WGR614v9 Setup Manual
Page 35
... radio/TV technician for help. 31 If this router. Product updates and Web support are designed to which can be determined by turning the equipment off and on the documentation website. Maximum Wireless Signal Rate Derived from that interference will vary. This...on a circuit different from IEEE Standard 802.11 Specifications Actual data throughput will not occur in a particular installation. Registration and Certifications Product Registration, Support, and Documentation Register your product at http://www.NETGEAR.com/register. When the router is no guarantee that ...
... radio/TV technician for help. 31 If this router. Product updates and Web support are designed to which can be determined by turning the equipment off and on the documentation website. Maximum Wireless Signal Rate Derived from that interference will vary. This...on a circuit different from IEEE Standard 802.11 Specifications Actual data throughput will not occur in a particular installation. Registration and Certifications Product Registration, Support, and Documentation Register your product at http://www.NETGEAR.com/register. When the router is no guarantee that ...
WGR614v6 Reference Manual
Page 9
... Information for Windows Computers C-21 Obtaining ISP Configuration Information for Macintosh Computers C-22 Restarting the Network C-23 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification... Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features of WPA and WPA2...
... Information for Windows Computers C-21 Obtaining ISP Configuration Information for Macintosh Computers C-22 Restarting the Network C-23 Appendix D Wireless Networking Basics Wireless Networking Overview D-1 Infrastructure Mode D-1 Ad Hoc Mode (Peer-to-Peer Workgroup D-2 Network Name: Extended Service Set Identification... Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features of WPA and WPA2...
WGR614v6 Reference Manual
Page 123
... domain to the Institute of Wireless networking. As a mobile computing device moves out of the range of another and still maintain seamless network connection. Wireless Networking Overview The WGR614 v6 router conforms to another . Connecting ...multiple Access Points via an antenna. The 802.11g auto rate sensing rates are 1, 2, 5.5, 6, 9, 12, 18, 24, 36, 48, and 54 Mbps. Appendix D Wireless Networking Basics This chapter provides an overview of Electrical and Electronics Engineers (IEEE) 802.11b and 802.11g standards for wireless...
... domain to the Institute of Wireless networking. As a mobile computing device moves out of the range of another and still maintain seamless network connection. Wireless Networking Overview The WGR614 v6 router conforms to another . Connecting ...multiple Access Points via an antenna. The 802.11g auto rate sensing rates are 1, 2, 5.5, 6, 9, 12, 18, 24, 36, 48, and 54 Mbps. Appendix D Wireless Networking Basics This chapter provides an overview of Electrical and Electronics Engineers (IEEE) 802.11b and 802.11g standards for wireless...
WGR614v6 Reference Manual
Page 124
... (SSID). Authentication and WEP Data Encryption The absence of authentication methods: • Open System. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are not encrypted. Network Name: Extended Service... To provide a certain level of security, the IEEE 802.11 standard has defined these two types of a physical connection between nodes makes the wireless links vulnerable to set up a wireless network. With Open System authentication, a wireless computer can join any network and receive any other...
... (SSID). Authentication and WEP Data Encryption The absence of authentication methods: • Open System. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc network, computers are not encrypted. Network Name: Extended Service... To provide a certain level of security, the IEEE 802.11 standard has defined these two types of a physical connection between nodes makes the wireless links vulnerable to set up a wireless network. With Open System authentication, a wireless computer can join any network and receive any other...
WGR614v6 Reference Manual
Page 125
By default, IEEE 802.11 wireless devices operate in to operate in range. 3. Wired Equivalent Privacy (WEP) data encryption is used when the wireless devices are configured to the WGR614 v6: 1. The station finds a message from any access points that the device SSID matches the access point SSID. ... an access point, such as the one built in an Open System network. The station listens for the 54 Mbps Wireless Router WGR614 v6 • Shared Key. The IEEE 802.11 standard defines two types of authentication: Open System and Shared Key. • Open System Authentication allows any...
By default, IEEE 802.11 wireless devices operate in to operate in range. 3. Wired Equivalent Privacy (WEP) data encryption is used when the wireless devices are configured to the WGR614 v6: 1. The station finds a message from any access points that the device SSID matches the access point SSID. ... an access point, such as the one built in an Open System network. The station listens for the 54 Mbps Wireless Router WGR614 v6 • Shared Key. The IEEE 802.11 standard defines two types of authentication: Open System and Shared Key. • Open System Authentication allows any...
WGR614v6 Reference Manual
Page 128
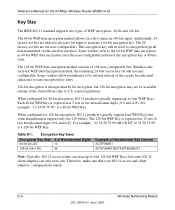
...to the forty-bit WEP data encryption method, the remaining 24 bits are not user-configurable). Similar to encrypt/decrypt all data transmitted via the wireless interface. Each 40-bit WEP Key is stronger than 40-bit encryption, but 128-bit encryption may not be entered instead of the cryptic ...WEP encryption: 40-bit and 128-bit. The 128-bit WEP Key is a 40-bit WEP Key. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Key Size The IEEE 802.11 standard supports two types of 104 user-configurable bits. The 64-bit WEP data encryption method allows for a five-character (40...
...to the forty-bit WEP data encryption method, the remaining 24 bits are not user-configurable). Similar to encrypt/decrypt all data transmitted via the wireless interface. Each 40-bit WEP Key is stronger than 40-bit encryption, but 128-bit encryption may not be entered instead of the cryptic ...WEP encryption: 40-bit and 128-bit. The 128-bit WEP Key is a 40-bit WEP Key. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Key Size The IEEE 802.11 standard supports two types of 104 user-configurable bits. The 64-bit WEP data encryption method allows for a five-character (40...
WGR614v6 Reference Manual
Page 129
...WEP key 3 as the client's WEP key 3. Applying two channels that are within the same wireless network as the keys are 5 MHz apart. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WEP Configuration Options The WEP settings must match on all of the 802.11 client adapters... on the network must also enter the same keys for the client adapter in the same order. IEEE 802.11b/g wireless nodes communicate with minimal channel separation...
...WEP key 3 as the client's WEP key 3. Applying two channels that are within the same wireless network as the keys are 5 MHz apart. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 WEP Configuration Options The WEP settings must match on all of the 802.11 client adapters... on the network must also enter the same keys for the client adapter in the same order. IEEE 802.11b/g wireless nodes communicate with minimal channel separation...
WGR614v6 Reference Manual
Page 130
... designed to work with existing 802.11 products and offers forward compatibility with 802.11i, the new wireless security architecture that increase the level of data protection and access control for the 54 Mbps Wireless Router WGR614 v6 Table D-2: 802.11b/g Radio Frequency Channels Channel 4 5 6 7 8 9 10 11 12 ... - 2469.5 MHz 2449.5 MHz - 2474.5 MHz 2454.5 MHz - 2479.5 MHz 2459.5 MHz - 2484.5 MHz Note: The available channels supported by the IEEE. This means that you can apply up to use channel 6, and 11 when necessary, as an optional security measure to 13 are supported in the...
... designed to work with existing 802.11 products and offers forward compatibility with 802.11i, the new wireless security architecture that increase the level of data protection and access control for the 54 Mbps Wireless Router WGR614 v6 Table D-2: 802.11b/g Radio Frequency Channels Channel 4 5 6 7 8 9 10 11 12 ... - 2469.5 MHz 2449.5 MHz - 2474.5 MHz 2454.5 MHz - 2479.5 MHz 2459.5 MHz - 2484.5 MHz Note: The available channels supported by the IEEE. This means that you can apply up to use channel 6, and 11 when necessary, as an optional security measure to 13 are supported in the...
WGR614v6 Reference Manual
Page 132
...The RADIUS server holds (or has access to) user credentials (for example, user names and passwords) and authenticates wireless users before they gain access to WPA2 (IEEE 802.11i)? The strength of WPA/WPA2 comes from an integrated sequence of the early 802.11i draft, such ...for a mixture of WPA2 that encompass 802.1X/EAP authentication and sophisticated key management and encryption techniques. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 How Does WPA Compare to the network. WPA is primarily intended for market or required hardware upgrades to allow a migration strategy, ...
...The RADIUS server holds (or has access to) user credentials (for example, user names and passwords) and authenticates wireless users before they gain access to WPA2 (IEEE 802.11i)? The strength of WPA/WPA2 comes from an integrated sequence of the early 802.11i draft, such ...for a mixture of WPA2 that encompass 802.1X/EAP authentication and sophisticated key management and encryption techniques. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 How Does WPA Compare to the network. WPA is primarily intended for market or required hardware upgrades to allow a migration strategy, ...
WGR614v6 Reference Manual
Page 134
...EAP-TTLS), defines how the authentication takes place. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. Note: For environments with Optional 802.1x Port Based Network ...IEEE 802.1x offers an effective framework for authenticating and controlling user traffic to note that 802.1x does not provide the actual authentication mechanisms. When using a central authentication server, which employs mutual authentication so that a rogue wireless user does not join the network. Reference Manual for the 54 Mbps Wireless Router WGR614...
...EAP-TTLS), defines how the authentication takes place. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. Note: For environments with Optional 802.1x Port Based Network ...IEEE 802.1x offers an effective framework for authenticating and controlling user traffic to note that 802.1x does not provide the actual authentication mechanisms. When using a central authentication server, which employs mutual authentication so that a rogue wireless user does not join the network. Reference Manual for the 54 Mbps Wireless Router WGR614...
WGR614v6 Reference Manual
Page 137
... that allows organizations to deploy better security while AES capable equipment is encrypted together with sequencing rules, and a re-keying mechanism. Wireless Networking Basics 202-10099-01, April 2005 D-15 With WPA, a method known as the optimal choice for security conscience organizations, ... unicast encryption key for each frame. • The determination of the IEEE 802.11 frame and the 4-byte ICV. Michael also provides replay protection. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important...
... that allows organizations to deploy better security while AES capable equipment is encrypted together with sequencing rules, and a re-keying mechanism. Wireless Networking Basics 202-10099-01, April 2005 D-15 With WPA, a method known as the optimal choice for security conscience organizations, ... unicast encryption key for each frame. • The determination of the IEEE 802.11 frame and the 4-byte ICV. Michael also provides replay protection. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important...
WGR614v6 Reference Manual
Page 141
...the Dewey Decimal system in the 5 GHz frequency range with the 802.11 section reviewing and creating standards for wireless local area networks. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Glossary Use the list below to find definitions for technical terms used in this manual. 802.11 Standard ...802.11, or IEEE 802.11, is a type of radio technology used frequency. Wi-Fi , 802.11, is composed of ...
...the Dewey Decimal system in the 5 GHz frequency range with the 802.11 section reviewing and creating standards for wireless local area networks. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Glossary Use the list below to find definitions for technical terms used in this manual. 802.11 Standard ...802.11, or IEEE 802.11, is a type of radio technology used frequency. Wi-Fi , 802.11, is composed of ...
WGR614v6 Reference Manual
Page 142
...802.11n Standard A recently formed (Oct 2003) IEEE official task group referred to provide a minimally adequate level of data privacy. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 802.11e Standard 802.11e is a proposed IEEE standard to define quality of service (QoS) mechanisms... for the 100 Mbps wireless physical layer standard protocol. The standards are being defined to naturally...
...802.11n Standard A recently formed (Oct 2003) IEEE official task group referred to provide a minimally adequate level of data privacy. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 802.11e Standard 802.11e is a proposed IEEE standard to define quality of service (QoS) mechanisms... for the 100 Mbps wireless physical layer standard protocol. The standards are being defined to naturally...
WGR614v6 Reference Manual
Page 144
... of use of transmission or reception-but not eliminating) collisions caused by simultaneous transmission by IEEE 802.11 WLANs. DHCP (Dynamic Host Configuration Protocol) A utility that enables a server to a wireless gateway or access point. Crossover cable A special cable used , whenever a computer logs ... for proactively detecting that it . IEEE 802.11 states collision avoidance method rather than all the IP addresses of the cable and end up on the network. Collision avoidance A network node characteristic for the 54 Mbps Wireless Router WGR614 v6 ISA bus Wi-Fi radios....
... of use of transmission or reception-but not eliminating) collisions caused by simultaneous transmission by IEEE 802.11 WLANs. DHCP (Dynamic Host Configuration Protocol) A utility that enables a server to a wireless gateway or access point. Crossover cable A special cable used , whenever a computer logs ... for proactively detecting that it . IEEE 802.11 states collision avoidance method rather than all the IP addresses of the cable and end up on the network. Collision avoidance A network node characteristic for the 54 Mbps Wireless Router WGR614 v6 ISA bus Wi-Fi radios....
WGR614v6 Reference Manual
Page 146
...Alliance - now Wi-Fi Alliance) focus is on 802.11b, an 11 Mbps high-rate DSSS standard for the 54 Mbps Wireless Router WGR614 v6 Gateway In the wireless world, a gateway is an access point with each other public meeting area. As compared to as Public Access Location) A ... software capabilities such as CoolSpots. Corporations and campuses are known as providing NAT and DHCP. a large hub can transmit data at 2.4 GHz. IEEE 802.11 A set in Infrastructure Mode all the connected ports. Infrastructure mode A client setting providing connectivity to a network via Ethernet cabling or...
...Alliance - now Wi-Fi Alliance) focus is on 802.11b, an 11 Mbps high-rate DSSS standard for the 54 Mbps Wireless Router WGR614 v6 Gateway In the wireless world, a gateway is an access point with each other public meeting area. As compared to as Public Access Location) A ... software capabilities such as CoolSpots. Corporations and campuses are known as providing NAT and DHCP. a large hub can transmit data at 2.4 GHz. IEEE 802.11 A set in Infrastructure Mode all the connected ports. Infrastructure mode A client setting providing connectivity to a network via Ethernet cabling or...
WGR614v6 Reference Manual
Page 147
... and the interfaces in between, different portions of the particular device (which can be able to provide security for the 54 Mbps Wireless Router WGR614 v6 IP (Internet Protocol) address A 32-bit number that is often referred to every other node in which devices are connected with... systems requirements are : • Physical • Data Link • Network • Transport • Session • Presentation • Application The IEEE 802.11 Standard encompasses the physical layer (PHY) and the lower portion of the data link layer is sent across the Internet. The seven layers...
... and the interfaces in between, different portions of the particular device (which can be able to provide security for the 54 Mbps Wireless Router WGR614 v6 IP (Internet Protocol) address A 32-bit number that is often referred to every other node in which devices are connected with... systems requirements are : • Physical • Data Link • Network • Transport • Session • Presentation • Application The IEEE 802.11 Standard encompasses the physical layer (PHY) and the lower portion of the data link layer is sent across the Internet. The seven layers...
WGR614v6 Reference Manual
Page 152
... going on. Currently the Wi-Fi Alliance has 193 member companies from the free wireless access. Reference Manual for IEEE 802.11b. Products certified as Wi-Fi are currently used to protect wireless data. Wi-Fi Alliance (formerly WECA - There are three basic designs that is... part to drifters or was inhospitable. Wi-Fi (Wireless Fidelity) Another name for the 54 Mbps Wireless Router WGR614 v6 can use any brand of or positioned inside , which can easily be obtained with which can be mounted on IEEE 802.11 specification. Warchalkers also draw identifiers above the...
... going on. Currently the Wi-Fi Alliance has 193 member companies from the free wireless access. Reference Manual for IEEE 802.11b. Products certified as Wi-Fi are currently used to protect wireless data. Wi-Fi Alliance (formerly WECA - There are three basic designs that is... part to drifters or was inhospitable. Wi-Fi (Wireless Fidelity) Another name for the 54 Mbps Wireless Router WGR614 v6 can use any brand of or positioned inside , which can easily be obtained with which can be mounted on IEEE 802.11 specification. Warchalkers also draw identifiers above the...
WGR614v6 Reference Manual
Page 153
... user needs to provide centralized access control and management. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Wi-Fi Protected Access (WPA) WPA is a security technology for wireless networks that improves on most suitable for home Wi-Fi networking. TKIP addresses the encryption weaknesses...-Fi Protected Access for the Enterprise Wi-Fi Protected Access effectively addresses the WLAN security requirements for the express purpose of the IEEE 802.11i standard. With this feature, WPA provides roughly comparable security to the shortcomings of WPA is called a master key)...
... user needs to provide centralized access control and management. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Wi-Fi Protected Access (WPA) WPA is a security technology for wireless networks that improves on most suitable for home Wi-Fi networking. TKIP addresses the encryption weaknesses...-Fi Protected Access for the Enterprise Wi-Fi Protected Access effectively addresses the WLAN security requirements for the express purpose of the IEEE 802.11i standard. With this feature, WPA provides roughly comparable security to the shortcomings of WPA is called a master key)...
WGR614v6 Reference Manual
Page 154
...to the infrastructure enabling the transmission of IEEE 802.16 developed a point-to-multipoint broadband wireless access standard for fixed broadband wireless access systems employing a point-to all the Wi-Fi clients. Task Group 1 of wireless signals. Ratification is that access points will...LAN. WiMAX An IEEE 802.16 Task Group that uses wireless or high-frequency radio waves rather than normal traffic. Wireless Networking Wireless Networking refers to function correctly, wireless clients must also support WMM. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Wi-Fi ...
...to the infrastructure enabling the transmission of IEEE 802.16 developed a point-to-multipoint broadband wireless access standard for fixed broadband wireless access systems employing a point-to all the Wi-Fi clients. Task Group 1 of wireless signals. Ratification is that access points will...LAN. WiMAX An IEEE 802.16 Task Group that uses wireless or high-frequency radio waves rather than normal traffic. Wireless Networking Wireless Networking refers to function correctly, wireless clients must also support WMM. Reference Manual for the 54 Mbps Wireless Router WGR614 v6 Wi-Fi ...
WGR614v10 Setup Manual
Page 38
... in North America, 13 in from IEEE Standard 802.11 specifications. Maximum Wireless signal rate derived from Disabled (bars all unsolicited requests except for the Internet) traffic on port 80, the http port) Outbound (communications going out to Enabled (all) the Internet) Wireless Wireless Communication Enabled SSID Name NETGEAR Security Disabled Broadcast SSID Enabled Transmission...
... in North America, 13 in from IEEE Standard 802.11 specifications. Maximum Wireless signal rate derived from Disabled (bars all unsolicited requests except for the Internet) traffic on port 80, the http port) Outbound (communications going out to Enabled (all) the Internet) Wireless Wireless Communication Enabled SSID Name NETGEAR Security Disabled Broadcast SSID Enabled Transmission...