User Guide
Page 10
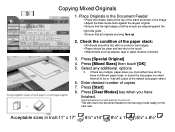
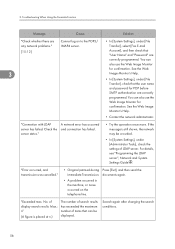
... curled or bent edges, Paper should be output on the same size. Acceptable sizes in the image Adjust the Side Guide flush against the right side guide . Ensure that the right edges of copies 7. Place Originals in different paper trays, or select the size paper you want ...4. If there are aligned against the largest original. Ensure that all be clean and feel dry to normal copy mode ready for the next user. Press [Clear Modes] key when you must be or they will return the document feeder to the touch, Attachments such as shown in...
... curled or bent edges, Paper should be output on the same size. Acceptable sizes in the image Adjust the Side Guide flush against the right side guide . Ensure that the right edges of copies 7. Place Originals in different paper trays, or select the size paper you want ...4. If there are aligned against the largest original. Ensure that all be clean and feel dry to normal copy mode ready for the next user. Press [Clear Modes] key when you must be or they will return the document feeder to the touch, Attachments such as shown in...
Operating Instructions
Page 8
...panel, preparation procedures for explanations on how to register information in a network environment, and use this machine. Also explains how to change User Tools settings and how to place originals. For enhanced security, we recommend that you first make the following settings: • Install the... machine, be installed in order to a network, configure and operate the machine in the Address Book. Network and System Settings Guide Explains how to connect the machine to view the html manuals. Printer Reference Explains Printer functions and operations. Manuals for This Machine...
...panel, preparation procedures for explanations on how to register information in a network environment, and use this machine. Also explains how to change User Tools settings and how to place originals. For enhanced security, we recommend that you first make the following settings: • Install the... machine, be installed in order to a network, configure and operate the machine in the Address Book. Network and System Settings Guide Explains how to connect the machine to view the html manuals. Printer Reference Explains Printer functions and operations. Manuals for This Machine...
Operating Instructions
Page 9
... the enhanced security functions, or user and administrator authentication. Other manuals • UNIX Supplement • Quick Reference Copy Guide • Quick Reference Printer Guide • Quick Reference Fax Guide • Quick Reference Scanner Guide • Manuals for DeskTopBinder Lite • DeskTopBinder Lite Setup Guide • DeskTopBinder Introduction Guide • Auto Document Link Guide • Manuals provided are referred...
... the enhanced security functions, or user and administrator authentication. Other manuals • UNIX Supplement • Quick Reference Copy Guide • Quick Reference Printer Guide • Quick Reference Fax Guide • Quick Reference Scanner Guide • Manuals for DeskTopBinder Lite • DeskTopBinder Lite Setup Guide • DeskTopBinder Introduction Guide • Auto Document Link Guide • Manuals provided are referred...
Operating Instructions
Page 16
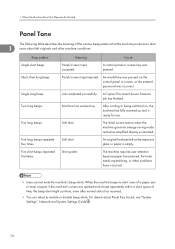
...The initial screen returns when the machine goes into energy-saving mode and when simplified display is empty. Soft alert. The machine requires user attention because paper has jammed, the toner needs replenishing, or other machine conditions. For details about left on the exposure glass or ..., the beep alert might continue, even after normal status has resumed. • You can select to alert 1 users about Panel Key Sound, see "System Settings", Network and System Settings Guide . 14 Strong alert. A control panel or screen key was incorrect. Single long beep. A Copier/Document Server ...
...The initial screen returns when the machine goes into energy-saving mode and when simplified display is empty. Soft alert. The machine requires user attention because paper has jammed, the toner needs replenishing, or other machine conditions. For details about left on the exposure glass or ..., the beep alert might continue, even after normal status has resumed. • You can select to alert 1 users about Panel Key Sound, see "System Settings", Network and System Settings Guide . 14 Strong alert. A control panel or screen key was incorrect. Single long beep. A Copier/Document Server ...
Operating Instructions
Page 43
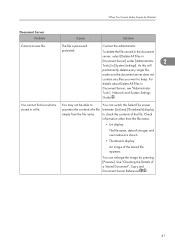
Check information other than the file name. • List display The file name, data of storage, and user name are shown. • Thumbnails display An image of a Stored Document", Copy and Document Server Reference . 41 The file is stored in [System Settings]. To .... See "Checking the Details of the stored file appears. For details about Delete All Files in Document Server, see "Administrator Tools", Network and System Settings Guide . You may not be able to ascertain the contents of the file. Contact the administrator.
Check information other than the file name. • List display The file name, data of storage, and user name are shown. • Thumbnails display An image of a Stored Document", Copy and Document Server Reference . 41 The file is stored in [System Settings]. To .... See "Checking the Details of the stored file appears. For details about Delete All Files in Document Server, see "Administrator Tools", Network and System Settings Guide . You may not be able to ascertain the contents of the file. Contact the administrator.
Operating Instructions
Page 58
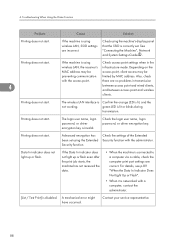
Transfer], select [Fax E-mail [15-12] Account], and then check that the user name and password for POP before SMTP authentication are correctly programmed. Check the server status." "Error occurred, and transmission was cancelled." • Original...that can be crowded. • In [System Settings], under [File Transfer], check that "User Name" and "Password" are Cannot log on the telephone line. For details, see "Programming the LDAP server", Network and System Settings Guide . No. Search again after changing the search conditions. 56 See the Web 3 Image Monitor's...
Transfer], select [Fax E-mail [15-12] Account], and then check that the user name and password for POP before SMTP authentication are correctly programmed. Check the server status." "Error occurred, and transmission was cancelled." • Original...that can be crowded. • In [System Settings], under [File Transfer], check that "User Name" and "Password" are Cannot log on the telephone line. For details, see "Programming the LDAP server", Network and System Settings Guide . No. Search again after changing the search conditions. 56 See the Web 3 Image Monitor's...
Operating Instructions
Page 59
... has occurred and connection has failed. • Try the operation once more. For details, see "Programming the LDAP server", Network and System 3 Settings Guide . appears, press [Stop]. "Put original back, check it Original jammed during and press the Start key." Memory Transmission. Tray." Check the settings." ... other tray is a problem with facsimile. Record the code number shown on the display. 57 name and the password for the user and connection has failed. "Original is being scanned by fax, cancel the job in progress. Are you sure you want to continue...
... has occurred and connection has failed. • Try the operation once more. For details, see "Programming the LDAP server", Network and System 3 Settings Guide . appears, press [Stop]. "Put original back, check it Original jammed during and press the Start key." Memory Transmission. Tray." Check the settings." ... other tray is a problem with facsimile. Record the code number shown on the display. 57 name and the password for the user and connection has failed. "Original is being scanned by fax, cancel the job in progress. Are you sure you want to continue...
Operating Instructions
Page 90
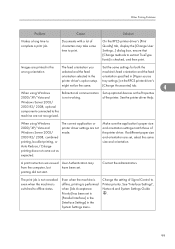
See "Connecting the Machine", Network and System Settings Guide . green LED is disabled. A mechanical error might have occurred. Contact your service representative. 88 For details, see p.89 "When the Data In Indicator Does Not ... problems in the infrastructure mode. Also, check there are incorrect. Check the settings of the Extended Security function with the access point. Check the login user name, login password, or driver encryption key. If the Data In indicator does not light up or flash. 4. Troubleshooting When Using the Printer Function Problem...
See "Connecting the Machine", Network and System Settings Guide . green LED is disabled. A mechanical error might have occurred. Contact your service representative. 88 For details, see p.89 "When the Data In Indicator Does Not ... problems in the infrastructure mode. Also, check there are incorrect. Check the settings of the Extended Security function with the access point. Check the login user name, login password, or driver encryption key. If the Data In indicator does not light up or flash. 4. Troubleshooting When Using the Printer Function Problem...
Operating Instructions
Page 101
...Settings menu. Even when the machine is offline, printing is not working. On the RPCS printer driver's [Print Quality] tab, display the [Change User Settings...] dialog box, ensure that [Change methods to print. of the printer driver. Make sure the application's paper size and orientation settings match ...may from the computer, but have been set , select the same size and orientation. See "Interface Settings", Network and System Settings Guide . 99 Other Printing Problems Problem Cause Solution It takes a long time to Printer priority. Images are not recognized.
...Settings menu. Even when the machine is offline, printing is not working. On the RPCS printer driver's [Print Quality] tab, display the [Change User Settings...] dialog box, ensure that [Change methods to print. of the printer driver. Make sure the application's paper size and orientation settings match ...may from the computer, but have been set , select the same size and orientation. See "Interface Settings", Network and System Settings Guide . 99 Other Printing Problems Problem Cause Solution It takes a long time to Printer priority. Images are not recognized.
Operating Instructions
Page 112
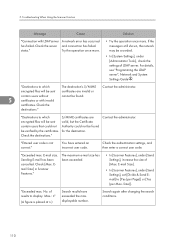
... settings of LDAP server. of [Max. Max.: n" (A figure is not correct." For details, see "Programming the LDAP server", Network and System Settings Guide . encrypted files will be sent contain users that could not be verified by the certificates. Contact the administrator. You have exceeded the max. Sending E-mail has been cancelled. Check...
... settings of LDAP server. of [Max. Max.: n" (A figure is not correct." For details, see "Programming the LDAP server", Network and System Settings Guide . encrypted files will be sent contain users that could not be verified by the certificates. Contact the administrator. You have exceeded the max. Sending E-mail has been cancelled. Check...
Operating Instructions
Page 115
...the device." Try one of LDAP server. Because there is not enough free hard disk space in the machine for LDAP Authentication. The user name and password differ from those set for storing in the media slot. 113 could not be scanned. "Memory is full. Select whether... Because of the pages could be disk space, the first page deleted." Specify whether to see "Programming the LDAP server", Network and System Settings Guide . "Memory is full. Because there is not enough free hard disk space in the machine for a while, and then retry the scan operation...
...the device." Try one of LDAP server. Because there is not enough free hard disk space in the machine for LDAP Authentication. The user name and password differ from those set for storing in the media slot. 113 could not be scanned. "Memory is full. Select whether... Because of the pages could be disk space, the first page deleted." Specify whether to see "Programming the LDAP server", Network and System Settings Guide . "Memory is full. Because there is not enough free hard disk space in the machine for a while, and then retry the scan operation...
Design Guide
Page 3
Print Controller Design Guide for Information Security 1-9-3 Capture Settings 41 1-9-4 Security Considerations 42 1-9-5 Captured Documents and Log Data 42 1-10 Additional Methods for Each Individual User 45 2-1-7 Job/Access Log Data Collection 45 2-1-8 Print Backup ...45 2-2 Printer ...47 2-2-1 Overview of Printer Operations 47 2-2-2 Data Flow...47 2-2-3 Data Security Considerations 51 2-3 Scanner (...
Print Controller Design Guide for Information Security 1-9-3 Capture Settings 41 1-9-4 Security Considerations 42 1-9-5 Captured Documents and Log Data 42 1-10 Additional Methods for Each Individual User 45 2-1-7 Job/Access Log Data Collection 45 2-1-8 Print Backup ...45 2-2 Printer ...47 2-2-1 Overview of Printer Operations 47 2-2-2 Data Flow...47 2-2-3 Data Security Considerations 51 2-3 Scanner (...
Design Guide
Page 6
...RICOH SP C820DN SP C821DN Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 AFICIO MP 6001 MP 6001 SP MP 7001 MP 7001 SP MP 8001 MP 8001 SP MP 9001 MP 9001 SP AFICIO... SP4210N SAVIN CLP340D CLP350D Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 9060 9060sp 9070 9070sp 9080 9080sp 9090 9090sp MLP37N Note: Some of the hardware (e.g. Print Controller Design Guide... to as Ricoh), as well as the "MFP" and "LP", respectively), which were designed and developed by the end user's machine. ...
...RICOH SP C820DN SP C821DN Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 AFICIO MP 6001 MP 6001 SP MP 7001 MP 7001 SP MP 8001 MP 8001 SP MP 9001 MP 9001 SP AFICIO... SP4210N SAVIN CLP340D CLP350D Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 9060 9060sp 9070 9070sp 9080 9080sp 9090 9090sp MLP37N Note: Some of the hardware (e.g. Print Controller Design Guide... to as Ricoh), as well as the "MFP" and "LP", respectively), which were designed and developed by the end user's machine. ...
Design Guide
Page 12
... the MFP/LP's access logs (e.g. Page 12 of the LCD screen as well as the charge-related processing (e.g. Print Controller Design Guide for access control, is handled via the host I /F. Receives image data through the host interface, which reads the original and then... for Information Security SCS (System Control Service) SRM (System Resource Manager) DCS (Delivery Control Service) MIRS (Machine Information Report Service) UCS (User Control Service) CCS (Certification Control Service) NRS (New Remote Service) LCS (Log Control Service) DESS (Data Encryption Security Service) Manages the...
... the MFP/LP's access logs (e.g. Page 12 of the LCD screen as well as the charge-related processing (e.g. Print Controller Design Guide for access control, is handled via the host I /F. Receives image data through the host interface, which reads the original and then... for Information Security SCS (System Control Service) SRM (System Resource Manager) DCS (Delivery Control Service) MIRS (Machine Information Report Service) UCS (User Control Service) CCS (Certification Control Service) NRS (New Remote Service) LCS (Log Control Service) DESS (Data Encryption Security Service) Manages the...
Design Guide
Page 13
SDK: Applications provided by Ricoh. Note: This is only available on the MFP/LP. GWWS also acts...TCP/IP command flow between the GW-API and external controller connected to the MFP HDD. Print Controller Design Guide for Information Security Netfile (GWWS) WebSys WebDocBox SDK/VAS EAC As a server, GWWS provides some of the... printing, deleting) via the Gigabit Ethernet-compatible network I/F. This includes the ability to view and make changes to user information and machine configuration settings, as well as store Printer documents to the MFP via a Web interface. In addition...
SDK: Applications provided by Ricoh. Note: This is only available on the MFP/LP. GWWS also acts...TCP/IP command flow between the GW-API and external controller connected to the MFP HDD. Print Controller Design Guide for Information Security Netfile (GWWS) WebSys WebDocBox SDK/VAS EAC As a server, GWWS provides some of the... printing, deleting) via the Gigabit Ethernet-compatible network I/F. This includes the ability to view and make changes to user information and machine configuration settings, as well as store Printer documents to the MFP via a Web interface. In addition...
Design Guide
Page 14
...UNIX operating system as the Address Book data stored in the HDD/flash ROM and User Code data stored in the Image Memory is managed by specified machine function(s). User data, such as independent processes (data/program modules). Access to this pre-determined set...and internal programs from an outside this data from Illegal Access via an external I /F for connection of peripheral devices (e.g. Print Controller Design Guide for Information Security 1-3 Data Security 1-3-1 External I/F The MFP/LP is equipped with the following external interfaces: • Serial I/F for ...
...UNIX operating system as the Address Book data stored in the HDD/flash ROM and User Code data stored in the Image Memory is managed by specified machine function(s). User data, such as independent processes (data/program modules). Access to this pre-determined set...and internal programs from an outside this data from Illegal Access via an external I /F for connection of peripheral devices (e.g. Print Controller Design Guide for Information Security 1-3 Data Security 1-3-1 External I/F The MFP/LP is equipped with the following external interfaces: • Serial I/F for ...
Design Guide
Page 15
... the MFP/LP has recognized the peripheral device. The internal arrangement is possible to disable each user, in tandem with the access control settings for @Remote operations is performed using Ricoh-unique protocols. It is possible to utilize such devices in which case the device and MFP ... the MFP, the external controller is then connected to the @Remote Center, or to internal programs or data. 5. Print Controller Design Guide for its peripherals is conducted via the network to pre-determined commands and data, and only take place after it has successfully cleared the...
... the MFP/LP has recognized the peripheral device. The internal arrangement is possible to disable each user, in tandem with the access control settings for @Remote operations is performed using Ricoh-unique protocols. It is possible to utilize such devices in which case the device and MFP ... the MFP, the external controller is then connected to the @Remote Center, or to internal programs or data. 5. Print Controller Design Guide for its peripherals is conducted via the network to pre-determined commands and data, and only take place after it has successfully cleared the...
Design Guide
Page 18
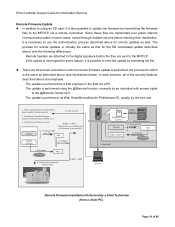
... and new firmware is not installed MD1 Digital signature 7. Download Client PC Remote Firmware Installation Performed by the end user 1. Since these files are employed. Files are attached to the digital signature before reaching their destination, it is also possible... digital signature Program Ricoh license server 1. There are sent to the MFP/LP. The process for remote updates is virtually the same as described above (see illustrations below). Generate MD1 using SHA-1 MD Digital signature 2. Print Controller Design Guide for Information Security Remote...
... and new firmware is not installed MD1 Digital signature 7. Download Client PC Remote Firmware Installation Performed by the end user 1. Since these files are employed. Files are attached to the digital signature before reaching their destination, it is also possible... digital signature Program Ricoh license server 1. There are sent to the MFP/LP. The process for remote updates is virtually the same as described above (see illustrations below). Generate MD1 using SHA-1 MD Digital signature 2. Print Controller Design Guide for Information Security Remote...
Design Guide
Page 19
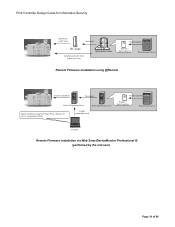
Print Controller Design Guide for Information Security Installation via RC-Gate Download RC-Gate Installation directly from @Remote Center @Remote Center Digital signature Program + digital signature Ricoh Licenese Server Remote Firmware Installation using @Remote Remote installation Download Ridoc IO OperationServer Ricoh distribution server Update performed using Web Smart Device Monitor V2 (device management utility...
Print Controller Design Guide for Information Security Installation via RC-Gate Download RC-Gate Installation directly from @Remote Center @Remote Center Digital signature Program + digital signature Ricoh Licenese Server Remote Firmware Installation using @Remote Remote installation Download Ridoc IO OperationServer Ricoh distribution server Update performed using Web Smart Device Monitor V2 (device management utility...
Design Guide
Page 20
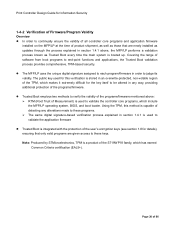
...makes it extremely difficult for the key itself to be altered in any alterations made to these keys. Print Controller Design Guide for Information Security 1-4-2 Verification of Firmware/Program Validity Overview In order to continually ensure the validity of all controller core programs...-based verification process explained in section 1.4.1 is used to validate the application firmware Trusted Boot is integrated with the protection of the user's encryption keys (see section 1.8 for details), ensuring that are newly installed as updates through the process explained in section 1.4.1 above...
...makes it extremely difficult for the key itself to be altered in any alterations made to these keys. Print Controller Design Guide for Information Security 1-4-2 Verification of Firmware/Program Validity Overview In order to continually ensure the validity of all controller core programs...-based verification process explained in section 1.4.1 is used to validate the application firmware Trusted Boot is integrated with the protection of the user's encryption keys (see section 1.8 for details), ensuring that are newly installed as updates through the process explained in section 1.4.1 above...