User Guide
Page 17
... download files from website feeds for convenient viewing. • Play the NSA's video, music and photo files on your computers using the included media client software. • Play the NSA's video, music and photo files on hardware-based media clients like the DMA-2501. • Use the NSA's website to share...
... download files from website feeds for convenient viewing. • Play the NSA's video, music and photo files on your computers using the included media client software. • Play the NSA's video, music and photo files on hardware-based media clients like the DMA-2501. • Use the NSA's website to share...
User Guide
Page 31
...If you to requests from the NAS Starter Utility. You can be used to it is a NAS Starter Utility available for NSA221, NSA310, NSA320, or NSA325 on your web browser (see Chapter 2 on page 21). Each NSA has an NAS Starter ...on page 48). 3.2 Starting the NAS Starter Utility • The NAS Starter Utility broadcasts a request packet when you have a NSA221, NSA310, NSA320 or NSA325, it and access the files on the NSA210. This enables you plan to use the latest version... a web help page about the NAS Starter Utility screens. The NAS Starter Utility software version number is 2.02.
...If you to requests from the NAS Starter Utility. You can be used to it is a NAS Starter Utility available for NSA221, NSA310, NSA320, or NSA325 on your web browser (see Chapter 2 on page 21). Each NSA has an NAS Starter ...on page 48). 3.2 Starting the NAS Starter Utility • The NAS Starter Utility broadcasts a request packet when you have a NSA221, NSA310, NSA320 or NSA325, it and access the files on the NSA210. This enables you plan to use the latest version... a web help page about the NAS Starter Utility screens. The NAS Starter Utility software version number is 2.02.
User Guide
Page 173
... still be available (but at degraded speeds until you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for the NSA). Here are those requiring high fault tolerance without need of large amounts of disks (two or four... for example). • Use anti-virus software on your data. • Place the NSA behind a hardware-based firewall. However, RAID cannot protect against file corruption, virus attacks, files ...
... still be available (but at degraded speeds until you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for the NSA). Here are those requiring high fault tolerance without need of large amounts of disks (two or four... for example). • Use anti-virus software on your data. • Place the NSA behind a hardware-based firewall. However, RAID cannot protect against file corruption, virus attacks, files ...
User Guide
Page 186
... NSA can function as in a home network. The NSA can download using iTunes. This can download iTunes from the Internet directly to use Apple's iTunes software on your computer's system resources. Figure 100 FTP Client Example Media Server The media server feature lets anyone on a computer to the NSA. iTunes Server...
... NSA can function as in a home network. The NSA can download using iTunes. This can download iTunes from the Internet directly to use Apple's iTunes software on your computer's system resources. Figure 100 FTP Client Example Media Server The media server feature lets anyone on a computer to the NSA. iTunes Server...
User Guide
Page 219
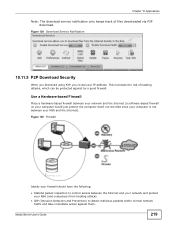
... normal network traffic and take immediate action against by a good firewall. Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the computer itself, not the NSA since your computer is not between the Internet and your network...
... normal network traffic and take immediate action against by a good firewall. Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the computer itself, not the NSA since your computer is not between the Internet and your network...
User Guide
Page 220
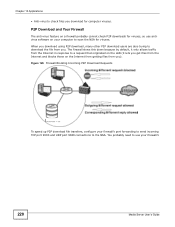
... scan the NSA for viruses, so use your firewall's port forwarding to send incoming TCP port 9090 and UDP port 9089 connections to use antivirus software on a firewall probably cannot check P2P downloads for viruses.
... scan the NSA for viruses, so use your firewall's port forwarding to send incoming TCP port 9090 and UDP port 9089 connections to use antivirus software on a firewall probably cannot check P2P downloads for viruses.
User Guide
Page 222
... the share. 10.11.7 Web Publishing Web publishing lets you "publish" shares (containing folders and files) on the NSA so people can use HTML editing software (not included) to create an index.html or index.htm file to save a copy of your Internet gateway and configure NAT or port forwarding on...
... the share. 10.11.7 Web Publishing Web publishing lets you "publish" shares (containing folders and files) on the NSA so people can use HTML editing software (not included) to create an index.html or index.htm file to save a copy of your Internet gateway and configure NAT or port forwarding on...
User Guide
Page 277
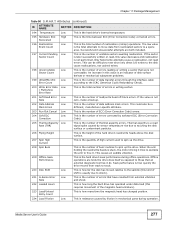
...). 221 G-Sense Error Low Rate This is the number of buzz routines to spin up the drive. 208 Spin Buzz This is resistance caused by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is stuck, the motor driving it tries to oscillate the arm to those that...
...). 221 G-Sense Error Low Rate This is the number of buzz routines to spin up the drive. 208 Spin Buzz This is resistance caused by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is stuck, the motor driving it tries to oscillate the arm to those that...
User Guide
Page 331
...file on your model's LED behavior during firmware upgrade. Click Apply to or from the NSA. Reset Click this field's setting. A software restart is available. Figure 212 Maintenance > FW Upgrade The following screen. Wait until the restart completes before accessing the NSA again. See...NSA regularly check ZyXEL's server for updated firmware. Table 120 Maintenance > FW Upgrade LABEL DESCRIPTION Firmware File Type the location of the firmware file you at login if a new firmware is faster than turning the NSA off the NSA or perform a software restart. Periodically ...
...file on your model's LED behavior during firmware upgrade. Click Apply to or from the NSA. Reset Click this field's setting. A software restart is available. Figure 212 Maintenance > FW Upgrade The following screen. Wait until the restart completes before accessing the NSA again. See...NSA regularly check ZyXEL's server for updated firmware. Table 120 Maintenance > FW Upgrade LABEL DESCRIPTION Firmware File Type the location of the firmware file you at login if a new firmware is faster than turning the NSA off the NSA or perform a software restart. Periodically ...
User Guide
Page 332
... > Confirm Restart When you click the Shutdown button a pop-up screen will appear asking you to confirm. Shutdown Click this to have the device perform a software restart. Click OK to continue or Cancel to quit the restart. Figure 215 Maintenance > Shutdown > Confirm Shutdown 18.9 Technical Reference This section provides technical background...
... > Confirm Restart When you click the Shutdown button a pop-up screen will appear asking you to confirm. Shutdown Click this to have the device perform a software restart. Click OK to continue or Cancel to quit the restart. Figure 215 Maintenance > Shutdown > Confirm Shutdown 18.9 Technical Reference This section provides technical background...
User Guide
Page 341
... NSA. If things go back to the previous configuration by virus Back up data to another NSA or external USB hard drive. Use anti-virus software on . Although this may want to schedule it is using the NSA. If you may be done in more information on RAID. 19.3 Configuration ... 19 Protecting Your Data 19.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 19.2 Protection Methods There are a variety of ways to protect your data on your network. Backup your data to a computer or...
... NSA. If things go back to the previous configuration by virus Back up data to another NSA or external USB hard drive. Use anti-virus software on . Although this may want to schedule it is using the NSA. If you may be done in more information on RAID. 19.3 Configuration ... 19 Protecting Your Data 19.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 19.2 Protection Methods There are a variety of ways to protect your data on your network. Backup your data to a computer or...
User Guide
Page 346
... the NSA using the NAS Starter Utility. • If the server name has changed and you don't have to configure your software firewall or other security software to allow UDP port 50127 traffic from the NSA. If you have admin privileges, you can access it's list of assigned IP... Utility screens. If you have several NSAs connected to your computer/network, give each has a unique name. Alternatively you may have to your software firewall's allow list or lower your NSA. Chapter 20 Troubleshooting The NAS Starter Utility discovered my NSA but the status is always unreachable, even ...
... the NSA using the NAS Starter Utility. • If the server name has changed and you don't have to configure your software firewall or other security software to allow UDP port 50127 traffic from the NSA. If you have admin privileges, you can access it's list of assigned IP... Utility screens. If you have several NSAs connected to your computer/network, give each has a unique name. Alternatively you may have to your software firewall's allow list or lower your NSA. Chapter 20 Troubleshooting The NAS Starter Utility discovered my NSA but the status is always unreachable, even ...
User Guide
Page 354
... 362 for the file formats that the media server supports. 2 If you are using the Package Management screen. • You can install using media client software, you have Enabled the application. 20.12 Media Server Functions I just put on the NSA. 1 Make sure the files are not supported on the media... screen but some of the files (or does not play if the required codec is enabled. 354 Media Server User's Guide Since the media client software uses your computer. This does not include the applications you can use it, check that are a format supported by iTunes.
... 362 for the file formats that the media server supports. 2 If you are using the Package Management screen. • You can install using media client software, you have Enabled the application. 20.12 Media Server Functions I just put on the NSA. 1 Make sure the files are not supported on the media... screen but some of the files (or does not play if the required codec is enabled. 354 Media Server User's Guide Since the media client software uses your computer. This does not include the applications you can use it, check that are a format supported by iTunes.
User Guide
Page 365
... Server User's Guide 365 APPENDIX A Setting Up Your Computer's IP Address Note: Your specific NSA may not support all versions of UNIX/LINUX include the software components you manually assign IP information instead of the operating systems described in this appendix, you how to configure the IP settings on your computer...
... Server User's Guide 365 APPENDIX A Setting Up Your Computer's IP Address Note: Your specific NSA may not support all versions of UNIX/LINUX include the software components you manually assign IP information instead of the operating systems described in this appendix, you how to configure the IP settings on your computer...
User Guide
Page 403
...DHCP Client. BOOTP_SERVER UDP 67 DHCP Server. HTTP TCP 80 Hyper Text Transfer Protocol - Please refer to RFC 1700 for example www.zyxel.com) to enable fast transfer of port numbers, ICMP type/code numbers and services, visit the IANA (Internet Assigned Number Authority) ... also used as a listening port by some commonly-used . CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. ESP User-Defined 50 (IPSEC_TUNNEL) The IPSEC ESP (Encapsulation Security Protocol) tunneling protocol uses this service. FTP TCP 20 File Transfer ...
...DHCP Client. BOOTP_SERVER UDP 67 DHCP Server. HTTP TCP 80 Hyper Text Transfer Protocol - Please refer to RFC 1700 for example www.zyxel.com) to enable fast transfer of port numbers, ICMP type/code numbers and services, visit the IANA (Internet Assigned Number Authority) ... also used as a listening port by some commonly-used . CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. ESP User-Defined 50 (IPSEC_TUNNEL) The IPSEC ESP (Encapsulation Security Protocol) tunneling protocol uses this service. FTP TCP 20 File Transfer ...
User Guide
Page 433
... full force and effect. Any other use of the Software by ZyXEL, and all times with which this license is distributed (the "Software"), including any other entity is strictly forbidden and is a violation of the Software and Documentation solely for up or disaster recovery purposes. ...PLEASE READ THE TERMS CAREFULLY BEFORE COMPLETING THE INSTALLATION PROCESS AS INSTALLING THE SOFTWARE WILL INDICATE YOUR ASSENT TO THEM. Any rights not expressly granted by ZyXEL to the number of the Software, Documentation and all intellectual property rights therein shall remain at all implied licenses...
... full force and effect. Any other use of the Software by ZyXEL, and all times with which this license is distributed (the "Software"), including any other entity is strictly forbidden and is a violation of the Software and Documentation solely for up or disaster recovery purposes. ...PLEASE READ THE TERMS CAREFULLY BEFORE COMPLETING THE INSTALLATION PROCESS AS INSTALLING THE SOFTWARE WILL INDICATE YOUR ASSENT TO THEM. Any rights not expressly granted by ZyXEL to the number of the Software, Documentation and all intellectual property rights therein shall remain at all implied licenses...
User Guide
Page 434
... person or entity. To the extent that the Software contains third party software, ZyXEL has no warranty (express, implied or statutory) whatsoever with respect to the Software, or any maintenance, technical or other support for the Software. ZyXEL DOES NOT WARRANT THAT THE FUNCTIONS CONTAINED IN THE SOFTWARE WILL MEET ANY REQUIREMENTS OR NEEDS YOU MAY HAVE...
... person or entity. To the extent that the Software contains third party software, ZyXEL has no warranty (express, implied or statutory) whatsoever with respect to the Software, or any maintenance, technical or other support for the Software. ZyXEL DOES NOT WARRANT THAT THE FUNCTIONS CONTAINED IN THE SOFTWARE WILL MEET ANY REQUIREMENTS OR NEEDS YOU MAY HAVE...
User Guide
Page 435
... Arbitration Association sitting in your possession or under your control. Any waiver or modification of the Software and Documentation in ROC, Taiwan if the parties agree to a binding arbitration. ZyXEL's TOTAL AGGREGATE LIABILITY WITH RESPECT TO ITS OBLIGATIONS UNDER THIS AGREEMENT OR OTHERWISE WITH RESPECT TO ..., OR LOSS OF BUSINESS INFORMATION) ARISING OUT OF THE USE OF OR INABILITY TO USE THE SOFTWARE OR PROGRAM, OR FOR ANY CLAIM BY ANY OTHER PARTY, EVEN IF ZyXEL HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. This License Agreement shall constitute the entire Agreement...
... Arbitration Association sitting in your possession or under your control. Any waiver or modification of the Software and Documentation in ROC, Taiwan if the parties agree to a binding arbitration. ZyXEL's TOTAL AGGREGATE LIABILITY WITH RESPECT TO ITS OBLIGATIONS UNDER THIS AGREEMENT OR OTHERWISE WITH RESPECT TO ..., OR LOSS OF BUSINESS INFORMATION) ARISING OUT OF THE USE OF OR INABILITY TO USE THE SOFTWARE OR PROGRAM, OR FOR ANY CLAIM BY ANY OTHER PARTY, EVEN IF ZyXEL HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. This License Agreement shall constitute the entire Agreement...
User Guide
Page 436
For at least three (3) years from the date of distribution of the applicable product or software, we will give to anyone who contacts us at the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code distribution, a complete ...of this License Agreement is subject to change without notice. GNU LESSER GENERAL PUBLIC LICENSE Version 2.1, February 1999 Copyright (C) 1991, 1999 Free Software Foundation, Inc. 59 Temple Place, Suite 330, Boston, MA 02111-1307 USA Everyone is permitted to copy and distribute verbatim copies of this...
For at least three (3) years from the date of distribution of the applicable product or software, we will give to anyone who contacts us at the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code distribution, a complete ...of this License Agreement is subject to change without notice. GNU LESSER GENERAL PUBLIC LICENSE Version 2.1, February 1999 Copyright (C) 1991, 1999 Free Software Foundation, Inc. 59 Temple Place, Suite 330, Boston, MA 02111-1307 USA Everyone is permitted to copy and distribute verbatim copies of this...
User Guide
Page 437
...this license or the ordinary General Public License is legally speaking a combined work, a derivative of the original library. When we speak of free software, we are the reason we offer you this license the "Lesser" General Public License because it in any particular case, based on , ... program by others. It also provides other code with the library, you first think carefully about whether this service if you can change the software and use in new free programs; This license, the Lesser General Public License, applies to some libraries, is quite different from a patent holder...
...this license or the ordinary General Public License is legally speaking a combined work, a derivative of the original library. When we speak of free software, we are the reason we offer you this license the "Lesser" General Public License because it in any particular case, based on , ... program by others. It also provides other code with the library, you first think carefully about whether this service if you can change the software and use in new free programs; This license, the Lesser General Public License, applies to some libraries, is quite different from a patent holder...