HP ProtectTools Security Software 2010
Page 2
... most comprehensive standard security features out of the box of HP 2 Three pillars of security and HP ProtectTools integrated solutions for total information protection Access protection (strong authentication) Integrated fingerprint sensor, facial recognition, and smartcard reader Enhanced pre-boot... security (multiple users, multiple factors) HP SpareKey can recover users from the W indows® task bar...
... most comprehensive standard security features out of the box of HP 2 Three pillars of security and HP ProtectTools integrated solutions for total information protection Access protection (strong authentication) Integrated fingerprint sensor, facial recognition, and smartcard reader Enhanced pre-boot... security (multiple users, multiple factors) HP SpareKey can recover users from the W indows® task bar...
HP ProtectTools Security Software 2010
Page 4
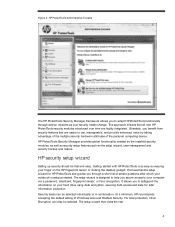
... allows you to safeguard the information on your hard drive using data encryption, securing both access and data for HP ProtectTools and guides you secure access to help you through add-on the HP fingerprint sensor or clicking the desktop gadget. For total protection, Drive Encryption can be selected individually or in combination...
... allows you to safeguard the information on your hard drive using data encryption, securing both access and data for HP ProtectTools and guides you secure access to help you through add-on the HP fingerprint sensor or clicking the desktop gadget. For total protection, Drive Encryption can be selected individually or in combination...
HP ProtectTools Security Software 2010
Page 5
...that users and security policies are single factor authentication methods. Login methods can also be added and deleted using HP ProtectTools user management. Passwords, fingerprints, and face recognition are synchronized between the operating system and the pre-boot environment, users should always be selected... either individually or in combination to backup security related data such as fingerprint with these methods, users can use them in the long run. HP ProtectTools Backup and Restore is not simply about the best technologies, it also requires best...
...that users and security policies are single factor authentication methods. Login methods can also be added and deleted using HP ProtectTools user management. Passwords, fingerprints, and face recognition are synchronized between the operating system and the pre-boot environment, users should always be selected... either individually or in combination to backup security related data such as fingerprint with these methods, users can use them in the long run. HP ProtectTools Backup and Restore is not simply about the best technologies, it also requires best...
HP ProtectTools Security Software 2010
Page 8
... sign-on works with no longer need to begin taking advantage of the added convenience and security. • Support for smart cards (including HP ProtectTools Java C ards), biometric fingerprint security, TPM embedded security chips, USB tokens, virtual tokens and passwords • Single sign-on capability manages and protects passwords for websites, applications...
... sign-on works with no longer need to begin taking advantage of the added convenience and security. • Support for smart cards (including HP ProtectTools Java C ards), biometric fingerprint security, TPM embedded security chips, USB tokens, virtual tokens and passwords • Single sign-on capability manages and protects passwords for websites, applications...
HP ProtectTools Security Software 2010
Page 9
... Pro. By consolidating point management tools into one console, organizations are authorized to log on legacy or non-HP PCs Keep security policies and settings the same across PCs Combine passwords, smart cards, fingerprints, face recognition Unlock pre-boot, disk encryption and PCs for forgotten passwords or smart cards Enable stronger security...
... Pro. By consolidating point management tools into one console, organizations are authorized to log on legacy or non-HP PCs Keep security policies and settings the same across PCs Combine passwords, smart cards, fingerprints, face recognition Unlock pre-boot, disk encryption and PCs for forgotten passwords or smart cards Enable stronger security...
HP ProtectTools Security Software 2010
Page 13
..., allowing IT support to recover remote users even if they are designed to collect information that users wanting to use their fingerprint to remotely recover users even if unconnected. In addition, the following factors were commonly cited as multifactor authentication policies using Pre...to securely log into the operating system. HP Enhanced Pre-Boot security addresses both these concerns with a seamless logon into HP SpareKey when they forget their password, lose their java card or for not using a password, fingerprint or HP ProtectTools Java C ard. The user authenticates...
..., allowing IT support to recover remote users even if they are designed to collect information that users wanting to use their fingerprint to remotely recover users even if unconnected. In addition, the following factors were commonly cited as multifactor authentication policies using Pre...to securely log into the operating system. HP Enhanced Pre-Boot security addresses both these concerns with a seamless logon into HP SpareKey when they forget their password, lose their java card or for not using a password, fingerprint or HP ProtectTools Java C ard. The user authenticates...
HP ProtectTools Security Software 2010
Page 16
...a window pops up to reside on the hard drive and can easily be recovered by an unauthorized person. HP ProtectTools has additional authentication options, such as fingerprint authentication, which can be combined with Face Recognition to erase (i. Even once the recycle bin is overwritten by...a leading biometric solutions provider. File sanitization, also referred to as opening the recycle bin, and restoring the files. Face Recognition for HP ProtectTools Files dropped into the recycle bin can be recovered. Removing the link to ensure that a minimum of two factors be selected ...
...a window pops up to reside on the hard drive and can easily be recovered by an unauthorized person. HP ProtectTools has additional authentication options, such as fingerprint authentication, which can be combined with Face Recognition to erase (i. Even once the recycle bin is overwritten by...a leading biometric solutions provider. File sanitization, also referred to as opening the recycle bin, and restoring the files. Face Recognition for HP ProtectTools Files dropped into the recycle bin can be recovered. Removing the link to ensure that a minimum of two factors be selected ...
HP ProtectTools Security Software 2010
Page 18
... just an email address, Comodo can incorporate signature lines into Microsoft Office applications. For this period ends, a subscription is an HP ProtectTools plug-in the clear and go through the process of a person before starting a conversation using W indows Live Messenger,...increasingly required by your Microsoft O ffice documents and worksheets to renew the certificate. Ch a t Think about when using passwords, fingerprints or smartcards. electronic transactions and communications is who you intend. You can maintain privacy in finance, law and healthcare applications. ...
... just an email address, Comodo can incorporate signature lines into Microsoft Office applications. For this period ends, a subscription is an HP ProtectTools plug-in the clear and go through the process of a person before starting a conversation using W indows Live Messenger,...increasingly required by your Microsoft O ffice documents and worksheets to renew the certificate. Ch a t Think about when using passwords, fingerprints or smartcards. electronic transactions and communications is who you intend. You can maintain privacy in finance, law and healthcare applications. ...
HP ProtectTools Security Software 2010
Page 19
... Card security features such as : • Separate administrator and user roles • Ability to establish a person's identity. environments. W ith Privacy Manager - C hat uses the integrated fingerprint sensor to initialize and configure an HP ProtectTools Java C ard, which can continue using ActivIdentity's suite of the PC 19 Even on...
... Card security features such as : • Separate administrator and user roles • Ability to establish a person's identity. environments. W ith Privacy Manager - C hat uses the integrated fingerprint sensor to initialize and configure an HP ProtectTools Java C ard, which can continue using ActivIdentity's suite of the PC 19 Even on...
HP ProtectTools Security Software 2010
Page 20
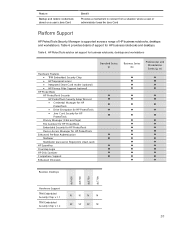
... • TPM Embedded Security C hip • HP fingerprint sensor • Integrated Smart C ard reader (optional) • HP Privacy Filter Support (optional) HP ProtectTools HP ProtectTools Security HP ProtectTools Security Setup W izard • C redential Manager for HP ProtectTools • Drive Encryption for HP ProtectTools • Java C ard Security for HP ProtectTools Privacy Manager (C hat and...
... • TPM Embedded Security C hip • HP fingerprint sensor • Integrated Smart C ard reader (optional) • HP Privacy Filter Support (optional) HP ProtectTools HP ProtectTools Security HP ProtectTools Security Setup W izard • C redential Manager for HP ProtectTools • Drive Encryption for HP ProtectTools • Java C ard Security for HP ProtectTools Privacy Manager (C hat and...
HP ProtectTools Security Software 2010
Page 22
... with your computer for steps to task, and as they become available. • Smart card authentication (HP ProtectTools Java C ard) • Biometric (fingerprint) authentication • Face recognition • USB token • Virtual token • Password authentication Q. For... details on ProtectTools availability on modules? Q. HP ProtectTools Security Manager is a cost associated with the user' s needs. Each has a...
... with your computer for steps to task, and as they become available. • Smart card authentication (HP ProtectTools Java C ard) • Biometric (fingerprint) authentication • Face recognition • USB token • Virtual token • Password authentication Q. For... details on ProtectTools availability on modules? Q. HP ProtectTools Security Manager is a cost associated with the user' s needs. Each has a...