Manuals
Page 42
... details about how to use the browser function, see "Specifying the Settings for registering a shortcut using the browser function. Home screen image You can also review icons of up to Favorites by User cannot be displayed in a Program". • For details about how to use the fax function, see Scan . 7. [Facsimile...
... details about how to use the browser function, see "Specifying the Settings for registering a shortcut using the browser function. Home screen image You can also review icons of up to Favorites by User cannot be displayed in a Program". • For details about how to use the fax function, see Scan . 7. [Facsimile...
Security Target
Page 36
... P.RCGATE.COMM.PROTECT Protection of communication with RC Gate As for communication with operation permission of the TOE shall be reviewed by unauthorised persons. All rights reserved. P.STORAGE.ENCRYPTION Encryption of storage devices The data stored on the HDD inside ... interfaces To prevent unauthorised use of the external interfaces of the TOE, operation of those policies and procedures. Copyright (c) 2012 RICOH COMPANY, LTD. 3.2 Organisational Security Policies The following organisational security policies are taken: Page 35 of 91 P.USER.AUTHORIZATION User ...
... P.RCGATE.COMM.PROTECT Protection of communication with RC Gate As for communication with operation permission of the TOE shall be reviewed by unauthorised persons. All rights reserved. P.STORAGE.ENCRYPTION Encryption of storage devices The data stored on the HDD inside ... interfaces To prevent unauthorised use of the external interfaces of the TOE, operation of those policies and procedures. Copyright (c) 2012 RICOH COMPANY, LTD. 3.2 Organisational Security Policies The following organisational security policies are taken: Page 35 of 91 P.USER.AUTHORIZATION User ...
Security Target
Page 40
...malicious purposes according to the guidance document. OE.AUDIT.REVIEWED Log audit The responsible manager of MFP shall ensure that audit logs are reviewed at appropriate intervals according to the guidance document and ensure... that administrators are aware of the security policies and procedures of their organisation; OE.ADMIN.TRAINED Administrator training The responsible manager of MFP shall ensure that users are aware of the security policies and procedures of activity. Copyright (c) 2012 RICOH...
...malicious purposes according to the guidance document. OE.AUDIT.REVIEWED Log audit The responsible manager of MFP shall ensure that audit logs are reviewed at appropriate intervals according to the guidance document and ensure... that administrators are aware of the security policies and procedures of their organisation; OE.ADMIN.TRAINED Administrator training The responsible manager of MFP shall ensure that users are aware of the security policies and procedures of activity. Copyright (c) 2012 RICOH...
Security Target
Page 41
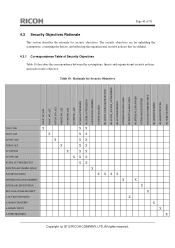
....NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE.INTERFACE.MANAGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT OE.ADMIN.TRAINED OE.ADMIN...ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright (c) 2012 RICOH COMPANY, LTD. Page 40 of Security Objectives Table 10 describes the correspondence between the assumptions, threats and organisational security policies, and each security objective...
....NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE.INTERFACE.MANAGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT OE.ADMIN.TRAINED OE.ADMIN...ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright (c) 2012 RICOH COMPANY, LTD. Page 40 of Security Objectives Table 10 describes the correspondence between the assumptions, threats and organisational security policies, and each security objective...
Security Target
Page 44
...LOGGED, the TOE creates and maintains a log of 91 P.AUDIT.LOGGING P.AUDIT.LOGGING is enforced by O.AUDIT.LOGGED, OE.AUDIT.REVIEWED, OE.AUDIT_STORAGE.PROTECTED and OE.AUDIT_ACCESS.AUTHORIZED. By OE.AUDIT_STORAGE.PROTECTED, if audit records are exported from the TOE to the guidance...the physical access by authorised persons. A.ACCESS.MANAGED A.ACCESS.MANAGED is protected from unauthorised access, deletion and alteration. Copyright (c) 2012 RICOH COMPANY, LTD. By OE.INTERFACE.MANAGED, the TOE constructs the IT environment that those records can be those communication data. P....
...LOGGED, the TOE creates and maintains a log of 91 P.AUDIT.LOGGING P.AUDIT.LOGGING is enforced by O.AUDIT.LOGGED, OE.AUDIT.REVIEWED, OE.AUDIT_STORAGE.PROTECTED and OE.AUDIT_ACCESS.AUTHORIZED. By OE.AUDIT_STORAGE.PROTECTED, if audit records are exported from the TOE to the guidance...the physical access by authorised persons. A.ACCESS.MANAGED A.ACCESS.MANAGED is protected from unauthorised access, deletion and alteration. Copyright (c) 2012 RICOH COMPANY, LTD. By OE.INTERFACE.MANAGED, the TOE constructs the IT environment that those records can be those communication data. P....
Security Target
Page 51
...events resulting from the audit records. FAU_SAR.2 Restricted audit review Hierarchical to: No other components. Dependencies: [FCS_CKM.2 Cryptographic key distribution, or FCS_COP.1 Cryptographic operation] FCS_CKM.4 Cryptographic key destruction Copyright (c) 2012 RICOH COMPANY, LTD. FAU_SAR.1.2 The TSF shall provide the audit... to: No other components. FAU_STG.1 Protected audit trail storage Hierarchical to : No other components. Dependencies: FAU_SAR.1 Audit review FAU_SAR.2.1 The TSF shall prohibit all of log items] from actions of identified users, the TSF shall be able to...
...events resulting from the audit records. FAU_SAR.2 Restricted audit review Hierarchical to: No other components. Dependencies: [FCS_CKM.2 Cryptographic key distribution, or FCS_COP.1 Cryptographic operation] FCS_CKM.4 Cryptographic key destruction Copyright (c) 2012 RICOH COMPANY, LTD. FAU_SAR.1.2 The TSF shall provide the audit... to: No other components. FAU_STG.1 Protected audit trail storage Hierarchical to : No other components. Dependencies: FAU_SAR.1 Audit review FAU_SAR.2.1 The TSF shall prohibit all of log items] from actions of identified users, the TSF shall be able to...
Security Target
Page 79
... expanded log items are recorded only when audit events occur and the audit log items shown in the audit log files to audit (audit log review). All rights reserved. FPT_STM.1 The date (year/month/day) and time (hour/minute/second) the TOE records for the audit log are ... (Login attempts from RC Gate are derived from RC Gate Communication interface Starting and releasing Lockout Table 29 Record of Management Function Copyright (c) 2012 RICOH COMPANY, LTD. The recorded audit log can be read the audit logs. FAU_SAR.1, FAU_SAR.2, and FAU_STG.1 The TOE displays the operation menu for...
... expanded log items are recorded only when audit events occur and the audit log items shown in the audit log files to audit (audit log review). All rights reserved. FPT_STM.1 The date (year/month/day) and time (hour/minute/second) the TOE records for the audit log are ... (Login attempts from RC Gate are derived from RC Gate Communication interface Starting and releasing Lockout Table 29 Record of Management Function Copyright (c) 2012 RICOH COMPANY, LTD. The recorded audit log can be read the audit logs. FAU_SAR.1, FAU_SAR.2, and FAU_STG.1 The TOE displays the operation menu for...