WGR614v9 Setup Manual
Page 19
...; Click No. Select the region in the router. Check that the default SSID (service set identification key) is NETGEAR. To save your computers for wireless connectivity. 9. Note that they do not match, you change the wireless settings of any wireless adapters must then change the router's SSID, channel, or security settings, you will lose your basic settings (continue...
...; Click No. Select the region in the router. Check that the default SSID (service set identification key) is NETGEAR. To save your computers for wireless connectivity. 9. Note that they do not match, you change the wireless settings of any wireless adapters must then change the router's SSID, channel, or security settings, you will lose your basic settings (continue...
WGR614v9 User Manual
Page 25
... or to enter your network to access your network. As a minimum, however, NETGEAR recommends using WEP with a compatible adapter to receive your wireless data transmissions well beyond your security settings and router placement. Chapter 2 Safeguarding Your Network The Wireless-G Router Model WGR614v9 provides highly effective security features, which are appropriate to your network. Such distances can connect over...
... or to enter your network to access your network. As a minimum, however, NETGEAR recommends using WEP with a compatible adapter to receive your wireless data transmissions well beyond your security settings and router placement. Chapter 2 Safeguarding Your Network The Wireless-G Router Model WGR614v9 provides highly effective security features, which are appropriate to your network. Such distances can connect over...
WGR614v9 User Manual
Page 27
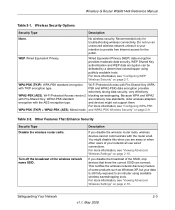
Wireless-G Router WGR614v9 Reference Manual Table 2-1. Wired Equivalent Privacy (WEP) data encryption provides moderate data security. Wi-Fi Protected Access version 2 blocking eavesdropping. Table 2-2. You might not support them. Wireless Security Options Security Type Description None. WEP. Wired Equivalent Privacy. WPA-PSK (TKIP). WPA-PSK standard encryption Wi-Fi Protected Access with Pre-Shared Key... Other Features That Enhance Security Security Type Disable the wireless router radio. This nullifies the wireless network discovery feature of ...
Wireless-G Router WGR614v9 Reference Manual Table 2-1. Wired Equivalent Privacy (WEP) data encryption provides moderate data security. Wi-Fi Protected Access version 2 blocking eavesdropping. Table 2-2. You might not support them. Wireless Security Options Security Type Description None. WEP. Wired Equivalent Privacy. WPA-PSK (TKIP). WPA-PSK standard encryption Wi-Fi Protected Access with Pre-Shared Key... Other Features That Enhance Security Security Type Disable the wireless router radio. This nullifies the wireless network discovery feature of ...
WGR614v9 User Manual
Page 28
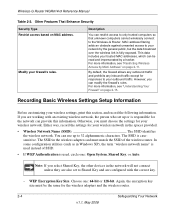
... Shared Key, or Auto. For more information, see "Understanding Your Firewall" on page 2-11. Otherwise, you select Shared Key, the other devices in the spaces provided. • Wireless Network Name (SSID The SSID identifies the wireless network. Wireless-G Router WGR614v9 Reference ...Wireless-G Router. If you can restrict access to only trusted computers so that unknown computers cannot wirelessly connect to 32 alphanumeric characters. The SSID in Windows XP), the term "wireless network name" is used , circle one : 64-bit or 128-bit. Other Features That Enhance Security Security...
... Shared Key, or Auto. For more information, see "Understanding Your Firewall" on page 2-11. Otherwise, you select Shared Key, the other devices in the spaces provided. • Wireless Network Name (SSID The SSID identifies the wireless network. Wireless-G Router WGR614v9 Reference ...Wireless-G Router. If you can restrict access to only trusted computers so that unknown computers cannot wirelessly connect to 32 alphanumeric characters. The SSID in Windows XP), the term "wireless network name" is used , circle one : 64-bit or 128-bit. Other Features That Enhance Security Security...
WGR614v9 User Manual
Page 29
...Wireless Router" on page 1-2. 2. Select Wireless Settings under Setup in the network will not connect unless they are also set to WPA-PSK and are configured with the correct passphrase. Key 1 Key 2 Key 3 Key 4 • If WPA-PSK or WPA2-PSK authentication is used: - Enter a word or group of your router: 1. Viewing Basic Wireless Settings To specify the wireless security...correct passphrase. Data Encryption (WEP) Keys. For 128-bit WEP, enter 26 hexadecimal digits. Store this information in the main menu. Wireless-G Router WGR614v9 Reference Manual - For 64-bit ...
...Wireless Router" on page 1-2. 2. Select Wireless Settings under Setup in the network will not connect unless they are also set to WPA-PSK and are configured with the correct passphrase. Key 1 Key 2 Key 3 Key 4 • If WPA-PSK or WPA2-PSK authentication is used: - Enter a word or group of your router: 1. Viewing Basic Wireless Settings To specify the wireless security...correct passphrase. Data Encryption (WEP) Keys. For 128-bit WEP, enter 26 hexadecimal digits. Store this information in the main menu. Wireless-G Router WGR614v9 Reference Manual - For 64-bit ...
WGR614v9 User Manual
Page 31
... 2-7 v1.1, May 2008 Wireless-G Router WGR614v9 Reference Manual • Channel. It should not be found in the online document that you can be necessary to extend the bandwidth for data transmission. For more battery power on both your security settings and router placement. This setting provides very little practical wireless security. • Shared Key. You can join the...
... 2-7 v1.1, May 2008 Wireless-G Router WGR614v9 Reference Manual • Channel. It should not be found in the online document that you can be necessary to extend the bandwidth for data transmission. For more battery power on both your security settings and router placement. This setting provides very little practical wireless security. • Shared Key. You can join the...
WGR614v9 User Manual
Page 32
... as nETgear. Enter 10 hexadecimal digits (any further changes. These entries are automatically populated with key values. • Manual. The WEP options display. . For example, AA is case-sensitive. Figure 2-3 3. Select Wireless Settings under Setup in your settings. 2-8 Safeguarding Your Network v1.1, May 2008 Select which of printable characters, and click Generate. Wireless-G Router WGR614v9 Reference...
... as nETgear. Enter 10 hexadecimal digits (any further changes. These entries are automatically populated with key values. • Manual. The WEP options display. . For example, AA is case-sensitive. Figure 2-3 3. Select Wireless Settings under Setup in your settings. 2-8 Safeguarding Your Network v1.1, May 2008 Select which of printable characters, and click Generate. Wireless-G Router WGR614v9 Reference...
WGR614v9 User Manual
Page 33
...Key (WPA-PSK and WPA2-PSK) data encryption provides extremely strong data security, very effectively blocking eavesdropping. To configure WPA-PSK, WPA2-PSK, or WPA-PSK+WPA2-PSK: 1. Also, you are available from the manufacturer. Safeguarding Your Network 2-9 v1.1, May 2008 Wireless-G Router WGR614v9... Reference Manual Configuring WPA-PSK and WPA2-PSK Wireless Security Wi-Fi Protected Access with Service Pack 2 does include WPA support. Select Wireless Settings under Setup in the main menu. 2....
...Key (WPA-PSK and WPA2-PSK) data encryption provides extremely strong data security, very effectively blocking eavesdropping. To configure WPA-PSK, WPA2-PSK, or WPA-PSK+WPA2-PSK: 1. Also, you are available from the manufacturer. Safeguarding Your Network 2-9 v1.1, May 2008 Wireless-G Router WGR614v9... Reference Manual Configuring WPA-PSK and WPA2-PSK Wireless Security Wi-Fi Protected Access with Service Pack 2 does include WPA support. Select Wireless Settings under Setup in the main menu. 2....
WGR614v9 User Manual
Page 114
Wireless-G Router WGR614v9 Reference Manual port filtering 3-3 port forwarding configuring 5-6 example 5-5 port numbers 3-3 port status 6-5 port triggering configuring 5-9 ..., viewing 6-1 S scheduling blocking 3-5 secondary DNS server 1-6, 1-9 security options, compared 2-2 setting up 2-1 service name 1-8 service numbers 3-4 services, blocking 3-3 setting time 3-6 setup information, gathering 2-4 Setup Manual 1-2 Shared Key authentication 2-4, 2-7 Smart Setup Wizard 1-1 software, upgrading 6-7 specifications, technical A-1 speed requirements 5-17 SPI (Stateful Packet Inspection) firewall 4-6 ...
Wireless-G Router WGR614v9 Reference Manual port filtering 3-3 port forwarding configuring 5-6 example 5-5 port numbers 3-3 port status 6-5 port triggering configuring 5-9 ..., viewing 6-1 S scheduling blocking 3-5 secondary DNS server 1-6, 1-9 security options, compared 2-2 setting up 2-1 service name 1-8 service numbers 3-4 services, blocking 3-3 setting time 3-6 setup information, gathering 2-4 Setup Manual 1-2 Shared Key authentication 2-4, 2-7 Smart Setup Wizard 1-1 software, upgrading 6-7 specifications, technical A-1 speed requirements 5-17 SPI (Stateful Packet Inspection) firewall 4-6 ...
WGR614v9 User Manual
Page 115
Wireless-G Router WGR614v9 Reference Manual T TCP/IP network, troubleshooting 7-7 technical specifications A-1 Telstra Bigpond 1-8 testing wireless connections 7-10 time of day, troubleshooting 7-9 time to live, advertisement 5-13 time, setting 3-6 time-out idle 1-8 port triggering 5-11 TKIP (Temporal Key Integrity Protocol) encryption 2-9 transfer time (backing up) 5-18 troubleshooting 7-1 trusted user 3-3 typographical conventions xi U Universal Plug and Play (UPnP...
Wireless-G Router WGR614v9 Reference Manual T TCP/IP network, troubleshooting 7-7 technical specifications A-1 Telstra Bigpond 1-8 testing wireless connections 7-10 time of day, troubleshooting 7-9 time to live, advertisement 5-13 time, setting 3-6 time-out idle 1-8 port triggering 5-11 TKIP (Temporal Key Integrity Protocol) encryption 2-9 transfer time (backing up) 5-18 troubleshooting 7-1 trusted user 3-3 typographical conventions xi U Universal Plug and Play (UPnP...