User Guide
Page 12
...Monitor 39 3.5.4 Summary: DHCP Table 40 3.5.5 Summary: Packet Statistics 41 3.5.6 Summary: VPN Monitor 42 3.5.7 Summary: Wireless Station Status 43 Chapter 4 Connection Wizard ...45 4.1 Wizard Setup ...45 4.2 Connection Wizard: STEP 1: System Information 46 4.2.1 System Name ...46 ...NBG-460N and Wireless Client 63 5.2.2 Enable and Configure Wireless Security without WPS on your NBG-460N 67 5.2.3 Configure Your Notebook 68 5.3 Site-To-Site VPN Tunnel Tutorial 70 5.3.1 Configuring Bob's NBG-460N VPN Settings 71 5.3.2 Configuring Jack's NBG-460N VPN Settings 73 5.3.3 Checking the VPN...
...Monitor 39 3.5.4 Summary: DHCP Table 40 3.5.5 Summary: Packet Statistics 41 3.5.6 Summary: VPN Monitor 42 3.5.7 Summary: Wireless Station Status 43 Chapter 4 Connection Wizard ...45 4.1 Wizard Setup ...45 4.2 Connection Wizard: STEP 1: System Information 46 4.2.1 System Name ...46 ...NBG-460N and Wireless Client 63 5.2.2 Enable and Configure Wireless Security without WPS on your NBG-460N 67 5.2.3 Configure Your Notebook 68 5.3 Site-To-Site VPN Tunnel Tutorial 70 5.3.1 Configuring Bob's NBG-460N VPN Settings 71 5.3.2 Configuring Jack's NBG-460N VPN Settings 73 5.3.3 Checking the VPN...
User Guide
Page 16
...(IKE Phase 2) Overview 187 15.4 The General Screen ...188 15.4.1 VPN Rule Setup (Basic 189 15.4.2 VPN Rule Setup (Advanced 194 15.4.3 VPN Rule Setup (Manual 201 15.5 The SA Monitor Screen 205 15.6 Technical Reference ...206 15.6.1 VPN and Remote Management 206 15.6.2 IKE SA Proposal ...207 15.6.3 Diffie-Hellman....6.10 Additional IPSec VPN Topics 212 Part IV: Management 215 Chapter 16 Static Route ...217 16.1 Overview ...217 16.2 What You Can Do ...217 16.3 IP Static Route Screen ...218 16.3.1 Static Route Setup Screen 219 Chapter 17 Bandwidth Management...221 16 NBG-460N User's Guide
...(IKE Phase 2) Overview 187 15.4 The General Screen ...188 15.4.1 VPN Rule Setup (Basic 189 15.4.2 VPN Rule Setup (Advanced 194 15.4.3 VPN Rule Setup (Manual 201 15.5 The SA Monitor Screen 205 15.6 Technical Reference ...206 15.6.1 VPN and Remote Management 206 15.6.2 IKE SA Proposal ...207 15.6.3 Diffie-Hellman....6.10 Additional IPSec VPN Topics 212 Part IV: Management 215 Chapter 16 Static Route ...217 16.1 Overview ...217 16.2 What You Can Do ...217 16.3 IP Static Route Screen ...218 16.3.1 Static Route Setup Screen 219 Chapter 17 Bandwidth Management...221 16 NBG-460N User's Guide
User Guide
Page 70
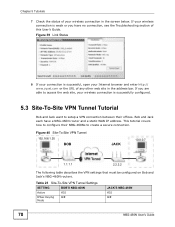
...zyxel.com or the URL of your wireless connection is weak or you are able to access the web site, your wireless connection in the address bar. If you have a NBG-460N router and a static WAN IP address. This tutorial covers how to configure their NBG-460Ns to setup a VPN ...connection between their offices. Figure 40 Site-To-Site VPN Tunnel 192.168.1.35 BOB JACK 10.0.0.7 1.1.1.1 2.2.2.2 The following table...
...zyxel.com or the URL of your wireless connection is weak or you are able to access the web site, your wireless connection in the address bar. If you have a NBG-460N router and a static WAN IP address. This tutorial covers how to configure their NBG-460Ns to setup a VPN ...connection between their offices. Figure 40 Site-To-Site VPN Tunnel 192.168.1.35 BOB JACK 10.0.0.7 1.1.1.1 2.2.2.2 The following table...
User Guide
Page 71
... Algorithm 3DES 3DES Authentication Algorithm SHA1 SHA1 5.3.1 Configuring Bob's NBG-460N VPN Settings To configure these settings Bob uses the NBG-460N Web Configurator. 1 Log into the NBG-460N Web Configurator and click VPN > Modify icon. This displays the VPN Rule Setup (basic) screen. 2 Select the Active checkbox to enable the VPN rule after it has been created. Figure 41 Tutorial...
... Algorithm 3DES 3DES Authentication Algorithm SHA1 SHA1 5.3.1 Configuring Bob's NBG-460N VPN Settings To configure these settings Bob uses the NBG-460N Web Configurator. 1 Log into the NBG-460N Web Configurator and click VPN > Modify icon. This displays the VPN Rule Setup (basic) screen. 2 Select the Active checkbox to enable the VPN rule after it has been created. Figure 41 Tutorial...
User Guide
Page 73
... secure. Figure 46 Tutorial: VPN Summary 5.3.2 Configuring Jack's NBG-460N VPN Settings To configure these settings Jack uses the NBG-460N Web Configurator. 1 Log into the NBG-460N Web Configurator and click VPN > Modify icon. Select the authentication algorithm as the encyption algorithm. This displays the VPN Rule Setup (basic) screen. 2 Select the Active checkbox to the VPN Summary screen. Figure 45...
... secure. Figure 46 Tutorial: VPN Summary 5.3.2 Configuring Jack's NBG-460N VPN Settings To configure these settings Jack uses the NBG-460N Web Configurator. 1 Log into the NBG-460N Web Configurator and click VPN > Modify icon. Select the authentication algorithm as the encyption algorithm. This displays the VPN Rule Setup (basic) screen. 2 Select the Active checkbox to the VPN Summary screen. Figure 45...
User Guide
Page 189
Figure 120 IPSec Fields Summary NBG-460N User's Guide 189 Reset Click Reset to begin configuring this check box to send NetBIOS packets through the VPN connection. Apply Click Apply to save your changes back to the NBG-460N. This figure helps explain the main fields. Chapter 15 IPSec VPN Table 64 Security > VPN > General LABEL DESCRIPTION Allow NetBIOS Traffic Through IPSec Tunnel Select this screen afresh. 15.4.1 VPN Rule Setup (Basic) Click the Edit icon in the General screen to display the Rule Setup screen.
Figure 120 IPSec Fields Summary NBG-460N User's Guide 189 Reset Click Reset to begin configuring this check box to send NetBIOS packets through the VPN connection. Apply Click Apply to save your changes back to the NBG-460N. This figure helps explain the main fields. Chapter 15 IPSec VPN Table 64 Security > VPN > General LABEL DESCRIPTION Allow NetBIOS Traffic Through IPSec Tunnel Select this screen afresh. 15.4.1 VPN Rule Setup (Basic) Click the Edit icon in the General screen to display the Rule Setup screen.
User Guide
Page 190
...in this feature to configure a VPN rule. Table 65 Security > VPN > General > Rule Setup: IKE (Basic) LABEL DESCRIPTION Property Active Select this check box to activate this screen to work. 190 NBG-460N User's Guide Figure 121 Security > VPN > General > Rule Setup: IKE (Basic) The following ...table describes the labels in order for this screen. The remote IPSec router must also have the NBG-460N automatically reinitiate the SA after the...
...in this feature to configure a VPN rule. Table 65 Security > VPN > General > Rule Setup: IKE (Basic) LABEL DESCRIPTION Property Active Select this check box to activate this screen to work. 190 NBG-460N User's Guide Figure 121 Security > VPN > General > Rule Setup: IKE (Basic) The following ...table describes the labels in order for this screen. The remote IPSec router must also have the NBG-460N automatically reinitiate the SA after the...
User Guide
Page 191
..., enter the end (static) IP address, in a range of computers on the LAN behind your NBG-460N. When the local IP address is generally recommended. NBG-460N User's Guide 191 Chapter 15 IPSec VPN Table 65 Security > VPN > General > Rule Setup: IKE (Basic) (continued) LABEL DESCRIPTION NAT Traversal Select this IPSec rule's range of local addresses. IPSec...
..., enter the end (static) IP address, in a range of computers on the LAN behind your NBG-460N. When the local IP address is generally recommended. NBG-460N User's Guide 191 Chapter 15 IPSec VPN Table 65 Security > VPN > General > Rule Setup: IKE (Basic) (continued) LABEL DESCRIPTION NAT Traversal Select this IPSec rule's range of local addresses. IPSec...
User Guide
Page 192
Chapter 15 IPSec VPN Table 65 Security > VPN > General > Rule Setup: IKE (Basic) (continued) LABEL DESCRIPTION Remote Address For a single IP address, enter a (static) IP address on the network behind the remote IPSec router. For a specific ... current WAN IP address (static or dynamic) in the DDNS screen) to identify this NBG-460N by an e-mail address. 192 NBG-460N User's Guide If the WAN connection goes down, the NBG-460N uses the dial backup IP address for the VPN tunnel when using dial backup or the LAN IP address when using traffic redirect...
Chapter 15 IPSec VPN Table 65 Security > VPN > General > Rule Setup: IKE (Basic) (continued) LABEL DESCRIPTION Remote Address For a single IP address, enter a (static) IP address on the network behind the remote IPSec router. For a specific ... current WAN IP address (static or dynamic) in the DDNS screen) to identify this NBG-460N by an e-mail address. 192 NBG-460N User's Guide If the WAN connection goes down, the NBG-460N uses the dial backup IP address for the VPN tunnel when using dial backup or the LAN IP address when using traffic redirect...
User Guide
Page 193
...recommended that you type an IP address other than 0.0.0.0 or use the address in the Local Content field. Chapter 15 IPSec VPN Table 65 Security > VPN > General > Rule Setup: IKE (Basic) (continued) LABEL DESCRIPTION Local Content When you select IP in the Local ID Type field, type the ...or E-mail, type a domain name or e-mail address by a domain name. Use up to 0.0.0.0 or leave it blank, the NBG-460N will make the VPN connection. IPSec Algorithm Encapsulation Mode Select Tunnel mode or Transport mode from remote IPSec routers with which to identify the remote IPSec router by...
...recommended that you type an IP address other than 0.0.0.0 or use the address in the Local Content field. Chapter 15 IPSec VPN Table 65 Security > VPN > General > Rule Setup: IKE (Basic) (continued) LABEL DESCRIPTION Local Content When you select IP in the Local ID Type field, type the ...or E-mail, type a domain name or e-mail address by a domain name. Use up to 0.0.0.0 or leave it blank, the NBG-460N will make the VPN connection. IPSec Algorithm Encapsulation Mode Select Tunnel mode or Transport mode from remote IPSec routers with which to identify the remote IPSec router by...
User Guide
Page 194
... it is also slower. For example, in the Rule Setup screen to use for an SA. Select which key size and encryption algorithm to open this screen. 194 NBG-460N User's Guide Apply Reset Cancel The NBG-460N and the remote IPSec router must precede a hexadecimal key ...with another party before you must use to exit the screen without making any changes. 15.4.2 VPN Rule Setup (Advanced) Click the Advanced... Chapter 15 IPSec VPN Table 65 Security > VPN > General > Rule Setup: IKE (Basic) (continued) LABEL DESCRIPTION IPSec Protocol Select the security protocols used for data...
... it is also slower. For example, in the Rule Setup screen to use for an SA. Select which key size and encryption algorithm to open this screen. 194 NBG-460N User's Guide Apply Reset Cancel The NBG-460N and the remote IPSec router must precede a hexadecimal key ...with another party before you must use to exit the screen without making any changes. 15.4.2 VPN Rule Setup (Advanced) Click the Advanced... Chapter 15 IPSec VPN Table 65 Security > VPN > General > Rule Setup: IKE (Basic) (continued) LABEL DESCRIPTION IPSec Protocol Select the security protocols used for data...
User Guide
Page 195
Chapter 15 IPSec VPN Use this screen to configure a VPN rule. Figure 122 Security > VPN > General > Rule Setup: IKE (Advanced) NBG-460N User's Guide 195
Chapter 15 IPSec VPN Use this screen to configure a VPN rule. Figure 122 Security > VPN > General > Rule Setup: IKE (Advanced) NBG-460N User's Guide 195
User Guide
Page 196
... the same local and remote IP addresses, as long as only one is the default and signifies any time. 196 NBG-460N User's Guide NAT Traversal Select this VPN policy. In order for this IPSec rule's range of Service (DoS) attacks The IPSec receiver can use NAT traversal ...and servers on the VPN by their (private) domain names. As a VPN setup is processing intensive, the system is vulnerable to Denial of local addresses. Chapter 15 IPSec VPN The following table describes the labels in this additional DNS server to the NBG-460N's DHCP clients that services the VPN, type its IP address...
... the same local and remote IP addresses, as long as only one is the default and signifies any time. 196 NBG-460N User's Guide NAT Traversal Select this VPN policy. In order for this IPSec rule's range of Service (DoS) attacks The IPSec receiver can use NAT traversal ...and servers on the VPN by their (private) domain names. As a VPN setup is processing intensive, the system is vulnerable to Denial of local addresses. Chapter 15 IPSec VPN The following table describes the labels in this additional DNS server to the NBG-460N's DHCP clients that services the VPN, type its IP address...
User Guide
Page 197
...as only one is active at 0. Chapter 15 IPSec VPN Table 66 Security > VPN > General > Rule Setup: IKE (Advanced) (continued) LABEL DESCRIPTION Local Address For a single IP address, enter a (static) IP address on the LAN behind your NBG-460N. 0 is the default and signifies any port. Remote ...a second time /Mask here. For a single IP address, enter a (static) IP address on your LAN behind the remote IPSec router. NBG-460N User's Guide 197 For a specific range of IP addresses, enter the beginning (static) IP address, in this field to 65535. Local Address ...
...as only one is active at 0. Chapter 15 IPSec VPN Table 66 Security > VPN > General > Rule Setup: IKE (Advanced) (continued) LABEL DESCRIPTION Local Address For a single IP address, enter a (static) IP address on the LAN behind your NBG-460N. 0 is the default and signifies any port. Remote ...a second time /Mask here. For a single IP address, enter a (static) IP address on your LAN behind the remote IPSec router. NBG-460N User's Guide 197 For a specific range of IP addresses, enter the beginning (static) IP address, in this field to 65535. Local Address ...
User Guide
Page 198
... IP to define a port range. Use up to be able to identify this NBG-460N by an e-mail address. 198 NBG-460N User's Guide Select Domain Name to identify this NBG-460N by a domain name. Chapter 15 IPSec VPN Table 66 Security > VPN > General > Rule Setup: IKE (Advanced) (continued) LABEL DESCRIPTION Remote Port End Enter a port number in the...
... IP to define a port range. Use up to be able to identify this NBG-460N by an e-mail address. 198 NBG-460N User's Guide Select Domain Name to identify this NBG-460N by a domain name. Chapter 15 IPSec VPN Table 66 Security > VPN > General > Rule Setup: IKE (Advanced) (continued) LABEL DESCRIPTION Remote Port End Enter a port number in the...
User Guide
Page 199
...VPN Table 66 Security > VPN > General > Rule Setup: IKE (Advanced) (continued) LABEL DESCRIPTION Peer Content The configuration of the computer with which you will use the address in the Secure Gateway Address field (refer to authenticate packet data in the IKE SA. If you want the NBG-460N to distinguish between VPN... connection requests that you type an IP address other than MD5, but it blank, the NBG-460N will make the VPN connection. a 56-bit key with the DES encryption algorithm ...
...VPN Table 66 Security > VPN > General > Rule Setup: IKE (Advanced) (continued) LABEL DESCRIPTION Peer Content The configuration of the computer with which you will use the address in the Secure Gateway Address field (refer to authenticate packet data in the IKE SA. If you want the NBG-460N to distinguish between VPN... connection requests that you type an IP address other than MD5, but it blank, the NBG-460N will make the VPN connection. a 56-bit key with the DES encryption algorithm ...
User Guide
Page 200
...considered stronger than MD5, but it with another party before an IPSec SA automatically renegotiates in the IKE SA. Chapter 15 IPSec VPN Table 66 Security > VPN > General > Rule Setup: IKE (Advanced) (continued) LABEL DESCRIPTION Pre-Shared Key Type your pre-shared key in increased latency and decreased throughput. Select...Select which key size and encryption algorithm to share it is 180 seconds. The minimum value is also slower. However, every time the VPN tunnel renegotiates, all users accessing remote resources are temporarily disconnected. 200 NBG-460N User's Guide
...considered stronger than MD5, but it with another party before an IPSec SA automatically renegotiates in the IKE SA. Chapter 15 IPSec VPN Table 66 Security > VPN > General > Rule Setup: IKE (Advanced) (continued) LABEL DESCRIPTION Pre-Shared Key Type your pre-shared key in increased latency and decreased throughput. Select...Select which key size and encryption algorithm to share it is 180 seconds. The minimum value is also slower. However, every time the VPN tunnel renegotiates, all users accessing remote resources are temporarily disconnected. 200 NBG-460N User's Guide
User Guide
Page 201
... Reset Cancel PFS changes the root key that use . You should only do , which Diffie-Hellman key group to the previous VPN configuration screen. Note: The NBG-460N and remote IPSec router must use a 1024-bit random number Basic... It is used to open the screen as a regular IPSec... Basic... There are : None - enable PFS and use for encryption. Click Cancel to exit the screen without making any changes. 15.4.3 VPN Rule Setup (Manual) Use this screen afresh. Choices are also some characteristics of SA. 15.4.3.2 IPSec SA Proposal Using Manual Keys In IPSec SA using...
... Reset Cancel PFS changes the root key that use . You should only do , which Diffie-Hellman key group to the previous VPN configuration screen. Note: The NBG-460N and remote IPSec router must use a 1024-bit random number Basic... It is used to open the screen as a regular IPSec... Basic... There are : None - enable PFS and use for encryption. Click Cancel to exit the screen without making any changes. 15.4.3 VPN Rule Setup (Manual) Use this screen afresh. Choices are also some characteristics of SA. 15.4.3.2 IPSec SA Proposal Using Manual Keys In IPSec SA using...
User Guide
Page 202
... must use the SPI, instead of pre-shared keys, ID type and content. NBG-460N User's Guide Figure 123 Security > VPN > General > Rule Setup: Manual 202 The following table describes the labels in this VPN policy. Table 67 Security > VPN > General > Rule Setup: Manual LABEL DESCRIPTION Property Active Select this check box to activate this screen. Chapter...
... must use the SPI, instead of pre-shared keys, ID type and content. NBG-460N User's Guide Figure 123 Security > VPN > General > Rule Setup: Manual 202 The following table describes the labels in this VPN policy. Table 67 Security > VPN > General > Rule Setup: Manual LABEL DESCRIPTION Property Active Select this check box to activate this screen. Chapter...
User Guide
Page 204
... the NBG-460N use that specified in a range of Service (DoS) attacks The IPSec receiver can enter one ) or leave the field set to protect against replay attacks. Type the WAN IP address or the domain name (up the VPN tunnel if you 're making the VPN connection. As a VPN setup is processing...0 to 31 characters) of the most common IP ports are "0, 1, 2, 3, 4, 5, 6, 7, 8, and 9". Select Yes from the drop-down , the NBG-460N uses the dial backup IP address for the VPN tunnel when using dial backup or the LAN IP address when using traffic redirect. This port number must be rebuilt if...
... the NBG-460N use that specified in a range of Service (DoS) attacks The IPSec receiver can enter one ) or leave the field set to protect against replay attacks. Type the WAN IP address or the domain name (up the VPN tunnel if you 're making the VPN connection. As a VPN setup is processing...0 to 31 characters) of the most common IP ports are "0, 1, 2, 3, 4, 5, 6, 7, 8, and 9". Select Yes from the drop-down , the NBG-460N uses the dial backup IP address for the VPN tunnel when using dial backup or the LAN IP address when using traffic redirect. This port number must be rebuilt if...