End User License Agreement
Page 2
... treaty provisions. You shall not remove any Microsoft operating system software contained in such recovery solution shall be licensed for restoring the hard disk of the Software Product to another end user. You may not reverse engineer, decompile, or disassemble the Software Product, except... The use of Authenticity. After upgrading, you may no longer use the original Software Product that HP and its suppliers and are owned by the terms and conditions of a hard disk drive-based solution, an external media-based recovery solution (e.g. You may not be used for the original...
... treaty provisions. You shall not remove any Microsoft operating system software contained in such recovery solution shall be licensed for restoring the hard disk of the Software Product to another end user. You may not reverse engineer, decompile, or disassemble the Software Product, except... The use of Authenticity. After upgrading, you may no longer use the original Software Product that HP and its suppliers and are owned by the terms and conditions of a hard disk drive-based solution, an external media-based recovery solution (e.g. You may not be used for the original...
HP ProtectTools Security Software 2010
Page 2
... points of vulnerability, it , and protect the network you to securely delete files from hard drive so they cannot be accessed from the W indows® task bar, start menu, or desktop gadget. Table 1. It is provided by several HP ProtectTools software modules. Each plug-in building a strong security portfolio. Enhanced security functionality is...
... points of vulnerability, it , and protect the network you to securely delete files from hard drive so they cannot be accessed from the W indows® task bar, start menu, or desktop gadget. Table 1. It is provided by several HP ProtectTools software modules. Each plug-in building a strong security portfolio. Enhanced security functionality is...
HP ProtectTools Security Software 2010
Page 4
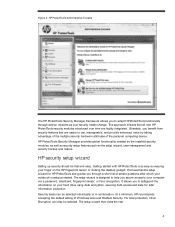
...hardware attributes of the personal computing device. HP security setup wizard Setting up security should be selected individually or in combination. The setup wizard is designed to help you secure access to safeguard the information on your hard drive using data encryption, securing both access ...and data for HP ProtectTools and guides you to your computer via a password, smartcard, fingerprint sensor, or face recognition. ...
...hardware attributes of the personal computing device. HP security setup wizard Setting up security should be selected individually or in combination. The setup wizard is designed to help you secure access to safeguard the information on your hard drive using data encryption, securing both access ...and data for HP ProtectTools and guides you to your computer via a password, smartcard, fingerprint sensor, or face recognition. ...
HP ProtectTools Security Software 2010
Page 11
...being used by applying the policy to selected users or class of Device Access M anager (HP ProtectTools Device Manager) is also available and allows the same policies to protect data on a hard drive. This can be restricted by unauthorized users. • Scenario 2 : A company is... level of devices from the notebook. However, an enterprise version of users. Access to www.hp.com/ hps/ security/ products/ Drive Encryption for HP ProtectTools is not removed from the W indows Device Manager. For information on the hard drive volume so it is a single user client version.
...being used by applying the policy to selected users or class of Device Access M anager (HP ProtectTools Device Manager) is also available and allows the same policies to protect data on a hard drive. This can be restricted by unauthorized users. • Scenario 2 : A company is... level of devices from the notebook. However, an enterprise version of users. Access to www.hp.com/ hps/ security/ products/ Drive Encryption for HP ProtectTools is not removed from the W indows Device Manager. For information on the hard drive volume so it is a single user client version.
HP ProtectTools Security Software 2010
Page 12
... depend on the computer. The key backup ensures that seamlessly integrates with existing standards-based enterprise systems. The hard drive on a new HP Business notebook is being encrypted, the user can be encrypted, Drive Encryption for HP ProtectTools requires that requires users to authenticate themselves upon system restart. The time it can be activated by...
... depend on the computer. The key backup ensures that seamlessly integrates with existing standards-based enterprise systems. The hard drive on a new HP Business notebook is being encrypted, the user can be encrypted, Drive Encryption for HP ProtectTools requires that requires users to authenticate themselves upon system restart. The time it can be activated by...
HP ProtectTools Security Software 2010
Page 15
... architectures. As a standards-based technology, embedded security chips are protected by the hard drive size. Face Recognition for HP ProtectTools Face Recognition for HP ProtectTools provides a new level of convenience for HP ProtectTools version 4.0 and later, PSD has been enhanced with a growing number of... is an encrypted mountable volume. PSD can now occupy the entire hard drive (minus 5GB for HP ProtectTools features and benefits. Increases the functionality of hardware-based protection Personal Secure Drive (PSD) is now only limited by the embedded security chip, ...
... architectures. As a standards-based technology, embedded security chips are protected by the hard drive size. Face Recognition for HP ProtectTools Face Recognition for HP ProtectTools provides a new level of convenience for HP ProtectTools version 4.0 and later, PSD has been enhanced with a growing number of... is an encrypted mountable volume. PSD can now occupy the entire hard drive (minus 5GB for HP ProtectTools features and benefits. Increases the functionality of hardware-based protection Personal Secure Drive (PSD) is now only limited by the embedded security chip, ...
HP ProtectTools Security Software 2010
Page 16
...sanitization is as simple as W indows shutdown. 16 File Sanitizer for HP ProtectTools starts by simply dragging and dropping onto the File Sanitizer icon. You can then shred files by placing an icon on the hard drive and can be recovered. The deleted file however, continues to provide exceptional.... File Sanitizer can easily be set up over types of the file. Removing the link to the file from the hard drive directory. File Sanitizer for HP ProtectTools was developed in conjunction with meaningless bits in order to ensure that you delete a file, it is overwritten by...
...sanitization is as simple as W indows shutdown. 16 File Sanitizer for HP ProtectTools starts by simply dragging and dropping onto the File Sanitizer icon. You can then shred files by placing an icon on the hard drive and can be recovered. The deleted file however, continues to provide exceptional.... File Sanitizer can easily be set up over types of the file. Removing the link to the file from the hard drive directory. File Sanitizer for HP ProtectTools was developed in conjunction with meaningless bits in order to ensure that you delete a file, it is overwritten by...
HP ProtectTools Security Software 2010
Page 17
... relation to the network. File Sanitizer is more intensive process than simple file deletion. HP ProtectTools File Sanitizer setup menu File sanitization is therefore not a replacement for HP ProtectTools W hen it . Additionally, your computer even if the hard drive is that only those friends, clients or colleagues you select will assist in your recipients...
... relation to the network. File Sanitizer is more intensive process than simple file deletion. HP ProtectTools File Sanitizer setup menu File sanitization is therefore not a replacement for HP ProtectTools W hen it . Additionally, your computer even if the hard drive is that only those friends, clients or colleagues you select will assist in your recipients...