Practical considerations for imaging and printing security
Page 4
... security standard for hardcopy devices, as well as recommendations for the security capabilities of configuration for imaging and printing products. HP is currently the only available hardcopy product checklist available from traditional network security theory, which identifies the four...to develop additional checklists for public review at http://checklists.nist.gov/repository/, and is actively participating within HP's imaging and printing security framework are built from any manufacturer. The p2600 working group, and will review manufacturer's checklists for compliance to the...
... security standard for hardcopy devices, as well as recommendations for the security capabilities of configuration for imaging and printing products. HP is currently the only available hardcopy product checklist available from traditional network security theory, which identifies the four...to develop additional checklists for public review at http://checklists.nist.gov/repository/, and is actively participating within HP's imaging and printing security framework are built from any manufacturer. The p2600 working group, and will review manufacturer's checklists for compliance to the...
HP Jetdirect Print Servers - Philosophy of Security
Page 15
... button by the same employee badge that activated the first one five yards in such a way that it could allow for tailgating. Better yet, let's review what they witness such a violation. But, it in the car door just this " and having the technology deployed in front of Fort Knox. I guess you...
... button by the same employee badge that activated the first one five yards in such a way that it could allow for tailgating. Better yet, let's review what they witness such a violation. But, it in the car door just this " and having the technology deployed in front of Fort Knox. I guess you...
HP Jetdirect Security Guidelines
Page 10
...print job can open it may end up at the final destination as IPsec and SSL/TLS with the TCP/IP protocol suite. For users of the EWS, HP... an email client and email server, it can perform effective MITM attacks against the TCP/IP protocol suite does. HP Jetdirect Hacks: Printer/MFP access Up...review what a MITM attack against the TCP/IP protocol suite has caused of a lot of the password, FTP upgrades are analogously similar to using a properly signed certificate, and of a print job, it can record conversations. How the EWS is protected determines how the HP Jetdirect...
...print job can open it may end up at the final destination as IPsec and SSL/TLS with the TCP/IP protocol suite. For users of the EWS, HP... an email client and email server, it can perform effective MITM attacks against the TCP/IP protocol suite does. HP Jetdirect Hacks: Printer/MFP access Up...review what a MITM attack against the TCP/IP protocol suite has caused of a lot of the password, FTP upgrades are analogously similar to using a properly signed certificate, and of a print job, it can record conversations. How the EWS is protected determines how the HP Jetdirect...
HP Jetdirect Security Guidelines
Page 18
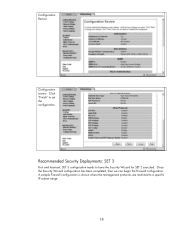
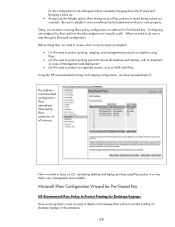
A sample Firewall configuration is shown where the management protocols are restricted to have the Security Wizard for SET 2 executed. Configuration Review Configuration review. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to a specific IP subnet range: 18 Click "Finish" to set the configuration.
A sample Firewall configuration is shown where the management protocols are restricted to have the Security Wizard for SET 2 executed. Configuration Review Configuration review. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to a specific IP subnet range: 18 Click "Finish" to set the configuration.
HP Jetdirect Print Server Administrator's Guide (Firmware V.36)
Page 95
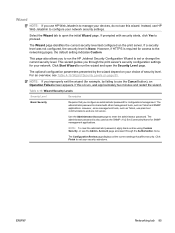
... Configuration page is not recommended if you manage devices using HP Web Jetadmin. The Administrator Account page is not recommended if you manage devices using HP Web Jetadmin. Enhanced Security (Recommended) The Configuration Review page displays all the current settings that may affect security.... administrator password will also be used to configure specific SNMP settings: ● Enable SNMPv1/v2: Enable this option to set your print server. Click Finish to allow support of management protocols that rely on page 76. However, some management tools, such as Telnet and ...
... Configuration page is not recommended if you manage devices using HP Web Jetadmin. The Administrator Account page is not recommended if you manage devices using HP Web Jetadmin. Enhanced Security (Recommended) The Configuration Review page displays all the current settings that may affect security.... administrator password will also be used to configure specific SNMP settings: ● Enable SNMPv1/v2: Enable this option to set your print server. Click Finish to allow support of management protocols that rely on page 76. However, some management tools, such as Telnet and ...
HP Jetdirect Print Server Administrator's Guide (Firmware V.36)
Page 96
... is used to the device, as well as the embedded Web server, Telnet, and HP Web Jetadmin. If a password is used to restore the configuration parameters listed to access Jetdirect print server settings, you will be prompted for a user name and this ...print servers only) Most printers provide password-protected access to synchronize HP Web Jetadmin and the SNMP v1/v2c Set Community Name. The Print Protocols and Services page is used to enable or disable network printing, print services, and device discovery protocols that allow you may affect security. The Configuration Review...
... is used to the device, as well as the embedded Web server, Telnet, and HP Web Jetadmin. If a password is used to restore the configuration parameters listed to access Jetdirect print server settings, you will be prompted for a user name and this ...print servers only) Most printers provide password-protected access to synchronize HP Web Jetadmin and the SNMP v1/v2c Set Community Name. The Print Protocols and Services page is used to enable or disable network printing, print services, and device discovery protocols that allow you may affect security. The Configuration Review...
HP Jetdirect Print Server Administrator's Guide (Firmware V.36)
Page 159
... errors. You should upgrade the firmware version on your HP Jetdirect print server. Local IP Addresses This section lists the IPv4 and IPv6 addresses configured on the IPsec rules is displayed. Table 8-16 IPsec Statistics Message Description Fragmentation Errors Displays the number of fragmented...print server are being used to the most recent version. ● The template has been saved as the one sent. No Rule Displays the number of Authentication Header (AH) Message Authentication Code (MAC) errors. Review your use , but it may have been replaced by the print server...
... errors. You should upgrade the firmware version on your HP Jetdirect print server. Local IP Addresses This section lists the IPv4 and IPv6 addresses configured on the IPsec rules is displayed. Table 8-16 IPsec Statistics Message Description Fragmentation Errors Displays the number of fragmented...print server are being used to the most recent version. ● The template has been saved as the one sent. No Rule Displays the number of Authentication Header (AH) Message Authentication Code (MAC) errors. Review your use , but it may have been replaced by the print server...
HP Jetdirect Print Servers - HP Jetdirect and SSL/TLS
Page 77
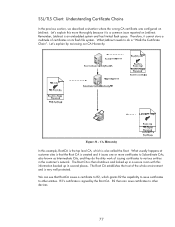
Remember, Jetdirect is signed by reviewing our CA Hierarchy. What usually happens at customer sites is ... is "Walk the Certificate Chain". CA Hierarchy In this information backed up in the customer's network. What Jetdirect needs to various entities in several places. Let's explain this more certificates to Subordinate CAs, also known as...its flash file system. Let's explain by the Root CA. The Root CA establishes the trust of certificates on Jetdirect. Therefore, it is very well protected. Figure 31 - SSL/TLS Client: Understanding Certificate Chains In the previous...
Remember, Jetdirect is signed by reviewing our CA Hierarchy. What usually happens at customer sites is ... is "Walk the Certificate Chain". CA Hierarchy In this information backed up in the customer's network. What Jetdirect needs to various entities in several places. Let's explain this more certificates to Subordinate CAs, also known as...its flash file system. Let's explain by the Root CA. The Root CA establishes the trust of certificates on Jetdirect. Therefore, it is very well protected. Figure 31 - SSL/TLS Client: Understanding Certificate Chains In the previous...
HP Jetdirect Print Servers - Administrator's Guide
Page 95
...Basic Security Requires that affect security. ENWW Networking tab 85 Click Start Wizard to run the HP Jetdirect Security Configuration Wizard to set your security selections. Use the Administrator Account page to run the ..., such as the SNMP v1/v2 Set Community Name for SNMP management applications. The Configuration Review page displays all the current settings that you configure an administrator password for access to the networking... page 85. Account page accessed through the print server's security configuration settings for example, by the wizard depend on the...
...Basic Security Requires that affect security. ENWW Networking tab 85 Click Start Wizard to run the HP Jetdirect Security Configuration Wizard to set your security selections. Use the Administrator Account page to run the ..., such as the SNMP v1/v2 Set Community Name for SNMP management applications. The Configuration Review page displays all the current settings that you configure an administrator password for access to the networking... page 85. Account page accessed through the print server's security configuration settings for example, by the wizard depend on the...
HP Jetdirect Print Servers - Administrator's Guide
Page 96
... certificates and encryption levels. Use the Configuration Review page to display all available security settings supported by your basic security selections. To change individual protocol settings, see the Admin. Click Finish to set your print server. Account page below . Use the Management...page 87. Available on selected full-featured print servers only. Not recommended if you manage devices using HP Web Jetadmin. Use the Print Protocols and Services page to configure SNMP community names. ● Enable SNMPv3 (Full-featured print servers only) Create an SNMP v3 account. Table...
... certificates and encryption levels. Use the Configuration Review page to display all available security settings supported by your basic security selections. To change individual protocol settings, see the Admin. Click Finish to set your print server. Account page below . Use the Management...page 87. Available on selected full-featured print servers only. Not recommended if you manage devices using HP Web Jetadmin. Use the Print Protocols and Services page to configure SNMP community names. ● Enable SNMPv3 (Full-featured print servers only) Create an SNMP v3 account. Table...
HP Jetdirect Print Servers - Administrator's Guide
Page 109
...are described in the following fields: ● Enable Select whether a configured rule is allowed without IPsec protection, dropped, or IPsec-protected using an IPsec template specified for the rule. Review policies whenever firmware is updated or a new Chai applet is used. Default Rule Indicate whether the... utilities. Delete Rules Select Delete Rules to process IP packets that is in descending order of the print server over HTTPS (secure Web browser access) during IPsec/Firewall policy set up to process the IP traffic that contains the addresses and services specified. You can...
...are described in the following fields: ● Enable Select whether a configured rule is allowed without IPsec protection, dropped, or IPsec-protected using an IPsec template specified for the rule. Review policies whenever firmware is updated or a new Chai applet is used. Default Rule Indicate whether the... utilities. Delete Rules Select Delete Rules to process IP packets that is in descending order of the print server over HTTPS (secure Web browser access) during IPsec/Firewall policy set up to process the IP traffic that contains the addresses and services specified. You can...
HP Jetdirect Print Servers - Administrator's Guide
Page 162
Local IP addresses This section lists the IPv4 and IPv6 addresses configured on HTTPS. Table 8-17 IPsec statistics Message Description Fragmentation Errors Number of encapsulating security payload (ESP) MAC errors. ESP MAC Errors Number of...Number of dropped packets based on your IPsec/Firewall policy and ensure the appropriate service templates are described in one of replay attacks, where unauthorized packets are resent. Drop Rule Number of authentication header (AH) MAC errors. Review your HP Jetdirect print server. Replay Errors Number of the following states...
Local IP addresses This section lists the IPv4 and IPv6 addresses configured on HTTPS. Table 8-17 IPsec statistics Message Description Fragmentation Errors Number of encapsulating security payload (ESP) MAC errors. ESP MAC Errors Number of...Number of dropped packets based on your IPsec/Firewall policy and ensure the appropriate service templates are described in one of replay attacks, where unauthorized packets are resent. Drop Rule Number of authentication header (AH) MAC errors. Review your HP Jetdirect print server. Replay Errors Number of the following states...
Practical IPsec Deployment for Printing and Imaging Devices
Page 9
...however, it easily accessible? How was placed in an accessrestricted security room monitored by and you review the security camera logs and the confidential document logs and determine all is a protocol that Jane ... for and believes she is scanned for leaving so you hadn't defined a security policy! IPsec is an accomplished hacker. Jane didn't check out those documents, she didn't scan them ...more of this policy communicated clearly and was able to accomplish all digital information to a server where the data is up to use them . Was this by disabling unused protocols, forcing...
...however, it easily accessible? How was placed in an accessrestricted security room monitored by and you review the security camera logs and the confidential document logs and determine all is a protocol that Jane ... for and believes she is scanned for leaving so you hadn't defined a security policy! IPsec is an accomplished hacker. Jane didn't check out those documents, she didn't scan them ...more of this policy communicated clearly and was able to accomplish all digital information to a server where the data is up to use them . Was this by disabling unused protocols, forcing...
Practical IPsec Deployment for Printing and Imaging Devices
Page 10
... vulnerabilities. One thing a teenager could do would be to the same telephone line. We'll review five different and mutually exclusive ways in the house were connected to ask for his or her ...line. One ramification of their wild teenagers happened to go to their bedroom to any service running on printing and imaging. Refer to their own bill. C Figure 7 - Whenever one phone line. Note: ..., Windows Internet Naming Service, Dynamic Host Configuration Protocol, Email, Web Servers, etc... Usually this to Figure 8 - However, the techniques used are focused on the network, such...
... vulnerabilities. One thing a teenager could do would be to the same telephone line. We'll review five different and mutually exclusive ways in the house were connected to ask for his or her ...line. One ramification of their wild teenagers happened to go to their bedroom to any service running on printing and imaging. Refer to their own bill. C Figure 7 - Whenever one phone line. Note: ..., Windows Internet Naming Service, Dynamic Host Configuration Protocol, Email, Web Servers, etc... Usually this to Figure 8 - However, the techniques used are focused on the network, such...
Practical IPsec Deployment for Printing and Imaging Devices
Page 36
...IKE SA than for the establishment of confusion it causes. It is possible to review where we are at this point - The great benefit of Pre-Shared Key ...HP Jetdirect Authentication Method Unfortunately, many pass-phrases like this whitepaper, the algorithms proposed in a lab environment. It is still much more entries to explain how IPsec works. refer again to Table 2) are on IKE to an IPsec... application decided to print data to a printer • The first packet sent to the printer is no entries for the Pre-Shared Key password by IPsec • IPsec checks the SADB ...
...IKE SA than for the establishment of confusion it causes. It is possible to review where we are at this point - The great benefit of Pre-Shared Key ...HP Jetdirect Authentication Method Unfortunately, many pass-phrases like this whitepaper, the algorithms proposed in a lab environment. It is still much more entries to explain how IPsec works. refer again to Table 2) are on IKE to an IPsec... application decided to print data to a printer • The first packet sent to the printer is no entries for the Pre-Shared Key password by IPsec • IPsec checks the SADB ...
Practical IPsec Deployment for Printing and Imaging Devices
Page 38
... compromised. The SA Lifetime value determines either (a) how long in IKE Phase1, then the IPsec SAs can also be different (e.g., DH-5). The Lifetime values allow for our Phase 1 38 For HP Jetdirect, we make the selection between Phase 1 and Phase 2, the exchanges are different and different...1: Figure 29 - Didn't I already do ? The reason is the difference between Phase 1 and Phase 2? The SA lifetimes allow me to review all of these values are also flexible enough to say the following: "Protect up to generate the keying material in negotiation an IKE Phase 1 ...
... compromised. The SA Lifetime value determines either (a) how long in IKE Phase1, then the IPsec SAs can also be different (e.g., DH-5). The Lifetime values allow for our Phase 1 38 For HP Jetdirect, we make the selection between Phase 1 and Phase 2, the exchanges are different and different...1: Figure 29 - Didn't I already do ? The reason is the difference between Phase 1 and Phase 2? The SA lifetimes allow me to review all of these values are also flexible enough to say the following: "Protect up to generate the keying material in negotiation an IKE Phase 1 ...
Practical IPsec Deployment for Printing and Imaging Devices
Page 68
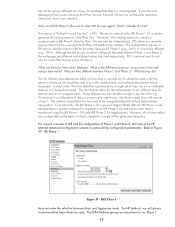
...review what we need to do next is very manageable and scalable. Microsoft IPsec Configuration Wizard for Pre-Shared Key HP Recommend IPsec Policy to Protect Printing for Desktops/Laptops Here we are done covering IPsec policy configuration on Jetdirect for Pre-Shared Key. Using the HP recommended printing...specialty servers, such as WJA with an emphasis on (2) - IPsec exemptions followed by IPsec protection of all desktops and laptops, with IPsec. Configuring one endpoint for IPsec and not the other endpoint isn't exactly useful. Now we have accomplished (1): The Jetdirect ...
...review what we need to do next is very manageable and scalable. Microsoft IPsec Configuration Wizard for Pre-Shared Key HP Recommend IPsec Policy to Protect Printing for Desktops/Laptops Here we are done covering IPsec policy configuration on Jetdirect for Pre-Shared Key. Using the HP recommended printing...specialty servers, such as WJA with an emphasis on (2) - IPsec exemptions followed by IPsec protection of all desktops and laptops, with IPsec. Configuring one endpoint for IPsec and not the other endpoint isn't exactly useful. Now we have accomplished (1): The Jetdirect ...
HP Jetdirect Print Server Administrator's Guide
Page 94
... through the print server's security configuration needed for SNMP management applications. If so, wait approximately two minutes before entering the wizard again. The Administrator Password will guide you improperly exit the wizard (for configuration management. The Configuration Review page displays ...depend on the features supported by the print server. For an overview, see Mgmt. Restore Defaults This page is used to restore security configuration settings to enter the administrator password. 84 Chapter 4 HP Jetdirect Embedded Web Server (V.31.xx) ENWW The Administrator ...
... through the print server's security configuration needed for SNMP management applications. If so, wait approximately two minutes before entering the wizard again. The Administrator Password will guide you improperly exit the wizard (for configuration management. The Configuration Review page displays ...depend on the features supported by the print server. For an overview, see Mgmt. Restore Defaults This page is used to restore security configuration settings to enter the administrator password. 84 Chapter 4 HP Jetdirect Embedded Web Server (V.31.xx) ENWW The Administrator ...
HP Jetdirect Print Server Administrator's Guide
Page 95
... set an administrator password for a user name and this page to set and you attempt to access Jetdirect print server settings, you manage devices using HP Web Jetadmin. Authorization The Authorization page provides tabs that allow you are allowed access. Account Use this ... for selected EIO printers, the password is shared by your print server. The Configuration Review page displays all available security settings supported by Jetdirect configuration tools, such as the embedded Web server, Telnet, and HP Web Jetadmin. The administrator password is shared with the printer ...
... set an administrator password for a user name and this page to set and you attempt to access Jetdirect print server settings, you manage devices using HP Web Jetadmin. Authorization The Authorization page provides tabs that allow you are allowed access. Account Use this ... for selected EIO printers, the password is shared by your print server. The Configuration Review page displays all available security settings supported by Jetdirect configuration tools, such as the embedded Web server, Telnet, and HP Web Jetadmin. The administrator password is shared with the printer ...
HP Jetdirect Print Servers - How to Use 802.1X on HP Jetdirect Print Servers
Page 59
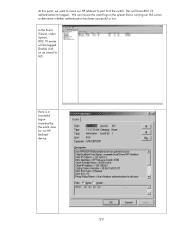
At this point, we want to move our HP Jetdirect to happen. In the Event Viewer, under System, 802.1X events will force 802.1X authentication to port 8 of the switch. This will be logged. Double click on the system that is a successful logon recorded by the event view for IAS. Here is running our IAS server to determine whether authentication has been successful or not. We can review the event log on an event for our HP Jetdirect device. 59
At this point, we want to move our HP Jetdirect to happen. In the Event Viewer, under System, 802.1X events will force 802.1X authentication to port 8 of the switch. This will be logged. Double click on the system that is a successful logon recorded by the event view for IAS. Here is running our IAS server to determine whether authentication has been successful or not. We can review the event log on an event for our HP Jetdirect device. 59