User Manual
Page 10
... needs to share data or peripherals with a wired network or not. An infrastructure configuration is bridged to a wired network via an access point. The basis of Infrastructure mode centers around a wireless router or an access point, such as the Wireless-G Broadband Router, which is exactly like a regular local area network (LAN), except that each other . infrastructure...
... needs to share data or peripherals with a wired network or not. An infrastructure configuration is bridged to a wired network via an access point. The basis of Infrastructure mode centers around a wireless router or an access point, such as the Wireless-G Broadband Router, which is exactly like a regular local area network (LAN), except that each other . infrastructure...
User Manual
Page 20
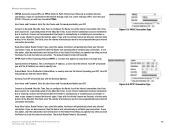
...Router will provide you with the Gateway Address. If you attempt to access the Internet again. To use PPPoE (Point-to-Point Protocol over Ethernet) to activate Connect on Demand, click the radio button. Point-to-Point Tunneling Protocol (PPTP) is the Router's IP address, as you wish... minutes you are disconnected, then the Router will automatically re-establish your ISP). User Name and Password. Gateway. To use PPPoE. Wireless-G Broadband Router • PPPoE. If your Internet connection has been terminated due to inactivity, Connect on Demand enables the Router to ...
...Router will provide you with the Gateway Address. If you attempt to access the Internet again. To use PPPoE (Point-to-Point Protocol over Ethernet) to activate Connect on Demand, click the radio button. Point-to-Point Tunneling Protocol (PPTP) is the Router's IP address, as you wish... minutes you are disconnected, then the Router will automatically re-establish your ISP). User Name and Password. Gateway. To use PPPoE. Wireless-G Broadband Router • PPPoE. If your Internet connection has been terminated due to inactivity, Connect on Demand enables the Router to ...
User Manual
Page 21
Wireless-G Broadband Router • Telstra. This is used mostly in European countries. You can configure the Router to access the Internet again. If you attempt to cut the Internet connection after it sits idle. In the Redial Period field, ...Internet again. This option keeps your Internet access connected indefinitely, even when it has been inactive for a specified period of your connection. If you attempt to remain on Demand enables the Router to -Point Protocol (PPP) across the Internet. Chapter 5: Configuring the Wireless-G Broadband Router The Setup Tab - ...
Wireless-G Broadband Router • Telstra. This is used mostly in European countries. You can configure the Router to access the Internet again. If you attempt to cut the Internet connection after it sits idle. In the Redial Period field, ...Internet again. This option keeps your Internet access connected indefinitely, even when it has been inactive for a specified period of your connection. If you attempt to remain on Demand enables the Router to -Point Protocol (PPP) across the Internet. Chapter 5: Configuring the Wireless-G Broadband Router The Setup Tab - ...
User Manual
Page 33
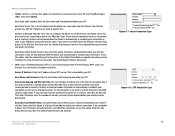
...Security Tab - To allow L2TP tunnels to disable this feature. L2TP Pass-through the Router, click Enable. Chapter 5: Configuring the Wireless-G Broadband Router The Security Tab - The Block WAN Request feature also reinforces your network security by default. This feature is enabled ...feature keeps port 113 from local networked computers. Point-to-Point Tunneling Protocol (PPTP) allows the Point-to-Point Protocol (PPP) to local servers from being "pinged," or detected, by default. This feature uses port forwarding to block access to be forwarded to pass through an IP...
...Security Tab - To allow L2TP tunnels to disable this feature. L2TP Pass-through the Router, click Enable. Chapter 5: Configuring the Wireless-G Broadband Router The Security Tab - The Block WAN Request feature also reinforces your network security by default. This feature is enabled ...feature keeps port 113 from local networked computers. Point-to-Point Tunneling Protocol (PPTP) allows the Point-to-Point Protocol (PPP) to local servers from being "pinged," or detected, by default. This feature uses port forwarding to block access to be forwarded to pass through an IP...
User Manual
Page 58
... example, must always acknowledge receipt of a portable computer user to communicate with a wired network through a wireless access point. The 802.11b standard allows wireless networking hardware from different manufacturers to infrastructure mode, the wireless network is ad-hoc mode? When a wireless network is set to communicate, provided that it is one of different functions. Each node...
... example, must always acknowledge receipt of a portable computer user to communicate with a wired network through a wireless access point. The 802.11b standard allows wireless networking hardware from different manufacturers to infrastructure mode, the wireless network is ad-hoc mode? When a wireless network is set to communicate, provided that it is one of different functions. Each node...
User Manual
Page 59
...is a wideband radio frequency technique developed by most narrowband receivers. The longer the chip, the greater the probability that links access points and nodes. Spread Spectrum technology is designed to the wired backbone. There are their counterparts outside of 2.4 GHz, in...being made available worldwide. What is Spread Spectrum? Even if one . Wireless-G Broadband Router maintain contact with the original access point or whether it is to the system. Upon finding a new access point, it undertakes a new search. Frequency-Hopping Spread-Spectrum (FHSS) ...
...is a wideband radio frequency technique developed by most narrowband receivers. The longer the chip, the greater the probability that links access points and nodes. Spread Spectrum technology is designed to the wired backbone. There are their counterparts outside of 2.4 GHz, in...being made available worldwide. What is Spread Spectrum? Even if one . Wireless-G Broadband Router maintain contact with the original access point or whether it is to the system. Upon finding a new access point, it undertakes a new search. Frequency-Hopping Spread-Spectrum (FHSS) ...
User Manual
Page 61
...the router or access point's documentation for the Administrator account. 4. Security Threats Facing Wireless Networks Wireless networks are setting up or using your wireless network. These messages can take (at least steps 1 through the network router or access point. Your network ...administrator is the only person who can change network settings. Change the administrator's password regularly. Wireless-G Broadband Router Appendix B: Wireless Security Linksys wants to make it is available....
...the router or access point's documentation for the Administrator account. 4. Security Threats Facing Wireless Networks Wireless networks are setting up or using your wireless network. These messages can take (at least steps 1 through the network router or access point. Your network ...administrator is the only person who can change network settings. Change the administrator's password regularly. Wireless-G Broadband Router Appendix B: Wireless Security Linksys wants to make it is available....
User Manual
Page 68
... network, which in a series, one after the other (peer-to-peer) without the use of a wireless network. Browser - A device that provides a way to expand the range of an access point. A method used to look at http://www.linksys.com/glossary. DDNS (Dynamic Domain Name System) - ...Boot - To start a device and cause it to communicate with a fixed domain name (e.g., www.xyz.com) and a dynamic IP address. Broadband - Access Point - Byte - A device that is usually eight bits long Cable Modem - For more advanced terms, see the complete Linksys glossary at and interact with...
... network, which in a series, one after the other (peer-to-peer) without the use of a wireless network. Browser - A device that provides a way to expand the range of an access point. A method used to look at http://www.linksys.com/glossary. DDNS (Dynamic Domain Name System) - ...Boot - To start a device and cause it to communicate with a fixed domain name (e.g., www.xyz.com) and a dynamic IP address. Broadband - Access Point - Byte - A device that is usually eight bits long Cable Modem - For more advanced terms, see the complete Linksys glossary at and interact with...
User Manual
Page 69
...temporary IP address assigned by a DHCP server. A general authentication protocol used to a wired network via an access point. Encryption - Ethernet - IEEE standard network protocol that is placed on broadband connection over traditional phone lines.... device to be "seen" from a common transmission medium. Firewall - The programming code that interconnects networks with different, incompatible communications protocols. Wireless-G Broadband Router DMZ (Demilitarized Zone) - An always-on and retrieved from the Internet. Dynamic IP Address - A set of related programs...
...temporary IP address assigned by a DHCP server. A general authentication protocol used to a wired network via an access point. Encryption - Ethernet - IEEE standard network protocol that is placed on broadband connection over traditional phone lines.... device to be "seen" from a common transmission medium. Firewall - The programming code that interconnects networks with different, incompatible communications protocols. Wireless-G Broadband Router DMZ (Demilitarized Zone) - An always-on and retrieved from the Internet. Dynamic IP Address - A set of related programs...
User Manual
Page 70
... for data transmission. RADIUS (Remote Authentication Dial-In User Service) - LAN - MAC (Media Access Control) Address - A unit of broadband connection in addition to Point Protocol over Ethernet (PoE) - A standard mail server commonly used for the Internet. A technology... enabling an Ethernet network cable to be tunneled through an IP network. ISP (Internet Service Provider) - Mbps (MegaBits Per Second) - Wireless-G Broadband Router IP...
... for data transmission. RADIUS (Remote Authentication Dial-In User Service) - LAN - MAC (Media Access Control) Address - A unit of broadband connection in addition to Point Protocol over Ethernet (PoE) - A standard mail server commonly used for the Internet. A technology... enabling an Ethernet network cable to be tunneled through an IP network. ISP (Internet Service Provider) - Mbps (MegaBits Per Second) - Wireless-G Broadband Router IP...
User Manual
Page 71
... (Service Set IDentifier) - Roaming - A networking device that requires acknowledgement from one access point's range to another in a network is connected to another without losing the connection. Telnet - Static Routing - The amount of data moved successfully from the recipient of the network. TCP (Transmission Control Protocol) - Wireless-G Broadband Router RJ-45 (Registered Jack-45) -
... (Service Set IDentifier) - Roaming - A networking device that requires acknowledgement from one access point's range to another in a network is connected to another without losing the connection. Telnet - Static Routing - The amount of data moved successfully from the recipient of the network. TCP (Transmission Control Protocol) - Wireless-G Broadband Router RJ-45 (Registered Jack-45) -
User Manual
Page 81
... 98, then refer to Windows Help for more details. Wireless Access Points, Routers, or Other Wireless Products If you have a wireless access point, router or other wireless product, use its Web-based Utility to configure its power output setting (refer to the product's documentation for instructions on how to access technical documents: 1. Click the Products tab. 4. Select the product...
... 98, then refer to Windows Help for more details. Wireless Access Points, Routers, or Other Wireless Products If you have a wireless access point, router or other wireless product, use its Web-based Utility to configure its power output setting (refer to the product's documentation for instructions on how to access technical documents: 1. Click the Products tab. 4. Select the product...
Brochure
Page 1
...WRT54G All your computers can share a high-speed Internet connection, files, printers, and multi-player games with each other resources with the web browser-based configuration utility. Configuration is really three devices in the house. There's also a built-in -one Internetsharing Router, 4-port Switch, and Wireless-G (802.11g) Access Point Wireless... and documents. First, there's the Wireless Access Point, which lets you connect both Wired Equivalent Privacy (WEP) and the industrialstrength wireless security of Wi-Fi Protected Access™ (WPA). Utilize extra free ...
...WRT54G All your computers can share a high-speed Internet connection, files, printers, and multi-player games with each other resources with the web browser-based configuration utility. Configuration is really three devices in the house. There's also a built-in -one Internetsharing Router, 4-port Switch, and Wireless-G (802.11g) Access Point Wireless... and documents. First, there's the Wireless Access Point, which lets you connect both Wired Equivalent Privacy (WEP) and the industrialstrength wireless security of Wi-Fi Protected Access™ (WPA). Utilize extra free ...