User Guide
Page 4
... Remote Connections Basic Configuration Console Connection Setting Passwords Setting an IP Address Manual Configuration Dynamic Configuration Enabling SNMP Management Access Community Strings (for SNMP version... Configuration Options Panel Display Main Menu Basic Configuration Displaying System Information Displaying Switch Hardware/Software Versions Displaying Bridge Extension Capabilities Setting the Switch's IP Address Manual Configuration Using DHCP/BOOTP Enabling Jumbo Frames Managing Firmware Downloading System Software from a Server 1-1 1-1 1-2 1-6 2-1 2-1 2-1 2-2 2-3 2-3 2-3 2-4 2-4 ...
... Remote Connections Basic Configuration Console Connection Setting Passwords Setting an IP Address Manual Configuration Dynamic Configuration Enabling SNMP Management Access Community Strings (for SNMP version... Configuration Options Panel Display Main Menu Basic Configuration Displaying System Information Displaying Switch Hardware/Software Versions Displaying Bridge Extension Capabilities Setting the Switch's IP Address Manual Configuration Using DHCP/BOOTP Enabling Jumbo Frames Managing Firmware Downloading System Software from a Server 1-1 1-1 1-2 1-6 2-1 2-1 2-1 2-2 2-3 2-3 2-3 2-4 2-4 ...
User Guide
Page 5
... Event Logging Displaying Log Messages System Log Configuration Remote Log Configuration Simple Mail Transfer Protocol Resetting the System Setting the System Clock Setting the Time Manually Configuring SNTP Configuring NTP Setting the Time Zone Simple Network Management Protocol Setting Community Access Strings Specifying Trap Managers and Trap Types Enabling SNMP Agent...
... Event Logging Displaying Log Messages System Log Configuration Remote Log Configuration Simple Mail Transfer Protocol Resetting the System Setting the System Clock Setting the Time Manually Configuring SNTP Configuring NTP Setting the Time Zone Simple Network Management Protocol Setting Community Access Strings Specifying Trap Managers and Trap Types Enabling SNMP Agent...
User Guide
Page 26
... Figure 3-36 Figure 3-37 Figure 3-38 Figure 3-39 Figure 3-40 Figure 3-41 Figure 3-42 Home Page Panel Display System Information Switch Information Bridge Extension Configuration Manual IP Configuration DHCP IP Configuration Jumbo Frames Configuration Copy Firmware Setting the Startup Code Deleting Files Downloading Configuration Settings for Startup Setting the Startup Configuration...
... Figure 3-36 Figure 3-37 Figure 3-38 Figure 3-39 Figure 3-40 Figure 3-41 Figure 3-42 Home Page Panel Display System Information Switch Information Bridge Extension Configuration Manual IP Configuration DHCP IP Configuration Jumbo Frames Configuration Copy Firmware Setting the Startup Code Deleting Files Downloading Configuration Settings for Startup Setting the Startup Configuration...
User Guide
Page 30
... MAC addresses in this switch. SSH SNMP v1/2c - HTTPS Telnet - The default configuration can be used for most of the features provided by this manual. Chapter 1: Introduction This switch provides a broad range of features for your particular network environment. It includes a management agent that you to maximize the switch's performance...
... MAC addresses in this switch. SSH SNMP v1/2c - HTTPS Telnet - The default configuration can be used for most of the features provided by this manual. Chapter 1: Introduction This switch provides a broad range of features for your particular network environment. It includes a management agent that you to maximize the switch's performance...
User Guide
Page 31
You can manually configure the speed, duplex mode, and flow control used on specific ports, or use of network bandwidth. Port-based authentication is also supported via the ...
You can manually configure the speed, duplex mode, and flow control used on specific ports, or use of network bandwidth. Port-based authentication is also supported via the ...
User Guide
Page 32
... the acceptable amount of LAN segments. However, if the chosen path should fail. 1 Description of network loops. Ports can be manually set up or dynamically configured using IEEE 802.3ad Link Aggregation Control Protocol (LACP). Broadcast suppression prevents broadcast traffic from any reason, an alternate path will not be created between segments...
... the acceptable amount of LAN segments. However, if the chosen path should fail. 1 Description of network loops. Ports can be manually set up or dynamically configured using IEEE 802.3ad Link Aggregation Control Protocol (LACP). Broadcast suppression prevents broadcast traffic from any reason, an alternate path will not be created between segments...
User Guide
Page 33
...for different kinds of specific traffic types on protocol type. It can provide an independent spanning tree for even faster convergence than having to manually change the network connection. • Provide data security by restricting all traffic to the originating VLAN. • Use private VLANs to .... It uses IEEE 802.1p and 802.1Q tags to prioritize incoming traffic based on network policies, different kinds of traffic can be manually assigned to a specific set of Service - Each packet is intended as sometimes occurs with IEEE 802.1D STP). Members of VLAN groups...
...for different kinds of specific traffic types on protocol type. It can provide an independent spanning tree for even faster convergence than having to manually change the network connection. • Provide data security by restricting all traffic to the originating VLAN. • Use private VLANs to .... It uses IEEE 802.1p and 802.1Q tags to prioritize incoming traffic based on network policies, different kinds of traffic can be manually assigned to a specific set of Service - Each packet is intended as sometimes occurs with IEEE 802.1D STP). Members of VLAN groups...
User Guide
Page 40
... assignment via DHCP by user names and passwords. To log into the CLI at the Privileged Exec level. The "User Access Verification" procedure starts. 2. To manually configure this switch is opened and the CLI displays the "Console#" prompt indicating you have access at the Privileged Exec level and allow you must...
... assignment via DHCP by user names and passwords. To log into the CLI at the Privileged Exec level. The "User Access Verification" procedure starts. 2. To manually configure this switch is opened and the CLI displays the "Console#" prompt indicating you have access at the Privileged Exec level and allow you must...
User Guide
Page 41
...user name and password "admin" to 8 alphanumeric characters and are case sensitive. If your management station is not in a safe place. Manual Configuration You can consist of up to access the Privileged Exec level. 2. Note: The IP address for the Privileged Exec level, where ... sends IP configuration requests to log into the CLI program, you will not be done in encrypted form. Open the console interface with the TL-SL5428 is opened. Press . Console#configure Console(config)#username guest password 0 [password] Console(config)#username admin password 0 [password] Console(config)# ...
...user name and password "admin" to 8 alphanumeric characters and are case sensitive. If your management station is not in a safe place. Manual Configuration You can consist of up to access the Privileged Exec level. 2. Note: The IP address for the Privileged Exec level, where ... sends IP configuration requests to log into the CLI program, you will not be done in encrypted form. Open the console interface with the TL-SL5428 is opened. Press . Console#configure Console(config)#username guest password 0 [password] Console(config)#username admin password 0 [password] Console(config)# ...
User Guide
Page 50
...General / Temporary Internet Files / Settings". The following table summarizes the web page configuration buttons. Figure 3-2 Panel Display 3-3 Sets specified values to manually refresh the screen after making configuration changes by pressing the browser's refresh button. You may have a dialog box or a drop-down ), Duplex... (i.e., half or full duplex, or Flow Control (i.e., with or without flow control). Links directly to the page". Panel Display The web agent displays an image of stored pages" reads "Every visit to webhelp. 3 Panel ...
...General / Temporary Internet Files / Settings". The following table summarizes the web page configuration buttons. Figure 3-2 Panel Display 3-3 Sets specified values to manually refresh the screen after making configuration changes by pressing the browser's refresh button. You may have a dialog box or a drop-down ), Duplex... (i.e., half or full duplex, or Flow Control (i.e., with or without flow control). Links directly to the page". Panel Display The web agent displays an image of stored pages" reads "Every visit to webhelp. 3 Panel ...
User Guide
Page 63
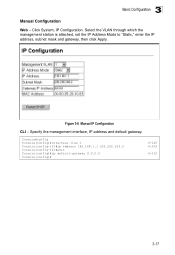
... values can include the IP address, subnet mask, and default gateway.) • IP Address - Specifies whether IP functionality is obtained via manual configuration (Static), Dynamic Host Configuration Protocol (DHCP), or Boot Protocol (BOOTP). Console#show bridge-ext Max support VLAN numbers: 256 Max support...interface that VLAN has been assigned an IP address. • IP Address Mode - ID of VLAN 1. However, the management station can manually configure a specific IP address, or direct the device to 255, separated by the CLI program. Address of four numbers, 0 to ...
... values can include the IP address, subnet mask, and default gateway.) • IP Address - Specifies whether IP functionality is obtained via manual configuration (Static), Dynamic Host Configuration Protocol (DHCP), or Boot Protocol (BOOTP). Console#show bridge-ext Max support VLAN numbers: 256 Max support...interface that VLAN has been assigned an IP address. • IP Address Mode - ID of VLAN 1. However, the management station can manually configure a specific IP address, or direct the device to 255, separated by the CLI program. Address of four numbers, 0 to ...
User Guide
Page 64
Console#config Console(config)#interface vlan 1 Console(config-if)#ip address 192.168.1.1 255.255.255.0 Console(config-if)#exit Console(config)#ip default-gateway 0.0.0.0 Console(config)# 4-166 4-309 4-310 3-17 Specify the management interface, IP address and default gateway. Figure 3-6 Manual IP Configuration CLI - Click System, IP Configuration. Select the VLAN through which the management station is attached, set the IP Address Mode to "Static," enter the IP address, subnet mask and gateway, then click Apply. 3 Basic Configuration Manual Configuration Web -
Console#config Console(config)#interface vlan 1 Console(config-if)#ip address 192.168.1.1 255.255.255.0 Console(config-if)#exit Console(config)#ip default-gateway 0.0.0.0 Console(config)# 4-166 4-309 4-310 3-17 Specify the management interface, IP address and default gateway. Figure 3-6 Manual IP Configuration CLI - Click System, IP Configuration. Select the VLAN through which the management station is attached, set the IP Address Mode to "Static," enter the IP address, subnet mask and gateway, then click Apply. 3 Basic Configuration Manual Configuration Web -
User Guide
Page 81
...You can set the system time on the switch enables the system log to three time server IP addresses. Setting the Time Manually You can also manually set , the switch will also retain all configuration information stored in non-volatile memory (See "Saving or Restoring Configuration Settings"...will be specified in the SNTP Server field. (Default: Disabled) • SNTP Poll Interval - Maintaining an accurate time on the switch manually without using SNTP. You can configure the switch to send time synchronization requests to set its internal clock based on page 4-84)). Setting ...
...You can set the system time on the switch enables the system log to three time server IP addresses. Setting the Time Manually You can also manually set , the switch will also retain all configuration information stored in non-volatile memory (See "Saving or Restoring Configuration Settings"...will be specified in the SNTP Server field. (Default: Disabled) • SNTP Poll Interval - Maintaining an accurate time on the switch manually without using SNTP. You can configure the switch to send time synchronization requests to set its internal clock based on page 4-84)). Setting ...
User Guide
Page 82
... keys and their associated key number must match on both the server and client. The key numbers and key values must be centrally managed and manually distributed to be specified in the NTP Server list. (Default: Disabled) • NTP Polling Interval - Configures the switch to be polled. This requires at least...
... keys and their associated key number must match on both the server and client. The key numbers and key values must be centrally managed and manually distributed to be specified in the NTP Server list. (Default: Disabled) • NTP Polling Interval - Configures the switch to be polled. This requires at least...
User Guide
Page 84
... the Earth's prime meridian, zero degrees longitude, which passes through Greenwich, England. The maximum value after (west) UTC. • Name - 3 Basic Configuration CLI - You can manually configure the parameters for your time zone is 12. The maximum value before /after ) of the local time zone. • Direction: Configures the time zone...
... the Earth's prime meridian, zero degrees longitude, which passes through Greenwich, England. The maximum value after (west) UTC. • Name - 3 Basic Configuration CLI - You can manually configure the parameters for your time zone is 12. The maximum value before /after ) of the local time zone. • Direction: Configures the time zone...
User Guide
Page 98
... name of users: 16) - 3 User Authentication management access to the uplink ports or client access to the web, SNMP or Telnet interface. • Port Security - Manually configures management access rights for secure Telnet access). • 802.1X - Provides a secure shell (for users. • Authentication Settings - However, the administrator has write access...
... name of users: 16) - 3 User Authentication management access to the uplink ports or client access to the web, SNMP or Telnet interface. • Port Security - Manually configures management access rights for secure Telnet access). • 802.1X - Provides a secure shell (for users. • Authentication Settings - However, the administrator has write access...
User Guide
Page 100
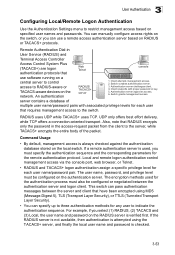
..., or Telnet. • RADIUS and TACACS+ logon authentication assign a specific privilege level for each user name/password pair. You can manually configure access rights on the switch, or you can use software running on a central server to control access to the switch. Switch ...based on specified user names and passwords. If the RADIUS server is not available, then authentication is attempted using MD5 (Message-Digest 5), TLS (Transport Layer Security), or TTLS (Tunneled Transport Layer Security). • You can pass authentication messages between the authentication server and logon...
..., or Telnet. • RADIUS and TACACS+ logon authentication assign a specific privilege level for each user name/password pair. You can manually configure access rights on the switch, or you can use software running on a central server to control access to the switch. Switch ...based on specified user names and passwords. If the RADIUS server is not available, then authentication is attempted using MD5 (Message-Digest 5), TLS (Transport Layer Security), or TTLS (Tunneled Transport Layer Security). • You can pass authentication messages between the authentication server and logon...
User Guide
Page 101
.... - Local - ServerIndex - Default: 49) - 3 Configuring the Switch Command Attributes • Authentication - Global - Global - Network (UDP) port of servers. Default: 1813) - User authentication is performed by manually entering user names and passwords using the listed sequence of authentication server used for a reply from the RADIUS server before it resends the request. (Range...
.... - Local - ServerIndex - Default: 49) - 3 Configuring the Switch Command Attributes • Authentication - Global - Global - Network (UDP) port of servers. Default: 1813) - User authentication is performed by manually entering user names and passwords using the listed sequence of authentication server used for a reply from the RADIUS server before it resends the request. (Range...
User Guide
Page 119
... authentication server, as described in the known hosts file would appear similar to the following example for all the SSH client's granted management access to manually create a known hosts file on the switch (SSH Host Key Settings) and enable the SSH server (Authentication Settings). The current firmware only accepts public key...
... authentication server, as described in the known hosts file would appear similar to the following example for all the SSH client's granted management access to manually create a known hosts file on the switch (SSH Host Key Settings) and enable the SSH server (Authentication Settings). The current firmware only accepts public key...
User Guide
Page 120
... timeout, the number of client sessions includes both checks succeed, the client is allowed. One of the following exchanges take place during initial connection or manually entered into the known host file. c. However, you do not need to negotiate a session key and encryption method. Only clients that have a private key corresponding...
... timeout, the number of client sessions includes both checks succeed, the client is allowed. One of the following exchanges take place during initial connection or manually entered into the known host file. c. However, you do not need to negotiate a session key and encryption method. Only clients that have a private key corresponding...