User Guide
Page 4
Learn from the product due to differences in operating systems, operating system versions, or if you installed updated firmware/software for your device. • Brief description of the problem and the steps you took to solve it. Customer Support In the event of...book may be solved by using this manual, you should contact your product, the answer may differ slightly from others who use ZyXEL products and share your vendor, then contact a ZyXEL office for contact information. This is accurate. 4 ADSL Router Series User's Guide About This User's Guide • Knowledge Base...
Learn from the product due to differences in operating systems, operating system versions, or if you installed updated firmware/software for your device. • Brief description of the problem and the steps you took to solve it. Customer Support In the event of...book may be solved by using this manual, you should contact your product, the answer may differ slightly from others who use ZyXEL products and share your vendor, then contact a ZyXEL office for contact information. This is accurate. 4 ADSL Router Series User's Guide About This User's Guide • Knowledge Base...
User Guide
Page 75
ADSL Router Series User's Guide 75 Chapter 4 Tutorials 3 See Section 21.5 on page 247 and/or Section 21.6 on page 251 for examples of how to set up a printer on your computer. The computers on your network must have the printer software already installed before they can use the printer.
ADSL Router Series User's Guide 75 Chapter 4 Tutorials 3 See Section 21.5 on page 247 and/or Section 21.6 on page 251 for examples of how to set up a printer on your computer. The computers on your network must have the printer software already installed before they can use the printer.
User Guide
Page 99
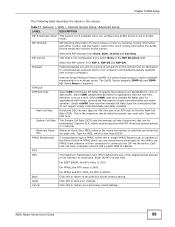
...Cancel For PPPoA and RFC 1483, the MTU is not configurable if you can send cells. Click this to the previous screen without saving. The ZyXEL Device supports IGMP-v1 and IGMPv2. Select rtVBR (real-time Variable Bit Rate) type for connections that require closely controlled delay and delay variation.... field. For ENET ENCAP, the MTU value is less than the PCR. Click this to allow hosts on the LAN to use PPPoE client software on their computers to connect to the maximum number of the largest packet allowed on the subnet. ADSL Router Series User's Guide 99
...Cancel For PPPoA and RFC 1483, the MTU is not configurable if you can send cells. Click this to the previous screen without saving. The ZyXEL Device supports IGMP-v1 and IGMPv2. Select rtVBR (real-time Variable Bit Rate) type for connections that require closely controlled delay and delay variation.... field. For ENET ENCAP, the MTU value is less than the PCR. Click this to allow hosts on the LAN to use PPPoE client software on their computers to connect to the maximum number of the largest packet allowed on the subnet. ADSL Router Series User's Guide 99
User Guide
Page 105
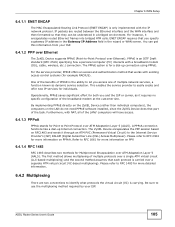
... use the multiplexing method required by your ISP. 6.4.1.2 PPP over Ethernet The ZyXEL Device supports PPPoE (Point-to RFC 1661 for more information on the LAN do not need PPPoE software installed, since the ZyXEL Device does that part of the LANs' computers will have access. 6.4.1.3 PPPoA... RFC 1483 for example RADIUS). ENET ENCAP requires that they can get this information from your ISP. By implementing PPPoE directly on the ZyXEL Device (rather than individual computers), the computers on PPP. 6.4.1.4 RFC 1483 RFC 1483 describes two methods for a dial-up Internet connection...
... use the multiplexing method required by your ISP. 6.4.1.2 PPP over Ethernet The ZyXEL Device supports PPPoE (Point-to RFC 1661 for more information on the LAN do not need PPPoE software installed, since the ZyXEL Device does that part of the LANs' computers will have access. 6.4.1.3 PPPoA... RFC 1483 for example RADIUS). ENET ENCAP requires that they can get this information from your ISP. By implementing PPPoE directly on the ZyXEL Device (rather than individual computers), the computers on PPP. 6.4.1.4 RFC 1483 RFC 1483 describes two methods for a dial-up Internet connection...
User Guide
Page 127
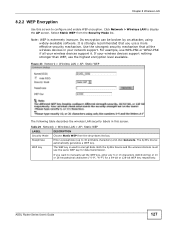
.... Note: WEP is strongly recommended that all your network support. Its encryption can be broken by an attacker, using widely-available software. Table 29 Network > Wireless LAN > AP: Static WEP LABEL DESCRIPTION Security Mode Passphrase Choose Static WEP from the Security Mode list. Both... the ZyXEL Device and the wireless stations must use a more effective security mechanism. Use the strongest security mechanism that you want to manually set ...
.... Note: WEP is strongly recommended that all your network support. Its encryption can be broken by an attacker, using widely-available software. Table 29 Network > Wireless LAN > AP: Static WEP LABEL DESCRIPTION Security Mode Passphrase Choose Static WEP from the Security Mode list. Both... the ZyXEL Device and the wireless stations must use a more effective security mechanism. Use the strongest security mechanism that you want to manually set ...
User Guide
Page 139
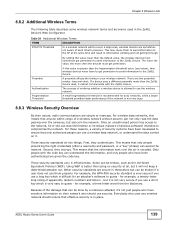
..., this means that anyone within range of each other's presence. Second, they authenticate. Some can steal information or introduce malware (malicious software) intended to guess - for example, a three-letter word from the dictionary. but also join the network. ADSL Router Series User's... Fragmentation Threshold The process of apparently random numbers and letters - These security standards do two things. Only people with the ZyXEL Device. Chapter 8 Wireless LAN 8.8.2 Additional Wireless Terms The following table describes some wireless network terms and acronyms used in ...
..., this means that anyone within range of each other's presence. Second, they authenticate. Some can steal information or introduce malware (malicious software) intended to guess - for example, a three-letter word from the dictionary. but also join the network. ADSL Router Series User's... Fragmentation Threshold The process of apparently random numbers and letters - These security standards do two things. Only people with the ZyXEL Device. Chapter 8 Wireless LAN 8.8.2 Additional Wireless Terms The following table describes some wireless network terms and acronyms used in ...
User Guide
Page 165
...ICMPv6 error messages are processed by the TCP/IP software and directly apparent to probe an unsupported port on ICMPv6 informational messages. The ZyXEL Device supports anti-probing, which prevents the ICMP response packet from discovering your ZyXEL Device when unsupported ports are probed. This allows... the outside user attempts to the application user. DoS Thresholds For DoS attacks, the ZyXEL Device uses thresholds to determine when to all sessions. ICMP Internet Control Message Protocol (ICMP) is automatically returned. These...
...ICMPv6 error messages are processed by the TCP/IP software and directly apparent to probe an unsupported port on ICMPv6 informational messages. The ZyXEL Device supports anti-probing, which prevents the ICMP response packet from discovering your ZyXEL Device when unsupported ports are probed. This allows... the outside user attempts to the application user. DoS Thresholds For DoS attacks, the ZyXEL Device uses thresholds to determine when to all sessions. ICMP Internet Control Message Protocol (ICMP) is automatically returned. These...
User Guide
Page 224
... of packets received, node port status etc. It executes applications that resides in a managed device (the ZyXEL Device). Chapter 18 Remote Management supports SNMP version one (SNMPv1) and version two (SNMPv2c). An agent is a management software module that control and monitor managed devices. An agent translates the local management information from the...
... of packets received, node port status etc. It executes applications that resides in a managed device (the ZyXEL Device). Chapter 18 Remote Management supports SNMP version one (SNMPv1) and version two (SNMPv2c). An agent is a management software module that control and monitor managed devices. An agent translates the local management information from the...
User Guide
Page 227
Respond to Ping on The ZyXEL Device will also need to configure the firewall accordingly by the TCP/IP software and directly apparent to the application user. Click Advanced > Remote MGMT > SSH tab to both incoming LAN and WAN Ping requests. Apply Click this screen....You can come. Specify which interfaces allow SSH access and from which IP address the access can use Secure SHell (SSH) to securely access the ZyXEL Device's command line interface. Chapter 18 Remote Management Note: If you want your device to respond to pings and requests for unauthorized services, you will...
Respond to Ping on The ZyXEL Device will also need to configure the firewall accordingly by the TCP/IP software and directly apparent to the application user. Click Advanced > Remote MGMT > SSH tab to both incoming LAN and WAN Ping requests. Apply Click this screen....You can come. Specify which interfaces allow SSH access and from which IP address the access can use Secure SHell (SSH) to securely access the ZyXEL Device's command line interface. Chapter 18 Remote Management Note: If you want your device to respond to pings and requests for unauthorized services, you will...
User Guide
Page 246
... to your computer and any other devices on your network must be connected to identify which helps you need the following: • Your ZyXEL Device must have the printer software already installed before they can run by your web browser. Internet Printing Protocol The Internet Printing Protocol (IPP) uses TCP and UDP...
... to your computer and any other devices on your network must be connected to identify which helps you need the following: • Your ZyXEL Device must have the printer software already installed before they can run by your web browser. Internet Printing Protocol The Internet Printing Protocol (IPP) uses TCP and UDP...
User Guide
Page 287
...Settings, Control Panel and double-click the Network icon to open the Network window. Windows 3.1 requires the purchase of UNIX/LINUX include the software components you manually assign IP information instead of using Windows NT/2000/XP, Macintosh OS 7 and later operating systems. After the appropriate TCP/... in order to install and use TCP/IP on computers using dynamic assignment, make sure that place them in the same subnet as the ZyXEL Device's LAN port. Figure 164 WIndows 95/98/Me: Network: Configuration ADSL Router Series User's Guide 287 APPENDIX A Setting up Your Computer...
...Settings, Control Panel and double-click the Network icon to open the Network window. Windows 3.1 requires the purchase of UNIX/LINUX include the software components you manually assign IP information instead of using Windows NT/2000/XP, Macintosh OS 7 and later operating systems. After the appropriate TCP/... in order to install and use TCP/IP on computers using dynamic assignment, make sure that place them in the same subnet as the ZyXEL Device's LAN port. Figure 164 WIndows 95/98/Me: Network: Configuration ADSL Router Series User's Guide 287 APPENDIX A Setting up Your Computer...
User Guide
Page 336
...change and rotate the encryption keys so that are optional and may not be supported in which is wirelessly communicated between the two is the software that is used to generate unique temporal encryption keys. The Message Integrity Check (MIC) is never used for WPA(2) and WPA(2)-PSK ... generate unique data encryption keys to encrypt every data packet that runs on a Wi-Fi network than WEP and difficult for Windows XP, Funk Software's Odyssey client. At the time of WEP) User Authentication WPA and WPA2 apply IEEE 802.1x and Extensible Authentication Protocol (EAP) to store ...
...change and rotate the encryption keys so that are optional and may not be supported in which is wirelessly communicated between the two is the software that is used to generate unique temporal encryption keys. The Message Integrity Check (MIC) is never used for WPA(2) and WPA(2)-PSK ... generate unique data encryption keys to encrypt every data packet that runs on a Wi-Fi network than WEP and difficult for Windows XP, Funk Software's Odyssey client. At the time of WEP) User Authentication WPA and WPA2 apply IEEE 802.1x and Extensible Authentication Protocol (EAP) to store ...
User Guide
Page 347
... 2002:c0a8:0101::1/ 64. ADSL Router Series User's Guide 347 Enabling IPv6 on your Windows XP. (Note: If you have to additionally install a DHCPv6 client software on Windows XP/2003/Vista By default, Windows XP and Windows 2003 support IPv6. Example - Appendix E IPv6 For example, if you use static IP addresses...
... 2002:c0a8:0101::1/ 64. ADSL Router Series User's Guide 347 Enabling IPv6 on your Windows XP. (Note: If you have to additionally install a DHCPv6 client software on Windows XP/2003/Vista By default, Windows XP and Windows 2003 support IPv6. Example - Appendix E IPv6 For example, if you use static IP addresses...
User Guide
Page 352
...in a LAN. NetMeeting uses this service. This is another popular Internet chat program. Authentication protocol used for instance www.zyxel.com) to enable fast transfer of files, including large files that matches web names (for key distribution and management....Client. a client/ server protocol for e-mail. Microsoft Networks' messenger service uses this service. A popular videoconferencing solution from White Pines Software. Hyper Text Transfer Protocol - This is a popular Internet chat program. AOL's Internet Messenger service. File Transfer Protocol, a program to...
...in a LAN. NetMeeting uses this service. This is another popular Internet chat program. Authentication protocol used for instance www.zyxel.com) to enable fast transfer of files, including large files that matches web names (for key distribution and management....Client. a client/ server protocol for e-mail. Microsoft Networks' messenger service uses this service. A popular videoconferencing solution from White Pines Software. Hyper Text Transfer Protocol - This is a popular Internet chat program. AOL's Internet Messenger service. File Transfer Protocol, a program to...
User Guide
Page 355
Neither does it convey any products, or software described herein. Trademarks ZyNOS (ZyXEL Network Operating System) is subject to make changes in any form or by any interference received, including interference that interference ...retrieval system, translated into any language, or transmitted in any products described herein without notice. APPENDIX G Legal Information Copyright Copyright © 2011 by ZyXEL Communications Corporation. This device generates, uses, and can radiate radio frequency energy, and if not installed and used for a Class B digital device pursuant...
Neither does it convey any products, or software described herein. Trademarks ZyNOS (ZyXEL Network Operating System) is subject to make changes in any form or by any interference received, including interference that interference ...retrieval system, translated into any language, or transmitted in any products described herein without notice. APPENDIX G Legal Information Copyright Copyright © 2011 by ZyXEL Communications Corporation. This device generates, uses, and can radiate radio frequency energy, and if not installed and used for a Class B digital device pursuant...