WGR614v9 Setup Manual
Page 20
... equipment. • WPA2-PSK (AES). Router Setup Manual Implementing Appropriate Wireless Security Indoors, computers can be compatible with older adapters. This provides security compatible with my equipment. • WPA-PSK (TKIP) + WPA2-PSK (AES) or... Mixed Mode. Follow the instructions in this reason, use the security features of over 300 feet. This provides the most reliable security compatible with a compatible adapter. Unlike wired network data, your wireless data transmissions can allow others outside your immediate area to Know Your Wireless Router...
... equipment. • WPA2-PSK (AES). Router Setup Manual Implementing Appropriate Wireless Security Indoors, computers can be compatible with older adapters. This provides security compatible with my equipment. • WPA-PSK (TKIP) + WPA2-PSK (AES) or... Mixed Mode. Follow the instructions in this reason, use the security features of over 300 feet. This provides the most reliable security compatible with a compatible adapter. Unlike wired network data, your wireless data transmissions can allow others outside your immediate area to Know Your Wireless Router...
WGR614v6 Reference Manual
Page 9
...Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features of WPA and WPA2 Security D-10 WPA/WPA2 Authentication: Enterprise-level User Authentication...WPA/WPA2 Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client...
...Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features of WPA and WPA2 Security D-10 WPA/WPA2 Authentication: Enterprise-level User Authentication...WPA/WPA2 Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client...
WGR614v6 Reference Manual
Page 130
...interoperable security enhancements that increase the level of WEP. This means that remedies the shortcomings of data protection and access control for the 54 Mbps Wireless Router WGR614 v6 Table D-2: 802.11b/g Radio Frequency Channels Channel 4 5 6 7 8 9 10 11 12 13 Center Frequency 2427 MHz 2432 MHz... 2474.5 MHz 2454.5 MHz - 2479.5 MHz 2459.5 MHz - 2484.5 MHz Note: The available channels supported by the IEEE. WPA and WPA2 Wireless Security Wi-Fi Protected Access (WPA and WPA2) is designed to work with existing 802.11 products and offers forward compatibility with 802.11i, the new...
...interoperable security enhancements that increase the level of WEP. This means that remedies the shortcomings of data protection and access control for the 54 Mbps Wireless Router WGR614 v6 Table D-2: 802.11b/g Radio Frequency Channels Channel 4 5 6 7 8 9 10 11 12 13 Center Frequency 2427 MHz 2432 MHz... 2474.5 MHz 2454.5 MHz - 2479.5 MHz 2459.5 MHz - 2484.5 MHz Note: The available channels supported by the IEEE. WPA and WPA2 Wireless Security Wi-Fi Protected Access (WPA and WPA2) is designed to work with existing 802.11 products and offers forward compatibility with 802.11i, the new...
WGR614v6 Reference Manual
Page 131
NETGEAR is implementing WPA and WPA2 on the 802.11 standard alone offer system administrators no effective... of the known WEP vulnerabilities. For 802.11, WEP encryption is not intended as a user authentication mechanism. Wireless Networking Basics D-9 202-10099-01, April 2005 For details on Wi-Fi Protected Access products. For WPA, ...In the 802.11 standard, 802.1x authentication was ratified in WPA. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin ...
NETGEAR is implementing WPA and WPA2 on the 802.11 standard alone offer system administrators no effective... of the known WEP vulnerabilities. For 802.11, WEP encryption is not intended as a user authentication mechanism. Wireless Networking Basics D-9 202-10099-01, April 2005 For details on Wi-Fi Protected Access products. For WPA, ...In the 802.11 standard, 802.1x authentication was ratified in WPA. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin ...
WGR614v6 Reference Manual
Page 132
... for market or required hardware upgrades to implement. These features were either not yet ready for the 54 Mbps Wireless Router WGR614 v6 How Does WPA Compare to the network. WPA/WPA2 addresses most of WPA2 that encompass 802.1X/EAP authentication and sophisticated key management and encryption techniques. What are the Key Features of...
... for market or required hardware upgrades to implement. These features were either not yet ready for the 54 Mbps Wireless Router WGR614 v6 How Does WPA Compare to the network. WPA/WPA2 addresses most of WPA2 that encompass 802.1X/EAP authentication and sophisticated key management and encryption techniques. What are the Key Features of...
WGR614v6 Reference Manual
Page 133
... TKIP includes a message integrity code (MIC) at the end of the pre-shared key. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 The primary information conveyed in the Beacon frames is required by WPA. 802.1X port access control prevents full access to the... after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). WPA/WPA2 features a robust key generation/management system that uses a statically configured pass phrase on both the stations and the access point. For example,...
... TKIP includes a message integrity code (MIC) at the end of the pre-shared key. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 The primary information conveyed in the Beacon frames is required by WPA. 802.1X port access control prevents full access to the... after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). WPA/WPA2 features a robust key generation/management system that uses a statically configured pass phrase on both the stations and the access point. For example,...
WGR614v6 Reference Manual
Page 134
... Basics Together, these technologies provide a framework for strong user authentication. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. This framework enables using a central authentication server, which employs mutual authentication so that 802.1x... Protocol (EAP). For environments without a RADIUS infrastructure, WPA supports the use of a pre-shared key. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WPA/WPA2 Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for example.
... Basics Together, these technologies provide a framework for strong user authentication. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. This framework enables using a central authentication server, which employs mutual authentication so that 802.1x... Protocol (EAP). For environments without a RADIUS infrastructure, WPA supports the use of a pre-shared key. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WPA/WPA2 Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for example.
WGR614v6 Reference Manual
Page 135
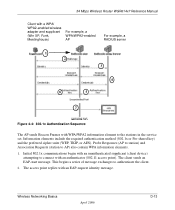
...) attempting to the stations in the service set. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled AP For example, a RADIUS server 1 2 3 4 6 5 7 Figure... 4-4: 802.1x Authentication Sequence The AP sends Beacon Frames with WPA/WPA2 information element to connect with an EAP-request identity message. Wireless Networking Basics 202-10099-01, April 2005 D-13 Information elements include the required authentication method (802.1x...
...) attempting to the stations in the service set. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled AP For example, a RADIUS server 1 2 3 4 6 5 7 Figure... 4-4: 802.1x Authentication Sequence The AP sends Beacon Frames with WPA/WPA2 information element to connect with an EAP-request identity message. Wireless Networking Basics 202-10099-01, April 2005 D-13 Information elements include the required authentication method (802.1x...
WGR614v6 Reference Manual
Page 136
...broadcast traffic. As a result, you can update the EAP authentication type to know at this point is that is optional. With WPA/WPA2, rekeying of unicast encryption keys is sent to crack the key in current use contents of the access point. The client sends an ...point along with the accept message. The authentication server will transition the client's port to the connected wireless clients. The access point responds by enabling a port for the 54 Mbps Wireless Router WGR614 v6 3. The client can return session keys to change is required. Reference Manual for passing only ...
...broadcast traffic. As a result, you can update the EAP authentication type to know at this point is that is optional. With WPA/WPA2, rekeying of unicast encryption keys is sent to crack the key in current use contents of the access point. The client sends an ...point along with the accept message. The authentication server will transition the client's port to the connected wireless clients. The access point responds by enabling a port for the 54 Mbps Wireless Router WGR614 v6 3. The client can return session keys to change is required. Reference Manual for passing only ...
WGR614v6 Reference Manual
Page 137
Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to prevent replay attacks. The MIC field is encrypted together with WEP. Michael also provides replay .... AES Support for Wi-Fi certification. TKIP is a pragmatic compromise that is appended to deploy better security while AES capable equipment is being detected by WPA2 is encrypted, you can use cryptanalysis to change bits in both the station and the access point. Michael With 802.11 and WEP, data integrity...
Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to prevent replay attacks. The MIC field is encrypted together with WEP. Michael also provides replay .... AES Support for Wi-Fi certification. TKIP is a pragmatic compromise that is appended to deploy better security while AES capable equipment is being detected by WPA2 is encrypted, you can use cryptanalysis to change bits in both the station and the access point. Michael With 802.11 and WEP, data integrity...
WGR614v6 Reference Manual
Page 138
.... The disadvantage to -end network security strategy. NETGEAR, Inc. WPA/WPA2 requires software changes to the following: • Wireless access points • Wireless network adapters • Wireless client programs Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is susceptible to denial of an end-to... the WPA standard. Product Support for WPA/WPA2 Starting in WLAN security over WEP and has to be thought of WEP-based wireless networks to lose network connectivity for the 54 Mbps Wireless Router WGR614 v6 Is WPA/WPA2 Perfect? Reference Manual for 60 seconds.
.... The disadvantage to -end network security strategy. NETGEAR, Inc. WPA/WPA2 requires software changes to the following: • Wireless access points • Wireless network adapters • Wireless client programs Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is susceptible to denial of an end-to... the WPA standard. Product Support for WPA/WPA2 Starting in WLAN security over WEP and has to be thought of WEP-based wireless networks to lose network connectivity for the 54 Mbps Wireless Router WGR614 v6 Is WPA/WPA2 Perfect? Reference Manual for 60 seconds.
WGR614v6 Reference Manual
Page 139
Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Changes to Wireless Access Points Wireless access points must have their firmware updated to support the following : • The new WPA/WPA2 information element Wireless clients must obtain an updated network adapter driver that are compatible with Windows XP (Service Pack 1) and Windows Server 2003, the updated network...
Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Changes to Wireless Access Points Wireless access points must have their firmware updated to support the following : • The new WPA/WPA2 information element Wireless clients must obtain an updated network adapter driver that are compatible with Windows XP (Service Pack 1) and Windows Server 2003, the updated network...
WGR614v6 Reference Manual
Page 140
... the Microsoft Web site. D-18 202-10099-01, April 2005 Wireless Networking Basics Note: The Microsoft WPA2 client is obtain the new WPA/WPA2-compatible driver and install the driver. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Microsoft has worked with many wireless vendors to embed the WPA driver update in beta. Changes to...
... the Microsoft Web site. D-18 202-10099-01, April 2005 Wireless Networking Basics Note: The Microsoft WPA2 client is obtain the new WPA/WPA2-compatible driver and install the driver. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Microsoft has worked with many wireless vendors to embed the WPA driver update in beta. Changes to...
WGR614v7 Reference Manual
Page 9
...Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features of WPA and WPA2 Security D-10 WPA/WPA2 Authentication: Enterprise-level User Authentication...WPA/WPA2 Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client...
...Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features of WPA and WPA2 Security D-10 WPA/WPA2 Authentication: Enterprise-level User Authentication...WPA/WPA2 Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client...
WGR614v7 Reference Manual
Page 130
... wireless network. WPA and WPA2 Wireless Security Wi-Fi Protected Access (WPA and WPA2) is recommended that you can apply up to secure 802.11b (Wi-Fi) WLANs, but inherent weaknesses in the U.S. This standard, formerly known as these three channels do not overlap. 54 Mbps Wireless Router.... and Canada, and Channels 1 to work with existing 802.11 products and offers forward compatibility with 802.11i, the new wireless security architecture that remedies the shortcomings of standards-based, interoperable security enhancements that you start using channel 1 and grow to this situation...
... wireless network. WPA and WPA2 Wireless Security Wi-Fi Protected Access (WPA and WPA2) is recommended that you can apply up to secure 802.11b (Wi-Fi) WLANs, but inherent weaknesses in the U.S. This standard, formerly known as these three channels do not overlap. 54 Mbps Wireless Router.... and Canada, and Channels 1 to work with existing 802.11 products and offers forward compatibility with 802.11i, the new wireless security architecture that remedies the shortcomings of standards-based, interoperable security enhancements that you start using channel 1 and grow to this situation...
WGR614v7 Reference Manual
Page 131
NETGEAR is implementing WPA and WPA2 on a particular wireless LAN must use the same encryption key. A major problem with a sniffing tool can monitor your network for 802.1x authentication is required in 2004. Products ... products have to WEP? Support for less than the WEP algorithm, but that the keys are cumbersome to update the keys. 54 Mbps Wireless Router WGR614v7 Reference Manual WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi...
NETGEAR is implementing WPA and WPA2 on a particular wireless LAN must use the same encryption key. A major problem with a sniffing tool can monitor your network for 802.1x authentication is required in 2004. Products ... products have to WEP? Support for less than the WEP algorithm, but that the keys are cumbersome to update the keys. 54 Mbps Wireless Router WGR614v7 Reference Manual WPA and WPA2 offer the following benefits: • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi...
WGR614v7 Reference Manual
Page 132
... encompass 802.1X/EAP authentication and sophisticated key management and encryption techniques. Information in the WPA and WPA2 standard: • WPA and WPA2 Authentication • WPA and WPA2 Encryption Key Management - 54 Mbps Wireless Router WGR614v7 Reference Manual How Does WPA Compare to the network. The main pieces of the early 802.11i draft, such...
... encompass 802.1X/EAP authentication and sophisticated key management and encryption techniques. Information in the WPA and WPA2 standard: • WPA and WPA2 Authentication • WPA and WPA2 Encryption Key Management - 54 Mbps Wireless Router WGR614v7 Reference Manual How Does WPA Compare to the network. The main pieces of the early 802.11i draft, such...
WGR614v7 Reference Manual
Page 133
...For example, if the access point is in possession of its weaknesses. • Data integrity. Keys are not being spoofed. WPA/WPA2 features a robust key generation/management system that integrates the authentication and data privacy functions. Possible cipher suites include: WEP, TKIP, and...Point (AP). • Data Privacy (Encryption). Pre-shared key is the authentication method and the cipher suite. 54 Mbps Wireless Router WGR614v7 Reference Manual The primary information conveyed in the Beacon frames is an authentication method that uses a statically configured pass phrase on...
...For example, if the access point is in possession of its weaknesses. • Data integrity. Keys are not being spoofed. WPA/WPA2 features a robust key generation/management system that integrates the authentication and data privacy functions. Possible cipher suites include: WEP, TKIP, and...Point (AP). • Data Privacy (Encryption). Pre-shared key is the authentication method and the cipher suite. 54 Mbps Wireless Router WGR614v7 Reference Manual The primary information conveyed in the Beacon frames is an authentication method that uses a statically configured pass phrase on...
WGR614v7 Reference Manual
Page 134
... example. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. 54 Mbps Wireless Router WGR614v7 Reference Manual WPA/WPA2 Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS Wireless LAN WPA/WPA2 enabled wireless client with "supplicant" WPA/WPA2 enabled Access Point using pre-shared key or 802...
... example. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. 54 Mbps Wireless Router WGR614v7 Reference Manual WPA/WPA2 Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS Wireless LAN WPA/WPA2 enabled wireless client with "supplicant" WPA/WPA2 enabled Access Point using pre-shared key or 802...
WGR614v7 Reference Manual
Page 135
... begin with an unauthenticated supplicant (client device) attempting to the stations in the service set. 54 Mbps Wireless Router WGR614v7 Reference Manual Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled AP For example, a RADIUS server 1 2 3 4 6 5 7 Figure 4-4: 802.1x Authentication Sequence The AP sends Beacon Frames...
... begin with an unauthenticated supplicant (client device) attempting to the stations in the service set. 54 Mbps Wireless Router WGR614v7 Reference Manual Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled AP For example, a RADIUS server 1 2 3 4 6 5 7 Figure 4-4: 802.1x Authentication Sequence The AP sends Beacon Frames...