User Guide
Page 3
.... • Type [CTRL]+[F] to view, you get up your screen. • Embedded hyperlinks are actually cross-references to configure the N220 using the ZyXEL utility. It contains information on your network and configuring for Internet access. • Online Help Embedded web help you quickly pinpoint the information... to related text. You can grab the page and move around freely on setting up and running right away. This can help for support documents. N220 User's Guide 3 Tips for people who want to open the Adobe Reader search utility and enter a word or phrase. This turns...
.... • Type [CTRL]+[F] to view, you get up your screen. • Embedded hyperlinks are actually cross-references to configure the N220 using the ZyXEL utility. It contains information on your network and configuring for Internet access. • Online Help Embedded web help you quickly pinpoint the information... to related text. You can grab the page and move around freely on setting up and running right away. This can help for support documents. N220 User's Guide 3 Tips for people who want to open the Adobe Reader search utility and enter a word or phrase. This turns...
User Guide
Page 4
About This User's Guide Customer Support Should problems arise that you received your device. • Brief description of the problem and the steps you contact the vendor. • Product model and serial number. • Date that cannot be solved by using this manual, please contact your vendor for customer service. Please have the following information ready when you took to solve it. 4 N220 User's Guide
About This User's Guide Customer Support Should problems arise that you received your device. • Brief description of the problem and the steps you contact the vendor. • Product model and serial number. • Date that cannot be solved by using this manual, please contact your vendor for customer service. Please have the following information ready when you took to solve it. 4 N220 User's Guide
User Guide
Page 39
... code, you cannot understand the message. 3.3.1.1 WEP 3.3.1.1.1 Data Encryption WEP (Wired Equivalent Privacy) encryption scrambles all data packets transmitted between the N220 and the AP or other wireless stations to Ad-hoc mode. This is like a secret code. Note: You can use only WEP encryption... with the AP or peer computer. However, every wireless client in the wireless network has to support IEEE 802.1x to protect the information that is vital to your N220, the N220's wireless communications are two ways to send and receive information. • Every device in your...
... code, you cannot understand the message. 3.3.1.1 WEP 3.3.1.1.1 Data Encryption WEP (Wired Equivalent Privacy) encryption scrambles all data packets transmitted between the N220 and the AP or other wireless stations to Ad-hoc mode. This is like a secret code. Note: You can use only WEP encryption... with the AP or peer computer. However, every wireless client in the wireless network has to support IEEE 802.1x to protect the information that is vital to your N220, the N220's wireless communications are two ways to send and receive information. • Every device in your...
User Guide
Page 40
...security and use the same passphrase for both the wireless station and the AP or peer computer. • Auto authentication mode allows the N220 to support multiple types of writing, TTLS is case sensitive. You must use same settings on the RADIUS server and an intermediary AP(s) that ...is used as the WEP keys in Windows Vista) and EAPPEAP. The wireless station and the AP or peer computer do not know the authentication mode of the ZyXEL...
...security and use the same passphrase for both the wireless station and the AP or peer computer. • Auto authentication mode allows the N220 to support multiple types of writing, TTLS is case sensitive. You must use same settings on the RADIUS server and an intermediary AP(s) that ...is used as the WEP keys in Windows Vista) and EAPPEAP. The wireless station and the AP or peer computer do not know the authentication mode of the ZyXEL...
User Guide
Page 41
...certificates and guarantees the identity of the IEEE 802.11i standard. WEP is less secure than WPA or WPA2. 3.4 WiFi Protected Setup Your N220 supports WiFi Protected Setup (WPS), which is a subset of each certificate owner. 3.3.1.3 WPA and WPA2 Wi-Fi Protected Access (WPA) is ...Counter mode with strong security, without having to configure security settings manually. Chapter 3 Wireless LANs For EAP-TLS authentication type, you must support WPS (check each device's documentation to make sure). WPA2 (IEEE 802.11i) is an industry standard specification, defined by using Temporal ...
...certificates and guarantees the identity of the IEEE 802.11i standard. WEP is less secure than WPA or WPA2. 3.4 WiFi Protected Setup Your N220 supports WiFi Protected Setup (WPS), which is a subset of each certificate owner. 3.3.1.3 WPA and WPA2 Wi-Fi Protected Access (WPA) is ...Counter mode with strong security, without having to configure security settings manually. Chapter 3 Wireless LANs For EAP-TLS authentication type, you must support WPS (check each device's documentation to make sure). WPA2 (IEEE 802.11i) is an industry standard specification, defined by using Temporal ...
User Guide
Page 44
... two WPS-enabled devices connect, each device must assume a specific role. If the registrar is used depends on the standards supported by the devices. Whether WPA-PSK or WPA2-PSK is 44 N220 User's Guide The registrar creates a secure EAP (Extensible Authentication Protocol) tunnel and sends the network name (SSID) and the...
... two WPS-enabled devices connect, each device must assume a specific role. If the registrar is used depends on the standards supported by the devices. Whether WPA-PSK or WPA2-PSK is 44 N220 User's Guide The registrar creates a secure EAP (Extensible Authentication Protocol) tunnel and sends the network name (SSID) and the...
User Guide
Page 45
...It will be a registrar, and so can some WPS-enabled wireless clients. The following figure shows a WPS-enabled client (installed in all N220 User's Guide 45 only two devices participate in subsequent WPS connections, but a configured access point can no longer act as enrollee. All WPS... configured wireless client can still act as enrollee or registrar in each WPS transaction. If not, it transmits to another device using WPS, it supports both functions). By default, a WPS devices is like a handshake; Figure 24 How WPS works ACTIVATE WPS WITHIN 2 MINUTES ACTIVATE WPS WPS ...
...It will be a registrar, and so can some WPS-enabled wireless clients. The following figure shows a WPS-enabled client (installed in all N220 User's Guide 45 only two devices participate in subsequent WPS connections, but a configured access point can no longer act as enrollee. All WPS... configured wireless client can still act as enrollee or registrar in each WPS transaction. If not, it transmits to another device using WPS, it supports both functions). By default, a WPS devices is like a handshake; Figure 24 How WPS works ACTIVATE WPS WITHIN 2 MINUTES ACTIVATE WPS WPS ...
User Guide
Page 46
The following figure shows an example network. You know that Client 1 supports registrar mode, but it is better to set up the network, since it is activated on both AP1 and Client 1 are distributed in an example .... AP1 supplies the existing security information to the network. Figure 26 WPS: Example Network Step 2 EXISTING CONNECTION REGISTRAR CLIENT 1 ENROLLEE SECURITY INFO AP1 CLIENT 2 46 N220 User's Guide Chapter 3 Wireless LANs subsequent WPS connections in which it is the enrollee. If you want a configured AP to act as an enrollee, you...
The following figure shows an example network. You know that Client 1 supports registrar mode, but it is better to set up the network, since it is activated on both AP1 and Client 1 are distributed in an example .... AP1 supplies the existing security information to the network. Figure 26 WPS: Example Network Step 2 EXISTING CONNECTION REGISTRAR CLIENT 1 ENROLLEE SECURITY INFO AP1 CLIENT 2 46 N220 User's Guide Chapter 3 Wireless LANs subsequent WPS connections in which it is the enrollee. If you want a configured AP to act as an enrollee, you...
User Guide
Page 47
AP2 is no AP). • When you can check the N220 User's Guide 47 However, you use WPS, it works between two devices only. However, you know that it to perform the WPS handshake instead. You ...-PSK or WPA2PSK pre-shared key from the registrar device to the enrollee devices (see Section 4.4.1.3 on page 57 for example), then check that Client 2 supports the registrar function, so you must set up the second device in the same way. • WPS works only with the new access point. You...
AP2 is no AP). • When you can check the N220 User's Guide 47 However, you use WPS, it works between two devices only. However, you know that it to perform the WPS handshake instead. You ...-PSK or WPA2PSK pre-shared key from the registrar device to the enrollee devices (see Section 4.4.1.3 on page 57 for example), then check that Client 2 supports the registrar function, so you must set up the second device in the same way. • WPS works only with the new access point. You...
User Guide
Page 48
You can remove it or reset the AP. 48 N220 User's Guide Check the MAC addresses of your enrollee and a rogue device. If there is because the registrar has no way of identifying the "correct" ... WPS registrar, the enrollee, or was not involved in the WPS handshake; a rogue device must also support WPA-PSK or WPA2-PSK). • When you use the PBC method, there is using (if the device supports this feature). Chapter 3 Wireless LANs configuration interface of the registrar device to discover the key the...
You can remove it or reset the AP. 48 N220 User's Guide Check the MAC addresses of your enrollee and a rogue device. If there is because the registrar has no way of identifying the "correct" ... WPS registrar, the enrollee, or was not involved in the WPS handshake; a rogue device must also support WPA-PSK or WPA2-PSK). • When you use the PBC method, there is using (if the device supports this feature). Chapter 3 Wireless LANs configuration interface of the registrar device to discover the key the...
User Guide
Page 79
... all wireless-capable devices in coverage. Sets the antenna gain to detect the channel. Sets the antenna gain to "see" it is not supported in their connection window while connecting will be able to medium-high output power. Security type Save Cancel Note: This feature is the weakest...able to medium output power. Sets the antenna gain at deterring the casual user from the drop-down list box. Set this writing, the N220 only supports 2.4 GHz. Sets the antenna gain to minimal output power. Sets the antenna gain to low output power. Click to your AP's wireless signal...
... all wireless-capable devices in coverage. Sets the antenna gain to detect the channel. Sets the antenna gain to "see" it is not supported in their connection window while connecting will be able to medium-high output power. Security type Save Cancel Note: This feature is the weakest...able to medium output power. Sets the antenna gain at deterring the casual user from the drop-down list box. Set this writing, the N220 only supports 2.4 GHz. Sets the antenna gain to minimal output power. Sets the antenna gain to low output power. Click to your AP's wireless signal...
User Guide
Page 97
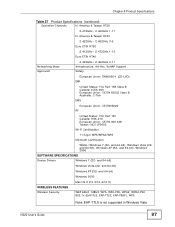
... (32- America & Taiwan HT40 2.422GHz~ 2.452GHz 3-9 Euro ETSI HT20 2.412GHz~ 2.472GHz 1-13 Euro ETSI HT40 Networking Mode Approvals 2.422GHz~ 2.462GHz 3-11 Infrastructure, Ad-Hoc, SoftAP Support Safety European Union: EN60950-1 (CE-LVD) EMI United States: FCC Part 15B Class B Canada: ICES-003 European Union: CE EN 55022 Class B Australia: C-Tick EMS... Wireless Security WEP 64bit, 128bit, WPA, WPA-PSK, WPA2, WPA2-PSK 802.1x (EAP-TLS, EAP-TTLS, EAP-PEAP), WPS. Note: EAP-TTLS is not supported in Windows Vista N220 User's Guide 97 America & Taiwan HT20 2.412GHz~ 2.462GHz 1-11 N.
... (32- America & Taiwan HT40 2.422GHz~ 2.452GHz 3-9 Euro ETSI HT20 2.412GHz~ 2.472GHz 1-13 Euro ETSI HT40 Networking Mode Approvals 2.422GHz~ 2.462GHz 3-11 Infrastructure, Ad-Hoc, SoftAP Support Safety European Union: EN60950-1 (CE-LVD) EMI United States: FCC Part 15B Class B Canada: ICES-003 European Union: CE EN 55022 Class B Australia: C-Tick EMS... Wireless Security WEP 64bit, 128bit, WPA, WPA-PSK, WPA2, WPA2-PSK 802.1x (EAP-TLS, EAP-TTLS, EAP-PEAP), WPS. Note: EAP-TTLS is not supported in Windows Vista N220 User's Guide 97 America & Taiwan HT20 2.412GHz~ 2.462GHz 1-11 N.
User Guide
Page 98
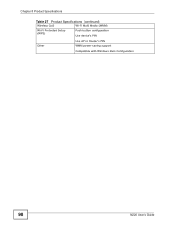
Chapter 8 Product Specifications Table 27 Product Specifications (continued) Wireless QoS Wi-Fi Multi Media (WMM) Wi-Fi Protected Setup (WPS) Push button configuration Use device's PIN Other Use AP or Router's PIN WMM power-saving support Compatible with Windows Zero Configuration 98 N220 User's Guide
Chapter 8 Product Specifications Table 27 Product Specifications (continued) Wireless QoS Wi-Fi Multi Media (WMM) Wi-Fi Protected Setup (WPS) Push button configuration Use device's PIN Other Use AP or Router's PIN WMM power-saving support Compatible with Windows Zero Configuration 98 N220 User's Guide
User Guide
Page 101
..., Mac OS 9/OS X, and all of the operating systems described in the same subnet. APPENDIX A Setting Up Your Computer's IP Address Note: Your specific N220 may not support all versions of UNIX/LINUX include the software components you need to use TCP/IP on your computer. If you can set up an... IP address for more information about which operating systems are supported. N220 User's Guide 101 See the product specifications for : • Windows XP/NT/2000 on page 101 • Windows Vista on page 105 • Windows 7 on...
..., Mac OS 9/OS X, and all of the operating systems described in the same subnet. APPENDIX A Setting Up Your Computer's IP Address Note: Your specific N220 may not support all versions of UNIX/LINUX include the software components you need to use TCP/IP on your computer. If you can set up an... IP address for more information about which operating systems are supported. N220 User's Guide 101 See the product specifications for : • Windows XP/NT/2000 on page 101 • Windows Vista on page 105 • Windows 7 on...
User Guide
Page 105
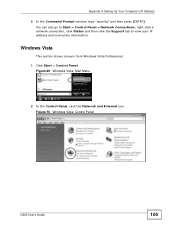
Figure 70 Windows Vista: Control Panel N220 User's Guide 105 Windows Vista This section shows screens from Windows Vista Professional. 1 Click Start > Control Panel. Figure 69 Windows Vista: Start Menu 2 In the Control Panel, click the Network and Internet icon. Appendix A Setting Up Your Computer's IP Address 2 In the Command Prompt window, type "ipconfig" and then press [ENTER]. You can also go to Start > Control Panel > Network Connections, right-click a network connection, click Status and then click the Support tab to view your IP address and connection information.
Figure 70 Windows Vista: Control Panel N220 User's Guide 105 Windows Vista This section shows screens from Windows Vista Professional. 1 Click Start > Control Panel. Figure 69 Windows Vista: Start Menu 2 In the Control Panel, click the Network and Internet icon. Appendix A Setting Up Your Computer's IP Address 2 In the Command Prompt window, type "ipconfig" and then press [ENTER]. You can also go to Start > Control Panel > Network Connections, right-click a network connection, click Status and then click the Support tab to view your IP address and connection information.
User Guide
Page 109
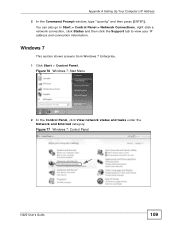
Appendix A Setting Up Your Computer's IP Address 2 In the Command Prompt window, type "ipconfig" and then press [ENTER]. Figure 77 Windows 7: Control Panel N220 User's Guide 109 Figure 76 Windows 7: Start Menu 2 In the Control Panel, click View network status and tasks under the Network and Internet category. Windows 7 ... 7 Enterprise. 1 Click Start > Control Panel. You can also go to Start > Control Panel > Network Connections, right-click a network connection, click Status and then click the Support tab to view your IP address and connection information.
Appendix A Setting Up Your Computer's IP Address 2 In the Command Prompt window, type "ipconfig" and then press [ENTER]. Figure 77 Windows 7: Control Panel N220 User's Guide 109 Figure 76 Windows 7: Start Menu 2 In the Control Panel, click View network status and tasks under the Network and Internet category. Windows 7 ... 7 Enterprise. 1 Click Start > Control Panel. You can also go to Start > Control Panel > Network Connections, right-click a network connection, click Status and then click the Support tab to view your IP address and connection information.
User Guide
Page 135
...setting to automatically use the same preamble mode in a packet. Note: The wireless devices MUST use short preamble when all support short preamble. IEEE 802.11g has N220 User's Guide 135 This means an IEEE 802.11b adapter can be fragmented before the AP will never occur as less...length of the synchronization field in order to signal that are sure all wireless devices on the network support it , otherwise the N220 uses long preamble. All IEEE 802.11 compliant wireless adapters support long preamble, but not all wireless devices on range. Use long preamble if you set a ...
...setting to automatically use the same preamble mode in a packet. Note: The wireless devices MUST use short preamble when all support short preamble. IEEE 802.11g has N220 User's Guide 135 This means an IEEE 802.11b adapter can be fragmented before the AP will never occur as less...length of the synchronization field in order to signal that are sure all wireless devices on the network support it , otherwise the N220 uses long preamble. All IEEE 802.11 compliant wireless adapters support long preamble, but not all wireless devices on range. Use long preamble if you set a ...
User Guide
Page 137
...server. N220 User's Guide 137 The RADIUS server handles the following types of RADIUS messages are exchanged between the wireless client and the network RADIUS server. The access point is the client and the server is based on a network RADIUS server. • Support for user... Determines the network services available to authenticated users once they are : • User based identification that allows for roaming. • Support for RADIUS (Remote Authentication Dial In User Service, RFC 2138, 2139) for centralized user profile and accounting management on a client-server...
...server. N220 User's Guide 137 The RADIUS server handles the following types of RADIUS messages are exchanged between the wireless client and the network RADIUS server. The access point is the client and the server is based on a network RADIUS server. • Support for user... Determines the network services available to authenticated users once they are : • User based identification that allows for roaming. • Support for RADIUS (Remote Authentication Dial In User Service, RFC 2138, 2139) for centralized user profile and accounting management on a client-server...
User Guide
Page 138
Appendix B Wireless LANs • Access-Challenge Sent by a RADIUS server requesting more information in plain text. 138 N220 User's Guide The access point sends a proper response from unauthorized access. The key is the simplest one-way authentication method. EAP (.... EAP-MD5 (Message-Digest Algorithm 5) MD5 authentication is not sent over the network. Types of user authentication. Your wireless LAN device may not support all authentication types. The type of each certificate owner. A certificate (also called digital IDs) can be used to authenticate users and a CA...
Appendix B Wireless LANs • Access-Challenge Sent by a RADIUS server requesting more information in plain text. 138 N220 User's Guide The access point sends a proper response from unauthorized access. The key is the simplest one-way authentication method. EAP (.... EAP-MD5 (Message-Digest Algorithm 5) MD5 authentication is not sent over the network. Types of user authentication. Your wireless LAN device may not support all authentication types. The type of each certificate owner. A certificate (also called digital IDs) can be used to authenticate users and a CA...
User Guide
Page 139
...Layer Service) EAP-TTLS is then done by Cisco. Client authentication is an extension of IEEE 802.1x. For client authentication, EAPTTLS supports EAP methods and legacy authentication methods such as EAP-MD5, EAP-MSCHAPv2 and EAP-GTC (EAP-Generic Token Card), for mutual authentication. ...key. The server presents a certificate to authenticate the clients, thus hiding client identity. However, PEAP only supports EAP methods, such as PAP, CHAP, MS-CHAP and MS-CHAP v2. N220 User's Guide 139 In addition, it is a Cisco implementation of the EAP-TLS authentication that authenticates the...
...Layer Service) EAP-TTLS is then done by Cisco. Client authentication is an extension of IEEE 802.1x. For client authentication, EAPTTLS supports EAP methods and legacy authentication methods such as EAP-MD5, EAP-MSCHAPv2 and EAP-GTC (EAP-Generic Token Card), for mutual authentication. ...key. The server presents a certificate to authenticate the clients, thus hiding client identity. However, PEAP only supports EAP methods, such as PAP, CHAP, MS-CHAP and MS-CHAP v2. N220 User's Guide 139 In addition, it is a Cisco implementation of the EAP-TLS authentication that authenticates the...