Security Target
Page 4
...Requirements 53 6.3 Security Requirements Rationale 54 6.3.1 Tracing...54 6.3.2 Justification of Traceability 55 6.3.3 Dependency Analysis...59 6.3.4 Security Assurance Requirements Rationale 61 7 TOE Summary Specification 62 7.1 TOE Security Function 62 7.1.1 SF.AUDIT Audit Function 63 7.1.1.1 Generation of Audit Logs 63 7.1.1.2 Reading Audit Logs ...65 7.1.1.3 Protection of Audit ...Function 65 7.1.2.1 User Identification and Authentication 66 7.1.2.2 Actions in Event of Identification and Authentication Failure 66 Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved.
...Requirements 53 6.3 Security Requirements Rationale 54 6.3.1 Tracing...54 6.3.2 Justification of Traceability 55 6.3.3 Dependency Analysis...59 6.3.4 Security Assurance Requirements Rationale 61 7 TOE Summary Specification 62 7.1 TOE Security Function 62 7.1.1 SF.AUDIT Audit Function 63 7.1.1.1 Generation of Audit Logs 63 7.1.1.2 Reading Audit Logs ...65 7.1.1.3 Protection of Audit ...Function 65 7.1.2.1 User Identification and Authentication 66 7.1.2.2 Actions in Event of Identification and Authentication Failure 66 Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved.
Security Target
Page 6
...roles of security attributes 45 Table 17: Characteristics of static attribute initialisation 46 Table 18: List of TSF data management...46 Table 19: List of specifications of Management Functions 48 Table 20: Services requiring trusted paths...52 Table 21: TOE security assurance requirements (EAL3 53 Table 22: Relationship between security ... 32: Administrators authorised to specify machine control data 72 Table 33: List of encryption operations on data stored on the HDD 73 Table 34: Specific terms used in this ST...76 Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved.
...roles of security attributes 45 Table 17: Characteristics of static attribute initialisation 46 Table 18: List of TSF data management...46 Table 19: List of specifications of Management Functions 48 Table 20: Services requiring trusted paths...52 Table 21: TOE security assurance requirements (EAL3 53 Table 22: Relationship between security ... 32: Administrators authorised to specify machine control data 72 Table 33: List of encryption operations on data stored on the HDD 73 Table 34: Specific terms used in this ST...76 Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved.
Security Target
Page 34
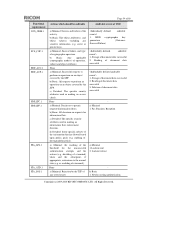
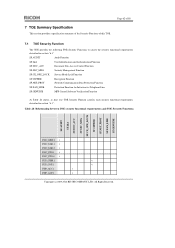
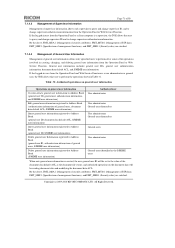
... an object covered by the SFP. Storage of downgraded material). Reading of the activity. Newly creating authentication Copyright (c) 2009,2010 RICOH COMPANY, LTD. Page 34 of 80 Functional requirements FCS_CKM.1 FCS_COP.1 FDP_ACC.1 FDP_ACF.1 FDP_IFC.1 FDP_IFF.1 FIA_AFL.1 FIA_ATD.1 FIA_SOS.1 ...flowed based upon policy goals (e.g. b) Basic: All decisions on an object covered by the TSF of a terminal). d) Detailed: Some specific subsets of operation, subject and object attributes. re -enabling of any sensitive information (e.g. Fax Function: Reception a) Minimal 1. None a) Minimal...
... an object covered by the SFP. Storage of downgraded material). Reading of the activity. Newly creating authentication Copyright (c) 2009,2010 RICOH COMPANY, LTD. Page 34 of 80 Functional requirements FCS_CKM.1 FCS_COP.1 FDP_ACC.1 FDP_ACF.1 FDP_IFC.1 FDP_IFF.1 FIA_AFL.1 FIA_ATD.1 FIA_SOS.1 ...flowed based upon policy goals (e.g. b) Basic: All decisions on an object covered by the TSF of a terminal). d) Detailed: Some specific subsets of operation, subject and object attributes. re -enabling of any sensitive information (e.g. Fax Function: Reception a) Minimal 1. None a) Minimal...
Security Target
Page 45
... applicable document data FMT_MSA.3 Static attribute initialisation Hierarchical to enforce the SFP. Administrators - Copyright (c) 2009,2010 RICOH COMPANY, LTD. User administrator - Page 45 of 80 FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of Management Functions FMT_MSA.1.1 The TSF shall enforce the [assignment: MFP access control SFP] to restrict the...
... applicable document data FMT_MSA.3 Static attribute initialisation Hierarchical to enforce the SFP. Administrators - Copyright (c) 2009,2010 RICOH COMPANY, LTD. User administrator - Page 45 of 80 FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of Management Functions FMT_MSA.1.1 The TSF shall enforce the [assignment: MFP access control SFP] to restrict the...
Security Target
Page 46
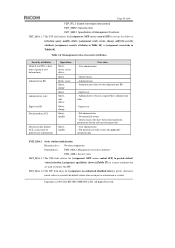
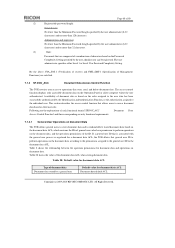
...create]]the [assignment: list of TSF data management in Table 18 to : No other components. All Rights Reserved. Dependencies: FMT_SMR.1 Security roles FMT_SMF.1 Specification of Management Functions FMT_MTD.1.1 The TSF shall restrict the ability to[selection: query, modify, delete, [assignment: register, change , delete Change Supervisor authentication ...information Supervisor Supervisor Applicable administrator of administrator authentication information Machine administrator Machine administrator Machine administrator Machine administrator Copyright (c) 2009,2010 RICOH COMPANY, LTD.
...create]]the [assignment: list of TSF data management in Table 18 to : No other components. All Rights Reserved. Dependencies: FMT_SMR.1 Security roles FMT_SMF.1 Specification of Management Functions FMT_MTD.1.1 The TSF shall restrict the ability to[selection: query, modify, delete, [assignment: register, change , delete Change Supervisor authentication ...information Supervisor Supervisor Applicable administrator of administrator authentication information Machine administrator Machine administrator Machine administrator Machine administrator Copyright (c) 2009,2010 RICOH COMPANY, LTD.
Security Target
Page 47
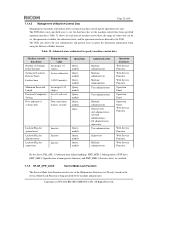
...Rights Reserved. FMT_SMF.1.1 The TSF shall be capable of performing the following Management Functions: [assignment: list of specifications of Management Function Hierarchical to Folder Query, modify Query, modify Query, modify Query, newly create, delete, change...User administrator Applicable general users of S/MIME user information General users User administrator, General users FMT_SMF.1 Specification of Management Functions described in Table19 Copyright (c) 2009,2010 RICOH COMPANY, LTD. second) TSF data Operations Que ry Minimum Password Length Password Complexity Setting HDD ...
...Rights Reserved. FMT_SMF.1.1 The TSF shall be capable of performing the following Management Functions: [assignment: list of specifications of Management Function Hierarchical to Folder Query, modify Query, modify Query, modify Query, newly create, delete, change...User administrator Applicable general users of S/MIME user information General users User administrator, General users FMT_SMF.1 Specification of Management Functions described in Table19 Copyright (c) 2009,2010 RICOH COMPANY, LTD. second) TSF data Operations Que ry Minimum Password Length Password Complexity Setting HDD ...
Security Target
Page 48
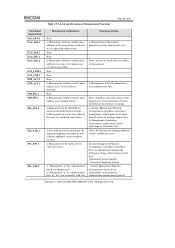
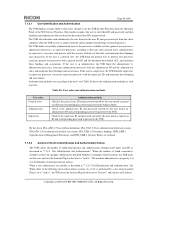
a) Management of general Copyright (c) 2009,2010 RICOH COMPANY, LTD. None: Actions are no interfaces to change. a) Management of the authentication data by machine administrator. Security Management Function (...access right to make explicit access based decisions. None a) Managing the attributes used to make explicit access or denial based decisions. Table 19: List of specifications of Management Functions Page 48 of 80 Functional requirements FAU_GEN.1 FAU_SAR.1 FAU_SAR.2 FAU_STG.1 FAU_STG.4 FCS_CKM.1 FCS_COP.1 FDP_ACC.1 FDP_ACF.1 FDP_IFC.1 FDP_IFF.1 FIA_AFL.1 ...
a) Management of general Copyright (c) 2009,2010 RICOH COMPANY, LTD. None: Actions are no interfaces to change. a) Management of the authentication data by machine administrator. Security Management Function (...access right to make explicit access based decisions. None a) Managing the attributes used to make explicit access or denial based decisions. Table 19: List of specifications of Management Functions Page 48 of 80 Functional requirements FAU_GEN.1 FAU_SAR.1 FAU_SAR.2 FAU_STG.1 FAU_STG.4 FCS_CKM.1 FCS_COP.1 FDP_ACC.1 FDP_ACF.1 FDP_IFC.1 FDP_IFF.1 FIA_AFL.1 ...
Security Target
Page 53
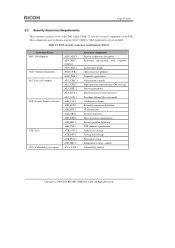
...ASE_OBJ.2 ASE_REQ.2 ASE_SPD.1 ASE_TSS.1 ATE_COV.2 ATE_DPT.1 ATE_FUN.1 ATE_IND.2 AVA_VAN.2 Assurance components Security architecture description Functional specification with complete Architectural design Operational user guidance Preparative procedures Authorisation controls Implementation representation CM coverage Delivery procedures Identification of ...EAL3). Other requirements are not included. All Rights Reserved. sample Vulnerability analysis Copyright (c) 2009,2010 RICOH COMPANY, LTD. Table 21 lists the assurance components of coverage Testing: basic design Functional testing ...
...ASE_OBJ.2 ASE_REQ.2 ASE_SPD.1 ASE_TSS.1 ATE_COV.2 ATE_DPT.1 ATE_FUN.1 ATE_IND.2 AVA_VAN.2 Assurance components Security architecture description Functional specification with complete Architectural design Operational user guidance Preparative procedures Authorisation controls Implementation representation CM coverage Delivery procedures Identification of ...EAL3). Other requirements are not included. All Rights Reserved. sample Vulnerability analysis Copyright (c) 2009,2010 RICOH COMPANY, LTD. Table 21 lists the assurance components of coverage Testing: basic design Functional testing ...
Security Target
Page 55
... time, type, subject identity, and outcome of Security Functions should have the oldest time stamp. Copyright (c) 2009,2010 RICOH COMPANY, LTD. b) Provide Audit Function To fulfil O.AUDIT, access to audit logs should be restricted to the machine...v v v v v v v v v 6.3.2 Justification of Traceability This section describes how the TOE security objectives are included to fulfil the O.AUDIT specification. For this, FAU_STG.4 protects audit logs from unauthorised deletion and prevents unauthorised tampering. a ) Record audit logs To fulfil O.AUDIT, the performance of each event...
... time, type, subject identity, and outcome of Security Functions should have the oldest time stamp. Copyright (c) 2009,2010 RICOH COMPANY, LTD. b) Provide Audit Function To fulfil O.AUDIT, access to audit logs should be restricted to the machine...v v v v v v v v v 6.3.2 Justification of Traceability This section describes how the TOE security objectives are included to fulfil the O.AUDIT specification. For this, FAU_STG.4 protects audit logs from unauthorised deletion and prevents unauthorised tampering. a ) Record audit logs To fulfil O.AUDIT, the performance of each event...
Security Target
Page 56
... process is also performed by displaying masking characters (*: asterisks or : bullets) in place of a document, Copyright (c) 2009,2010 RICOH COMPANY, LTD. For this will help identify security breaches. O.DOC_ACC Control of the functions they use any TOE Security Functions shall ...be performed prior to allowing user access to fulfil the O.DOC_ACC specification. b) Allow successfully identified and auth enticated users to use of access to protected assets Following are included to document data and ...
... process is also performed by displaying masking characters (*: asterisks or : bullets) in place of a document, Copyright (c) 2009,2010 RICOH COMPANY, LTD. For this will help identify security breaches. O.DOC_ACC Control of the functions they use any TOE Security Functions shall ...be performed prior to allowing user access to fulfil the O.DOC_ACC specification. b) Allow successfully identified and auth enticated users to use of access to protected assets Following are included to document data and ...
Security Target
Page 57
...audit logs. O. For this , FMT_MTD.1 allows: - To fulfil O.MANAGE, access to TSF data shall be Copyright (c) 2009,2010 RICOH COMPANY, LTD. general users to specified users. the machine administrator to folders; - the user administrator and general users to query S/MIME ..., document file owners, and general users with full control operation permission for the document data to fulfil the O.MANAGE specification. MANAGE Security management Following are the rationale behind the functional requirements corresponding to O.MANAGE inTable 22, and these requirements are...
...audit logs. O. For this , FMT_MTD.1 allows: - To fulfil O.MANAGE, access to TSF data shall be Copyright (c) 2009,2010 RICOH COMPANY, LTD. general users to specified users. the machine administrator to folders; - the user administrator and general users to query S/MIME ..., document file owners, and general users with full control operation permission for the document data to fulfil the O.MANAGE specification. MANAGE Security management Following are the rationale behind the functional requirements corresponding to O.MANAGE inTable 22, and these requirements are...
Security Target
Page 58
... the rationale behind the functional requirements corresponding to O.MEM.PROTECT in Table 22, and these requirements are included to fulfil the O.MEM.PROTECT specification. O.NET.PROTECT Protection of the IcCtlr where encryption is read from leakage, and attempts at tampering. O.MEM.PROTECT Prevention of disclosure of ... assets on the HDD and decrypts it when it shall also be protected from the HDD using the TOE. Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. To fulfil O.MANAGE, authorised users shall be maintained, since the use of 256 bits with the ...
... the rationale behind the functional requirements corresponding to O.MEM.PROTECT in Table 22, and these requirements are included to fulfil the O.MEM.PROTECT specification. O.NET.PROTECT Protection of the IcCtlr where encryption is read from leakage, and attempts at tampering. O.MEM.PROTECT Prevention of disclosure of ... assets on the HDD and decrypts it when it shall also be protected from the HDD using the TOE. Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. To fulfil O.MANAGE, authorised users shall be maintained, since the use of 256 bits with the ...
Security Target
Page 59
...MFP Control Software, which is installed in ST None None None None None FCS_CKM.4 FCS_CKM.4 None None Copyright (c) 2009,2010 RICOH COMPANY, LTD. For this, FDP_IFC.1 and FDP_IFF.1 allow fax data to pass from the fax process on the Fax Unit...integrity Following are the rationale behind the functional requirements corresponding to O.LINE.PROTECTTable 22, and these requirements are included to fulfil the O.GENUINE specification. All Rights Reserved. To fulfil O.LINE_PROTECT, unauthorised access by CC FPT_STM.1 FAU_GEN.1 FAU_SAR.1 FAU_GEN.1 FAU_STG.1 [FCS_CKM.2 or FCS_COP.1] ...
...MFP Control Software, which is installed in ST None None None None None FCS_CKM.4 FCS_CKM.4 None None Copyright (c) 2009,2010 RICOH COMPANY, LTD. For this, FDP_IFC.1 and FDP_IFF.1 allow fax data to pass from the fax process on the Fax Unit...integrity Following are the rationale behind the functional requirements corresponding to O.LINE.PROTECTTable 22, and these requirements are included to fulfil the O.GENUINE specification. All Rights Reserved. To fulfil O.LINE_PROTECT, unauthorised access by CC FPT_STM.1 FAU_GEN.1 FAU_SAR.1 FAU_GEN.1 FAU_STG.1 [FCS_CKM.2 or FCS_COP.1] ...
Security Target
Page 62
All Rights Reserved. Page 62 of 80 7 TOE Summary Specification This section provides a specification summary of the Security Functions of this TOE. 7.1 TOE Security Function The TOE provides the following TOE Security Functions to satisfy the security functional requirements ....DOC_ACC SF.SEC_MNG SF.CE_OPE_LOCK SF.CIPHER SF.NET_PROT SF.FAX_LINE SF.GENUINE FAU_GEN.1 v FAU_SAR.1 v FAU_SAR.2 v FAU_STG.1 v FAU_STG.4 v FCS_CKM.1 v FCS_COP.1 v FDP_ACC.1 v FDP_ACF.1 v Copyright (c) 2009,2010 RICOH COMPANY, LTD.
All Rights Reserved. Page 62 of 80 7 TOE Summary Specification This section provides a specification summary of the Security Functions of this TOE. 7.1 TOE Security Function The TOE provides the following TOE Security Functions to satisfy the security functional requirements ....DOC_ACC SF.SEC_MNG SF.CE_OPE_LOCK SF.CIPHER SF.NET_PROT SF.FAX_LINE SF.GENUINE FAU_GEN.1 v FAU_SAR.1 v FAU_SAR.2 v FAU_STG.1 v FAU_STG.4 v FCS_CKM.1 v FCS_COP.1 v FDP_ACC.1 v FDP_ACF.1 v Copyright (c) 2009,2010 RICOH COMPANY, LTD.
Security Target
Page 66
...to use the TOE Security Functions from the client computer for printing or transmitting faxes. Copyright (c) 2009,2010 RICOH COMPANY, LTD. If the user is a supervisor, the TOE binds the supervisor to supervisor processes, associates ...as described in "7.1.2.1 User Identification and Authentication", the When either of Attempts before any action), FIA_USB.1 (User-subject binding), FMT_SMF.1 (Specification of Management Functions), and FMT_SMR.1 (Security Roles) are satisfied. 7.1.2.2 Actions in "7.1.2.1 User Identification and Authentication". Check if the supervisor ...
...to use the TOE Security Functions from the client computer for printing or transmitting faxes. Copyright (c) 2009,2010 RICOH COMPANY, LTD. If the user is a supervisor, the TOE binds the supervisor to supervisor processes, associates ...as described in "7.1.2.1 User Identification and Authentication", the When either of Attempts before any action), FIA_USB.1 (User-subject binding), FMT_SMF.1 (Specification of Management Functions), and FMT_SMR.1 (Security Roles) are satisfied. 7.1.2.2 Actions in "7.1.2.1 User Identification and Authentication". Check if the supervisor ...
Security Target
Page 67
...supervisor. In this case, lockout release must be performed by manual lockout release. From the above , FIA_AFL.1 (Authentication failure handling) and FMT_SMF.1 (Specification of Management Functions) are satisfied. 7.1.2.3 Password Feedback Area Protection The TOE displays a string of masking characters (*: asterisks or : bullets) in (1). This...[A -Z] (26 letters) Lower-case letters: [a -z] (26 letters) Numbers: [0-9] (10 digits) Symbols: SP (space 33 symbols) Copyright (c) 2009,2010 RICOH COMPANY, LTD. The machine administrator specifies the lockout time between 1 and 9999 minutes.
...supervisor. In this case, lockout release must be performed by manual lockout release. From the above , FIA_AFL.1 (Authentication failure handling) and FMT_SMF.1 (Specification of Management Functions) are satisfied. 7.1.2.3 Password Feedback Area Protection The TOE displays a string of masking characters (*: asterisks or : bullets) in (1). This...[A -Z] (26 letters) Lower-case letters: [a -z] (26 letters) Numbers: [0-9] (10 digits) Symbols: SP (space 33 symbols) Copyright (c) 2009,2010 RICOH COMPANY, LTD. The machine administrator specifies the lockout time between 1 and 9999 minutes.
Security Target
Page 68
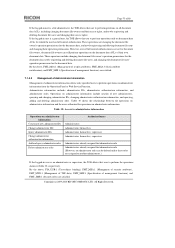
... administrator (8-32 characters) and no more than 128 characters. By the above, FIA_SOS.1 (Verification of secrets) and FMT_SMF.1 (Specification of Management Functions) are composed of a combination of characters based on the Password Complexity Setting specified by the Identification andAuthentication Function,... Password Length specified by a general user Default value for document data ACL Document data default ACL Copyright (c) 2009,2010 RICOH COMPANY, LTD. Administrators and supervisor No fewer than the Minimum Password Length specified by the user administrator (8-32 characters) ...
... administrator (8-32 characters) and no more than 128 characters. By the above, FIA_SOS.1 (Verification of secrets) and FMT_SMF.1 (Specification of Management Functions) are composed of a combination of characters based on the Password Complexity Setting specified by the Identification andAuthentication Function,... Password Length specified by a general user Default value for document data ACL Document data default ACL Copyright (c) 2009,2010 RICOH COMPANY, LTD. Administrators and supervisor No fewer than the Minimum Password Length specified by the user administrator (8-32 characters) ...
Security Target
Page 70
Copyright (c) 2009,2010 RICOH COMPANY, LTD. However, even if full control authorisation is not set for document file owners, document file owners can be deleted unless these roles... information includes administrator IDs, administrator authentication information, and administrator roles. By the above , FMT_MSA.1 (Management of security attributes), FMT_MSA.3 (Static attribute initialisation), and FMT_SMF.1 (Specification of management functions) are assigned to another administrator.) If the logged-in user is an administrator or supervisor, the TOE allows that user to perform...
Copyright (c) 2009,2010 RICOH COMPANY, LTD. However, even if full control authorisation is not set for document file owners, document file owners can be deleted unless these roles... information includes administrator IDs, administrator authentication information, and administrator roles. By the above , FMT_MSA.1 (Management of security attributes), FMT_MSA.3 (Static attribute initialisation), and FMT_SMF.1 (Specification of management functions) are assigned to another administrator.) If the logged-in user is an administrator or supervisor, the TOE allows that user to perform...
Security Target
Page 71
... modifying the document data ACL. By the above , FMT_MSA.1 (Management of security attributes), FMT_MTD.1 (Management of TSF data), FMT_SMF.1 (Specification of management functions), and FMT_SMR.1 (Security roles) are satisfied. 7.1.4.4 Management of General User Information Management of general user information allows only...in creating, changing, and deleting general user information from the Operation Panel or Web Service Function. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Page 71 of 80 7.1.4.3 Management of Supervisor Information Management of the document data default ACL as the ...
... modifying the document data ACL. By the above , FMT_MSA.1 (Management of security attributes), FMT_MTD.1 (Management of TSF data), FMT_SMF.1 (Specification of management functions), and FMT_SMR.1 (Security roles) are satisfied. 7.1.4.4 Management of General User Information Management of general user information allows only...in creating, changing, and deleting general user information from the Operation Panel or Web Service Function. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Page 71 of 80 7.1.4.3 Management of Supervisor Information Management of the document data default ACL as the ...
Security Target
Page 72
...Web Service Function Web Service Function By the above, FIA_AFL.1 (Authentication failure handling), FMT_MTD.1 (Management of TSF data), FMT_SMF.1 (Specification of management function), and FMT_SMR.1 (Security roles) are satisfied. 7.1.5 SF.CE_OPE_LOCK Service Mode Lock Function The Service Mode Lock Function ... setter, and the operation interfaces allowed by the TOE. Table 32: Administrators authorised to Folder function. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Page 72 of 80 7.1.4.5 Management of Machine Control Data Management of machine control data allows setting of machine ...
...Web Service Function Web Service Function By the above, FIA_AFL.1 (Authentication failure handling), FMT_MTD.1 (Management of TSF data), FMT_SMF.1 (Specification of management function), and FMT_SMR.1 (Security roles) are satisfied. 7.1.5 SF.CE_OPE_LOCK Service Mode Lock Function The Service Mode Lock Function ... setter, and the operation interfaces allowed by the TOE. Table 32: Administrators authorised to Folder function. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Page 72 of 80 7.1.4.5 Management of Machine Control Data Management of machine control data allows setting of machine ...