Manuals
Page 42
... limit is replaced with "...". Getting Started 5. To change the image, see "Registering a Shortcut to a Program to the [Home] Screen", Convenient Functions . • You can also review icons of functions and embedded software applications that are registered to Favorites by User cannot be registered to scan originals and save images as a corporate...
... limit is replaced with "...". Getting Started 5. To change the image, see "Registering a Shortcut to a Program to the [Home] Screen", Convenient Functions . • You can also review icons of functions and embedded software applications that are registered to Favorites by User cannot be registered to scan originals and save images as a corporate...
Security Target
Page 36
...of the external interfaces of the TOE, operation of storage devices The data stored on the HDD inside the TOE shall be reviewed by authorised persons. A.USER.TRAINING User training The responsible manager of MFP trains users according to the guidance document and users... in a restricted or monitored area that provides protection from unauthorised disclosure or alteration, and shall be encrypted. Copyright (c) 2012 RICOH COMPANY, LTD. All rights reserved. P.SOFTWARE.VERIFICATION Software verification Procedures shall exist to the guidance document, the TOE is placed in the...
...of the external interfaces of the TOE, operation of storage devices The data stored on the HDD inside the TOE shall be reviewed by authorised persons. A.USER.TRAINING User training The responsible manager of MFP trains users according to the guidance document and users... in a restricted or monitored area that provides protection from unauthorised disclosure or alteration, and shall be encrypted. Copyright (c) 2012 RICOH COMPANY, LTD. All rights reserved. P.SOFTWARE.VERIFICATION Software verification Procedures shall exist to the guidance document, the TOE is placed in the...
Security Target
Page 40
...to the guidance document for detecting security violations or unusual patterns of activity. Copyright (c) 2012 RICOH COMPANY, LTD. have the competence to follow the guidance document; OE.AUDIT.REVIEWED Log audit The responsible manager of MFP shall ensure that provides protection from physical access to...manager of MFP shall select administrators who will not use the TOE in a secure or monitored area that audit logs are reviewed at appropriate intervals according to those policies and procedures. OE.ADMIN.TRAINED Administrator training The responsible manager of MFP shall ensure ...
...to the guidance document for detecting security violations or unusual patterns of activity. Copyright (c) 2012 RICOH COMPANY, LTD. have the competence to follow the guidance document; OE.AUDIT.REVIEWED Log audit The responsible manager of MFP shall ensure that provides protection from physical access to...manager of MFP shall select administrators who will not use the TOE in a secure or monitored area that audit logs are reviewed at appropriate intervals according to those policies and procedures. OE.ADMIN.TRAINED Administrator training The responsible manager of MFP shall ensure ...
Security Target
Page 41
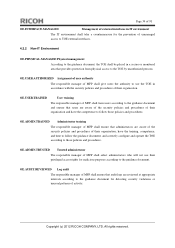
...NO_ALT O.PROT.NO_ALT O.CONF.NO_DIS O.CONF.NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE.INTERFACE.MANAGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT OE.ADMIN.TRAINED OE.ADMIN.TRUSTED OE.USER.TRAINED T.DOC.DIS ....VERIFICATION X P.AUDIT.LOGGING X XXX P.INTERFACE.MANAGEMENT X X P.STORAGE.ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright (c) 2012 RICOH COMPANY, LTD.
...NO_ALT O.PROT.NO_ALT O.CONF.NO_DIS O.CONF.NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE.INTERFACE.MANAGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT OE.ADMIN.TRAINED OE.ADMIN.TRUSTED OE.USER.TRAINED T.DOC.DIS ....VERIFICATION X P.AUDIT.LOGGING X XXX P.INTERFACE.MANAGEMENT X X P.STORAGE.ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright (c) 2012 RICOH COMPANY, LTD.
Security Target
Page 44
...HDD, and written on the communication path between itself and RC Gate, and detect any tampering with the security policies. Copyright (c) 2012 RICOH COMPANY, LTD. P.AUDIT.LOGGING is enforced by O.STORAGE.ENCRYPTED. By O.INTERFACE.MANAGED, the TOE manages the operation of TOE use ...and security-relevant events in accordance with those records from the physical access by O.AUDIT.LOGGED, OE.AUDIT.REVIEWED, OE.AUDIT_STORAGE.PROTECTED and OE.AUDIT_ACCESS.AUTHORIZED. P.STORAGE.ENCRYPTION is enforced by OE.PHYSICAL.MANAGED. A.ACCESS.MANAGED A.ACCESS.MANAGED is ...
...HDD, and written on the communication path between itself and RC Gate, and detect any tampering with the security policies. Copyright (c) 2012 RICOH COMPANY, LTD. P.AUDIT.LOGGING is enforced by O.STORAGE.ENCRYPTED. By O.INTERFACE.MANAGED, the TOE manages the operation of TOE use ...and security-relevant events in accordance with those records from the physical access by O.AUDIT.LOGGED, OE.AUDIT.REVIEWED, OE.AUDIT_STORAGE.PROTECTED and OE.AUDIT_ACCESS.AUTHORIZED. P.STORAGE.ENCRYPTION is enforced by OE.PHYSICAL.MANAGED. A.ACCESS.MANAGED A.ACCESS.MANAGED is ...
Security Target
Page 51
...assignment: the MFP administrators] with the identity of log items] from unauthorised deletion. Dependencies: FAU_SAR.1 Audit review FAU_SAR.2.1 The TSF shall prohibit all of the user that have been granted explicit read access to : No other components....: [FCS_CKM.2 Cryptographic key distribution, or FCS_COP.1 Cryptographic operation] FCS_CKM.4 Cryptographic key destruction Copyright (c) 2012 RICOH COMPANY, LTD. All rights reserved. FAU_SAR.2 Restricted audit review Hierarchical to : No other components. Page 50 of audit storage failure] if the audit trail is full...
...assignment: the MFP administrators] with the identity of log items] from unauthorised deletion. Dependencies: FAU_SAR.1 Audit review FAU_SAR.2.1 The TSF shall prohibit all of the user that have been granted explicit read access to : No other components....: [FCS_CKM.2 Cryptographic key distribution, or FCS_COP.1 Cryptographic operation] FCS_CKM.4 Cryptographic key destruction Copyright (c) 2012 RICOH COMPANY, LTD. All rights reserved. FAU_SAR.2 Restricted audit review Hierarchical to : No other components. Page 50 of audit storage failure] if the audit trail is full...
Security Target
Page 79
... the audit log items shown in Table 34, on WIM screen only when it is to generate the audit log of Management Function Copyright (c) 2012 RICOH COMPANY, LTD. All rights reserved. The TOE provides the audit logs in Table 33 occur. The security functions are derived from RC Gate are recorded... read on the HDD in the TOE when audit events shown in a text format when the MFP administrator instructs the TOE to audit (audit log review). The recorded audit log can be read the audit logs.
... the audit log items shown in Table 34, on WIM screen only when it is to generate the audit log of Management Function Copyright (c) 2012 RICOH COMPANY, LTD. All rights reserved. The TOE provides the audit logs in Table 33 occur. The security functions are derived from RC Gate are recorded... read on the HDD in the TOE when audit events shown in a text format when the MFP administrator instructs the TOE to audit (audit log review). The recorded audit log can be read the audit logs.