User Guide
Page 2
.... 2 Media Server User's Guide Related Documentation • Quick Start Guide The Quick Start Guide shows how to ensure that the information in this book may differ slightly from your product due to differences in this manual is accurate. IMPORTANT! Screenshots and graphics in your product firmware or your computer operating system.
.... 2 Media Server User's Guide Related Documentation • Quick Start Guide The Quick Start Guide shows how to ensure that the information in this book may differ slightly from your product due to differences in this manual is accurate. IMPORTANT! Screenshots and graphics in your product firmware or your computer operating system.
User Guide
Page 23
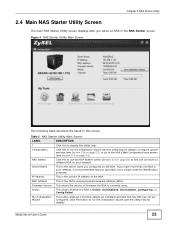
... for the NSA. Server Name This is currently using. If you configured for details), configure system settings (see Section 2.8 on page 27), or go to a different NSA on page 31). IP Address This is the current IP address of firmware the NSA is the server name you have more than one...
... for the NSA. Server Name This is currently using. If you configured for details), configure system settings (see Section 2.8 on page 27), or go to a different NSA on page 31). IP Address This is the current IP address of firmware the NSA is the server name you have more than one...
User Guide
Page 28
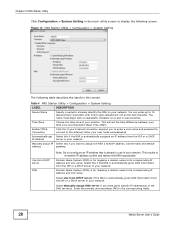
... an alphabetic character (a-z) and is for mapping a domain name to display the following table describes the labels in your network. This will set the time difference between your network. Domain Name System (DNS) is case sensitive. Enter the primary and secondary DNS in the main utility screen to its corresponding IP...
... an alphabetic character (a-z) and is for mapping a domain name to display the following table describes the labels in your network. This will set the time difference between your network. Domain Name System (DNS) is case sensitive. Enter the primary and secondary DNS in the main utility screen to its corresponding IP...
User Guide
Page 78
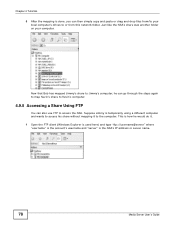
.... 4.9.5 Accessing a Share Using FTP You can then simply copy and paste or drag and drop files from this network folder. Suppose Jimmy is temporarily using a different computer and wants to access his share without mapping it . 1 Open the FTP client (Windows Explorer is used here) and type "ftp://username@server" where...
.... 4.9.5 Accessing a Share Using FTP You can then simply copy and paste or drag and drop files from this network folder. Suppose Jimmy is temporarily using a different computer and wants to access his share without mapping it . 1 Open the FTP client (Windows Explorer is used here) and type "ftp://username@server" where...
User Guide
Page 149
... Manual Daylight Saving DESCRIPTION Click this for the NSA to retrieve the correct time from late spring to fall when many countries set the time difference between your time zone and Greenwich Mean Time (GMT). Start Date Select this option to manually enter Daylight Saving Time settings. GMT or UTC...
... Manual Daylight Saving DESCRIPTION Click this for the NSA to retrieve the correct time from late spring to fall when many countries set the time difference between your time zone and Greenwich Mean Time (GMT). Start Date Select this option to manually enter Daylight Saving Time settings. GMT or UTC...
User Guide
Page 160
... JBOD is the storage method that you install a second disk. (and create new shares, access rights and so on the NSA. Alternatively, you could create a different JBOD volume if you consider this chapter. 7.6.1 Volumes and RAID A volume is a table that volume (disk). You can create volumes on a disk or disks. Below...
... JBOD is the storage method that you install a second disk. (and create new shares, access rights and so on the NSA. Alternatively, you could create a different JBOD volume if you consider this chapter. 7.6.1 Volumes and RAID A volume is a table that volume (disk). You can create volumes on a disk or disks. Below...
User Guide
Page 161
.../or speed. JBOD (Just a Bunch Of Disks) is not a RAID storage method but in addition it is another way to one of data and storing different data pieces on each file is used on a separate, dedicated drive, or be acceptable for example. Parity is included in the event of data. This...
.../or speed. JBOD (Just a Bunch Of Disks) is not a RAID storage method but in addition it is another way to one of data and storing different data pieces on each file is used on a separate, dedicated drive, or be acceptable for example. Parity is included in the event of data. This...
User Guide
Page 162
.... 162 Media Server User's Guide The major benefit of data from the A file. Data can be read across disks but written sequentially to turn multiple different-sized drives into one , so they must be written and read sequentially. JBOD can be read at RAID 0 on the NSA. Typical applications for data...
.... 162 Media Server User's Guide The major benefit of data from the A file. Data can be read across disks but written sequentially to turn multiple different-sized drives into one , so they must be written and read sequentially. JBOD can be read at RAID 0 on the NSA. Typical applications for data...
User Guide
Page 169
... Translation (NAT) to allow access to protect the NSA from attacks from the Internet (see RAID and Data Protection on the NSA. Note: To use a different TCP port number from the one the NSA uses for FTP Access 192.168.1.20 a.b.c.d TCP: 21 TCP: 21 In the above example, the Internet...
... Translation (NAT) to allow access to protect the NSA from attacks from the Internet (see RAID and Data Protection on the NSA. Note: To use a different TCP port number from the one the NSA uses for FTP Access 192.168.1.20 a.b.c.d TCP: 21 TCP: 21 In the above example, the Internet...
User Guide
Page 170
...'s UPnP port mappings. See Section 9.4 on page 177 for CIFS allows users to connect from the NSA, delete files on FTP. Since you can use a different WAN port number (instead of the default of 192.168.1.34 through DHCP, WAN access stops working because the Internet gateway still tries to forward...
...'s UPnP port mappings. See Section 9.4 on page 177 for CIFS allows users to connect from the NSA, delete files on FTP. Since you can use a different WAN port number (instead of the default of 192.168.1.34 through DHCP, WAN access stops working because the Internet gateway still tries to forward...
User Guide
Page 171
... feature configure's the Internet gateway's NAT IP address mapping and port mapping settings. Use this screen to set which port Internet users need to use a different WAN port number (instead of the default of port 80) to these files from the Internet.
... feature configure's the Internet gateway's NAT IP address mapping and port mapping settings. Use this screen to set which port Internet users need to use a different WAN port number (instead of the default of port 80) to these files from the Internet.
User Guide
Page 172
... box, people will be replaced if you clear this icon is your Internet gateway's WAN IP address (the IP address your Internet gateway to use different port numbers. WAN Port If you apply the setting. Make sure there is not another service is using the same port (the Internet gateway has...
... box, people will be replaced if you clear this icon is your Internet gateway's WAN IP address (the IP address your Internet gateway to use different port numbers. WAN Port If you apply the setting. Make sure there is not another service is using the same port (the Internet gateway has...
User Guide
Page 213
... NSA AB After Sync USB AC NSA AB AB Both storage devices contain A. • A copy of files A and B from the USB device is deleted. The difference in both directions simultaneously, both storage devices transfer unique files to the NSA. The same concept applies when you synchronize files from the NSA to...
... NSA AB After Sync USB AC NSA AB AB Both storage devices contain A. • A copy of files A and B from the USB device is deleted. The difference in both directions simultaneously, both storage devices transfer unique files to the NSA. The same concept applies when you synchronize files from the NSA to...
User Guide
Page 263
Attributes (continued) ID ATTRIBUTE NAME BETTER DESCRIPTION 190 Temperature Difference from 100 High This indicates the value of errors reading or writing a sector that an external diagnostic tool has it . Successful and unsuccessful attempts are ... successfully written or read /write heads above the disk surface. 207 Spin High Current This is the quantity of reallocation (remap) operations. Manufacturers can be a different, manufacturer-specific attribute. 203 Run Out Cancel Low This is the number of ECC (Error Correction Code) errors. 204 Soft ECC Correction Low This is...
Attributes (continued) ID ATTRIBUTE NAME BETTER DESCRIPTION 190 Temperature Difference from 100 High This indicates the value of errors reading or writing a sector that an external diagnostic tool has it . Successful and unsuccessful attempts are ... successfully written or read /write heads above the disk surface. 207 Spin High Current This is the quantity of reallocation (remap) operations. Manufacturers can be a different, manufacturer-specific attribute. 203 Run Out Cancel Low This is the number of ECC (Error Correction Code) errors. 204 Soft ECC Correction Low This is...
User Guide
Page 270
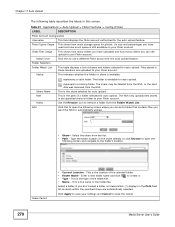
... selected for auto upload. The NSA only uploads files stored in the specified share or folder to open the following screen and navigate to use a different Flickr account for the auto upload feature. Type the folder location in the share directly or click Browse to your Flickr account. Grace Period •...
... selected for auto upload. The NSA only uploads files stored in the specified share or folder to open the following screen and navigate to use a different Flickr account for the auto upload feature. Type the folder location in the share directly or click Browse to your Flickr account. Grace Period •...
User Guide
Page 273
... slash (/) displays in these locations are automatically selected. Files stored in the Path field. This table displays a list of 1 to 10080 minutes (up to use a different YouTube account for the auto upload feature. Chapter 11 Auto Upload Table 92 Applications > Auto Upload > Config (YouTube) (continued) LABEL Switch User Folder Selection Folder...
... slash (/) displays in these locations are automatically selected. Files stored in the Path field. This table displays a list of 1 to 10080 minutes (up to use a different YouTube account for the auto upload feature. Chapter 11 Auto Upload Table 92 Applications > Auto Upload > Config (YouTube) (continued) LABEL Switch User Folder Selection Folder...
User Guide
Page 294
Jump to a different page to create or edit a NSA group. 294 Media Server User's Guide Table 102 Sharing > Groups LABEL DESCRIPTION Add Group Click this to open a screen ...
Jump to a different page to create or edit a NSA group. 294 Media Server User's Guide Table 102 Sharing > Groups LABEL DESCRIPTION Add Group Click this to open a screen ...
User Guide
Page 315
... external access, such as the local certificate authority. This is open to external access. Modify the Existing Certificate Note: Each web browser handles certificate installation differently. Anyone who connects via HTTPS to install a certificate that has been authorized by the NSA as allowing users to connect through the Internet using FTP...
... external access, such as the local certificate authority. This is open to external access. Modify the Existing Certificate Note: Each web browser handles certificate installation differently. Anyone who connects via HTTPS to install a certificate that has been authorized by the NSA as allowing users to connect through the Internet using FTP...
User Guide
Page 325
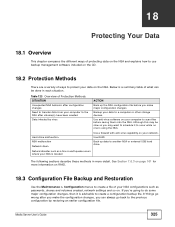
... backup file. Back up the NSA configuration file before saving them onto the NSA. CHAPTER 18 Protecting Your Data 18.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 18.2 Protection Methods There are a variety...
... backup file. Back up the NSA configuration file before saving them onto the NSA. CHAPTER 18 Protecting Your Data 18.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 18.2 Protection Methods There are a variety...
User Guide
Page 328
... functions, it is recommended that the hard drive may fail soon. Do not remove or install a hard disk while the NSA is installed correctly in a different NSA or computer. 2 If you had to replace the drive, turn on the NSA and go to the Storage screen. • If you have a RAID... whole volume. Replace or install a hard drive. The NSA automatically tries to create a whole new volume on the computer). 328 Media Server User's Guide Try a different hard drive or test the original hard disk in the disk bay. The HDD LED is off , remove the front panel and make sure that...
... functions, it is recommended that the hard drive may fail soon. Do not remove or install a hard disk while the NSA is installed correctly in a different NSA or computer. 2 If you had to replace the drive, turn on the NSA and go to the Storage screen. • If you have a RAID... whole volume. Replace or install a hard drive. The NSA automatically tries to create a whole new volume on the computer). 328 Media Server User's Guide Try a different hard drive or test the original hard disk in the disk bay. The HDD LED is off , remove the front panel and make sure that...