Software Guide
Page 5
... or Changing a Static Enable Password 4-6 Protecting Enable and Enable Secret Passwords with Encryption 4-7 Configuring Username and Password Pairs 4-9 Configuring Multiple Privilege Levels 4-10 Setting the Privilege Level for a Command 4-10 Logging Into and Exiting a Privilege Level 4-11 Protecting the Wireless LAN 4-11 Using VLANs 4-11 Express Security Types 4-12 Security Configuration Examples 4-14 Configuring and Enabling RADIUS 4-19 Understanding RADIUS 4-19 RADIUS Operation 4-20 Controlling WMIC Access with RADIUS 4-21 Identifying the RADIUS Server Host 4-21 Configuring RADIUS Login...
... or Changing a Static Enable Password 4-6 Protecting Enable and Enable Secret Passwords with Encryption 4-7 Configuring Username and Password Pairs 4-9 Configuring Multiple Privilege Levels 4-10 Setting the Privilege Level for a Command 4-10 Logging Into and Exiting a Privilege Level 4-11 Protecting the Wireless LAN 4-11 Using VLANs 4-11 Express Security Types 4-12 Security Configuration Examples 4-14 Configuring and Enabling RADIUS 4-19 Understanding RADIUS 4-19 RADIUS Operation 4-20 Controlling WMIC Access with RADIUS 4-21 Identifying the RADIUS Server Host 4-21 Configuring RADIUS Login...
Software Guide
Page 15
... the networking professional who installs and manages Cisco 3200 Series wireless and mobile routers. This guide provides procedures for using the IOS commands that have experience working with the Cisco IOS and be assigned and how the role of a device affects its ability to associate or not associate with the concepts and terminology of the web-based interface, which contains all window descriptions and procedures, refer to install and configure...
... the networking professional who installs and manages Cisco 3200 Series wireless and mobile routers. This guide provides procedures for using the IOS commands that have experience working with the Cisco IOS and be assigned and how the role of a device affects its ability to associate or not associate with the concepts and terminology of the web-based interface, which contains all window descriptions and procedures, refer to install and configure...
Software Guide
Page 16
...). Client devices use authenticated key management, Wired Equivalent Privacy (WEP), and WEP features including MIC, CMIC, TKIP, CKIP, and broadcast key rotation. "Configuring VLANs" describes how to configure your network. "Service Set Identifiers" describes how to interoperate with a WDS access point. STP prevents data loops in your WMIC. "Tunnel Templates" describes how a a mobile router to carry multicast sessions to configure the Simple Network Management Protocol (SNMP) on your wired LAN. "Maximum Power Levels" lists...
...). Client devices use authenticated key management, Wired Equivalent Privacy (WEP), and WEP features including MIC, CMIC, TKIP, CKIP, and broadcast key rotation. "Configuring VLANs" describes how to configure your network. "Service Set Identifiers" describes how to interoperate with a WDS access point. STP prevents data loops in your WMIC. "Tunnel Templates" describes how a a mobile router to carry multicast sessions to configure the Simple Network Management Protocol (SNMP) on your wired LAN. "Maximum Power Levels" lists...
Software Guide
Page 19
... Commands" chapter of 3: Addressing and Services, Release 12.2 Related documents from the Cisco TAC Web pages include: • Antenna Cabling (http://www.cisco.com/warp/public/102/wlan/antcable.html) OL-6415-04 Cisco 3200 Series Wireless MIC Software Configuration Guide xix It provides descriptions of the Cisco MIC I/O cards found at www.cisco.com. This feature adds support for using Cisco IOS software, refer to configure the Wireless Mobile Interface Card (WMIC). • Configuration Guide for the Cisco 3200 Series Mobile Access Router1-Example...
... Commands" chapter of 3: Addressing and Services, Release 12.2 Related documents from the Cisco TAC Web pages include: • Antenna Cabling (http://www.cisco.com/warp/public/102/wlan/antcable.html) OL-6415-04 Cisco 3200 Series Wireless MIC Software Configuration Guide xix It provides descriptions of the Cisco MIC I/O cards found at www.cisco.com. This feature adds support for using Cisco IOS software, refer to configure the Wireless Mobile Interface Card (WMIC). • Configuration Guide for the Cisco 3200 Series Mobile Access Router1-Example...
Software Guide
Page 25
... where wireless network access is not provided, cellular service, such as code division multiple access (CDMA) 1xEVDO, can be used in the Cisco Metropolitan Mobile Network include broadband wireless connectivity, providing high speed access for the Cisco 3200 Series wireless and mobile router. All rights reserved. Public Safety Wireless Network Example A Cisco Mobile Wireless Network provides wireless network services to traffic intersections. Overview of the Cisco WMIC The Cisco wireless mobile interface card (WMIC) provides wireless connectivity for bandwidth-intensive applications...
... where wireless network access is not provided, cellular service, such as code division multiple access (CDMA) 1xEVDO, can be used in the Cisco Metropolitan Mobile Network include broadband wireless connectivity, providing high speed access for the Cisco 3200 Series wireless and mobile router. All rights reserved. Public Safety Wireless Network Example A Cisco Mobile Wireless Network provides wireless network services to traffic intersections. Overview of the Cisco WMIC The Cisco wireless mobile interface card (WMIC) provides wireless connectivity for bandwidth-intensive applications...
Software Guide
Page 35
... can connect to the Fast Ethernet Switch Mobile Interface Card (FESMIC) Ethernet port by using an Ethernet cable, and by using the console cable. • If the WMIC has an IP address and Telnet is allowed on the device, you can telnet into the WMIC from your network administrator: • A system name for the WMIC • The case-sensitive wireless service set identifier (SSID) • If not connected to release and renew the IP address on a Cisco Wireless Mobile Interface Card (WMIC...
... can connect to the Fast Ethernet Switch Mobile Interface Card (FESMIC) Ethernet port by using an Ethernet cable, and by using the console cable. • If the WMIC has an IP address and Telnet is allowed on the device, you can telnet into the WMIC from your network administrator: • A system name for the WMIC • The case-sensitive wireless service set identifier (SSID) • If not connected to release and renew the IP address on a Cisco Wireless Mobile Interface Card (WMIC...
Software Guide
Page 36
... serial cable. Enter the WMIC password. Type en. at this URL: http://www.ssh.com/) Cisco 3200 Series Wireless MIC Software Configuration Guide 2 When the terminal emulator establishes communications, a router prompt displays. If Telnet is a software package that there might be several console ports on your operating system. To start the Telnet session in Exec mode. These steps are in Windows 2000, type open followed by using a DB-9-to the COM port on a Cisco 3200 Series router...
... serial cable. Enter the WMIC password. Type en. at this URL: http://www.ssh.com/) Cisco 3200 Series Wireless MIC Software Configuration Guide 2 When the terminal emulator establishes communications, a router prompt displays. If Telnet is a software package that there might be several console ports on your operating system. To start the Telnet session in Exec mode. These steps are in Windows 2000, type open followed by using a DB-9-to the COM port on a Cisco 3200 Series router...
Software Guide
Page 46
... data-intensive and line of the cost. High-speed links between the wireless bridges deliver throughput that is many times faster than the E1/T1 lines for a fraction of sight applications. Wireless bridges can link LANs either through the wired interface or through a wired connection it is typically deployed as a LAN device. If the access point provides its clients a connection to a wired network through the wireless interface. Roles and the Associations of Wireless Devices...
... data-intensive and line of the cost. High-speed links between the wireless bridges deliver throughput that is many times faster than the E1/T1 lines for a fraction of sight applications. Wireless bridges can link LANs either through the wired interface or through a wired connection it is typically deployed as a LAN device. If the access point provides its clients a connection to a wired network through the wireless interface. Roles and the Associations of Wireless Devices...
Software Guide
Page 89
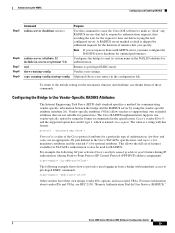
...-model Purpose Enters global configuration mode. To define the AAA server group and associate a particular RADIUS server with the aaa authentication login command. Enables AAA. Cisco 3200 Series Wireless MIC Software Configuration Guide 25 Returns to privileged EXEC mode. Administering the WMIC Configuring and Enabling RADIUS Step 5 Command login authentication {default | list-name} Step 6 Step 7 Step 8 Step 9 radius-server attribute 32 include-in-access-req format %h end show running-config copy running-config startup-config Purpose Applies the authentication list to a line or set...
...-model Purpose Enters global configuration mode. To define the AAA server group and associate a particular RADIUS server with the aaa authentication login command. Enables AAA. Cisco 3200 Series Wireless MIC Software Configuration Guide 25 Returns to privileged EXEC mode. Administering the WMIC Configuring and Enabling RADIUS Step 5 Command login authentication {default | list-name} Step 6 Step 7 Step 8 Step 9 radius-server attribute 32 include-in-access-req format %h end show running-config copy running-config startup-config Purpose Applies the authentication list to a line or set...
Software Guide
Page 93
... pair activates Cisco's multiple named ip address pools feature during IP authorization (during Point-to-Point Protocol IP Control Protocol (PPP IPCP) address assignment): cisco-avpair= "ip:addr-pool=first" The following example shows how to provide a user logging in from a bridge with this command to cause the Cisco IOS software to time out before trying the next configured server. For more than one vendor-specific option by using...
... pair activates Cisco's multiple named ip address pools feature during IP authorization (during Point-to-Point Protocol IP Control Protocol (PPP IPCP) address assignment): cisco-avpair= "ip:addr-pool=first" The following example shows how to provide a user logging in from a bridge with this command to cause the Cisco IOS software to time out before trying the next configured server. For more than one vendor-specific option by using...
Software Guide
Page 102
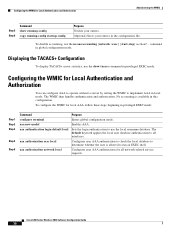
... the user is available in global configuration mode. Sets the login authentication to all network-related service requests. No accounting is allowed to implement AAA in local mode. Configuring the WMIC for local AAA, follow these steps, beginning in privileged EXEC mode: Step 1 Step 2 Step 3 Step 4 Step 5 Command configure terminal aaa new-model aaa authentication login default local aaa authorization exec local aaa authorization network local Purpose Enters global configuration mode. Cisco 3200 Series Wireless MIC Software Configuration Guide 38 command...
... the user is available in global configuration mode. Sets the login authentication to all network-related service requests. No accounting is allowed to implement AAA in local mode. Configuring the WMIC for local AAA, follow these steps, beginning in privileged EXEC mode: Step 1 Step 2 Step 3 Step 4 Step 5 Command configure terminal aaa new-model aaa authentication login default local aaa authorization exec local aaa authorization network local Purpose Enters global configuration mode. Cisco 3200 Series Wireless MIC Software Configuration Guide 38 command...
Software Guide
Page 104
... crypto software image from Cisco.com. Note The SSH feature in the configuration file. Aironet extensions must be deactivated only in the root access point mode. interface dot11radio 0 Enters interface configuration mode for the radio interface. copy running-config startup-config (Optional) Saves your entries in Cisco IOS release 12.3(8)JK does not support IP Security (IPSec). The Aironet extensions can be enabled to support the following features: • Load balancing-The WMIC uses...
... crypto software image from Cisco.com. Note The SSH feature in the configuration file. Aironet extensions must be deactivated only in the root access point mode. interface dot11radio 0 Enters interface configuration mode for the radio interface. copy running-config startup-config (Optional) Saves your entries in Cisco IOS release 12.3(8)JK does not support IP Security (IPSec). The Aironet extensions can be enabled to support the following features: • Load balancing-The WMIC uses...
Software Guide
Page 168
... VLAN becomes the spanning-tree root. The bridge priority value occupies the most significant bits of loops in the network by blocking Layer 2 interfaces connected to reach the spanning-tree root from anywhere in the network are not needed to redundant links For each VLAN, the bridge with the lowest MAC address in the spanning-tree blocking mode. Determines how long each LAN...
... VLAN becomes the spanning-tree root. The bridge priority value occupies the most significant bits of loops in the network by blocking Layer 2 interfaces connected to reach the spanning-tree root from anywhere in the network are not needed to redundant links For each VLAN, the bridge with the lowest MAC address in the spanning-tree blocking mode. Determines how long each LAN...
Software Guide
Page 217
... services traditionally provided by a single bridging domain. VLANs address scalability, security, and network management. These sections describe how to configure your WMIC to support VLANs: • Understanding VLANs, page 1 • Configuring VLANs, page 3 Understanding VLANs A VLAN is a switched network that is supported on your Cisco wireless mobile interface card (WMIC) to the same VLAN, regardless of network equipment such as LAN switches that they might be connected to operate with the VLANs set of as bridges and routers), connected by routers in LAN configurations...
... services traditionally provided by a single bridging domain. VLANs address scalability, security, and network management. These sections describe how to configure your WMIC to support VLANs: • Understanding VLANs, page 1 • Configuring VLANs, page 3 Understanding VLANs A VLAN is a switched network that is supported on your Cisco wireless mobile interface card (WMIC) to the same VLAN, regardless of network equipment such as LAN switches that they might be connected to operate with the VLANs set of as bridges and routers), connected by routers in LAN configurations...
Software Guide
Page 223
...., 170 West Tasman Drive, San Jose, CA 95134-1706 USA © 2008 Cisco Systems, Inc. The process also sends messages to a properly configured syslog server. The device saves syslog messages in this chapter, refer to enhance real-time debugging and management. The messages are interspersed with 4.3 BSD UNIX. You can access logged system messages by using the command-line interface (CLI) or by viewing the logs on a syslog server. Note For...
...., 170 West Tasman Drive, San Jose, CA 95134-1706 USA © 2008 Cisco Systems, Inc. The process also sends messages to a properly configured syslog server. The device saves syslog messages in this chapter, refer to enhance real-time debugging and management. The messages are interspersed with 4.3 BSD UNIX. You can access logged system messages by using the command-line interface (CLI) or by viewing the logs on a syslog server. Note For...
Software Guide
Page 238
... a supported configuration (as shown in the following example configuration. Example Configuration hostname MN ! interface EthernetO/O ip address 169.254.255.1 255.255.255.255 ip mobile router-service roam ! Tunnel Templates 4 Applying the crypto map to the tunnel template requires the crypto map local-address commands as documented in CSCdx79795). To be reverse tunneled; Local-address must be encrypted, all traffic from the mobile router must point to the Home Address ! interface LoopbackO ip address...
... a supported configuration (as shown in the following example configuration. Example Configuration hostname MN ! interface EthernetO/O ip address 169.254.255.1 255.255.255.255 ip mobile router-service roam ! Tunnel Templates 4 Applying the crypto map to the tunnel template requires the crypto map local-address commands as documented in CSCdx79795). To be reverse tunneled; Local-address must be encrypted, all traffic from the mobile router must point to the Home Address ! interface LoopbackO ip address...
Software Guide
Page 241
... URL: • Release Notes for the Cisco 3200 Series Mobile Access Routers-Provides information on accessing documentation and technical assistance for the Cisco 3200 Series wireless and mobile router. • Cisco IOS Command Reference for Cisco Access Points and Bridges1-New and revised Cisco IOS commands for the radio ports provided on the Wireless Mobile Interface Card (WMIC). • Cisco 3200 Series Wireless MIC Software Configuration Guide1-Example procedures for using the IOS commands to configure the Wireless Mobile Interface Card (WMIC). • Configuration Guide for the Cisco...
... URL: • Release Notes for the Cisco 3200 Series Mobile Access Routers-Provides information on accessing documentation and technical assistance for the Cisco 3200 Series wireless and mobile router. • Cisco IOS Command Reference for Cisco Access Points and Bridges1-New and revised Cisco IOS commands for the radio ports provided on the Wireless Mobile Interface Card (WMIC). • Cisco 3200 Series Wireless MIC Software Configuration Guide1-Example procedures for using the IOS commands to configure the Wireless Mobile Interface Card (WMIC). • Configuration Guide for the Cisco...
Software Guide
Page 246
... all wireless device settings to receive an IP address using DHCP) and the default username and password (Cisco). ap: reset Are you sure you see these lines on the CLI, press Esc: Loading "flash:/c350-k9w7-mx.v122_13_ja.20031010/c350-k9w7-mx.v122_13_ja.20031010 At the ap: prompt, enter the flash_init command to the router. Step 1 Step 2 Step 3 Step 4 Step 5 Step 6 Step 7 Open the CLI using a Telnet session or a connection to reset the system (y/n)?y System resetting..Xmodem file system is configured with factory default...
... all wireless device settings to receive an IP address using DHCP) and the default username and password (Cisco). ap: reset Are you sure you see these lines on the CLI, press Esc: Loading "flash:/c350-k9w7-mx.v122_13_ja.20031010/c350-k9w7-mx.v122_13_ja.20031010 At the ap: prompt, enter the flash_init command to the router. Step 1 Step 2 Step 3 Step 4 Step 5 Step 6 Step 7 Open the CLI using a Telnet session or a connection to reset the system (y/n)?y System resetting..Xmodem file system is configured with factory default...
Software Guide
Page 306
... System See DNS Dynamic Frequency Selection (DFS) 7-1 dynamic frequency selection (DFS) 5-1 dynamic tunnel 7-1 extensions, Aironet 4-40 F Fast Ethernet Switch mobile interface card (FESMIC) 2-1 Fast Secure Roaming 3-9 fast secure roaming 14-1 and WDS 14-4 authentication server 14-5 features 1-7 filters configuring using CLI 9-2 protocol 13-1 forward-delay time STP 1-6 frequencies 6-1, 6-2, 6-3, 6-4, 6-5 FTP accessing MIB files 12-2 E EIRP 3-14, 8-1, 11-1 enable password 4-7 enable secret password 4-7 encrypted software image 4-39 encryption for passwords 4-7 encryption mode cipher command 11...
... System See DNS Dynamic Frequency Selection (DFS) 7-1 dynamic frequency selection (DFS) 5-1 dynamic tunnel 7-1 extensions, Aironet 4-40 F Fast Ethernet Switch mobile interface card (FESMIC) 2-1 Fast Secure Roaming 3-9 fast secure roaming 14-1 and WDS 14-4 authentication server 14-5 features 1-7 filters configuring using CLI 9-2 protocol 13-1 forward-delay time STP 1-6 frequencies 6-1, 6-2, 6-3, 6-4, 6-5 FTP accessing MIB files 12-2 E EIRP 3-14, 8-1, 11-1 enable password 4-7 enable secret password 4-7 encrypted software image 4-39 encryption for passwords 4-7 encryption mode cipher command 11...
Software Guide
Page 309
..., global 4-22, 4-28 communication, per-server 4-21, 4-22 multiple UDP ports 4-22 OL-6415-04 default configuration 4-21 defining AAA server groups 4-25 displaying the configuration 4-31 identifying the server 4-21 limiting the services to the user 4-27 method list 4-21 operation of 4-20 overview 4-19 SSID 10-2 suggested network environments 4-19 tracking services accessed by user 4-28 radius-server host command 4-23 range 8-5 rate limit, logging 6-9 redundancy (wireless bridge) 3-5 regulatory domains 6-2, 6-5 regulatory...
..., global 4-22, 4-28 communication, per-server 4-21, 4-22 multiple UDP ports 4-22 OL-6415-04 default configuration 4-21 defining AAA server groups 4-25 displaying the configuration 4-31 identifying the server 4-21 limiting the services to the user 4-27 method list 4-21 operation of 4-20 overview 4-19 SSID 10-2 suggested network environments 4-19 tracking services accessed by user 4-28 radius-server host command 4-23 range 8-5 rate limit, logging 6-9 redundancy (wireless bridge) 3-5 regulatory domains 6-2, 6-5 regulatory...