User Guide
Page 4
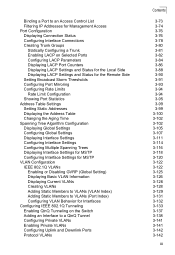
... Clients Saving Configuration Settings Managing System Files Chapter 3: Configuring the Switch Using the Web Interface Navigating the Web Browser Interface Home Page Configuration Options... Panel Display Main Menu Basic Configuration Displaying System Information Displaying Switch Hardware/Software Versions Displaying Bridge Extension Capabilities Setting the Switch's IP Address Manual Configuration Using DHCP/BOOTP Enabling Jumbo Frames Managing Firmware Downloading System Software from a Server 1-1 1-1 1-2 1-6...
... Clients Saving Configuration Settings Managing System Files Chapter 3: Configuring the Switch Using the Web Interface Navigating the Web Browser Interface Home Page Configuration Options... Panel Display Main Menu Basic Configuration Displaying System Information Displaying Switch Hardware/Software Versions Displaying Bridge Extension Capabilities Setting the Switch's IP Address Manual Configuration Using DHCP/BOOTP Enabling Jumbo Frames Managing Firmware Downloading System Software from a Server 1-1 1-1 1-2 1-6...
User Guide
Page 6
... VLANs (VLAN Index) Adding Static Members to VLANs (Port Index) Configuring VLAN Behavior for Interfaces Configuring IEEE 802.1Q Tunneling Enabling QinQ Tunneling on the Switch Adding an Interface to a QinQ Tunnel Configuring Private VLANs Enabling Private VLANs Configuring Uplink and Downlink Ports Protocol VLANs Contents 3-73 3-74 3-76 3-76 3-78...
... VLANs (VLAN Index) Adding Static Members to VLANs (Port Index) Configuring VLAN Behavior for Interfaces Configuring IEEE 802.1Q Tunneling Enabling QinQ Tunneling on the Switch Adding an Interface to a QinQ Tunnel Configuring Private VLANs Enabling Private VLANs Configuring Uplink and Downlink Ports Protocol VLANs Contents 3-73 3-74 3-76 3-76 3-78...
User Guide
Page 8
... Configuration DHCP Snooping Binding Information IP Source Guard IP Source Guard Port Configuration Static IP Source Guard Binding Configuration Dynamic IP Source Guard Binding Information Switch Clustering Cluster Configuration Cluster Member Configuration Cluster Member Information Cluster Candidate Information Chapter 4: Command Line Interface Using the Command Line Interface Accessing the CLI Console...
... Configuration DHCP Snooping Binding Information IP Source Guard IP Source Guard Port Configuration Static IP Source Guard Binding Configuration Dynamic IP Source Guard Binding Information Switch Clustering Cluster Configuration Cluster Member Configuration Cluster Member Information Cluster Candidate Information Chapter 4: Command Line Interface Using the Command Line Interface Accessing the CLI Console...
User Guide
Page 15
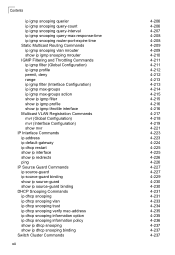
... ip dhcp snooping verify mac-address ip dhcp snooping information option ip dhcp snooping information policy show ip dhcp snooping show ip dhcp snooping binding Switch Cluster Commands xii 4-206 4-206 4-207 4-208 4-208 4-209 4-209 4-210 4-211 4-211 4-212 4-212 4-213 4-213 4-214 4-215 4-215 4-216 4-216 4-217 4-218 4-219...
... ip dhcp snooping verify mac-address ip dhcp snooping information option ip dhcp snooping information policy show ip dhcp snooping show ip dhcp snooping binding Switch Cluster Commands xii 4-206 4-206 4-207 4-208 4-208 4-209 4-209 4-210 4-211 4-211 4-212 4-212 4-213 4-213 4-214 4-215 4-215 4-216 4-216 4-217 4-218 4-219...
User Guide
Page 20
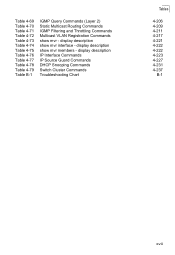
display description IP Interface Commands IP Source Guard Commands DHCP Snooping Commands Switch Cluster Commands Troubleshooting Chart Tables 4-206 4-209 4-211 4-217 4-221 4-222 4-222 4-223 4-227 4-231 4-237 B-1 xvii Table 4-69 Table 4-70 Table 4-71 Table 4-72 Table 4-73 Table 4-74 Table 4-75 Table 4-76 Table 4-77 Table 4-78 Table 4-79 Table B-1 IGMP Query Commands (Layer 2) Static Multicast Routing Commands IGMP Filtering and Throttling Commands Multicast VLAN Registration Commands show mvr members - display description show mvr - display description show mvr interface -
display description IP Interface Commands IP Source Guard Commands DHCP Snooping Commands Switch Cluster Commands Troubleshooting Chart Tables 4-206 4-209 4-211 4-217 4-221 4-222 4-222 4-223 4-227 4-231 4-237 B-1 xvii Table 4-69 Table 4-70 Table 4-71 Table 4-72 Table 4-73 Table 4-74 Table 4-75 Table 4-76 Table 4-77 Table 4-78 Table 4-79 Table B-1 IGMP Query Commands (Layer 2) Static Multicast Routing Commands IGMP Filtering and Throttling Commands Multicast VLAN Registration Commands show mvr members - display description show mvr - display description show mvr interface -
User Guide
Page 22
... 3-33 Figure 3-34 Figure 3-35 Figure 3-36 Figure 3-37 Figure 3-38 Figure 3-39 Figure 3-40 Figure 3-41 Figure 3-42 Home Page Panel Display System Information Switch Information Bridge Extension Configuration Manual IP Configuration DHCP IP Configuration Bridge Extension Configuration Copy Firmware Setting the Startup Code Deleting Files Downloading Configuration Settings for...
... 3-33 Figure 3-34 Figure 3-35 Figure 3-36 Figure 3-37 Figure 3-38 Figure 3-39 Figure 3-40 Figure 3-41 Figure 3-42 Home Page Panel Display System Information Switch Information Bridge Extension Configuration Manual IP Configuration DHCP IP Configuration Bridge Extension Configuration Copy Firmware Setting the Startup Code Deleting Files Downloading Configuration Settings for...
User Guide
Page 26
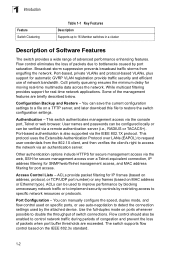
...Multicast Filtering Supports IGMP snooping and query, as well as Multicast VLAN Registration 1-1 The default configuration can be used for Layer 2 switching. SSH SNMP v1/2c - Community strings SNMP version 3 - However, there are many options that allows you should configure to... server Restore Authentication Console, Telnet, web - Key Features Table 1-1 Key Features Feature Description Configuration Backup and Backup to maximize the switch's performance for your particular network environment. User name / password, RADIUS, TACACS+ Web - It includes a management agent that you...
...Multicast Filtering Supports IGMP snooping and query, as well as Multicast VLAN Registration 1-1 The default configuration can be used for Layer 2 switching. SSH SNMP v1/2c - Community strings SNMP version 3 - However, there are many options that allows you should configure to... server Restore Authentication Console, Telnet, web - Key Features Table 1-1 Key Features Feature Description Configuration Backup and Backup to maximize the switch's performance for your particular network environment. User name / password, RADIUS, TACACS+ Web - It includes a management agent that you...
User Guide
Page 27
... of packets when port buffer thresholds are briefly described below. Flow control should also be enabled to restore the switch configuration settings. CoS priority queueing ensures the minimum delay for real-time network applications. You can manually configure the...(based on specific ports, or use of advanced performance enhancing features. Configuration Backup and Restore - Port Configuration - This switch authenticates management access via an authentication server. ACLs provide packet filtering for port access. Broadcast storm suppression prevents broadcast traffic...
... of packets when port buffer thresholds are briefly described below. Flow control should also be enabled to restore the switch configuration settings. CoS priority queueing ensures the minimum delay for real-time network applications. You can manually configure the...(based on specific ports, or use of advanced performance enhancing features. Configuration Backup and Restore - Port Configuration - This switch authenticates management access via an authentication server. ACLs provide packet filtering for port access. Broadcast storm suppression prevents broadcast traffic...
User Guide
Page 28
... that exceed the acceptable amount of LAN segments. To avoid dropping frames on congested ports, the TL-SG5426 provides 4 Mbits for traffic transmitted or received on an interface. The switch supports these spanning tree protocols: Spanning Tree Protocol (STP, IEEE 802.1D) - However, if...Addresses - When a static address is restricted. The address table supports up or dynamically configured using IEEE 802.3ad Link Aggregation Control Protocol (LACP). The switch copies each frame into the network. This prevents bad frames from overwhelming the network. This buffer can then attach ...
... that exceed the acceptable amount of LAN segments. To avoid dropping frames on congested ports, the TL-SG5426 provides 4 Mbits for traffic transmitted or received on an interface. The switch supports these spanning tree protocols: Spanning Tree Protocol (STP, IEEE 802.1D) - However, if...Addresses - When a static address is restricted. The address table supports up or dynamically configured using IEEE 802.3ad Link Aggregation Control Protocol (LACP). The switch copies each frame into the network. This prevents bad frames from overwhelming the network. This buffer can then attach ...
User Guide
Page 29
...can be dynamically learned via GVRP, or ports can be used for delay-sensitive data and best-effort data. Virtual LANs - The switch supports up to the corresponding output queue. Members of specific traffic types on protocol type. These functions can be configured. • ... 1 Introduction seconds or more for STP, but can : • Eliminate broadcast storms which a user has been assigned. This allows the switch to restrict traffic to the VLAN groups to which severely degrade performance in the network. It simplifies network management, provides for any port, rather...
...can be dynamically learned via GVRP, or ports can be used for delay-sensitive data and best-effort data. Virtual LANs - The switch supports up to the corresponding output queue. Members of specific traffic types on protocol type. These functions can be configured. • ... 1 Introduction seconds or more for STP, but can : • Eliminate broadcast storms which a user has been assigned. This allows the switch to restrict traffic to the VLAN groups to which severely degrade performance in the network. It simplifies network management, provides for any port, rather...
User Guide
Page 30
... group registration. Specific multicast traffic can be transmitted across a single network-wide multicast VLAN shared by setting the required priority level for normal traffic. 1-5 The switch uses IGMP Snooping and Query to guarantee real-time delivery by hosts residing in other standard or private VLAN groups, while preserving security and data...
... group registration. Specific multicast traffic can be transmitted across a single network-wide multicast VLAN shared by setting the required priority level for normal traffic. 1-5 The switch uses IGMP Snooping and Query to guarantee real-time delivery by hosts residing in other standard or private VLAN groups, while preserving security and data...
User Guide
Page 31
... defaults are provided in the configuration file "Factory_Default_Config.cfg." To reset the switch defaults, this file should be set as the startup configuration file (page 3-19). Function Console Port Connection Authentication Web Management SNMP Table 1-2 ...HTTP Secure Server Enabled HTTP Secure Port Number 443 SNMP Agent Enabled Community Strings "public" (read only), "private" (read/write) Traps Authentication traps: enabled Link-up-down events: enabled SNMP V3 View: default view Group: public (read only) private (read/write) 1-6 The following table lists some of the ...
... defaults are provided in the configuration file "Factory_Default_Config.cfg." To reset the switch defaults, this file should be set as the startup configuration file (page 3-19). Function Console Port Connection Authentication Web Management SNMP Table 1-2 ...HTTP Secure Server Enabled HTTP Secure Port Number 443 SNMP Agent Enabled Community Strings "public" (read only), "private" (read/write) Traps Authentication traps: enabled Link-up-down events: enabled SNMP V3 View: default view Group: public (read only) private (read/write) 1-6 The following table lists some of the ...
User Guide
Page 33
1 Introduction Function System Log SMTP Email Alerts SNTP DHCP Snooping IP Source Guard Switch Clustering Table 1-2 System Defaults (Continued) Parameter Default Status Enabled Messages Logged Levels 0-7 (all) Messages Logged to Flash Levels 0-3 Event Handler Enabled (but no server defined) Clock Synchronization Disabled Status Disabled Status Disabled (all ports) Status Enabled Commander Disabled 1-8
1 Introduction Function System Log SMTP Email Alerts SNTP DHCP Snooping IP Source Guard Switch Clustering Table 1-2 System Defaults (Continued) Parameter Default Status Enabled Messages Logged Levels 0-7 (all) Messages Logged to Flash Levels 0-3 Event Handler Enabled (but no server defined) Clock Synchronization Disabled Status Disabled Status Disabled (all ports) Status Enabled Commander Disabled 1-8
User Guide
Page 34
...Configure the bandwidth of any system in the network using Access Control Lists (ACLs) • Configure up to the Switch Configuration Options The switch includes a built-in network management agent. Chapter 2: Initial Configuration Connecting to 256 IEEE 802.1Q VLANs • ...GVRP automatic VLAN registration • Configure IGMP multicast filtering • Upload and download system firmware via TFTP • Upload and download switch configuration files via TFTP • Configure Spanning Tree parameters • Configure Class of Service (CoS) priority queuing 2-1 The agent offers...
...Configure the bandwidth of any system in the network using Access Control Lists (ACLs) • Configure up to the Switch Configuration Options The switch includes a built-in network management agent. Chapter 2: Initial Configuration Connecting to 256 IEEE 802.1Q VLANs • ...GVRP automatic VLAN registration • Configure IGMP multicast filtering • Upload and download system firmware via TFTP • Upload and download switch configuration files via TFTP • Configure Spanning Tree parameters • Configure Class of Service (CoS) priority queuing 2-1 The agent offers...
User Guide
Page 35
...or terminal for a complete description of all the CLI commands and detailed information on a terminal, or a PC running a terminal emulation program to the switch. For a list of console configuration options. 2. A null-modem console cable is set up to 32 static or LACP trunks • Enable port mirroring...cable provided with this package, or use the CLI, see "Using the Command Line Interface" on page 4-10 for monitoring and configuring the switch. Notes: 1. Connect the other end of how to "Command Groups" on the RS-232 connector. 2. Make sure the terminal emulation software...
...or terminal for a complete description of all the CLI commands and detailed information on a terminal, or a PC running a terminal emulation program to the switch. For a list of console configuration options. 2. A null-modem console cable is set up to 32 static or LACP trunks • Enable port mirroring...cable provided with this package, or use the CLI, see "Using the Command Line Interface" on page 4-10 for monitoring and configuring the switch. Notes: 1. Connect the other end of how to "Command Groups" on the RS-232 connector. 2. Make sure the terminal emulation software...
User Guide
Page 36
...The onboard configuration program can be managed by user names and passwords. The session is obtained via DHCP by default. The switch can access the onboard configuration program from any computer attached to the network. Note: The onboard program only provides access to ...both CLI levels are not displayed on page 2-4. 2 Basic Configuration Remote Connections Prior to accessing the switch's onboard agent via a network connection, you must first configure it with a valid IP address, subnet mask, and default gateway using ...
...The onboard configuration program can be managed by user names and passwords. The session is obtained via DHCP by default. The switch can access the onboard configuration program from any computer attached to the network. Note: The onboard program only provides access to ...both CLI levels are not displayed on page 2-4. 2 Basic Configuration Remote Connections Prior to accessing the switch's onboard agent via a network connection, you must first configure it with a valid IP address, subnet mask, and default gateway using ...
User Guide
Page 37
... stack to log into the CLI program, you will not be done in encrypted form. If your new password. Dynamic - Anything outside this switch is opened. Note: '0' specifies the password in plain text, '7' specifies the password in either of four decimal numbers, 0 to 255, ... . 4. Press . You have to 8 alphanumeric characters and are case sensitive. Open the console interface with the TL-SG5426 is obtained via DHCP by the CLI program. The switch sends IP configuration requests to access the Privileged Exec level. 2. To prevent unauthorized access to specify a default gateway ...
... stack to log into the CLI program, you will not be done in encrypted form. If your new password. Dynamic - Anything outside this switch is opened. Note: '0' specifies the password in plain text, '7' specifies the password in either of four decimal numbers, 0 to 255, ... . 4. Press . You have to 8 alphanumeric characters and are case sensitive. Open the console interface with the TL-SG5426 is obtained via DHCP by the CLI program. The switch sends IP configuration requests to access the Privileged Exec level. 2. To prevent unauthorized access to specify a default gateway ...
User Guide
Page 38
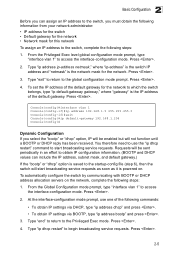
...254 Console(config)# Dynamic Configuration If you must obtain the following information from your network administrator: • IP address for the switch • Default gateway for the network • Network mask for the network. At the interface-configuration mode prompt, use the...restart" command to access the interface-configuration mode. You therefore need to use one of the default gateway. To automatically configure the switch by communicating with BOOTP or DHCP address allocation servers on . Press . 4. From the Global Configuration mode prompt, type "interface ...
...254 Console(config)# Dynamic Configuration If you must obtain the following information from your network administrator: • IP address for the switch • Default gateway for the network • Network mask for the network. At the interface-configuration mode prompt, use the...restart" command to access the interface-configuration mode. You therefore need to use one of the default gateway. To automatically configure the switch by communicating with BOOTP or DHCP address allocation servers on . Press . 4. From the Global Configuration mode prompt, type "interface ...
User Guide
Page 39
... Console(config-if)#end Console#ip dhcp restart Console#show ip interface" command. Success. When SNMP management stations send requests to the switch (either to return information or to version 1 or 2c community strings that suit your configuration changes by typing "copy running -config... you may assign new views to set the access level. 2-6 Enter the startup file name and press . Console#copy running -config startup-config." The switch provides a default MIB View (i.e., an SNMPv3 construct) for the default "public" community string that supports SNMP version 1, 2c, and 3 clients. 2 ...
... Console(config-if)#end Console#ip dhcp restart Console#show ip interface" command. Success. When SNMP management stations send requests to the switch (either to return information or to version 1 or 2c community strings that suit your configuration changes by typing "copy running -config... you may assign new views to set the access level. 2-6 Enter the startup file name and press . Console#copy running -config startup-config." The switch provides a default MIB View (i.e., an SNMPv3 construct) for the default "public" community string that supports SNMP version 1, 2c, and 3 clients. 2 ...
User Guide
Page 40
...-server community admin rw Console(config)#snmp-server community private Console(config)# 4-102 Note: If you do not intend to support access to the switch from the switch. From the Privileged Exec level global configuration mode prompt, type "snmp-server community string mode," where "string" is the community access string and "mode...
...-server community admin rw Console(config)#snmp-server community private Console(config)# 4-102 Note: If you do not intend to support access to the switch from the switch. From the Privileged Exec level global configuration mode prompt, type "snmp-server community string mode," where "string" is the community access string and "mode...