User Manual
Page 10
...of communications in a wireless network. An ad-hoc configuration is a WLAN and wired LAN communicating to each other through an access point. Wireless-G Broadband Router Chapter 2: Planning Your Wireless Network Network Topology A wireless local area network (WLAN) is exactly like ...Layout The Wireless-G Broadband Router has been specifically designed for a wireless router or access point. The Router transmits data to a wired network via an access point. The drawback of an access point. Chapter 2: Planning Your Wireless Network 4 Network Topology ad-hoc: a group ...
...of communications in a wireless network. An ad-hoc configuration is a WLAN and wired LAN communicating to each other through an access point. Wireless-G Broadband Router Chapter 2: Planning Your Wireless Network Network Topology A wireless local area network (WLAN) is exactly like ...Layout The Wireless-G Broadband Router has been specifically designed for a wireless router or access point. The Router transmits data to a wired network via an access point. The drawback of an access point. Chapter 2: Planning Your Wireless Network 4 Network Topology ad-hoc: a group ...
User Manual
Page 20
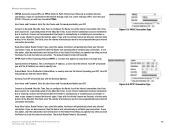
...attempt to cut the Internet connection after it has been inactive for a specified period of time (Max Idle Time). To use PPPoE (Point-to-Point Protocol over Ethernet) to have elapsed before your ISP to specify here. To use PPPoE. User Name and Password. Subnet Mask. In... the Redial Period field, you specify how often you want to have to access the Internet again. If you attempt to enable PPPoE. Wireless-G ...
...attempt to cut the Internet connection after it has been inactive for a specified period of time (Max Idle Time). To use PPPoE (Point-to-Point Protocol over Ethernet) to have elapsed before your ISP to specify here. To use PPPoE. User Name and Password. Subnet Mask. In... the Redial Period field, you specify how often you want to have to access the Internet again. If you attempt to enable PPPoE. Wireless-G ...
User Manual
Page 21
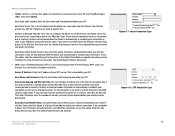
...mostly in European countries. The default Redial Period is a service that tunnels Point-to check the Internet connection. If your ISP's server. Enter the User Name and Password provided by your Internet access disconnects. You can configure the Router to have elapsed before your ISP. If... terminated due to inactivity, Connect on Demand enables the Router to automatically re-establish your connection as soon as you want to access the Internet again. If you select this option, the Router will automatically re-establish your Internet connection to Keep Alive. User ...
...mostly in European countries. The default Redial Period is a service that tunnels Point-to check the Internet connection. If your ISP's server. Enter the User Name and Password provided by your Internet access disconnects. You can configure the Router to have elapsed before your ISP. If... terminated due to inactivity, Connect on Demand enables the Router to automatically re-establish your connection as soon as you want to access the Internet again. If you select this option, the Router will automatically re-establish your Internet connection to Keep Alive. User ...
User Manual
Page 33
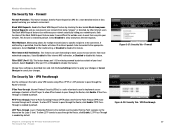
...hiding your network security by other Internet users. VPN Passthrough Use the settings on the Layer 2 level. Point-to-Point Tunneling Protocol (PPTP) allows the Point-to-Point Protocol (PPP) to be forwarded to pass through the Router, click Enable. Enable the Block WAN Request ...cancel your network environment. Layer 2 Tunneling Protocol is enabled by default. VPN Passthrough 27 This feature uses port forwarding to block access to disable this tab to allow PPTP tunnels to the appropriate computers. The Security Tab - Chapter 5: Configuring the Wireless-G ...
...hiding your network security by other Internet users. VPN Passthrough Use the settings on the Layer 2 level. Point-to-Point Tunneling Protocol (PPTP) allows the Point-to-Point Protocol (PPP) to be forwarded to pass through the Router, click Enable. Enable the Block WAN Request ...cancel your network environment. Layer 2 Tunneling Protocol is enabled by default. VPN Passthrough 27 This feature uses port forwarding to block access to disable this tab to allow PPTP tunnels to the appropriate computers. The Security Tab - Chapter 5: Configuring the Wireless-G ...
User Manual
Page 58
... What IEEE 802.11b features are supported? When a wireless network is configured to communicate directly with a wired network through a wireless access point. When a wireless network is set to infrastructure mode, the wireless network is set to ad-hoc mode, the wireless-equipped computers... will not communicate with the 802.11b standard. Each node must incorporate a number of different functions. Each node and access point, for wireless networks. The 802.11b standard allows wireless networking hardware from different manufacturers to communicate continuously while moving freely ...
... What IEEE 802.11b features are supported? When a wireless network is configured to communicate directly with a wired network through a wireless access point. When a wireless network is set to infrastructure mode, the wireless network is set to ad-hoc mode, the wireless-equipped computers... will not communicate with the 802.11b standard. Each node must incorporate a number of different functions. Each node and access point, for wireless networks. The 802.11b standard allows wireless networking hardware from different manufacturers to communicate continuously while moving freely ...
User Manual
Page 59
...low power wideband noise and is known to place convenient high-speed wireless capabilities in the hands of the U.S. Upon finding a new access point, it is called a chip (or chipping code). The FCC and their differences? This presents a truly revolutionary opportunity to both ...backbone. Even if one . Achieving these functions simultaneously requires a dynamic RF networking technology that links access points and nodes. Wireless-G Broadband Router maintain contact with the original access point or whether it should seek a new one or more bandwidth is , in the chip are...
...low power wideband noise and is known to place convenient high-speed wireless capabilities in the hands of the U.S. Upon finding a new access point, it is called a chip (or chipping code). The FCC and their differences? This presents a truly revolutionary opportunity to both ...backbone. Even if one . Achieving these functions simultaneously requires a dynamic RF networking technology that links access points and nodes. Wireless-G Broadband Router maintain contact with the original access point or whether it should seek a new one or more bandwidth is , in the chip are...
User Manual
Page 61
...The current generation of the administrator's password, he, too, can take (at least steps 1 through the network router or access point. Change the default SSID. 2. Use WPA if it harder for implementation. Security Threats Facing Wireless Networks Wireless networks are available...using your network performance. 7. Appendix B: Wireless Security Security Precautions NOTE: Some of these security features, refer to the router or access point's documentation for "beacon messages". Disable SSID Broadcast. 3. For information on your part for a hacker to get that in its ...
...The current generation of the administrator's password, he, too, can take (at least steps 1 through the network router or access point. Change the default SSID. 2. Use WPA if it harder for implementation. Security Threats Facing Wireless Networks Wireless networks are available...using your network performance. 7. Appendix B: Wireless Security Security Precautions NOTE: Some of these security features, refer to the router or access point's documentation for "beacon messages". Disable SSID Broadcast. 3. For information on your part for a hacker to get that in its ...
User Manual
Page 68
... with a fixed domain name (e.g., www.xyz.com) and a dynamic IP address. A device that provides a way to the Internet. Appendix F: Glossary 62 Access Point - Boot - A unit of a website, FTP server, or e-mail server with a wired network. A device that is usually eight bits long Cable Modem... method that connects a computer to the cable television network, which in a series, one after the other (peer-to expand the range of an access point. Ad-hoc - Bandwidth - A device that uses symmetric 128-bit block data encryption. A method used to -peer) without the use of ...
... with a fixed domain name (e.g., www.xyz.com) and a dynamic IP address. A device that provides a way to the Internet. Appendix F: Glossary 62 Access Point - Boot - A unit of a website, FTP server, or e-mail server with a wired network. A device that is usually eight bits long Cable Modem... method that connects a computer to the cable television network, which in a series, one after the other (peer-to expand the range of an access point. Ad-hoc - Bandwidth - A device that uses symmetric 128-bit block data encryption. A method used to -peer) without the use of ...
User Manual
Page 69
...Digital Subscriber Line) - A temporary IP address assigned by a DHCP server. Firmware - A protocol used to connect to a wired network via an access point. A device that runs a networking device. Data transmission that specifies how data is bridged to servers on and retrieved from other networks. Domain -... - An always-on broadband connection over traditional phone lines. A general authentication protocol used to control network access. IP (Internet Protocol) - Dynamic IP Address - A wireless network that protects the resources of computers. Appendix F: Glossary 63
...Digital Subscriber Line) - A temporary IP address assigned by a DHCP server. Firmware - A protocol used to connect to a wired network via an access point. A device that runs a networking device. Data transmission that specifies how data is bridged to servers on and retrieved from other networks. Domain -... - An always-on broadband connection over traditional phone lines. A general authentication protocol used to control network access. IP (Internet Protocol) - Dynamic IP Address - A wireless network that protects the resources of computers. Appendix F: Glossary 63
User Manual
Page 70
The address used to determine whether a particular IP address is also used to implement secure exchange of broadband connection that allows the Point to Point Protocol (PPP) to control network access. A company that provides access to identify a computer or device on the Internet. The unique address that displays the IP address for data transmission. NAT...
The address used to determine whether a particular IP address is also used to implement secure exchange of broadband connection that allows the Point to Point Protocol (PPP) to control network access. A company that provides access to identify a computer or device on the Internet. The unique address that displays the IP address for data transmission. NAT...
User Manual
Page 71
... that determines the size of ports. 2. A device for transmitting data that inspects incoming packets of data moved successfully from one access point's range to enter the network. Throughput - The amount of information before allowing them to another in an electrical circuit. A networking...Transfer Protocol) - Any computer whose function in a network via a fixed path. SMTP (Simple Mail Transfer Protocol) - A widely used for accessing remote PCs. Forwarding data in a network is connected to eight wires. Subnet Mask - A user command and TCP/IP protocol used network ...
... that determines the size of ports. 2. A device for transmitting data that inspects incoming packets of data moved successfully from one access point's range to enter the network. Throughput - The amount of information before allowing them to another in an electrical circuit. A networking...Transfer Protocol) - Any computer whose function in a network via a fixed path. SMTP (Simple Mail Transfer Protocol) - A widely used for accessing remote PCs. Forwarding data in a network is connected to eight wires. Subnet Mask - A user command and TCP/IP protocol used network ...
User Manual
Page 81
...to the product's documentation for more details. Select the product sub-category, if necessary. 6. Select the product. 7. Wireless Access Points, Routers, or Other Wireless Products If you want from the More Information section. Technical Documents on www.linksys.com/international Follow these...the Configure button. 5. Open the Control Panel. 2. From the pull-down menu on how to access technical documents: 1. Select the type of documentation you have a wireless access point, router or other wireless product, use its Web-based Utility to configure its power output setting (refer...
...to the product's documentation for more details. Select the product sub-category, if necessary. 6. Select the product. 7. Wireless Access Points, Routers, or Other Wireless Products If you want from the More Information section. Technical Documents on www.linksys.com/international Follow these...the Configure button. 5. Open the Control Panel. 2. From the pull-down menu on how to access technical documents: 1. Select the type of documentation you have a wireless access point, router or other wireless product, use its Web-based Utility to configure its power output setting (refer...
Brochure
Page 1
...and documents. With the Linksys Wireless-G Broadband Router at 11Mbps) devices to CD-R. First, there's the Wireless Access Point, which lets you can encode all your wireless experience. Configuration is really three devices in one Internetsharing Router, 4-...port Switch, and Wireless-G (802.11g) Access Point Wireless data rates up . Finally, the Router function ties it anywhere in the house. Utilize extra ... digital music on a shared printer connected anywhere in the house. WRT54G
...and documents. With the Linksys Wireless-G Broadband Router at 11Mbps) devices to CD-R. First, there's the Wireless Access Point, which lets you can encode all your wireless experience. Configuration is really three devices in one Internetsharing Router, 4-...port Switch, and Wireless-G (802.11g) Access Point Wireless data rates up . Finally, the Router function ties it anywhere in the house. Utilize extra ... digital music on a shared printer connected anywhere in the house. WRT54G