User Guide
Page 20
... „ Connect the access point directly to the access point: „ Use the 3Com Integrated Power-over-Ethernet power supply. CONNECTING POWER It is advisable to connect the power and check the Ethernet cables and LEDs before installing the unit in a hard-to replace the standard detachable antennas ...with one of the external antennas available for your own power-over-Ethernet hub or switch, which must also comply with the IEEE 802.3af standard. 2-6 CHAPTER 2: INSTALLING THE ACCESS POINT Figure 2 Antenna Adjustment Depending on...
... „ Connect the access point directly to the access point: „ Use the 3Com Integrated Power-over-Ethernet power supply. CONNECTING POWER It is advisable to connect the power and check the Ethernet cables and LEDs before installing the unit in a hard-to replace the standard detachable antennas ...with one of the external antennas available for your own power-over-Ethernet hub or switch, which must also comply with the IEEE 802.3af standard. 2-6 CHAPTER 2: INSTALLING THE ACCESS POINT Figure 2 Antenna Adjustment Depending on...
User Guide
Page 63
... is "admin." (Length: 3-16 characters, case sensitive) New Password - Clients can act as a secure replacement for access authentication. Figure 29 Administration Administration Username - The SSH protocol uses generated public keys to encrypt all data transfers passing between the access point and SSH-enabled management station clients and ensures that SSH client software needs to...
... is "admin." (Length: 3-16 characters, case sensitive) New Password - Clients can act as a secure replacement for access authentication. Figure 29 Administration Administration Username - The SSH protocol uses generated public keys to encrypt all data transfers passing between the access point and SSH-enabled management station clients and ensures that SSH client software needs to...
User Guide
Page 97
... 802.11i standard. WPA2: WPA was introduced as a standard requirement 4-57 TKIP avoids the problems of the IEEE 802.11i wireless security standard. WPA-compatible clients can use either MAC authentication or 802.1X authentication. The AES-CCMP encryption cipher is manually entered... key. WPA Pre-Shared Key Mode (WPA-PSK, WPA2-PSK): For enterprise deployment, WPA requires a RADIUS authentication server to replace WEP. This enables the access point to determine which clients are using a 128-bit key. The Pre-Shared Key mode uses a common password for user authentication ...
... 802.11i standard. WPA2: WPA was introduced as a standard requirement 4-57 TKIP avoids the problems of the IEEE 802.11i wireless security standard. WPA-compatible clients can use either MAC authentication or 802.1X authentication. The AES-CCMP encryption cipher is manually entered... key. WPA Pre-Shared Key Mode (WPA-PSK, WPA2-PSK): For enterprise deployment, WPA requires a RADIUS authentication server to replace WEP. This enables the access point to determine which clients are using a 128-bit key. The Pre-Shared Key mode uses a common password for user authentication ...
User Guide
Page 238
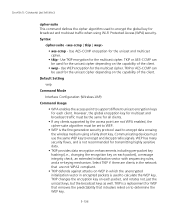
...key. 5-136 Syntax cipher-suite • aes-ccmp - Default Setting wep Command Mode Interface Configuration (Wireless-VAP) Command Usage • WPA enables the access point to encrypt and decrypt radio signals. CHAPTER 5: COMMAND LINE INTERFACE cipher-suite This command defines the cipher algorithm used to calculate the ... set to WEP. • WEP is a replacement for WEP that removes the predictability that are not WPA enabled, the cipher-suite algorithm must be the same for all clients. • If any clients supported by the access point are not WPA2 compliant. • TKIP defends ...
...key. 5-136 Syntax cipher-suite • aes-ccmp - Default Setting wep Command Mode Interface Configuration (Wireless-VAP) Command Usage • WPA enables the access point to encrypt and decrypt radio signals. CHAPTER 5: COMMAND LINE INTERFACE cipher-suite This command defines the cipher algorithm used to calculate the ... set to WEP. • WEP is a replacement for WEP that removes the predictability that are not WPA enabled, the cipher-suite algorithm must be the same for all clients. • If any clients supported by the access point are not WPA2 compliant. • TKIP defends ...