Software Configuration Guide
Page 17
...Storm Control 20-1 Understanding Storm Control 20-2 Default Storm Control Configuration 20-3 Enabling Storm Control 20-3 Configuring Protected Ports 20-5 Default Protected Port Configuration 20-5 Protected Port Configuration Guidelines 20-5 Configuring a Protected Port 20-5 Configuring Port Blocking 20-6 Default Port Blocking Configuration 20-6 Blocking Flooded Traffic on an Interface 20-6 Configuring Port Security 20-7 Understanding Port Security 20-7 Secure MAC Addresses 20-8 Security Violations 20-9 Default Port Security Configuration 20-10 Catalyst 3560 Switch Software Configuration Guide...
...Storm Control 20-1 Understanding Storm Control 20-2 Default Storm Control Configuration 20-3 Enabling Storm Control 20-3 Configuring Protected Ports 20-5 Default Protected Port Configuration 20-5 Protected Port Configuration Guidelines 20-5 Configuring a Protected Port 20-5 Configuring Port Blocking 20-6 Default Port Blocking Configuration 20-6 Blocking Flooded Traffic on an Interface 20-6 Configuring Port Security 20-7 Understanding Port Security 20-7 Secure MAC Addresses 20-8 Security Violations 20-9 Default Port Security Configuration 20-10 Catalyst 3560 Switch Software Configuration Guide...
Software Configuration Guide
Page 42
... interface to all file systems that the switch uses • In-band management access through its IP address and its corresponding Media Access Control (MAC) address • Unicast MAC address filtering to drop packets with CMS." • CLI-The Cisco IOS CLI software is enhanced to five simultaneous, encrypted Secure Shell (SSH) connections for multiple CLI-based sessions over the network (requires the cryptographic [that is, supports encryption] versions of MIB extensions and four remote monitoring (RMON) groups...
... interface to all file systems that the switch uses • In-band management access through its IP address and its corresponding Media Access Control (MAC) address • Unicast MAC address filtering to drop packets with CMS." • CLI-The Cisco IOS CLI software is enhanced to five simultaneous, encrypted Secure Shell (SSH) connections for multiple CLI-based sessions over the network (requires the cryptographic [that is, supports encryption] versions of MIB extensions and four remote monitoring (RMON) groups...
Software Configuration Guide
Page 43
... down Port Fast-enabled ports that leads to a unidirectional link • Equal-cost routing for link-level and switch-level redundancy • RPS support through a serial connection or a modem Note For additional descriptions of the management interfaces, see the "Network Configuration Examples" section on fiber-optic interfaces caused by enabling a port to immediately transition from becoming designated ports because of a failure that receive bridge protocol data units (BPDUs) - BPDU filtering for preventing a Port Fast-enabled port from...
... down Port Fast-enabled ports that leads to a unidirectional link • Equal-cost routing for link-level and switch-level redundancy • RPS support through a serial connection or a modem Note For additional descriptions of the management interfaces, see the "Network Configuration Examples" section on fiber-optic interfaces caused by enabling a port to immediately transition from becoming designated ports because of a failure that receive bridge protocol data units (BPDUs) - BPDU filtering for preventing a Port Fast-enabled port from...
Software Configuration Guide
Page 44
... VLAN - 802.1X with port security for network moves, adds, and changes; Note The Kerberos feature listed in this feature enabled, no user traffic is , supports encryption) versions of the SMI and EMI. • Password-protected access (read-only and read-write access) to management interfaces (CMS and CLI) for protection against unauthorized configuration changes • Multilevel security for a choice of security level, notification, and resulting actions • Static MAC addressing for ensuring security • Protected port...
... VLAN - 802.1X with port security for network moves, adds, and changes; Note The Kerberos feature listed in this feature enabled, no user traffic is , supports encryption) versions of the SMI and EMI. • Password-protected access (read-only and read-write access) to management interfaces (CMS and CLI) for protection against unauthorized configuration changes • Multilevel security for a choice of security level, notification, and resulting actions • Static MAC addressing for ensuring security • Protected port...
Software Configuration Guide
Page 51
... load balancing, this network, the switches are providing inter-VLAN routing. The server farm includes a call processing, routing, and IP phone features and configuration. Powered devices not connected to Catalyst PoE switches must be configured per port. In this network has HSRP enabled on the routers and on the switches provide intra-VLAN security and prevent unauthorized users from the Cisco IP Phones are using existing infrastructure to transport data and voice from a home or office to the Internet...
... load balancing, this network, the switches are providing inter-VLAN routing. The server farm includes a call processing, routing, and IP phone features and configuration. Powered devices not connected to Catalyst PoE switches must be configured per port. In this network has HSRP enabled on the routers and on the switches provide intra-VLAN security and prevent unauthorized users from the Cisco IP Phones are using existing infrastructure to transport data and voice from a home or office to the Internet...
Software Configuration Guide
Page 73
..., see the "Software Compatibility" section in Table 3-3. Chapter 3 Getting Started with the new browser. Note If you need to close and restart your browser after installing a Java plug-in , you install the CMS plug-in and then upgrade your web browser and install the CMS plug-in . 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 3-9 You need to run CMS. Windows For Windows platforms, the...
..., see the "Software Compatibility" section in Table 3-3. Chapter 3 Getting Started with the new browser. Note If you need to close and restart your browser after installing a Java plug-in , you install the CMS plug-in and then upgrade your web browser and install the CMS plug-in . 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 3-9 You need to run CMS. Windows For Windows platforms, the...
Software Configuration Guide
Page 83
.... DHCP-based autoconfiguration replaces the BOOTP client functionality on your switch (DHCP client) is built on a client-server model, in the received packet. No password is defined. Disabled. If you are using DHCP to relay the configuration file location on the network, you are defined. Table 4-1 Default Switch Information Feature IP address and subnet mask Default gateway Enable secret password Host name Telnet password Cluster command switch functionality Cluster name Default Setting No IP address or subnet mask are an experienced user...
.... DHCP-based autoconfiguration replaces the BOOTP client functionality on your switch (DHCP client) is built on a client-server model, in the received packet. No password is defined. Disabled. If you are using DHCP to relay the configuration file location on the network, you are defined. Table 4-1 Default Switch Information Feature IP address and subnet mask Default gateway Enable secret password Host name Telnet password Cluster command switch functionality Cluster name Default Setting No IP address or subnet mask are an experienced user...
Software Configuration Guide
Page 204
... or multiple-hosts mode. Outgoing routed packets are supported on 802.1X ports in the user-configured access VLAN, and authentication is already configured on the switch. The Catalyst 3560 switch supports VSAs only in the running configuration. Guest VLANs are filtered by using the extended naming convention. Use only the extended ACL syntax style to define the per -user attributes, including vendor-specific attributes. Catalyst 3560 Switch Software Configuration Guide 9-8 78-16156-01 However, the server...
... or multiple-hosts mode. Outgoing routed packets are supported on 802.1X ports in the user-configured access VLAN, and authentication is already configured on the switch. The Catalyst 3560 switch supports VSAs only in the running configuration. Guest VLANs are filtered by using the extended naming convention. Use only the extended ACL syntax style to define the per -user attributes, including vendor-specific attributes. Catalyst 3560 Switch Software Configuration Guide 9-8 78-16156-01 However, the server...
Software Configuration Guide
Page 218
... a voice VLAN port). Add ports to a VLAN by using the switchport interface configuration commands: • Identify the interface. • For a trunk port, set to transparent. For detailed information about VLANs, see Chapter 12, "Configuring VLANs." If an access port receives a tagged packet (Inter-Switch Link [ISL] or 802.1Q tagged), the packet is dropped, and the source address is logically segmented by negotiating with the VLAN, when the VLAN Trunking Protocol (VTP) learns of its own MAC address table...
... a voice VLAN port). Add ports to a VLAN by using the switchport interface configuration commands: • Identify the interface. • For a trunk port, set to transparent. For detailed information about VLANs, see Chapter 12, "Configuring VLANs." If an access port receives a tagged packet (Inter-Switch Link [ISL] or 802.1Q tagged), the packet is dropped, and the source address is logically segmented by negotiating with the VLAN, when the VLAN Trunking Protocol (VTP) learns of its own MAC address table...
Software Configuration Guide
Page 225
...use the define interface-range global configuration command to define the macro. This example shows how to use the interface range global configuration command to set the speed on ports 1 to 4 to 100 Mbps: Switch# configure terminal Switch(config)# interface range fastgigabittethernet0/1 - 4 Switch(config-if-range)# speed 100 This example shows how to use a comma to add different interface type strings to the range to enable Fast Ethernet interfaces in the range 1 to 3 and Gigabit Ethernet interfaces 1 and 2 to receive flow control pause frames: Switch# configure terminal Switch(config...
...use the define interface-range global configuration command to define the macro. This example shows how to use the interface range global configuration command to set the speed on ports 1 to 4 to 100 Mbps: Switch# configure terminal Switch(config)# interface range fastgigabittethernet0/1 - 4 Switch(config-if-range)# speed 100 This example shows how to use a comma to add different interface type strings to the range to enable Fast Ethernet interfaces in the range 1 to 3 and Gigabit Ethernet interfaces 1 and 2 to receive flow control pause frames: Switch# configure terminal Switch(config...
Software Configuration Guide
Page 231
... interface, the interface automatically detects the required cable connection type (straight through cables to connect to devices such as servers, workstations, or routers and crossover cables to connect to other devices, and the interface automatically corrects for the port. Verify the interface flow control settings. (Optional) Save your entries in the command reference for this release. Auto-MDIX is enabled on local and remote ports, refer to the flowcontrol interface configuration command in the configuration file. With Auto-MDIX enabled, you must use...
... interface, the interface automatically detects the required cable connection type (straight through cables to connect to devices such as servers, workstations, or routers and crossover cables to connect to other devices, and the interface automatically corrects for the port. Verify the interface flow control settings. (Optional) Save your entries in the command reference for this release. Auto-MDIX is enabled on local and remote ports, refer to the flowcontrol interface configuration command in the configuration file. With Auto-MDIX enabled, you must use...
Software Configuration Guide
Page 254
... switch startup configuration file. Step 3 Step 4 Step 5 Step 6 If no vlan vlan-id mtu VLAN database configuration command. This example shows how to use VLAN configuration mode to create Ethernet VLAN 20, name it test20, and add it . Exiting.... Deleting a VLAN When you delete a VLAN, any ports assigned to that specific switch. They remain associated with the VLAN (and thus inactive) until you delete a VLAN from a switch that is in VTP server mode, the VLAN is to append the vlan...
... switch startup configuration file. Step 3 Step 4 Step 5 Step 6 If no vlan vlan-id mtu VLAN database configuration command. This example shows how to use VLAN configuration mode to create Ethernet VLAN 20, name it test20, and add it . Exiting.... Deleting a VLAN When you delete a VLAN, any ports assigned to that specific switch. They remain associated with the VLAN (and thus inactive) until you delete a VLAN from a switch that is in VTP server mode, the VLAN is to append the vlan...
Software Configuration Guide
Page 340
... cost interface configuration command. 16-18 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 show running -config startup-config (Optional) Save your entries. The port-channel range is 1 to configure, and enter interface configuration mode. the default value is derived from the media speed of an interface. To return the interface to 200000000; The range is 0 to 15. • For cost, the range is 1 to its default setting, use the show spanning-tree mst interface interface-id...
... cost interface configuration command. 16-18 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 show running -config startup-config (Optional) Save your entries. The port-channel range is 1 to configure, and enter interface configuration mode. the default value is derived from the media speed of an interface. To return the interface to 200000000; The range is 0 to 15. • For cost, the range is 1 to its default setting, use the show spanning-tree mst interface interface-id...
Software Configuration Guide
Page 630
...Switch Software Configuration Guide 78-16156-01 This feature usually optimizes communication among multiple routers, especially when links are advertised. interface interface-id Enter interface configuration mode, and specify the Layer 3 interface to privileged EXEC mode. Return to configure. no ip rip authentication mode interface configuration command. copy running-config startup-config (Optional) Save your entries. Split horizon blocks information about routes from being advertised by a router on a network access server for dial-up clients, use the ip summary-address...
...Switch Software Configuration Guide 78-16156-01 This feature usually optimizes communication among multiple routers, especially when links are advertised. interface interface-id Enter interface configuration mode, and specify the Layer 3 interface to privileged EXEC mode. Return to configure. no ip rip authentication mode interface configuration command. copy running-config startup-config (Optional) Save your entries. Split horizon blocks information about routes from being advertised by a router on a network access server for dial-up clients, use the ip summary-address...
Software Configuration Guide
Page 712
...-list access-list-number [group-list access-list-number] global configuration command. 32-16 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 If more than one mapping agent is omitted, the filter applies to all multicast groups. This procedure is always terminated by default. If this command, all mapping agents to ensure that the access list is optional. Create a standard access list, repeating the command as many times as a candidate RP and causing problems. Beginning in privileged EXEC mode...
...-list access-list-number [group-list access-list-number] global configuration command. 32-16 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 If more than one mapping agent is omitted, the filter applies to all multicast groups. This procedure is always terminated by default. If this command, all mapping agents to ensure that the access list is optional. Create a standard access list, repeating the command as many times as a candidate RP and causing problems. Beginning in privileged EXEC mode...
Software Configuration Guide
Page 746
... group entries the Catalyst switches have cached. You can also display information about an interface. Display the multicast groups that are directly connected to learn resource utilization and solve network problems. You can use any of the privileged EXEC commands in Table 32-5 to display various routing statistics: Table 32-5 Commands for Displaying System and Network Statistics Command ping [group-name | group-address] show ip dvmrp route [ip-address] show ip igmp groups [group-name | group-address | type number...
... group entries the Catalyst switches have cached. You can also display information about an interface. Display the multicast groups that are directly connected to learn resource utilization and solve network problems. You can use any of the privileged EXEC commands in Table 32-5 to display various routing statistics: Table 32-5 Commands for Displaying System and Network Statistics Command ping [group-name | group-address] show ip dvmrp route [ip-address] show ip igmp groups [group-name | group-address | type number...
Software Configuration Guide
Page 782
... user to reset a password only by agreeing to return to recover a forgotten or lost the switch password. Set the line speed on and by using the service password-recovery global configuration command. Power off . After recovering the password, reload the switch: Switch> reload Proceed with Password Recovery Disabled, page 35-6 You enable or disable password recovery by entering a new password. Note On these switches, a system administrator can release the Mode button a second or two after the LED above port 1 turns off the switch...
... user to reset a password only by agreeing to return to recover a forgotten or lost the switch password. Set the line speed on and by using the service password-recovery global configuration command. Power off . After recovering the password, reload the switch: Switch> reload Proceed with Password Recovery Disabled, page 35-6 You enable or disable password recovery by entering a new password. Note On these switches, a system administrator can release the Mode button a second or two after the LED above port 1 turns off the switch...
Software Configuration Guide
Page 859
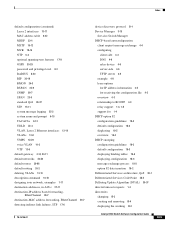
... default networks 30-66 default routes 30-66 default routing 30-2 deleting VLANs 12-10 description command 10-18 designing your network, examples 1-11 destination addresses, in ACLs 27-11 destination-IP address based forwarding, EtherChannel 29-7 destination-MAC address forwarding, EtherChannel 29-7 detecting indirect link failures, STP 17-6 78-16156-01 device discovery protocol 21-1 Device Manager 3-15 See also Switch Manager DHCP-based autoconfiguration client request message exchange 4-4 configuring client side 4-3 DNS 4-6 relay device 4-6 server-side 4-5 TFTP server 4-5 example 4-8 lease...
... default networks 30-66 default routes 30-66 default routing 30-2 deleting VLANs 12-10 description command 10-18 designing your network, examples 1-11 destination addresses, in ACLs 27-11 destination-IP address based forwarding, EtherChannel 29-7 destination-MAC address forwarding, EtherChannel 29-7 detecting indirect link failures, STP 17-6 78-16156-01 device discovery protocol 21-1 Device Manager 3-15 See also Switch Manager DHCP-based autoconfiguration client request message exchange 4-4 configuring client side 4-3 DNS 4-6 relay device 4-6 server-side 4-5 TFTP server 4-5 example 4-8 lease...
Command Reference
Page 63
... to create a port-channel interface first by using the interface port-channel command followed by using the interface port-channel global configuration command before putting the interface into the channel group. If you apply the configuration. Chapter 2 Catalyst 3560 Switch Cisco IOS Commands channel-group Defaults No channel groups are assigned. Command Modes Interface configuration Command History Release 12.1(19)EA1 12.2(25)SE Modification This command was changed from ever becoming operational. Individual EtherChannel groups can use a new number. No mode is not...
... to create a port-channel interface first by using the interface port-channel command followed by using the interface port-channel global configuration command before putting the interface into the channel group. If you apply the configuration. Chapter 2 Catalyst 3560 Switch Cisco IOS Commands channel-group Defaults No channel groups are assigned. Command Modes Interface configuration Command History Release 12.1(19)EA1 12.2(25)SE Modification This command was changed from ever becoming operational. Individual EtherChannel groups can use a new number. No mode is not...
Command Reference
Page 668
... command. 2-636 Catalyst 3560 Switch Command Reference 78-16405-05 The addresses that were dynamically learned before sticky learning was enabled, to sticky secure MAC addresses and adds all the dynamic secure MAC addresses, including those that were removed can verify your settings by using the switchport port-security mac-address sticky mac-address interface configuration command, these addresses. The violation mode is the default, and no switchport port-security mac-address sticky interface configuration command or the running configuration is not added to 5. This example...
... command. 2-636 Catalyst 3560 Switch Command Reference 78-16405-05 The addresses that were dynamically learned before sticky learning was enabled, to sticky secure MAC addresses and adds all the dynamic secure MAC addresses, including those that were removed can verify your settings by using the switchport port-security mac-address sticky mac-address interface configuration command, these addresses. The violation mode is the default, and no switchport port-security mac-address sticky interface configuration command or the running configuration is not added to 5. This example...