Page 75
...printed by using passwords when the TOE is only allowed to operate the audit log and newly create an HDD cryptographic key. (2) Specification of the Management Function. FMT_SMR.1 maintains the users who have the privileges. (4) Use trusted channels for these countermeasures, O.CONF.NO_ALT...and if the person is the normal user, the External Authentication is allowed to operate the login password of supervisor. Copyright (c) 2011 RICOH COMPANY, LTD. FMT_MTD.1 allows the MFP administrator and applicable normal user to operate the login password of administrator. By satisfying FMT_MTD.1,...
...printed by using passwords when the TOE is only allowed to operate the audit log and newly create an HDD cryptographic key. (2) Specification of the Management Function. FMT_SMR.1 maintains the users who have the privileges. (4) Use trusted channels for these countermeasures, O.CONF.NO_ALT...and if the person is the normal user, the External Authentication is allowed to operate the login password of supervisor. Copyright (c) 2011 RICOH COMPANY, LTD. FMT_MTD.1 allows the MFP administrator and applicable normal user to operate the login password of administrator. By satisfying FMT_MTD.1,...
Security Target
Page 78
... FAU_STG.1 FAU_GEN.1 FAU_SAR.1 FCS_COP.1 Dependencies Not Satisfied in the HDD, and decrypts the data to manage the cryptographic keys. (4) Specification of Management Function. By satisfying FTP_ITC.1, which are concealed, and any tampering on the communication path is fulfilled. 6.3.3 Dependency Analysis... fulfilled. FMT_MTD.1 allows the MFP administrator to be stored in ST None None None None None None FCS_CKM.4 Copyright (c) 2011 RICOH COMPANY, LTD. To fulfil this countermeasure, O.RCGATE.COMM.PROTECT is detected. By satisfying FCS_CKM.1, FCS_COP.1, FMT_MTD.1, FMT_SMF.1 and...
... FAU_STG.1 FAU_GEN.1 FAU_SAR.1 FCS_COP.1 Dependencies Not Satisfied in the HDD, and decrypts the data to manage the cryptographic keys. (4) Specification of Management Function. By satisfying FTP_ITC.1, which are concealed, and any tampering on the communication path is fulfilled. 6.3.3 Dependency Analysis... fulfilled. FMT_MTD.1 allows the MFP administrator to be stored in ST None None None None None None FCS_CKM.4 Copyright (c) 2011 RICOH COMPANY, LTD. To fulfil this countermeasure, O.RCGATE.COMM.PROTECT is detected. By satisfying FCS_CKM.1, FCS_COP.1, FMT_MTD.1, FMT_SMF.1 and...
Security Target
Page 81
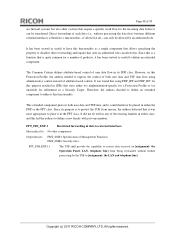
... are recorded, and expanded log items are described for each security function. Page 80 of 93 7 TOE Summary Specification This section describes the TOE summary specification for each corresponding security functional requirement. 7.1 Audit Function The Audit Function is to generate the audit log of TOE...and failure of login operations from the system clock of Management Function Date settings (year/month/day), time settings (hour/minute) Copyright (c) 2011 RICOH COMPANY, LTD. FAU_GEN.1 and FAU_GEN.2 The TOE records the audit log items, shown in Table 35, on a Web browser screen only ...
... are recorded, and expanded log items are described for each security function. Page 80 of 93 7 TOE Summary Specification This section describes the TOE summary specification for each corresponding security functional requirement. 7.1 Audit Function The Audit Function is to generate the audit log of TOE...and failure of login operations from the system clock of Management Function Date settings (year/month/day), time settings (hour/minute) Copyright (c) 2011 RICOH COMPANY, LTD. FAU_GEN.1 and FAU_GEN.2 The TOE records the audit log items, shown in Table 35, on a Web browser screen only ...
Security Target
Page 88
If the user deletes document data, the TOE Copyright (c) 2011 RICOH COMPANY, LTD. If the role is used and to detect data tampering. FDP_RIP.1 Methods to MFP management. If the role is that of supervisor and ... operate Fax Reception Function that of the residual data included in the available function list set for an authorised TOE user who attempts to overwrite specific patterns on the HDD and disable the reusing of MFP administrator, the user can operate only functions that are included in the deleted documents, temporary...
If the user deletes document data, the TOE Copyright (c) 2011 RICOH COMPANY, LTD. If the role is used and to detect data tampering. FDP_RIP.1 Methods to MFP management. If the role is that of supervisor and ... operate Fax Reception Function that of the residual data included in the available function list set for an authorised TOE user who attempts to overwrite specific patterns on the HDD and disable the reusing of MFP administrator, the user can operate only functions that are included in the deleted documents, temporary...