User Guide
Page 17
...card readers, MP3 players, mass storage devices, and digital cameras without using a computer. • Have the NSA handle large file downloads. • Automatically download files from website feeds for convenient viewing. • Play the NSA's video, music and photo files on your computers using the ...included media client software. • Play the NSA's video, music and photo files on hardware-based media clients like the DMA-2501. •...
...card readers, MP3 players, mass storage devices, and digital cameras without using a computer. • Have the NSA handle large file downloads. • Automatically download files from website feeds for convenient viewing. • Play the NSA's video, music and photo files on your computers using the ...included media client software. • Play the NSA's video, music and photo files on hardware-based media clients like the DMA-2501. •...
User Guide
Page 186
... in the following example. The NSA can free up your computer's system resources. Your FTP client must be set to use Apple's iTunes software on a computer to play video, music, and photos from the NSA (without having to copy them to another computer). iTunes Server The ... (FTPES) is a group of encryption from the FTP server for web pages. • FTP: A standard Internet file transfer service. • P2P download: Peer-to-peer files sharing protocol. 186 Media Server User's Guide It requests for a mutual method of personal computer and electronics companies that uses either...
... in the following example. The NSA can free up your computer's system resources. Your FTP client must be set to use Apple's iTunes software on a computer to play video, music, and photos from the NSA (without having to copy them to another computer). iTunes Server The ... (FTPES) is a group of encryption from the FTP server for web pages. • FTP: A standard Internet file transfer service. • P2P download: Peer-to-peer files sharing protocol. 186 Media Server User's Guide It requests for a mutual method of personal computer and electronics companies that uses either...
User Guide
Page 219
... 10 Applications Note: The download service notification only keeps track of hacking attacks, which can be protected against them. Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the ...computer itself, not the NSA since your computer is not between the Internet and your network and protect your IP address. Figure 124 Download Service Notification 10.11.5 P2P Download Security When you download using P2P...
... 10 Applications Note: The download service notification only keeps track of hacking attacks, which can be protected against them. Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the ...computer itself, not the NSA since your computer is not between the Internet and your network and protect your IP address. Figure 124 Download Service Notification 10.11.5 P2P Download Security When you download using P2P...
User Guide
Page 220
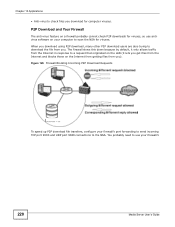
... Your Firewall The anti-virus feature on a firewall probably cannot check P2P downloads for computer viruses. The firewall slows this down because by default, it lets you get files from the Internet and blocks those on the LAN (... firewall's 220 Media Server User's Guide Chapter 10 Applications • Anti-virus to download the file from you. When you download using P2P download, many other P2P download users are also trying to check files you download for viruses, so use antivirus software on your computer to use your firewall's port forwarding to send incoming TCP...
... Your Firewall The anti-virus feature on a firewall probably cannot check P2P downloads for computer viruses. The firewall slows this down because by default, it lets you get files from the Internet and blocks those on the LAN (... firewall's 220 Media Server User's Guide Chapter 10 Applications • Anti-virus to download the file from you. When you download using P2P download, many other P2P download users are also trying to check files you download for viruses, so use antivirus software on your computer to use your firewall's port forwarding to send incoming TCP...
User Guide
Page 433
... RUN, DISTRIBUTE, MODIFY AND IMPROVE THE SOFTWARE UNDER THE APPLICABLE TERMS OF SUCH THRID PARTY'S LICENSES ("OPEN-SOURCED COMPONENTS"). ZYXEL MAY HAVE DISTRIBUTED TO YOU HARDWARE AND/OR SOFTWARE, OR MADE AVAILABLE FOR ELECTRONIC DOWNLOADS THESE FREE SOFTWARE PROGRAMS OF THRID PARTIES AND YOU ARE ...LICENSED TO FREELY COPY, MODIFY AND REDISTIBUTE THAT SOFTWARE UNDER THE APPLICABLE LICENSE TERMS OF...
... RUN, DISTRIBUTE, MODIFY AND IMPROVE THE SOFTWARE UNDER THE APPLICABLE TERMS OF SUCH THRID PARTY'S LICENSES ("OPEN-SOURCED COMPONENTS"). ZYXEL MAY HAVE DISTRIBUTED TO YOU HARDWARE AND/OR SOFTWARE, OR MADE AVAILABLE FOR ELECTRONIC DOWNLOADS THESE FREE SOFTWARE PROGRAMS OF THRID PARTIES AND YOU ARE ...LICENSED TO FREELY COPY, MODIFY AND REDISTIBUTE THAT SOFTWARE UNDER THE APPLICABLE LICENSE TERMS OF...
User Guide
Page 537
...is available for Contributions To SQLite SQLite is insufficient. Because the SQLite software found at large and to the software, use and distribute SQLite. If you make future changes Copyright Release for free download from time to time contribute changes and enhancements to likewise disclaim their.... We are not able to accept patches or changes to SQLite that you that are asked to dedicate their contributions to download the SQLite software from that implements an embeddable SQL database engine. We make this release to make changes or enhancements as an employee, then...
...is available for Contributions To SQLite SQLite is insufficient. Because the SQLite software found at large and to the software, use and distribute SQLite. If you make future changes Copyright Release for free download from time to time contribute changes and enhancements to likewise disclaim their.... We are not able to accept patches or changes to SQLite that you that are asked to dedicate their contributions to download the SQLite software from that implements an embeddable SQL database engine. We make this release to make changes or enhancements as an employee, then...
User Guide
Page 565
Illegal downloading or sharing of any products, or software described herein. ZyXEL bears NO responsibility or liability for your use of files can radiate radio frequency energy, and if not installed and used in a particular installation. ZyXEL is no guarantee that may not be ... patent rights of or damage to provide reasonable protection against harmful interference in severe civil and criminal penalties. Published by ZyXEL Communications Corporation. Neither does it convey any means, electronic, mechanical, magnetic, optical, chemical, photocopying, manual, or otherwise...
Illegal downloading or sharing of any products, or software described herein. ZyXEL bears NO responsibility or liability for your use of files can radiate radio frequency energy, and if not installed and used in a particular installation. ZyXEL is no guarantee that may not be ... patent rights of or damage to provide reasonable protection against harmful interference in severe civil and criminal penalties. Published by ZyXEL Communications Corporation. Neither does it convey any means, electronic, mechanical, magnetic, optical, chemical, photocopying, manual, or otherwise...