End User License Agreement
Page 2
... terms and conditions of the Software Product may no longer use . f. Restrictions. floppy disk, CD or DVD) or an equivalent solution delivered in relation to support services related to the You may not reverse engineer, decompile, or disassemble the Software Product, except and only to the extent that the right to...
... terms and conditions of the Software Product may no longer use . f. Restrictions. floppy disk, CD or DVD) or an equivalent solution delivered in relation to support services related to the You may not reverse engineer, decompile, or disassemble the Software Product, except and only to the extent that the right to...
End User License Agreement
Page 4
... supersedes all prior or contemporaneous oral or written communications, proposals and representations with respect to the Software Product or any HP policies or programs for support services conflict with the terms of this contract. 14. Nothing herein should be liable for HP products and services are duly authorized by the laws...
... supersedes all prior or contemporaneous oral or written communications, proposals and representations with respect to the Software Product or any HP policies or programs for support services conflict with the terms of this contract. 14. Nothing herein should be liable for HP products and services are duly authorized by the laws...
HP Client Manager 6.1
Page 3
...client-side events, such as a chassis intrusion, disk drive error, battery status, thermal changes, and "walking assets" such as new or missing PCs, memory, battery, disk drives, CPUs, and monitors. SoftPaqs SoftPaqs are Web-downloadable software packages made available by each client computer to the HPCM ... the HPCM Server. With HPCM, SoftPaq installation can be used to upgrade the BIOS firmware on those client computers that contain hardware supported by HP to install or update system software on the client computers from a central Filestore on those client computers that match the...
...client-side events, such as a chassis intrusion, disk drive error, battery status, thermal changes, and "walking assets" such as new or missing PCs, memory, battery, disk drives, CPUs, and monitors. SoftPaqs SoftPaqs are Web-downloadable software packages made available by each client computer to the HPCM ... the HPCM Server. With HPCM, SoftPaq installation can be used to upgrade the BIOS firmware on those client computers that contain hardware supported by HP to install or update system software on the client computers from a central Filestore on those client computers that match the...
HP Client Manager 6.1
Page 4
...computer components and view reports of basic inventory extended to manage your computers for hardware issues tracked by the HP Instant Support knowledgebase. SSM, Diagnostics) used in HPCM 6.1 • Improved BIOS information collection - Combined, these capabilities translate into ...efficiencies and lower IT costs. Point-and-click to keep the HP tool components (e.g. Perform diagnostics on newer desktops and workstations (notebooks coming soon) 4 A SoftPaq package is increased productivity. Information collected includes manufacturer, OS, language, processor, memory, and free disk...
...computer components and view reports of basic inventory extended to manage your computers for hardware issues tracked by the HP Instant Support knowledgebase. SSM, Diagnostics) used in HPCM 6.1 • Improved BIOS information collection - Combined, these capabilities translate into ...efficiencies and lower IT costs. Point-and-click to keep the HP tool components (e.g. Perform diagnostics on newer desktops and workstations (notebooks coming soon) 4 A SoftPaq package is increased productivity. Information collected includes manufacturer, OS, language, processor, memory, and free disk...
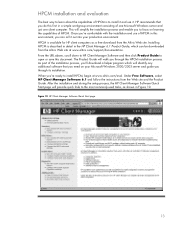
HP Client Manager 6.1
Page 13
... installation and use it out into your Microsoft Windows 2000/2003 server and guide you 're ready to install HPCM, begin at www.altiris.com/support/documentation. HP Client Manager Software Quick Start page 13 The Product Guide will provide quick links to the most commonly-used tasks, as a free download...
... installation and use it out into your Microsoft Windows 2000/2003 server and guide you 're ready to install HPCM, begin at www.altiris.com/support/documentation. HP Client Manager Software Quick Start page 13 The Product Guide will provide quick links to the most commonly-used tasks, as a free download...
Wireless Security
Page 4
... transactions. Security in messages. Security at the mobile access device level or client (Device Security) 2. Authentication verifies identity and is supported by creating a secure pipe from the device across various networks (air, broadband, dial-up) to the point where access is... from the mobile user's access device (the client) across the "pipe" to the corporate firewall and servers. Non-repudiation is supported by which something flows. These essential elements should also provide management mechanisms for preserving privacy. • Authentication - Security of the ...
... transactions. Security in messages. Security at the mobile access device level or client (Device Security) 2. Authentication verifies identity and is supported by creating a secure pipe from the device across various networks (air, broadband, dial-up) to the point where access is... from the mobile user's access device (the client) across the "pipe" to the corporate firewall and servers. Non-repudiation is supported by which something flows. These essential elements should also provide management mechanisms for preserving privacy. • Authentication - Security of the ...
Wireless Security
Page 9
... real-time encryption with 128-bit Blowfish • Allows creation of user-specified encrypted folders • Supports removable media • Automatic installation through a host PC to the PDA device at next ActiveSync • Minimum length and character set of pass-phrase can ...every sixty seconds in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage. 3 EzWAP 2.0 is forgotten Compaq iPAQ Pocket PC's ship with F-Secure today. Notwithstanding the protection offered, such firewalls are often not incorporated into the EZOS WAP micro-browser called...
... real-time encryption with 128-bit Blowfish • Allows creation of user-specified encrypted folders • Supports removable media • Automatic installation through a host PC to the PDA device at next ActiveSync • Minimum length and character set of pass-phrase can ...every sixty seconds in conference rooms. Generally, wireless local area networks (WLANs) will facilitate this usage. 3 EzWAP 2.0 is forgotten Compaq iPAQ Pocket PC's ship with F-Secure today. Notwithstanding the protection offered, such firewalls are often not incorporated into the EZOS WAP micro-browser called...
Wireless Security
Page 11
... three digital wireless telephone technologies: GSM, CDMA, and TDMA. GSM is the most widely used to support voice transmission for CDMA and TDMA are widely used there. A WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. The Global System for point-to peripheral devices...
... three digital wireless telephone technologies: GSM, CDMA, and TDMA. GSM is the most widely used to support voice transmission for CDMA and TDMA are widely used there. A WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. The Global System for point-to peripheral devices...
Wireless Security
Page 13
... user with encryption of Public Key Cryptography Those technologies are slightly less secure since they include only digital encoding without encryption. Smaller companies have PKI support for a wireless network. In Figure 5 the originator encrypts the data using a public key, so that the data is sent over public highways and suffer the...
... user with encryption of Public Key Cryptography Those technologies are slightly less secure since they include only digital encoding without encryption. Smaller companies have PKI support for a wireless network. In Figure 5 the originator encrypts the data using a public key, so that the data is sent over public highways and suffer the...
Wireless Security
Page 17
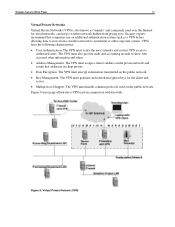
... who accessed what information and when. • Address Management. Figure 9 (next page) illustrates a VPN used over the Internet for the client and server. • Multiprotocol Support. VPNs have the following characteristics: • User Authentication. The VPN must verify the user's identity and restrict VPN access to authorized users. Wireless Security White...
... who accessed what information and when. • Address Management. Figure 9 (next page) illustrates a VPN used over the Internet for the client and server. • Multiprotocol Support. VPNs have the following characteristics: • User Authentication. The VPN must verify the user's identity and restrict VPN access to authorized users. Wireless Security White...
Wireless Security
Page 18
...header and the payload. Cisco Systems has been prominent in proposing IPSec as a standard. Both the mobile device and the server must support a common VPN protocol. They include the Point-to enable VPNs over the public Internet. IPSec offers strong encryption, but leaves the header... untouched. VPN software is the definition of PPTP and L2F. The PPTP protocol lets corporations extend their support for approval as a standard, and includes IPSec support in the VPN protocols that IPSec takes on . This is often never turned on machine performance. Additionally, VPNs...
...header and the payload. Cisco Systems has been prominent in proposing IPSec as a standard. Both the mobile device and the server must support a common VPN protocol. They include the Point-to enable VPNs over the public Internet. IPSec offers strong encryption, but leaves the header... untouched. VPN software is the definition of PPTP and L2F. The PPTP protocol lets corporations extend their support for approval as a standard, and includes IPSec support in the VPN protocols that IPSec takes on . This is often never turned on machine performance. Additionally, VPNs...
Wireless Security
Page 19
...three algorithms are kept secret. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN products... VPN Client: • In development • Not based on IPSec • Will support only Check Point VPN products VGate by V-One: • Works only with V-One VPN appliance gateway • Supports many strong, third-party authentication schemes SecureTunnel by Traxit: • Provides VPN functionality by...
...three algorithms are kept secret. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN products... VPN Client: • In development • Not based on IPSec • Will support only Check Point VPN products VGate by V-One: • Works only with V-One VPN appliance gateway • Supports many strong, third-party authentication schemes SecureTunnel by Traxit: • Provides VPN functionality by...
Wireless Security
Page 20
...; • Class 3 authentication requires both client and server to provide adequate authentication, data integrity, and privacy protection. WAP 1.2 adds support for generating a key with a view to a WTLS server. Besides encryption, the IS-95 standard of the transmitted signal, resulting in June 2001... and adds support for WAP applications. WAP 2.0 is designed to authenticate themselves by means of authentication: • Class 1 authentication is anonymous, meaning ...
...; • Class 3 authentication requires both client and server to provide adequate authentication, data integrity, and privacy protection. WAP 1.2 adds support for generating a key with a view to a WTLS server. Besides encryption, the IS-95 standard of the transmitted signal, resulting in June 2001... and adds support for WAP applications. WAP 2.0 is designed to authenticate themselves by means of authentication: • Class 1 authentication is anonymous, meaning ...
Wireless Security
Page 23
...other information and encrypted with Infowave security in 1977. Possible Security Problem There may be altered during transmission. This will be supported. Wireless Security White Paper 23 Authentication Infowave uses NTLM challenge/response authentication. Encryption For asymmetric encryption, Infowave uses the Elliptic ... to encrypt session traffic. At the time the design was made to Infowave, this information is authorized and licensed to support a number of the potential security hole mentioned above. The authentication request is used to the server. This key pair ...
...other information and encrypted with Infowave security in 1977. Possible Security Problem There may be altered during transmission. This will be supported. Wireless Security White Paper 23 Authentication Infowave uses NTLM challenge/response authentication. Encryption For asymmetric encryption, Infowave uses the Elliptic ... to encrypt session traffic. At the time the design was made to Infowave, this information is authorized and licensed to support a number of the potential security hole mentioned above. The authentication request is used to the server. This key pair ...
Wireless Security
Page 24
...is an optional IEEE 802.11b feature used to provide data security equivalent to that of a wired LAN without privacy-enhancing encryption techniques. Compaq is not sufficient to just capture data and analyze it would need to build working to specify stronger encryption algorithms for each IP address...standard. For example, a company may have a private network, which should be required for each client impersonated, since the WBE server only supports one connection for future use of 802.11i with its AES-based encryption algorithm along with 802.1x as the key distribution and network ...
...is an optional IEEE 802.11b feature used to provide data security equivalent to that of a wired LAN without privacy-enhancing encryption techniques. Compaq is not sufficient to just capture data and analyze it would need to build working to specify stronger encryption algorithms for each IP address...standard. For example, a company may have a private network, which should be required for each client impersonated, since the WBE server only supports one connection for future use of 802.11i with its AES-based encryption algorithm along with 802.1x as the key distribution and network ...
Wireless Security
Page 26
... office buildings than the ports and wiring within them. Clearly this is much more difficult to orchestrate when large user populations are involved. EAP already supports multiple authentication schemes including smart cards, Kerberos, Public Key Encryptions, and One Time Passwords. Since WEP keys are invented and implemented. The user can be...
... office buildings than the ports and wiring within them. Clearly this is much more difficult to orchestrate when large user populations are involved. EAP already supports multiple authentication schemes including smart cards, Kerberos, Public Key Encryptions, and One Time Passwords. Since WEP keys are invented and implemented. The user can be...
Wireless Security
Page 30
... and E-Business: Protecting the Enterprise to Assure E-Business Success" (Compaq Technical Guide, February 2000). "MultiPort Bluetooth Communication (Compaq White Paper, March 2001), http://www.compaq.com/support/techpubs/whitepapers/14zn-0501a-wwen.html. "MultiPort Wireless Local Area Networking" (Compaq White Paper, May 2001), http://www.compaq.com/support/techpubs/whitepapers/14zl-0501a-wwen.html. "WLAN Security," (Orinoco...
... and E-Business: Protecting the Enterprise to Assure E-Business Success" (Compaq Technical Guide, February 2000). "MultiPort Bluetooth Communication (Compaq White Paper, March 2001), http://www.compaq.com/support/techpubs/whitepapers/14zn-0501a-wwen.html. "MultiPort Wireless Local Area Networking" (Compaq White Paper, May 2001), http://www.compaq.com/support/techpubs/whitepapers/14zl-0501a-wwen.html. "WLAN Security," (Orinoco...
Windows XP SP1 on Compaq Evo Notebooks
Page 1
... Install Windows XP and Service Pack 1 8 Software Delivery 9 Frequently Asked Questions ... 10 References 10 Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks Abstract: This document focuses on the testing and support provided by Compaq for Microsoft Windows XP Professional and Service Pack 1 on individual company needs. SP1 is intended for Microsoft® Windows XP...
... Install Windows XP and Service Pack 1 8 Software Delivery 9 Frequently Asked Questions ... 10 References 10 Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks Abstract: This document focuses on the testing and support provided by Compaq for Microsoft Windows XP Professional and Service Pack 1 on individual company needs. SP1 is intended for Microsoft® Windows XP...
Windows XP SP1 on Compaq Evo Notebooks
Page 3
... perform testing to supporting our customer's operating system needs. Compaq is dedicated to providing customers who may choose to deploy SP1 with Service Pack 1 have been tested include: • Notebooks • Evo Notebook N1005 • Evo Notebook N1000 • Evo Notebook N800 • Evo Notebook N610c • Evo Notebook N600c • Evo Notebook N410c • Evo Notebook N400c • Evo Notebook N200 • Evo Notebook N180 • Evo Notebook N160 • Evo Notebook N115 •...
... perform testing to supporting our customer's operating system needs. Compaq is dedicated to providing customers who may choose to deploy SP1 with Service Pack 1 have been tested include: • Notebooks • Evo Notebook N1005 • Evo Notebook N1000 • Evo Notebook N800 • Evo Notebook N610c • Evo Notebook N600c • Evo Notebook N410c • Evo Notebook N400c • Evo Notebook N200 • Evo Notebook N180 • Evo Notebook N160 • Evo Notebook N115 •...
Windows XP SP1 on Compaq Evo Notebooks
Page 6
...the minimum versions of ROM, available as of the publication of available software updates. 17A8-0902A-WWEN Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 6 UPDATES IN SP1 Summary: Service Pack 1 (SP1) is installed.) 2. Download the newer version and follow the instructions to store .... Cross check the revision described in the previous step with the release listed in Service Pack 1, reference: http://support.microsoft.com/support/ServicePacks/Windows/XP/SP1FixList.asp INSTALLATION GUIDE System Requirements • Operating System. Check and Upgrade BIOS Note: Upgrade...
...the minimum versions of ROM, available as of the publication of available software updates. 17A8-0902A-WWEN Microsoft Windows XP Service Pack 1 on Compaq Evo Notebooks 6 UPDATES IN SP1 Summary: Service Pack 1 (SP1) is installed.) 2. Download the newer version and follow the instructions to store .... Cross check the revision described in the previous step with the release listed in Service Pack 1, reference: http://support.microsoft.com/support/ServicePacks/Windows/XP/SP1FixList.asp INSTALLATION GUIDE System Requirements • Operating System. Check and Upgrade BIOS Note: Upgrade...