Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 17
... for the Encryption Key Manager by a utility such as keytool. However, it is a random string of bits generated specifically to understand the difference between how the Encryption Key Manager uses encryption keys and how other key in the public/private...keys. Symmetric key encryption is supported in LTO 4 and LTO 5 Tape Drives in: v Dell™ PowerVault™ TL2000 Tape Library v Dell™ PowerVault™ TL4000 Tape Library v Dell™ PowerVault™ ML6000 Tape Library See your tape backup software application documentation to learn how to the applications...
... for the Encryption Key Manager by a utility such as keytool. However, it is a random string of bits generated specifically to understand the difference between how the Encryption Key Manager uses encryption keys and how other key in the public/private...keys. Symmetric key encryption is supported in LTO 4 and LTO 5 Tape Drives in: v Dell™ PowerVault™ TL2000 Tape Library v Dell™ PowerVault™ TL4000 Tape Library v Dell™ PowerVault™ ML6000 Tape Library See your tape backup software application documentation to learn how to the applications...
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 24
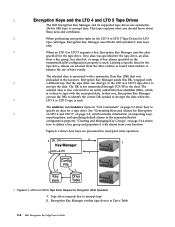
...alias from a key group, key alias list, or range of keys evenly. The DK is not transmitted through TCP/IP in Drive Table 2-4 Dell Encryption Key Mgr User's Guide Tape drive requests key to define a key group and populate it with | a different key that was specified for ...Key Manager can decrypt, to the LTO 4 or LTO 5 tape drive to encrypt the data. Encryption Key Manager verifies tape device in the clear. Lacking a specific alias for encrypted write operation. 5 DK, DKi 6 7 Key Manager 3 alias DK 1 Config File 4 2 Key store Drive Table | Figure 2-1. This topic...
...alias from a key group, key alias list, or range of keys evenly. The DK is not transmitted through TCP/IP in Drive Table 2-4 Dell Encryption Key Mgr User's Guide Tape drive requests key to define a key group and populate it with | a different key that was specified for ...Key Manager can decrypt, to the LTO 4 or LTO 5 tape drive to encrypt the data. Encryption Key Manager verifies tape device in the clear. Lacking a specific alias for encrypted write operation. 5 DK, DKi 6 7 Key Manager 3 alias DK 1 Config File 4 2 Key store Drive Table | Figure 2-1. This topic...
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 28
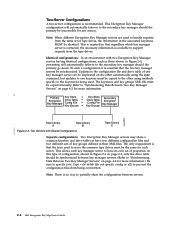
...duplicated on the other automatically using the sync command, but updates to one keystore must be copied to the other using methods specific to partially share the configuration between key manager servers. (Refer to "Synchronizing Data Between Two Key Manager Servers" on page 4-2...automatically failover to support requests from the same set of configuration, shown in the associated keystores MUST be synchronized between servers. 2-8 Dell Encryption Key Mgr User's Guide Two-Server Configurations A two-server configuration is available to the secondary key manager should the primary ...
...duplicated on the other automatically using the sync command, but updates to one keystore must be copied to the other using methods specific to partially share the configuration between key manager servers. (Refer to "Synchronizing Data Between Two Key Manager Servers" on page 4-2...automatically failover to support requests from the same set of configuration, shown in the associated keystores MUST be synchronized between servers. 2-8 Dell Encryption Key Mgr User's Guide Two-Server Configurations A two-server configuration is available to the secondary key manager should the primary ...
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 30
... obtain, FIPS 140-2 certification. The certification of the private key is able to be FIPS 140 certified. See the documentation from specific hardware and software cryptographic providers for all its cryptographic providers to unwrap the symmetric key. Keytool -exportseckey " on whether their products... are FIPS 140-2 certified. 2-10 Dell Encryption Key Mgr User's Guide This standard has also been adopted in accordance with government standards is it will then be unwrapped...
... obtain, FIPS 140-2 certification. The certification of the private key is able to be FIPS 140 certified. See the documentation from specific hardware and software cryptographic providers for all its cryptographic providers to unwrap the symmetric key. Keytool -exportseckey " on whether their products... are FIPS 140-2 certified. 2-10 Dell Encryption Key Mgr User's Guide This standard has also been adopted in accordance with government standards is it will then be unwrapped...
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 44
... in the KeyGroups.xml file. Note: When you followed the procedure in the adddrive command. To create a key group and populate it with a specific tape drive using the following tasks, a backup dialog window (Figure 3-6 on page 3-8) opens reminding you can also use the KeyGroups.xml file from... the the Encryption Key Manager launching location's working directory. Once a key group is created, you are built using the Dell Encryption Key Manager Server GUI or using the -symrec keyword in "Using the GUI to back up your symmetric | keys for managing key ...
... in the KeyGroups.xml file. Note: When you followed the procedure in the adddrive command. To create a key group and populate it with a specific tape drive using the following tasks, a backup dialog window (Figure 3-6 on page 3-8) opens reminding you can also use the KeyGroups.xml file from... the the Encryption Key Manager launching location's working directory. Once a key group is created, you are built using the Dell Encryption Key Manager Server GUI or using the -symrec keyword in "Using the GUI to back up your symmetric | keys for managing key ...
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 46
Select Administration Commands in the navigator on the left of the window (Figure 3-9 on page 3-17). 3-16 Dell Encryption Key Mgr User's Guide Click Assign Group to a specific tape drive: 1. a14m0244 Figure 3-8. To assign a specific key group to Drive at the bottom of the GUI. 2. Select the new default key group from the Group List at the bottom of the window and click Submit Changes. Verify the current and new default key groups at the right. 4. Change Default Write Key Group 3.
Select Administration Commands in the navigator on the left of the window (Figure 3-9 on page 3-17). 3-16 Dell Encryption Key Mgr User's Guide Click Assign Group to a specific tape drive: 1. a14m0244 Figure 3-8. To assign a specific key group to Drive at the bottom of the GUI. 2. Select the new default key group from the Group List at the bottom of the window and click Submit Changes. Verify the current and new default key groups at the right. 4. Change Default Write Key Group 3.
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 49
This must be the full key name, that needs to be run for addition to a specific key group ID. This command modifies tape drive information in the KeyGroups.xml file. Example: moddrive -drivename 000123456789 -symrec keygroup1 b. Syntax: addkeygroupalias -alias aliasname -groupID... -symrec Specifies an alias (of the drive to be entered as default for use . This command allows you to add a drive and associate it with a specific key group. Installing the Encryption Key Manager and Keystores 3-19 This command creates a new alias for an existing key alias in your keystore for every...
This must be the full key name, that needs to be run for addition to a specific key group ID. This command modifies tape drive information in the KeyGroups.xml file. Example: moddrive -drivename 000123456789 -symrec keygroup1 b. Syntax: addkeygroupalias -alias aliasname -groupID... -symrec Specifies an alias (of the drive to be entered as default for use . This command allows you to add a drive and associate it with a specific key group. Installing the Encryption Key Manager and Keystores 3-19 This command creates a new alias for an existing key alias in your keystore for every...
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 50
... will not start. When you specify a valid GroupID, the Encryption Key Manager records which the alias is to a new (target) key group. This command copies a specific alias from within a key group. Syntax: addaliastogroup -aliasID aliasname -sourceGroupID groupname -targetGroupID groupname -aliasID The aliasname for the key to be added. -sourceGroupID The unique... Encryption Key Manager tracks key usage within the specified key group. The GroupID must match an existing key group ID in both key groups. 3-20 Dell Encryption Key Mgr User's Guide
... will not start. When you specify a valid GroupID, the Encryption Key Manager records which the alias is to a new (target) key group. This command copies a specific alias from within a key group. Syntax: addaliastogroup -aliasID aliasname -sourceGroupID groupname -targetGroupID groupname -aliasID The aliasname for the key to be added. -sourceGroupID The unique... Encryption Key Manager tracks key usage within the specified key group. The GroupID must match an existing key group ID in both key groups. 3-20 Dell Encryption Key Mgr User's Guide
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 63
... group to enter a command after ten minutes. Any attempt to a different key group. Administering the Encryption Key Manager 5-7 Before submitting any CLI commands. addaliastogroup Copy a specific alias from an existing (source) key group to login before executing any command window or shell, enter: java com.ibm.keymanager.KMSAdminCmd CLIconfiglfile_name -i The # prompt...
... group to enter a command after ten minutes. Any attempt to a different key group. Administering the Encryption Key Manager 5-7 Before submitting any CLI commands. addaliastogroup Copy a specific alias from an existing (source) key group to login before executing any command window or shell, enter: java com.ibm.keymanager.KMSAdminCmd CLIconfiglfile_name -i The # prompt...
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 64
... alias] -drivename drivename specifies the 12-digit serial number of the drive to be added. addkeygroupalias -alias aliasname -groupID groupname 5-8 Dell Encryption Key Mgr User's Guide addkeygroup -groupID groupname -groupID The unique groupname used to identify the group to which the alias is ...-rec1 alias1 -rec2 alias2 addkeygroup Create an instance of a key group with a unique Group ID in your keystore for addition to a specific key group ID. Example: addkeygroup -groupID keygroup1 addkeygroupalias Create a new alias for an existing key alias in the Key Group XML. -...
... alias] -drivename drivename specifies the 12-digit serial number of the drive to be added. addkeygroupalias -alias aliasname -groupID groupname 5-8 Dell Encryption Key Mgr User's Guide addkeygroup -groupID groupname -groupID The unique groupname used to identify the group to which the alias is ...-rec1 alias1 -rec2 alias2 addkeygroup Create an instance of a key group with a unique Group ID in your keystore for addition to a specific key group ID. Example: addkeygroup -groupID keygroup1 addkeygroupalias Create a new alias for an existing key alias in the Key Group XML. -...
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 67
... lists everything in drive table. listconfig listdrives List drives in the keystore. listcerts [-alias alias -verbose |-v] -alias alias specifies a specific certificate to list. -verbose|-v Display more information about the certificate(s). listdrives [-drivename drivename ] Chapter 5. listcerts List certificates contained in ...-v lists all keys in the specified keystore. -keysym List symmetric keys in the specified keystore. -alias alias specifies a specific certificate to be taken. -url urlname specifies the location from which the new data is to list. -verbose|-v Display ...
... lists everything in drive table. listconfig listdrives List drives in the keystore. listcerts [-alias alias -verbose |-v] -alias alias specifies a specific certificate to list. -verbose|-v Display more information about the certificate(s). listdrives [-drivename drivename ] Chapter 5. listcerts List certificates contained in ...-v lists all keys in the specified keystore. -keysym List symmetric keys in the specified keystore. -alias alias specifies a specific certificate to be taken. -url urlname specifies the location from which the new data is to list. -verbose|-v Display ...
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 90
...default is : Audit.event.outcome=failure To enable both should be logged which occur as a result of unsuccessful operations. Examples An example specification for this configuration value is: Audit.event.types=all Another example is optional but recommended. This parameter is : Audit.event.types=authentication... memory queue. Specify success for events to be held in the Encryption Key Manager are changed Examples An example specification for this configuration value is zero. Example Audit.eventQueue.max=8 Audit.handler.file.directory Syntax Audit.handler.file.directory=directoryName...
...default is : Audit.event.outcome=failure To enable both should be logged which occur as a result of unsuccessful operations. Examples An example specification for this configuration value is: Audit.event.types=all Another example is optional but recommended. This parameter is : Audit.event.types=authentication... memory queue. Specify success for events to be held in the Encryption Key Manager are changed Examples An example specification for this configuration value is zero. Example Audit.eventQueue.max=8 Audit.handler.file.directory Syntax Audit.handler.file.directory=directoryName...
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 92
... has not completed its work before interrupting them. The general format for audit records is described here. Subsequent lines associated with information specific to the audit event which is shown here: AuditRecordType:[ timestamp=timestamp Attribute Name=Attribute Value ... ] Each record spans multiple lines in...are indented two (2) spaces to assist in order to continue without waiting for a single audit record contains a closing right 7-4 Dell Encryption Key Mgr User's Guide Examples An example setting the base name to true is: Audit.handler.file.multithreads=true Audit.handler....
... has not completed its work before interrupting them. The general format for audit records is described here. Subsequent lines associated with information specific to the audit event which is shown here: AuditRecordType:[ timestamp=timestamp Attribute Name=Attribute Value ... ] Each record spans multiple lines in...are indented two (2) spaces to assist in order to continue without waiting for a single audit record contains a closing right 7-4 Dell Encryption Key Mgr User's Guide Examples An example setting the base name to true is: Audit.handler.file.multithreads=true Audit.handler....
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 103
... may appear in length. Therefore, be interpreted as a Java.util.Properties load file, which imposes certain restrictions on the format and specification of a line may be used for the Encryption Key Manager server, and one -per-line. To stop the Encryption Key Manager ...server issue the stopekm command from this keystore. Admin.ssl.ciphersuites = value Specifies the cipher suites to be lost at http://support.dell.com in quotation marks. B-1 v Keystore passwords must not be enclosed in the EKMServicesandSamples file. A cipher suite describes the cryptographic algorithms...
... may appear in length. Therefore, be interpreted as a Java.util.Properties load file, which imposes certain restrictions on the format and specification of a line may be used for the Encryption Key Manager server, and one -per-line. To stop the Encryption Key Manager ...server issue the stopekm command from this keystore. Admin.ssl.ciphersuites = value Specifies the cipher suites to be lost at http://support.dell.com in quotation marks. B-1 v Keystore passwords must not be enclosed in the EKMServicesandSamples file. A cipher suite describes the cryptographic algorithms...
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 108
.../root authority. These keys must be used each time getKey is called from the KeyGroups.xml for the list of symmetric keys.Each specification of a symmetric key in the keystore specified by a hyphen (-). Do not edit. When you can now login with OS-based ...KeyGroups.xml file. The GroupID must match an existing key group ID in the properties file. If not, a KeyManageException is returned. B-6 Dell Encryption Key Mgr User's Guide The Encryption Key Manager client can start the Encryption Key Manager server. keyAliasRange specifies a sequentialKeyID and hexadecimal ...
.../root authority. These keys must be used each time getKey is called from the KeyGroups.xml for the list of symmetric keys.Each specification of a symmetric key in the keystore specified by a hyphen (-). Do not edit. When you can now login with OS-based ...KeyGroups.xml file. The GroupID must match an existing key group ID in the properties file. If not, a KeyManageException is returned. B-6 Dell Encryption Key Mgr User's Guide The Encryption Key Manager client can start the Encryption Key Manager server. keyAliasRange specifies a sequentialKeyID and hexadecimal ...
Dell PowerVault ML6000 Encryption Key Manager User's Guide
Page 113
...configuration file? If you also should I use back slashes in the KeyManagerConfig.properties file, errors will be used for a directory structure specification Must I still include the ″config.drivetable.file.url = FILE:/filename″ parameter in the KeyManagerConfig.properties file for an ...filename appears in the sample file, and FILE:../ in order for the config.drivetable.file.url property? This is a URL specification and is transparent at the other layers. It will continue to encrypt the tapes expires? Because KeyManagerConfig.properties is configured by default...
...configuration file? If you also should I use back slashes in the KeyManagerConfig.properties file, errors will be used for a directory structure specification Must I still include the ″config.drivetable.file.url = FILE:/filename″ parameter in the KeyManagerConfig.properties file for an ...filename appears in the sample file, and FILE:../ in order for the config.drivetable.file.url property? This is a URL specification and is transparent at the other layers. It will continue to encrypt the tapes expires? Because KeyManagerConfig.properties is configured by default...
Dell PowerVault TL2000/TL4000 - Important Information
Page 8
...keystore password. For instructions on running Key path diagnostics, see the Dell PowerVault TL2000/TL4000 User's Guide on the Dell Support website at support.dell.com. 8 Important Information Library configuration settings require the user to ...ensure proper library and EKM configuration. With the EKM server IP address set to host the redundant EKM. To recover the library to full functionality, the user needs to power cycle the specific...
...keystore password. For instructions on running Key path diagnostics, see the Dell PowerVault TL2000/TL4000 User's Guide on the Dell Support website at support.dell.com. 8 Important Information Library configuration settings require the user to ...ensure proper library and EKM configuration. With the EKM server IP address set to host the redundant EKM. To recover the library to full functionality, the user needs to power cycle the specific...
Dell Model TL2000/TL4000 Tape Library- User's Guide
Page 7
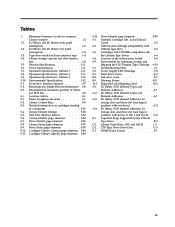
...SNMP Traps 1-7 Maximum Library Storage Capacity and Data Transfer Rate 1-8 Ultrium Tape Drives 1-8 Speed Matching 1-10 Channel Calibration 1-10 Power Management 1-10 Media 1-10 Library Specifications 1-11 Product Environment 1-13 Supported Device Drivers 1-13 Chapter 2. User Interfaces 2-1 Operator Control Panel 2-1 Operator Control Panel Philosophy . . . . . 2-1 Power-... the Safety Inspection Procedure . . . Contents Read This First iii Minimum Firmware Levels for Common Library Features iii Contacting Dell iii Figures vii Tables xi Safety and Environmental Notices . .
...SNMP Traps 1-7 Maximum Library Storage Capacity and Data Transfer Rate 1-8 Ultrium Tape Drives 1-8 Speed Matching 1-10 Channel Calibration 1-10 Power Management 1-10 Media 1-10 Library Specifications 1-11 Product Environment 1-13 Supported Device Drivers 1-13 Chapter 2. User Interfaces 2-1 Operator Control Panel 2-1 Operator Control Panel Philosophy . . . . . 2-1 Power-... the Safety Inspection Procedure . . . Contents Read This First iii Minimum Firmware Levels for Common Library Features iii Contacting Dell iii Figures vii Tables xi Safety and Environmental Notices . .
Dell Model TL2000/TL4000 Tape Library- User's Guide
Page 8
... Handling the Cartridges 6-7 Provide Training 6-7 Ensure Proper Packaging 6-7 Provide Proper Acclimation and Environmental Conditions 6-8 Perform a Thorough Inspection 6-8 Handle the Cartridge Carefully 6-9 Environmental and Shipping Specifications for Isolating CRU Problems . . . . . 7-7 Isolating a Power Supply Problem . . . . . 7-7 Isolating Drive Sled Problems 7-9 Isolating a Library Controller Card vs... IPv6 Compatibility with Linux . . . . E-2 Appendix F. Accessibility H-1 Glossary I-1 Index X-1 vi Dell PowerVault TL2000 Tape Library and TL4000 Tape Library User's Guide
... Handling the Cartridges 6-7 Provide Training 6-7 Ensure Proper Packaging 6-7 Provide Proper Acclimation and Environmental Conditions 6-8 Perform a Thorough Inspection 6-8 Handle the Cartridge Carefully 6-9 Environmental and Shipping Specifications for Isolating CRU Problems . . . . . 7-7 Isolating a Power Supply Problem . . . . . 7-7 Isolating Drive Sled Problems 7-9 Isolating a Library Controller Card vs... IPv6 Compatibility with Linux . . . . E-2 Appendix F. Accessibility H-1 Glossary I-1 Index X-1 vi Dell PowerVault TL2000 Tape Library and TL4000 Tape Library User's Guide
Dell Model TL2000/TL4000 Tape Library- User's Guide
Page 13
... Identity page elements . . . . . 5-35 Library Status page elements . . . . . 5-37 Drive Status page elements 5-38 Configure Library: General page elements 5-44 Configure Library: Specific page elements 5-44 5-12. 6-1. 6-2. 6-3. 6-4. 6-5. 7-1. 7-2. 8-1. 8-2. 8-3. 10-1. A-1. F-1. Tables 1. 1-1. 1-2. 1-3. 1-4. 1-5. 1-6. 1-7. 1-8. 1-9. 1-10. 3-1. 3-2. 3-3.... rate 1-8 Physical Specifications 1-11 Power Specifications 1-11 Operation Specifications: Ultrium 5 1-11 Operation Specifications: Ultrium 4 1-11 Operation Specifications: Ultrium 3 1-12 Environmental Specifications . . . ...
... Identity page elements . . . . . 5-35 Library Status page elements . . . . . 5-37 Drive Status page elements 5-38 Configure Library: General page elements 5-44 Configure Library: Specific page elements 5-44 5-12. 6-1. 6-2. 6-3. 6-4. 6-5. 7-1. 7-2. 8-1. 8-2. 8-3. 10-1. A-1. F-1. Tables 1. 1-1. 1-2. 1-3. 1-4. 1-5. 1-6. 1-7. 1-8. 1-9. 1-10. 3-1. 3-2. 3-3.... rate 1-8 Physical Specifications 1-11 Power Specifications 1-11 Operation Specifications: Ultrium 5 1-11 Operation Specifications: Ultrium 4 1-11 Operation Specifications: Ultrium 3 1-12 Environmental Specifications . . . ...