Security Target
Page 5
Page 4 of 91 7.3 Document Access Control Function 82 7.4 Use-of-Feature Restriction Function 84 7.5 Network Protection Function 85 7.6 Residual Data Overwrite Function 85 7.7 Stored Data Protection Function 86 7.8 Security Management Function 86 7.9 Software Verification Function 91 7.10 Fax Line Separation Function 91 Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
Page 4 of 91 7.3 Document Access Control Function 82 7.4 Use-of-Feature Restriction Function 84 7.5 Network Protection Function 85 7.6 Residual Data Overwrite Function 85 7.7 Stored Data Protection Function 86 7.8 Security Management Function 86 7.9 Software Verification Function 91 7.10 Fax Line Separation Function 91 Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
Security Target
Page 8
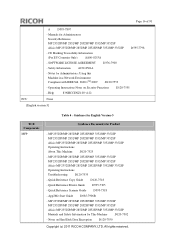
.... Title : Aficio MP 2352/2852/3352 series Security Target Version : 1.00 Date : 2011-12-19 Author : RICOH COMPANY, LTD. 1.2 TOE Reference The TOE is identified by the MFP names and the versions of the TOE is shown below . Although the MFP product names vary depending on the MFP. TOE is shown below . Software System/Copy...
.... Title : Aficio MP 2352/2852/3352 series Security Target Version : 1.00 Date : 2011-12-19 Author : RICOH COMPANY, LTD. 1.2 TOE Reference The TOE is identified by the MFP names and the versions of the TOE is shown below . Although the MFP product names vary depending on the MFP. TOE is shown below . Software System/Copy...
Security Target
Page 10
... connected to the local area network (hereafter "LAN") and telephone lines, as shown in the TOE environment. Copyright (c) 2011 RICOH COMPANY, LTD. MFP A machinery that is the TOE itself, and hardware and software other than the TOE. Print, fax, network transmission, and deletion of the TOE or through LAN communications. LAN Network...
... connected to the local area network (hereafter "LAN") and telephone lines, as shown in the TOE environment. Copyright (c) 2011 RICOH COMPANY, LTD. MFP A machinery that is the TOE itself, and hardware and software other than the TOE. Print, fax, network transmission, and deletion of the TOE or through LAN communications. LAN Network...
Security Target
Page 12
...Security Features of the following security features: - Audit Function - Network Protection Function - Stored Data Protection Function - Software Verification Function - Fax Line Separation Function 1.4 TOE Description This section describes Physical Boundary of TOE, Guidance Documents, ..., USB Port, SD Card Slot, and SD Card. Identification and Authentication Function - Residual Data Overwrite Function - Copyright (c) 2011 RICOH COMPANY, LTD. Document Access Control Function - To ensure provision of -Feature Restriction Function - Use-of confidentiality and integrity for those...
...Security Features of the following security features: - Audit Function - Network Protection Function - Stored Data Protection Function - Software Verification Function - Fax Line Separation Function 1.4 TOE Description This section describes Physical Boundary of TOE, Guidance Documents, ..., USB Port, SD Card Slot, and SD Card. Identification and Authentication Function - Residual Data Overwrite Function - Copyright (c) 2011 RICOH COMPANY, LTD. Document Access Control Function - To ensure provision of -Feature Restriction Function - Use-of confidentiality and integrity for those...
Security Target
Page 13
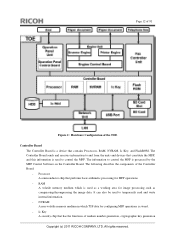
Processor A semiconductor chip that constitute the MFP, and this information is processed by the MFP Control Software on the Controller Board. NVRAM A non-volatile memory medium in which is stored. - All rights reserved. RAM A volatile memory medium ...contains Processors, RAM, NVRAM, Ic Key, and FlashROM. The following describes the components of random number generation, cryptographic key generation Copyright (c) 2011 RICOH COMPANY, LTD. It can also be used to control the MFP. The Controller Board sends and receives information to temporarily read and write internal ...
Processor A semiconductor chip that constitute the MFP, and this information is processed by the MFP Control Software on the Controller Board. NVRAM A non-volatile memory medium in which is stored. - All rights reserved. RAM A volatile memory medium ...contains Processors, RAM, NVRAM, Ic Key, and FlashROM. The following describes the components of random number generation, cryptographic key generation Copyright (c) 2011 RICOH COMPANY, LTD. It can also be used to control the MFP. The Controller Board sends and receives information to temporarily read and write internal ...
Security Target
Page 14
...RemoteFax, Web Support, Web Uapl, NetworkDocBox, animation, LANG0, LANG1, and Data Erase Onb. All rights reserved. The Operation Panel Control Software performs the following devices: key switches, LED indicators, an LCD touch screen, and Operation Control Board. It stores documents, login user names...that constitute the TOE, is the identifier for connection to print and eject paper documents, and Engine Control Board. Copyright (c) 2011 RICOH COMPANY, LTD. OpePanel, which is one of the components that is a user interface installed on the Operation Panel Control Board....
...RemoteFax, Web Support, Web Uapl, NetworkDocBox, animation, LANG0, LANG1, and Data Erase Onb. All rights reserved. The Operation Panel Control Software performs the following devices: key switches, LED indicators, an LCD touch screen, and Operation Control Board. It stores documents, login user names...that constitute the TOE, is the identifier for connection to print and eject paper documents, and Engine Control Board. Copyright (c) 2011 RICOH COMPANY, LTD. OpePanel, which is one of the components that is a user interface installed on the Operation Panel Control Board....
Security Target
Page 16
... Guide D595-7317 - SOFTWARE LICENSE AGREEMENT D376-7900 - MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Manuals and Safety Information for Administrators: Using this Machine in a Network Environment Compliant with IEEE Std. 2600.1TM-2009 D120-7554 - Manuals for Users MP 2352/MP 2852/MP 3352 Aficio MP 2352/MP 2852/MP 3352 D595-7804 - Quick...
... Guide D595-7317 - SOFTWARE LICENSE AGREEMENT D376-7900 - MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Manuals and Safety Information for Administrators: Using this Machine in a Network Environment Compliant with IEEE Std. 2600.1TM-2009 D120-7554 - Manuals for Users MP 2352/MP 2852/MP 3352 Aficio MP 2352/MP 2852/MP 3352 D595-7804 - Quick...
Security Target
Page 17
CE Marking Traceability Information (For EU Countries Only) AA00-0253A - SOFTWARE LICENSE AGREEMENT D376-7900 - Operating Instructions Notes on Hard Disk Data Encryption D120-7550 Copyright (c) 2011 RICOH COMPANY, LTD. MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Operating Instructions Troubleshooting D120-7535 - Safety Information A232-8561A - Help 83NHCCENZ1...
CE Marking Traceability Information (For EU Countries Only) AA00-0253A - SOFTWARE LICENSE AGREEMENT D376-7900 - Operating Instructions Notes on Hard Disk Data Encryption D120-7550 Copyright (c) 2011 RICOH COMPANY, LTD. MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Operating Instructions Troubleshooting D120-7535 - Safety Information A232-8561A - Help 83NHCCENZ1...
Security Target
Page 18
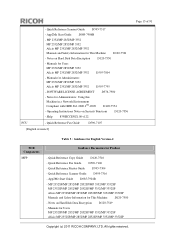
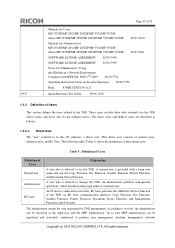
... perform user management, machine management, network Copyright (c) 2011 RICOH COMPANY, LTD. The administrator means the user registered for Administrators MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP D595-7801 - According to use the TOE. These...users. All rights reserved. SOFTWARE LICENSE AGREEMENT D376-7905 - The following table (Table 5) shows the definitions of 91 - Up to the TOE. Notes for Users MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP D595-7810 - The...
... perform user management, machine management, network Copyright (c) 2011 RICOH COMPANY, LTD. The administrator means the user registered for Administrators MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP D595-7801 - According to use the TOE. These...users. All rights reserved. SOFTWARE LICENSE AGREEMENT D376-7905 - The following table (Table 5) shows the definitions of 91 - Up to the TOE. Notes for Users MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP D595-7810 - The...
Security Target
Page 25
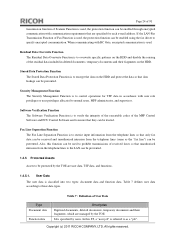
... Function is to verify the integrity of the executable codes of the MFP Control Software and FCU Control Software and to encrypt the data on the HDD and protect the data so that data leakage can be prevented. Table 7 : Definition of User Data Type ... their fragments, which are user data, TSF data, and functions. 1.4.5.1. Table 7 defines user data according to as the "fax line") can be prevented. Copyright (c) 2011 RICOH COMPANY, LTD. When communicating with RC Gate, encrypted communication is classified into two types: document data and function data. User Data The user data is...
... Function is to verify the integrity of the executable codes of the MFP Control Software and FCU Control Software and to encrypt the data on the HDD and protect the data so that data leakage can be prevented. Table 7 : Definition of User Data Type ... their fragments, which are user data, TSF data, and functions. 1.4.5.1. Table 7 defines user data according to as the "fax line") can be prevented. Copyright (c) 2011 RICOH COMPANY, LTD. When communicating with RC Gate, encrypted communication is classified into two types: document data and function data. User Data The user data is...
Security Target
Page 26
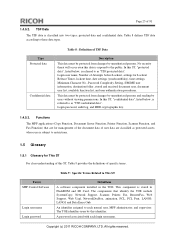
...Font, LANG0, LANG1 and Data Erase Onb. The components that are for management of the document data of specific terms. Terms MFP Control Software Login user name Login password Table 9 : Specific Terms Related to as protected assets, whose use is subject to restrictions. 1.5 Glossary ... information, destination folder, stored and received document user, document user list, available function list, and user authentication procedures. Copyright (c) 2011 RICOH COMPANY, LTD. TSF Data The TSF data is classified into two types: protected data and confidential data. Login user name, Number of...
...Font, LANG0, LANG1 and Data Erase Onb. The components that are for management of the document data of specific terms. Terms MFP Control Software Login user name Login password Table 9 : Specific Terms Related to as protected assets, whose use is subject to restrictions. 1.5 Glossary ... information, destination folder, stored and received document user, document user list, available function list, and user authentication procedures. Copyright (c) 2011 RICOH COMPANY, LTD. TSF Data The TSF data is classified into two types: protected data and confidential data. Login user name, Number of...
Security Target
Page 36
The audit log shall be protected from physical access by authorised persons. Copyright (c) 2011 RICOH COMPANY, LTD. P.INTERFACE.MANAGEMENT Management of those policies and procedures. P.RCGATE.COMM.PROTECT Protection of their organisation ... communication data between itself and RC Gate. 3.3 Assumptions The assumptions related to this TOE usage environment are identified and described. P.SOFTWARE.VERIFICATION Software verification Procedures shall exist to self-verify executable code in a restricted or monitored area that provides protection from unauthorised disclosure or alteration...
The audit log shall be protected from physical access by authorised persons. Copyright (c) 2011 RICOH COMPANY, LTD. P.INTERFACE.MANAGEMENT Management of those policies and procedures. P.RCGATE.COMM.PROTECT Protection of their organisation ... communication data between itself and RC Gate. 3.3 Assumptions The assumptions related to this TOE usage environment are identified and described. P.SOFTWARE.VERIFICATION Software verification Procedures shall exist to self-verify executable code in a restricted or monitored area that provides protection from unauthorised disclosure or alteration...
Security Target
Page 39
... the TOE. O.RCGATE.COMM.PROTECT Protection of communication with RC Gate The TOE shall conceal the communication data on the HDD. Copyright (c) 2011 RICOH COMPANY, LTD. O.SOFTWARE.VERIFIED Software verification The TOE shall provide procedures to self-verify executable code in accordance with the security policies. O.INTERFACE.MANAGED Management of external interfaces by...
... the TOE. O.RCGATE.COMM.PROTECT Protection of communication with RC Gate The TOE shall conceal the communication data on the HDD. Copyright (c) 2011 RICOH COMPANY, LTD. O.SOFTWARE.VERIFIED Software verification The TOE shall provide procedures to self-verify executable code in accordance with the security policies. O.INTERFACE.MANAGED Management of external interfaces by...
Security Target
Page 41
...O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DIS O.CONF.NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE....X X X T.FUNC.ALT X X X T.PROT.ALT X X X T.CONF.DIS X X X T.CONF.ALT X X X P.USER.AUTHORIZATION X X P.SOFTWARE.VERIFICATION X P.AUDIT.LOGGING X XXX P.INTERFACE.MANAGEMENT X X P.STORAGE.ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright ...
...O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DIS O.CONF.NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE....X X X T.FUNC.ALT X X X T.PROT.ALT X X X T.CONF.DIS X X X T.CONF.ALT X X X P.USER.AUTHORIZATION X X P.SOFTWARE.VERIFICATION X P.AUDIT.LOGGING X XXX P.INTERFACE.MANAGEMENT X X P.STORAGE.ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright ...
Security Target
Page 43
... O.USER.AUTHORIZED and OE.USER.AUTHORIZED. T.CONF.DIS is enforced by these objectives. P. By O.SOFTWARE.VERIFIED, the TOE provides measures for self-verifying the executable code of users, and users are authorised... accordance with a login user name but without an access permission to the TSF confidential data. P.SOFTWARE.VERIFICATION is countered by O.CONF.NO_DIS, O.USER.AUTHORIZED and OE.USER.AUTHORIZED. Page 42 of 91... persons without a login user name, or by O.SOFTWARE.VERIFIED. T.CONF.ALT is enforced by persons with the security policies before being allowed to use the...
... O.USER.AUTHORIZED and OE.USER.AUTHORIZED. T.CONF.DIS is enforced by these objectives. P. By O.SOFTWARE.VERIFIED, the TOE provides measures for self-verifying the executable code of users, and users are authorised... accordance with a login user name but without an access permission to the TSF confidential data. P.SOFTWARE.VERIFICATION is countered by O.CONF.NO_DIS, O.USER.AUTHORIZED and OE.USER.AUTHORIZED. Page 42 of 91... persons without a login user name, or by O.SOFTWARE.VERIFIED. T.CONF.ALT is enforced by persons with the security policies before being allowed to use the...
Security Target
Page 66
... TSF shall provide authorised users with the capability to verify the integrity of [selection: [assignment: the MFP Control Software, FCU Control Software]]. Dependencies: FIA_UID.1 Timing of [selection: [assignment: the audit log data file]]. Copyright (c) 2011 RICOH COMPANY, LTD. FPT_TST.1.2 The TSF shall provide authorised users with roles. 6.1.6 Class FPT: Protection of user authentication...
... TSF shall provide authorised users with the capability to verify the integrity of [selection: [assignment: the MFP Control Software, FCU Control Software]]. Dependencies: FIA_UID.1 Timing of [selection: [assignment: the audit log data file]]. Copyright (c) 2011 RICOH COMPANY, LTD. FPT_TST.1.2 The TSF shall provide authorised users with roles. 6.1.6 Class FPT: Protection of user authentication...
Security Target
Page 69
... Table 32 : Relationship between Security Objectives and Functional Requirements O.DOC.NO_DI S O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED O.INTERFACE.MANAGED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT FAU_GEN.1 FAU_GEN.2 FAU_STG.1 FAU_STG.4 FAU_SAR.1 FAU_SAR.2 FCS_CKM.1 FCS_COP.1 FDP_ACC.1(a) X X X FDP_ACC.1(b) FDP_ACF.1(a) X X X FDP_ACF.1(b) FDP_RIP.1 X X FIA_AFL.1 FIA_ATD.1 FIA_SOS.1 FIA_UAU...
... Table 32 : Relationship between Security Objectives and Functional Requirements O.DOC.NO_DI S O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED O.INTERFACE.MANAGED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT FAU_GEN.1 FAU_GEN.2 FAU_STG.1 FAU_STG.4 FAU_SAR.1 FAU_SAR.2 FCS_CKM.1 FCS_COP.1 FDP_ACC.1(a) X X X FDP_ACC.1(b) FDP_ACF.1(a) X X X FDP_ACF.1(b) FDP_RIP.1 X X FIA_AFL.1 FIA_ATD.1 FIA_SOS.1 FIA_UAU...
Security Target
Page 70
....1. (4) Management of the security attributes. Page 69 of 91 O.DOC.NO_DI S O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED O.INTERFACE.MANAGED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT FMT_MSA.3(b) FMT_MTD.1 FMT_SMF.1 FMT_SMR.1 FPT_STM.1 FPT_TST.1 FTA_SSL.3 FTP_ITC.1 X X X X X X X X X X X X X... user who is registered on the document user list, and a specified user Copyright (c) 2011 RICOH COMPANY, LTD. Deleted documents, temporary documents and their fragments. To fulfil this security objective, it...
....1. (4) Management of the security attributes. Page 69 of 91 O.DOC.NO_DI S O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED O.INTERFACE.MANAGED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT FMT_MSA.3(b) FMT_MTD.1 FMT_SMF.1 FMT_SMR.1 FPT_STM.1 FPT_TST.1 FTA_SSL.3 FTP_ITC.1 X X X X X X X X X X X X X... user who is registered on the document user list, and a specified user Copyright (c) 2011 RICOH COMPANY, LTD. Deleted documents, temporary documents and their fragments. To fulfil this security objective, it...
Security Target
Page 75
... the event FPT_STM.1 provides a trusted time stamp, and a reliable record of the times when events occurred are verified. To fulfil this countermeasure, O.SOFTWARE.VERIFIED is encrypted. Copyright (c) 2011 RICOH COMPANY, LTD. FAU_SAR.1 allows the MFP administrator to be auditable, with the identification information of the occurrence factor. (2) Protect the audit log. By...
... the event FPT_STM.1 provides a trusted time stamp, and a reliable record of the times when events occurred are verified. To fulfil this countermeasure, O.SOFTWARE.VERIFIED is encrypted. Copyright (c) 2011 RICOH COMPANY, LTD. FAU_SAR.1 allows the MFP administrator to be auditable, with the identification information of the occurrence factor. (2) Protect the audit log. By...
Security Target
Page 92
...the hash does not match its original value and the certificate is disconnected. The TOE also verifies the integrity of the FCU Control Software can be forwarded. If the hash matches its original value or the certificate verification fails, the TOE displays the error message and becomes... received faxes so that the integrity of the audit log data files. Copyright (c) 2011 RICOH COMPANY, LTD. If any communication that unauthorised intrusion from telephone lines. FPT_TST.1 The TOE verifies software at the TOE start-up. Since the TOE is set to receive only faxes as ...
...the hash does not match its original value and the certificate is disconnected. The TOE also verifies the integrity of the FCU Control Software can be forwarded. If the hash matches its original value or the certificate verification fails, the TOE displays the error message and becomes... received faxes so that the integrity of the audit log data files. Copyright (c) 2011 RICOH COMPANY, LTD. If any communication that unauthorised intrusion from telephone lines. FPT_TST.1 The TOE verifies software at the TOE start-up. Since the TOE is set to receive only faxes as ...