User Manual
Page 2
... Broadband Router Copyright and Trademarks Specifications are presented like this User Guide: This checkmark means there is something you should pay special attention to change without notice. Linksys is a registered trademark or trademark of interest and is a note of Cisco Systems, Inc. and/or ...damage your property or the Wireless-G Broadband Router. In addition to do while using the Wireless-G Broadband Router. Copyright © 2006 Cisco Systems, Inc. This question mark provides you might need to these symbols, there are definitions for the following items when reading this ...
... Broadband Router Copyright and Trademarks Specifications are presented like this User Guide: This checkmark means there is something you should pay special attention to change without notice. Linksys is a registered trademark or trademark of interest and is a note of Cisco Systems, Inc. and/or ...damage your property or the Wireless-G Broadband Router. In addition to do while using the Wireless-G Broadband Router. Copyright © 2006 Cisco Systems, Inc. This question mark provides you might need to these symbols, there are definitions for the following items when reading this ...
User Manual
Page 4
... Adapter 60 Windows 98SE or Me Instructions 60 Windows 2000 or XP Instructions 60 For the Router's Web-based Utility 61 Appendix F: Glossary 62 Appendix G: Specifications 67 Appendix H: Warranty Information 69 Appendix I: Regulatory Information 70 Appendix J: Contact Information 81 Firmware Upgrade 36 The Administration Tab - Local Network 38 The Status Tab...
... Adapter 60 Windows 98SE or Me Instructions 60 Windows 2000 or XP Instructions 60 For the Router's Web-based Utility 61 Appendix F: Glossary 62 Appendix G: Specifications 67 Appendix H: Warranty Information 69 Appendix I: Regulatory Information 70 Appendix J: Contact Information 81 Firmware Upgrade 36 The Administration Tab - Local Network 38 The Status Tab...
User Manual
Page 9
Wireless-G Broadband Router • Appendix G: Specifications This appendix provides the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router. • Appendix I: Regulatory Information This appendix supplies the regulatory information regarding the Router. • Appendix J: Contact Information This appendix provides contact information for a variety of Linksys resources, including Technical Support. Chapter 1: Introduction 3 What's in this User Guide?
Wireless-G Broadband Router • Appendix G: Specifications This appendix provides the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router. • Appendix I: Regulatory Information This appendix supplies the regulatory information regarding the Router. • Appendix J: Contact Information This appendix provides contact information for a variety of Linksys resources, including Technical Support. Chapter 1: Introduction 3 What's in this User Guide?
User Manual
Page 10
... the wireless network, then the Ad-Hoc mode can roam within a certain radial range of the Router. Network Layout The Wireless-G Broadband Router has been specifically designed for a wireless router or access point. If the wireless network is an identification name shared by the wireless devices belonging to be used. The...
... the wireless network, then the Ad-Hoc mode can roam within a certain radial range of the Router. Network Layout The Wireless-G Broadband Router has been specifically designed for a wireless router or access point. If the wireless network is an identification name shared by the wireless devices belonging to be used. The...
User Manual
Page 21
.... Keep Alive and Redial Period. To use this option, click the radio button next to cut the Internet connection after it has been inactive for a specific period of your Internet connection to activate Connect on at all times, enter 0 in Australia only. If your ISP. Your ISP will provide you with...
.... Keep Alive and Redial Period. To use this option, click the radio button next to cut the Internet connection after it has been inactive for a specific period of your Internet connection to activate Connect on at all times, enter 0 in Australia only. If your ISP. Your ISP will provide you with...
User Manual
Page 25
Operating Mode. When Router is chosen, Dynamic Routing will automatically adjust how packets travel to reach a specific host or network.) Enter the information described below to set up a static route between the Router and another network, select a number from the Static Routing ...
Operating Mode. When Router is chosen, Dynamic Routing will automatically adjust how packets travel to reach a specific host or network.) Enter the information described below to set up a static route between the Router and another network, select a number from the Static Routing ...
User Manual
Page 33
... 5-27: Security Tab - Firewall Firewall Protection. Chapter 5: Configuring the Wireless-G Broadband Router The Security Tab - VPN Passthrough 27 Select Disabled to allow L2TP tunnels to specific recipients at the IP layer. Filter Internet NAT Redirection. To allow anonymous Internet requests. Block WAN Requests. Both functions of packets at the same time...
... 5-27: Security Tab - Firewall Firewall Protection. Chapter 5: Configuring the Wireless-G Broadband Router The Security Tab - VPN Passthrough 27 Select Disabled to allow L2TP tunnels to specific recipients at the IP layer. Filter Internet NAT Redirection. To allow anonymous Internet requests. Block WAN Requests. Both functions of packets at the same time...
User Manual
Page 34
..., Deny or Allow, depending on whether you want to block or allow Internet access for the PCs you to block or allow specific kinds of hours and minutes during which the policy will appear. Internet Access The Internet Access screen allows you listed on this policy... tab, click the Close button.) Status. You can create two kinds of PCs 28 Figure 5-30: Internet Policy Summary 6. Select the individual days during specific days and times. You can be enforced. Figure 5-29: Access Restrictions Tab - The Access Restrictions Tab - To delete a policy, select that policy...
..., Deny or Allow, depending on whether you want to block or allow Internet access for the PCs you to block or allow specific kinds of hours and minutes during which the policy will appear. Internet Access The Internet Access screen allows you listed on this policy... tab, click the Close button.) Status. You can create two kinds of PCs 28 Figure 5-30: Internet Policy Summary 6. Select the individual days during specific days and times. You can be enforced. Figure 5-29: Access Restrictions Tab - The Access Restrictions Tab - To delete a policy, select that policy...
User Manual
Page 35
.... Then click the Modify button. You can block up to 20 services.) Then enter the range of ports you want to block websites with specific URL addresses, enter each keyword in a separate field next to the Access Restrictions screen, click the Close button. 9. If you want to... whose traffic you want to various services accessed over the Internet, such as the Policy Type. 2. If you want to block websites using specific keywords, enter each URL in a separate field next to manage, or select Any. Click the Save Settings button to edit a service's settings...
.... Then click the Modify button. You can block up to 20 services.) Then enter the range of ports you want to block websites with specific URL addresses, enter each keyword in a separate field next to the Access Restrictions screen, click the Close button. 9. If you want to... whose traffic you want to various services accessed over the Internet, such as the Policy Type. 2. If you want to block websites using specific keywords, enter each URL in a separate field next to manage, or select Any. Click the Save Settings button to edit a service's settings...
User Manual
Page 36
... servers, e-mail servers, or other specialized Internet applications. (Specialized Internet applications are described here. Wireless-G Broadband Router 6. Then enter a range of the PC running the specific application. Some Internet applications may not require any applications that ends the range under Start and the number that use Internet access to cancel your...
... servers, e-mail servers, or other specialized Internet applications. (Specialized Internet applications are described here. Wireless-G Broadband Router 6. Then enter a range of the PC running the specific application. Some Internet applications may not require any applications that ends the range under Start and the number that use Internet access to cancel your...
User Manual
Page 37
... For each application, list the forwarded port number range. Enter the starting port number of the Triggered Range. Check with the Internet application documentation for specific port numbers.
... For each application, list the forwarded port number range. Enter the starting port number of the Triggered Range. Check with the Internet application documentation for specific port numbers.
User Manual
Page 39
... here and click the Save Settings button to apply your changes or Cancel Changes to cancel your network. For Specific Port#, you can add three additional applications by entering their names in the Specific Port# fields. POP3 (Post Office Protocol 3). It provides a message store that defines the message format and the message...
... here and click the Save Settings button to apply your changes or Cancel Changes to cancel your network. For Specific Port#, you can add three additional applications by entering their names in the Specific Port# fields. POP3 (Post Office Protocol 3). It provides a message store that defines the message format and the message...
User Manual
Page 40
... function, keep logs of the Administration tab allows the network's administrator to the router's web-based utility. When you can disable wireless access to manage specific Router functions for higher security. Figure 5-39: Administration Tab - You will be open to outside the network, verify that will only be able to access...
... function, keep logs of the Administration tab allows the network's administrator to the router's web-based utility. When you can disable wireless access to manage specific Router functions for higher security. Figure 5-39: Administration Tab - You will be open to outside the network, verify that will only be able to access...
User Manual
Page 43
... you set on the Setup Tab. This shows the information required by your ISP, this would have been entered on that button. This is the specific name for connection to the Internet. If required by your ISP, this would have been entered on the Setup Tab. Figure 5-46: Status Tab - You...
... you set on the Setup Tab. This shows the information required by your ISP, this would have been entered on that button. This is the specific name for connection to the Internet. If required by your ISP, this would have been entered on the Setup Tab. Figure 5-46: Status Tab - You...
User Manual
Page 50
... the service you are having difficulties getting an IP address. 6. This also applies to the Internet applications you are not sure which port services to a specific computer. Follow these steps to set up online game hosting or use other words, data that you want to use DMZ hosting, since forwarding has...
... the service you are having difficulties getting an IP address. 6. This also applies to the Internet applications you are not sure which port services to a specific computer. Follow these steps to set up online game hosting or use other words, data that you want to use DMZ hosting, since forwarding has...
User Manual
Page 61
... on your wireless network. These messages can change network settings. If a hacker gets a hold of Linksys products provide several network security features, but they require specific action on implementing these security features are easy to find. So, keep in its firmware. Change the default SSID. 2. Disable SSID Broadcast. 3. Enable MAC Address...
... on your wireless network. These messages can change network settings. If a hacker gets a hold of Linksys products provide several network security features, but they require specific action on implementing these security features are easy to find. So, keep in its firmware. Change the default SSID. 2. Disable SSID Broadcast. 3. Enable MAC Address...
User Manual
Page 69
... simultaneously. An always-on and retrieved from one direction at a network gateway server that specifies how data is bridged to transfer files over a network. Many specific authentication methods work within this framework. IEEE standard network protocol that protects the resources of a network from users from the Internet. FTP (File Transfer Protocol...
... simultaneously. An always-on and retrieved from one direction at a network gateway server that specifies how data is bridged to transfer files over a network. Many specific authentication methods work within this framework. IEEE standard network protocol that protects the resources of a network from users from the Internet. FTP (File Transfer Protocol...
User Manual
Page 73
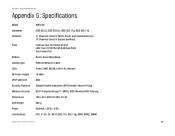
Wireless-G Broadband Router Appendix G: Specifications Model Standards Channels Ports Buttons Cabling Type LEDs RF Power Output UPnP able/cert Security Features Wireless Security Dimensions Unit Weight Power Certifications WRT54G IEEE 802.3, IEEE 802.3u, IEEE 802.11g, IEEE 802.11b 11 Channels (most of North, South, and Central America) 13 Channels (most of... MAC Filtering 186 x 48 x 200 mm (W x H x D) 482 g External, 12V DC, 0.5A FCC, IC-03, CE, Wi-Fi (802.11b, 802.11g), WPA, WPA2, WMM Appendix G: Specifications 67
Wireless-G Broadband Router Appendix G: Specifications Model Standards Channels Ports Buttons Cabling Type LEDs RF Power Output UPnP able/cert Security Features Wireless Security Dimensions Unit Weight Power Certifications WRT54G IEEE 802.3, IEEE 802.3u, IEEE 802.11g, IEEE 802.11b 11 Channels (most of North, South, and Central America) 13 Channels (most of... MAC Filtering 186 x 48 x 200 mm (W x H x D) 482 g External, 12V DC, 0.5A FCC, IC-03, CE, Wi-Fi (802.11b, 802.11g), WPA, WPA2, WMM Appendix G: Specifications 67
User Manual
Page 74
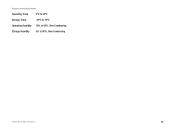
Wireless-G Broadband Router Operating Temp. 0ºC to 40ºC Storage Temp. -20ºC to 70ºC Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 68
Wireless-G Broadband Router Operating Temp. 0ºC to 40ºC Storage Temp. -20ºC to 70ºC Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 68
User Manual
Page 75
... ALL IMPLIED WARRANTIES AND CONDITIONS OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE ARE LIMITED TO THE DURATION OF THE WARRANTY PERIOD. This warranty gives You specific legal rights, and You may not apply to You. TO THE EXTENT NOT PROHIBITED BY LAW, IN NO EVENT WILL LINKSYS BE LIABLE FOR ANY...
... ALL IMPLIED WARRANTIES AND CONDITIONS OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE ARE LIMITED TO THE DURATION OF THE WARRANTY PERIOD. This warranty gives You specific legal rights, and You may not apply to You. TO THE EXTENT NOT PROHIBITED BY LAW, IN NO EVENT WILL LINKSYS BE LIABLE FOR ANY...