Design Guide
Page 2
... 12 1-3 Data Security ...14 1-3-1 External I/F ...14 1-3-2 Protection of Program Data from Illegal Access via an External Device 14 1-4 Protection of MFP/LP Firmware 17 1-4-1 Firmware Installation/Update 17 1-4-2 Verification of Firmware/Program Validity 20 1-5 Authentication, Access Control 21 1-5-1 Authentication ...21 1-5-2 IC Card Authentication 24 1-5-3 Access Control...25 1-6 Administrator Settings 26 1-7 Data Protection ...27...
... 12 1-3 Data Security ...14 1-3-1 External I/F ...14 1-3-2 Protection of Program Data from Illegal Access via an External Device 14 1-4 Protection of MFP/LP Firmware 17 1-4-1 Firmware Installation/Update 17 1-4-2 Verification of Firmware/Program Validity 20 1-5 Authentication, Access Control 21 1-5-1 Authentication ...21 1-5-2 IC Card Authentication 24 1-5-3 Access Control...25 1-6 Administrator Settings 26 1-7 Data Protection ...27...
Design Guide
Page 7
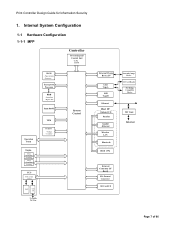
... 1-1-1 MFP Controller Processing and Control Unit ・CPU ・RAM RAM - Image data - Mgmt. control TPM NVRAM - Counters System Control SAF Line I /F Page 7 of 86 Firmware Encryption Processor HDD - Print Controller Design Guide for Information Security 1. Page memory - Line External Charge Device I/F USB TypeA USB TypeB Ethernet Host I/F Optional I/F: Parallel Gigabit...
... 1-1-1 MFP Controller Processing and Control Unit ・CPU ・RAM RAM - Image data - Mgmt. control TPM NVRAM - Counters System Control SAF Line I /F Page 7 of 86 Firmware Encryption Processor HDD - Print Controller Design Guide for Information Security 1. Page memory - Line External Charge Device I/F USB TypeA USB TypeB Ethernet Host I/F Optional I/F: Parallel Gigabit...
Design Guide
Page 8
... files. • RC Gate: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for any illegal alterations. ...Page 8 of the software installed on the hardware platform, which includes checking for firmware storage media. • RAM, HDD: Image data stored in the RAM and HDD memory undergoes compression, decompression and other image ...
... files. • RC Gate: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for any illegal alterations. ...Page 8 of the software installed on the hardware platform, which includes checking for firmware storage media. • RAM, HDD: Image data stored in the RAM and HDD memory undergoes compression, decompression and other image ...
Design Guide
Page 9
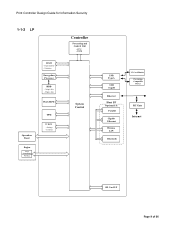
Firmware Encryption Processor HDD - Settings - Page memory - Mgmt. data Flash ROM Operation Panel Engine Image Processing Printing TPM NVRAM - Image data - Counters Controller Processing and Control Unit ・CPU ・RAM System Control USB TypeA USB TypeB Ethernet Host I/F Optional I/F: Parallel Gigabit Ethernet Wireless LAN Bluetooth IC Card Reader Pict Bridge Compatible Device RC Gate Internet SD Card I/F Page 9 of 86 Print Controller Design Guide for Information Security 1-1-2 LP RAM -
Firmware Encryption Processor HDD - Settings - Page memory - Mgmt. data Flash ROM Operation Panel Engine Image Processing Printing TPM NVRAM - Image data - Counters Controller Processing and Control Unit ・CPU ・RAM System Control USB TypeA USB TypeB Ethernet Host I/F Optional I/F: Parallel Gigabit Ethernet Wireless LAN Bluetooth IC Card Reader Pict Bridge Compatible Device RC Gate Internet SD Card I/F Page 9 of 86 Print Controller Design Guide for Information Security 1-1-2 LP RAM -
Design Guide
Page 10
... Information Security • RC Gate: Intermediary device connected to the LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for any illegal alterations.... Page 10 of the software installed on the hardware platform, which includes checking for firmware storage media. • RAM, HDD: Image data stored in the RAM and HDD memory undergoes compression, decompression and other image ...
... Information Security • RC Gate: Intermediary device connected to the LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for any illegal alterations.... Page 10 of the software installed on the hardware platform, which includes checking for firmware storage media. • RAM, HDD: Image data stored in the RAM and HDD memory undergoes compression, decompression and other image ...
Design Guide
Page 12
diagnostics, firmware update, settings changes). Address Book, Document Server, MFP/LP functions). Also contains a printer language processing subsystem (e.g. Activates the scanning engine, which reads the original and ...
diagnostics, firmware update, settings changes). Address Book, Document Server, MFP/LP functions). Also contains a printer language processing subsystem (e.g. Activates the scanning engine, which reads the original and ...
Design Guide
Page 17
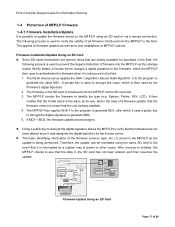
... 64 MB SD card Progra m Digital signature Ricoh License Server 1. If MD1 = MD2, the firmware update process begins. Verification of firmware version If MD1 ≠ MD2 Update process is cancelled and new firmware is overwritten with new files Firmware Update Using an SD Card Page 17 of ...is stored in the event that the data in the field. 1. Compare MD1 and MD2 3. This applies to firmware updates as well as the firmware's digital signature. 2. The Ricoh license server applies the SHA-1 algorithm (Secure Hash Algorithm 1) to the program to new installations of model and...
... 64 MB SD card Progra m Digital signature Ricoh License Server 1. If MD1 = MD2, the firmware update process begins. Verification of firmware version If MD1 ≠ MD2 Update process is cancelled and new firmware is overwritten with new files Firmware Update Using an SD Card Page 17 of ...is stored in the event that the data in the field. 1. Compare MD1 and MD2 3. This applies to firmware updates as well as the firmware's digital signature. 2. The Ricoh license server applies the SHA-1 algorithm (Secure Hash Algorithm 1) to the program to new installations of model and...
Design Guide
Page 18
... via Web SmartDeviceMonitor Professional IS, usually by an individual with new files If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. The process for remote updates is being requested 4. Firmware is overwritten with access rights to confirm that a remote update is virtually the same as that for...
... via Web SmartDeviceMonitor Professional IS, usually by an individual with new files If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. The process for remote updates is being requested 4. Firmware is overwritten with access rights to confirm that a remote update is virtually the same as that for...
Design Guide
Page 19
... Installation via RC-Gate Download RC-Gate Installation directly from @Remote Center @Remote Center Digital signature Program + digital signature Ricoh Licenese Server Remote Firmware Installation using @Remote Remote installation Download Ridoc IO OperationServer Ricoh distribution server Update performed using Web Smart Device Monitor V2 (device management utility) Update commands issued Digital signature Program...
... Installation via RC-Gate Download RC-Gate Installation directly from @Remote Center @Remote Center Digital signature Program + digital signature Ricoh Licenese Server Remote Firmware Installation using @Remote Remote installation Download Ridoc IO OperationServer Ricoh distribution server Update performed using Web Smart Device Monitor V2 (device management utility) Update commands issued Digital signature Program...
Design Guide
Page 20
...valid programs are newly installed as Trusted Boot every time the main system is booted up. The public key used to validate the application firmware Trusted Boot is integrated with the protection of the user's encryption keys (see section 1.8 for details), ensuring that are given access to ..., TPM-based security. Note: Produced by STMicroelectronics, TPM is capable of detecting any way, providing additional protection of the programs/firmware. Page 20 of software from boot programs to judge its validity. The MFP/LP uses the unique digital signature assigned to each program...
...valid programs are newly installed as Trusted Boot every time the main system is booted up. The public key used to validate the application firmware Trusted Boot is integrated with the protection of the user's encryption keys (see section 1.8 for details), ensuring that are given access to ..., TPM-based security. Note: Produced by STMicroelectronics, TPM is capable of detecting any way, providing additional protection of the programs/firmware. Page 20 of software from boot programs to judge its validity. The MFP/LP uses the unique digital signature assigned to each program...
Design Guide
Page 37
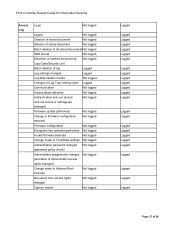
... Not logged Authentication lock-out (actual Not logged lock-out occurs or settings are changed) Firmware update performed Not logged Change in firmware configuration Not logged detected Firmware configuration Not logged Encryption key operation performed Not logged Invalid firmware detected Not logged Change made to Time/Date settings Not logged Authentication password changed Not...
... Not logged Authentication lock-out (actual Not logged lock-out occurs or settings are changed) Firmware update performed Not logged Change in firmware configuration Not logged detected Firmware configuration Not logged Encryption key operation performed Not logged Invalid firmware detected Not logged Change made to Time/Date settings Not logged Authentication password changed Not...
Design Guide
Page 53
.../LP modules. Since the MFP/LP will reject such data, it is also destroyed if accompanying information alerts the MFP/LP that illegal fonts or firmware were downloaded to then safely send the printing data over the communication path. Page 53 of the MFP/LP's internal modules. Therefore, even in the...
.../LP modules. Since the MFP/LP will reject such data, it is also destroyed if accompanying information alerts the MFP/LP that illegal fonts or firmware were downloaded to then safely send the printing data over the communication path. Page 53 of the MFP/LP's internal modules. Therefore, even in the...