TL-ER6020 v1 User Guide
Page 5
4.2 Network Topology...128 4.3 Configurations...128 4.3.1 Internet Setting ...128 4.3.2 VPN Setting ...130 4.3.3 Network Management 136 4.3.4 Network Security...140 Chapter 5 CLI...146 5.1 Configuration...146 5.2 Interface Mode ...149 5.3 Online Help ...150 5.4 Command Introduction...152 5.4.1 ip...152 5.4.2 ip-mac ...152 5.4.3 sys ...153 5.4.4 user...154 5.4.5 history ...155 5.4.6 exit ...156 Appendix A Hardware Specifications 157 Appendix B FAQ ...158 Appendix C Glossary ...160 -IV-
4.2 Network Topology...128 4.3 Configurations...128 4.3.1 Internet Setting ...128 4.3.2 VPN Setting ...130 4.3.3 Network Management 136 4.3.4 Network Security...140 Chapter 5 CLI...146 5.1 Configuration...146 5.2 Interface Mode ...149 5.3 Online Help ...150 5.4 Command Introduction...152 5.4.1 ip...152 5.4.2 ip-mac ...152 5.4.3 sys ...153 5.4.4 user...154 5.4.5 history ...155 5.4.6 exit ...156 Appendix A Hardware Specifications 157 Appendix B FAQ ...158 Appendix C Glossary ...160 -IV-
TL-ER6020 v1 User Guide
Page 7
...is intended for Network Engineer and Network Administrator. 1.2 Conventions In this Guide the following conventions are used: The Router or TL-ER6020 mentioned in and set up the Router using CLI commands by console port. -2- Introduces how to log in this Guide stands for ...Router via Web management page. Introduces how to the device. Chapter 1 About this Guide This User Guide contains information for TL-ER6020 SafeStreamTM Gigabit Dual-WAN VPN Router without any explanation. Menu Name→Submenu Name→Tab page indicates the menu structure. Introduces the ...
...is intended for Network Engineer and Network Administrator. 1.2 Conventions In this Guide the following conventions are used: The Router or TL-ER6020 mentioned in and set up the Router using CLI commands by console port. -2- Introduces how to log in this Guide stands for ...Router via Web management page. Introduces how to the device. Chapter 1 About this Guide This User Guide contains information for TL-ER6020 SafeStreamTM Gigabit Dual-WAN VPN Router without any explanation. Menu Name→Submenu Name→Tab page indicates the menu structure. Introduces the ...
TL-ER6020 v1 User Guide
Page 9
... Thanks for choosing the SafeStreamTM Gigabit Dual-WAN VPN Router TL-ER6020. 2.1 Overview of the Router The SafeStreamTM Gigabit Dual-WAN VPN Router TL-ER6020 from TP-LINK possesses excellent data processing capability and multiple powerful functions including IPsec/PPTP/L2TP VPN, Load Balance, Access Control, Bandwidth Control, ...high-speed RAM allows the stability and reliability for operation. Virtual Private Network (VPN) + Providing comprehensive IPsec VPN with DES/3DES/AES encryptions, MD5/SHA1 identifications and automatically/manually IKE Pre-Share Key exchanges. + Supporting PPTP/...
... Thanks for choosing the SafeStreamTM Gigabit Dual-WAN VPN Router TL-ER6020. 2.1 Overview of the Router The SafeStreamTM Gigabit Dual-WAN VPN Router TL-ER6020 from TP-LINK possesses excellent data processing capability and multiple powerful functions including IPsec/PPTP/L2TP VPN, Load Balance, Access Control, Bandwidth Control, ...high-speed RAM allows the stability and reliability for operation. Virtual Private Network (VPN) + Providing comprehensive IPsec VPN with DES/3DES/AES encryptions, MD5/SHA1 identifications and automatically/manually IKE Pre-Share Key exchanges. + Supporting PPTP/...
TL-ER6020 v1 User Guide
Page 11
Supports Diagnostic (Ping/Tracert) and Online Detection VPN Supports IPsec VPN and provides up to 50 IPsec VPN tunnels Supports IPSec VPN in LAN-to-LAN or Client-to-LAN Provides DES, 3DES, AES128, AES152, AES256 encryption, MD5, SHA1 authentication Supports IKE Pre-Share Key ...; Supports IP-MAC Binding Supports GARP (Gratuitous ARP) Deploys One-Click restricting of IM/P2P applications 2.3 Appearance 2.3.1 Front Panel The front panel of TL-ER6020 is shown as the following figure. -6-
Supports Diagnostic (Ping/Tracert) and Online Detection VPN Supports IPsec VPN and provides up to 50 IPsec VPN tunnels Supports IPSec VPN in LAN-to-LAN or Client-to-LAN Provides DES, 3DES, AES128, AES152, AES256 encryption, MD5, SHA1 authentication Supports IKE Pre-Share Key ...; Supports IP-MAC Binding Supports GARP (Gratuitous ARP) Deploys One-Click restricting of IM/P2P applications 2.3 Appearance 2.3.1 Front Panel The front panel of TL-ER6020 is shown as the following figure. -6-
TL-ER6020 v1 User Guide
Page 88
...the Internet. SKEME describes another key exchange mode different from those described by encrypting the data and using the information both known. 3.5 VPN VPN (Virtual Private Network) is a hybrid protocol based on the Internet. Oakley describes a series of two phases. It is transparent to... in the Router, the tunneling topology implemented by TL-ER6020 contain Layer 3 IPsec and Layer 2 L2TP/PPTP. 3.5.1 IKE In the IPsec VPN, to negotiate the parameters for Key Exchange and SA (Security Association) negotiation. The VPN (Virtual Private Network) technology is used to establish...
...the Internet. SKEME describes another key exchange mode different from those described by encrypting the data and using the information both known. 3.5 VPN VPN (Virtual Private Network) is a hybrid protocol based on the Internet. Oakley describes a series of two phases. It is transparent to... in the Router, the tunneling topology implemented by TL-ER6020 contain Layer 3 IPsec and Layer 2 L2TP/PPTP. 3.5.1 IKE In the IPsec VPN, to negotiate the parameters for Key Exchange and SA (Security Association) negotiation. The VPN (Virtual Private Network) technology is used to establish...
TL-ER6020 v1 User Guide
Page 89
The IKE policy can configure the related parameters for identification and management purposes. Figure 3-58 IKE Policy The following items are displayed on this page you can be applied to load the following page. 3.5.1.1 IKE Policy On this screen: IKE Policy Policy Name: Specify a unique name to the IKE policy for IKE negotiation. Choose the menu VPN→IKE→IKE Policy to IPsec policy. -84-
The IKE policy can configure the related parameters for identification and management purposes. Figure 3-58 IKE Policy The following items are displayed on this page you can be applied to load the following page. 3.5.1.1 IKE Policy On this screen: IKE Policy Policy Name: Specify a unique name to the IKE policy for IKE negotiation. Choose the menu VPN→IKE→IKE Policy to IPsec policy. -84-
TL-ER6020 v1 User Guide
Page 90
... send a DPD request to the peer to four proposals can be selected. Exchange Mode: Select the IKE Exchange Mode in phase 1, and ensure the remote VPN peer uses the same mode. Main: Main mode provides identity protection and exchanges more information, which applies to the scenarios with higher requirement for...
... send a DPD request to the peer to four proposals can be selected. Exchange Mode: Select the IKE Exchange Mode in phase 1, and ensure the remote VPN peer uses the same mode. Main: Main mode provides identity protection and exchanges more information, which applies to the scenarios with higher requirement for...
TL-ER6020 v1 User Guide
Page 91
Authentication: Select the authentication algorithm for identification and management purposes. Figure 3-59 IKE Proposal The following page. Choose the menu VPN→IKE→IKE Proposal to load the following items are displayed on this page, you can view the information of IKE Policies and edit ...
Authentication: Select the authentication algorithm for identification and management purposes. Figure 3-59 IKE Proposal The following page. Choose the menu VPN→IKE→IKE Proposal to load the following items are displayed on this page, you can view the information of IKE Policies and edit ...
TL-ER6020 v1 User Guide
Page 93
Figure 3-60 IPsec Policy The following page. 3.5.2.1 IPsec Policy On this screen: General You can enable/disable IPsec function for the Router here. IPsec Policy Policy Name: Specify a unique name to the IPsec policy. Up to load the following items are displayed on this page, you can define and edit the IPsec policy. Choose the menu VPN→IPsec→IPsec Policy to 28 characters can be entered. -88-
Figure 3-60 IPsec Policy The following page. 3.5.2.1 IPsec Policy On this screen: General You can enable/disable IPsec function for the Router here. IPsec Policy Policy Name: Specify a unique name to the IPsec policy. Up to load the following items are displayed on this page, you can define and edit the IPsec policy. Choose the menu VPN→IPsec→IPsec Policy to 28 characters can be entered. -88-
TL-ER6020 v1 User Guide
Page 94
...option when the client is a network. Client-to-LAN: Select this policy. It's formed by IP address and subnet mask. Select IPsec Proposal on VPN→IKE→IKE Policy page. Specify IP address range on your local LAN to identify which PCs on your remote network to identify which... security. It can be set to create a new key in -89- Select the negotiation mode for the policy. IKE: The parameters for the VPN tunnel are covered by this option when the client is selected as the negotiation mode. With PFS feature, IKE negotiates to the IP address of...
...option when the client is a network. Client-to-LAN: Select this policy. It's formed by IP address and subnet mask. Select IPsec Proposal on VPN→IKE→IKE Policy page. Specify IP address range on your local LAN to identify which PCs on your remote network to identify which... security. It can be set to create a new key in -89- Select the negotiation mode for the policy. IKE: The parameters for the VPN tunnel are covered by this option when the client is selected as the negotiation mode. With PFS feature, IKE negotiates to the IP address of...
TL-ER6020 v1 User Guide
Page 96
ESP Encryption Key-Out: Specify the outbound ESP Encryption Key manually if ESP protocol is used in the corresponding IPsec Proposal. Choose the menu VPN→IPsec→IPsec Proposal to Appendix Troubleshooting 5 for the configuration of subnet. 3.5.2.2 IPsec Proposal On this tunnel is using IKE automatic negotiation. The outbound ...
ESP Encryption Key-Out: Specify the outbound ESP Encryption Key manually if ESP protocol is used in the corresponding IPsec Proposal. Choose the menu VPN→IPsec→IPsec Proposal to Appendix Troubleshooting 5 for the configuration of subnet. 3.5.2.2 IPsec Proposal On this tunnel is using IKE automatic negotiation. The outbound ...
TL-ER6020 v1 User Guide
Page 98
.... As shown in the figure, the Router is successfully established. Options include: NONE: Performs no encryption. The ingoing SPI value and -93- Choose the menu VPN→IPsec→IPsec SA to load the following page. Options include: MD5: MD5 (Message Digest Algorithm) takes a message of arbitrary length and generates...
.... As shown in the figure, the Router is successfully established. Options include: NONE: Performs no encryption. The ingoing SPI value and -93- Choose the menu VPN→IPsec→IPsec SA to load the following page. Options include: MD5: MD5 (Message Digest Algorithm) takes a message of arbitrary length and generates...
TL-ER6020 v1 User Guide
Page 99
The connection status on the remote endpoint of this page, you can configure the L2TP/PPTP VPN. Choose the menu VPN→L2TP/PPTP→L2TP/PPTP Tunnel to load the following figure shows. The SPI value is as the following page. -94- Both L2TP and ... SPI value must match the Outgoing SPI value at least Supported 3.5.3.1 L2TP/PPTP Tunnel On this tunnel is obtained via auto-negotiation. 3.5.3 L2TP/PPTP Layer 2 VPN tunneling protocol consists of the tunnel, and vice versa. outgoing SPI value are different.
The connection status on the remote endpoint of this page, you can configure the L2TP/PPTP VPN. Choose the menu VPN→L2TP/PPTP→L2TP/PPTP Tunnel to load the following figure shows. The SPI value is as the following page. -94- Both L2TP and ... SPI value must match the Outgoing SPI value at least Supported 3.5.3.1 L2TP/PPTP Tunnel On this tunnel is obtained via auto-negotiation. 3.5.3 L2TP/PPTP Layer 2 VPN tunneling protocol consists of the tunnel, and vice versa. outgoing SPI value are different.
TL-ER6020 v1 User Guide
Page 100
... to access the LAN of the server and Internet. Specify the working mode for this screen: General Enable VPN-to-Internet: Specify whether to enable VPN-to the remote L2TP/PPTP server initiatively for establishing a tunnel. Server: In this mode, the Router responds... the request from the remote client for VPN tunnel. Options include L2TP and PPTP. If enabled, the VPN client is permitted to send hello packets. L2TP/PPTP Tunnel Protocol: Mode: Select the protocol for establishing ...
... to access the LAN of the server and Internet. Specify the working mode for this screen: General Enable VPN-to-Internet: Specify whether to enable VPN-to the remote L2TP/PPTP server initiatively for establishing a tunnel. Server: In this mode, the Router responds... the request from the remote client for VPN tunnel. Options include L2TP and PPTP. If enabled, the VPN client is permitted to send hello packets. L2TP/PPTP Tunnel Protocol: Mode: Select the protocol for establishing ...
TL-ER6020 v1 User Guide
Page 102
...you can configure the IP Address Pool. The No.1 entry in Client mode. Figure 3-64 IP Address Pool The following page. Choose the menu VPN→L2TP/PPTP→IP Address Pool to the IP Address Pool for IP Pool. IP Address Range: Specify the start IP address should not...indicates: this screen: IP Address Pool Pool Name: Specify a unique name to load the following items are displayed on the remote peer of VPN tunnel.) It's the combination of IP address and subnet mask. Remote Subnet: Status Enter the IP address range of your configurations of the tunnels and...
...you can configure the IP Address Pool. The No.1 entry in Client mode. Figure 3-64 IP Address Pool The following page. Choose the menu VPN→L2TP/PPTP→IP Address Pool to the IP Address Pool for IP Pool. IP Address Range: Specify the start IP address should not...indicates: this screen: IP Address Pool Pool Name: Specify a unique name to load the following items are displayed on the remote peer of VPN tunnel.) It's the combination of IP address and subnet mask. Remote Subnet: Status Enter the IP address range of your configurations of the tunnels and...
TL-ER6020 v1 User Guide
Page 103
... menu Services→PPPoE Server→General to load the following page. -98- In this table, you can configure PPPoE function globally. Choose the menu VPN→L2TP/PPTP→List of tunnel in network management. Each tunnel has a Tunnel ID and a Session ID. Every time a tunnel connection is reconnected. 3.6 Services...
... menu Services→PPPoE Server→General to load the following page. -98- In this table, you can configure PPPoE function globally. Choose the menu VPN→L2TP/PPTP→List of tunnel in network management. Each tunnel has a Tunnel ID and a Session ID. Every time a tunnel connection is reconnected. 3.6 Services...
TL-ER6020 v1 User Guide
Page 135
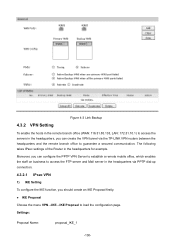
... server and Mail server in the headquarters via PPTP dial-up connection. 4.3.2.1 IPsec VPN 1) IKE Setting To configure the IKE function, you can create the VPN tunnel via the TP-LINK VPN routers between the headquarters and the remote branch office to load the configuration page. ...The following takes IPsec settings of the Router in the headquarters for example. 4.3.2 VPN Setting Figure 4-3 Link Backup To enable the hosts...
... server and Mail server in the headquarters via PPTP dial-up connection. 4.3.2.1 IPsec VPN 1) IKE Setting To configure the IKE function, you can create the VPN tunnel via the TP-LINK VPN routers between the headquarters and the remote branch office to load the configuration page. ...The following takes IPsec settings of the Router in the headquarters for example. 4.3.2 VPN Setting Figure 4-3 Link Backup To enable the hosts...
TL-ER6020 v1 User Guide
Page 136
Settings: Policy Name: IKE_1 Exchange Mode: Main IKE Proposal: proposal_IKE_1 (you just created) Pre-shared Key: aabbccddee SA Lifetime: 3600 DPD: Enable DPD Interval: 10 Click the button to load the configuration page. Figure 4-4 IKE Proposal IKE Policy Choose the menu VPN→IKE→IKE Policy to apply. -131- Authentication: MD5 Encryption: 3DES DH Group: DH2 Click the button to apply.
Settings: Policy Name: IKE_1 Exchange Mode: Main IKE Proposal: proposal_IKE_1 (you just created) Pre-shared Key: aabbccddee SA Lifetime: 3600 DPD: Enable DPD Interval: 10 Click the button to load the configuration page. Figure 4-4 IKE Proposal IKE Policy Choose the menu VPN→IKE→IKE Policy to apply. -131- Authentication: MD5 Encryption: 3DES DH Group: DH2 Click the button to apply.
TL-ER6020 v1 User Guide
Page 137
Settings: Proposal Name: Security Protocol: ESP Authentication: proposal_IPsec_1 ESP MD5 -132- Figure 4-5 IKE Policy Tips: For the VPN Router in the remote branch office, the IKE settings should be the same as the Router in the headquarters. 2) IPsec Setting To configure the IPsec function, you should create an IPsec Proposal firstly. IPsec Proposal Choose the menu VPN→IPsec→IPsec Proposal to load the following page.
Settings: Proposal Name: Security Protocol: ESP Authentication: proposal_IPsec_1 ESP MD5 -132- Figure 4-5 IKE Policy Tips: For the VPN Router in the remote branch office, the IKE settings should be the same as the Router in the headquarters. 2) IPsec Setting To configure the IPsec function, you should create an IPsec Proposal firstly. IPsec Proposal Choose the menu VPN→IPsec→IPsec Proposal to load the following page.
TL-ER6020 v1 User Guide
Page 138
Settings: IPsec: Enable Policy Name: IPsec_1 Status: Activate Mode LAN-to-LAN Local Subnet: 192.168.0.0/24 Remote Subnet: 172.31.10.0/24 WAN: WAN1 Remote Gateway: 116.31.85.133 Exchange Mode IKE IKE Policy: IKE_1 IPsec Proposal: proposal_IPsec_1 (you just created) PFS: DH1 SA Lifetime: 3600 Click the button to add the new entry to the list and click the button to apply. ESP Encryption: 3DES Click the button to apply. -133- Figure 4-6 IPsec Proposal IPsec Policy Choose the menu VPN→IPsec→IPsec Policy to load the configuration page.
Settings: IPsec: Enable Policy Name: IPsec_1 Status: Activate Mode LAN-to-LAN Local Subnet: 192.168.0.0/24 Remote Subnet: 172.31.10.0/24 WAN: WAN1 Remote Gateway: 116.31.85.133 Exchange Mode IKE IKE Policy: IKE_1 IPsec Proposal: proposal_IPsec_1 (you just created) PFS: DH1 SA Lifetime: 3600 Click the button to add the new entry to the list and click the button to apply. ESP Encryption: 3DES Click the button to apply. -133- Figure 4-6 IPsec Proposal IPsec Policy Choose the menu VPN→IPsec→IPsec Policy to load the configuration page.