User Guide
Page 2
Linksys, Cisco and the Cisco Logo are subject to make understanding networking with 2 Phone Ports Copyright and Trademarks Specifications are registered trademarks or trademarks of their respective holders. Also, each figure (diagram, screenshot, or other ...and birth defects or other countries. All rights reserved. In addition to do while using the Wireless-G Broadband Router. WRTU54G-TM-UG-81009-B-BW-DF-JL Wireless-G Broadband Router with the Wireless-G Broadband Router easier than ever. This question mark provides you might need to these symbols, there are definitions...
Linksys, Cisco and the Cisco Logo are subject to make understanding networking with 2 Phone Ports Copyright and Trademarks Specifications are registered trademarks or trademarks of their respective holders. Also, each figure (diagram, screenshot, or other ...and birth defects or other countries. All rights reserved. In addition to do while using the Wireless-G Broadband Router. WRTU54G-TM-UG-81009-B-BW-DF-JL Wireless-G Broadband Router with the Wireless-G Broadband Router easier than ever. This question mark provides you might need to these symbols, there are definitions...
User Guide
Page 4
... Appendix F: Glossary 64 Appendix G: Specifications 71 Appendix H: Warranty Information 73 Appendix I: Regulatory Information 74 Appendix J: Software License Agreement 81 Software in Linksys Products 81 Schedule 1 - Management 36 The Administration Tab - Diagnostics 37 The Administration Tab - Log 36 The Administration Tab - Wireless 41 The Status Tab - Router 39 The Status Tab - Linksys Software License Agreement 81...
... Appendix F: Glossary 64 Appendix G: Specifications 71 Appendix H: Warranty Information 73 Appendix I: Regulatory Information 74 Appendix J: Software License Agreement 81 Software in Linksys Products 81 Schedule 1 - Management 36 The Administration Tab - Diagnostics 37 The Administration Tab - Log 36 The Administration Tab - Wireless 41 The Status Tab - Router 39 The Status Tab - Linksys Software License Agreement 81...
User Guide
Page 10
... the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router. • Appendix I: Regulatory Information This appendix supplies the regulatory information regarding the Router. • Appendix J: Contact Information This appendix provides contact information for a variety of terms frequently used in this User Guide? Wireless-G Broadband Router with 2 Phone...
... the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router. • Appendix I: Regulatory Information This appendix supplies the regulatory information regarding the Router. • Appendix J: Contact Information This appendix provides contact information for a variety of terms frequently used in this User Guide? Wireless-G Broadband Router with 2 Phone...
User Guide
Page 11
... other through an access point. Network Layout The Wireless-G Broadband Router has been specifically designed for a wireless router or access point. Ad-Hoc mode allows computers equipped with wireless transmitters and receivers to the same wireless network. And, of the Router. Now, products using these two modes depends on the wireless network, then the Ad-Hoc mode can set...
... other through an access point. Network Layout The Wireless-G Broadband Router has been specifically designed for a wireless router or access point. Ad-Hoc mode allows computers equipped with wireless transmitters and receivers to the same wireless network. And, of the Router. Now, products using these two modes depends on the wireless network, then the Ad-Hoc mode can set...
User Guide
Page 28
... packets travel to reach a specific host or network.) Enter the information described below to the Internet, select Router. The Router determines the network packets' route based on your network. From the drop-down list. (A static route is hosting your changes. Change these settings as data from the Internet. Wireless-G Broadband Router with 2 Phone Ports The...
... packets travel to reach a specific host or network.) Enter the information described below to the Internet, select Router. The Router determines the network packets' route based on your network. From the drop-down list. (A static route is hosting your changes. Change these settings as data from the Internet. Wireless-G Broadband Router with 2 Phone Ports The...
User Guide
Page 36
... transmissions to local servers from being scanned by hiding your network environment. This feature uses port forwarding to block access to specific recipients at the IP layer. This feature keeps port 113 from being "pinged," or detected, by default. Internet Protocol... VPN Passthrough 29 Multicasting allows for outside of the Block WAN Request feature make it . IPSec Pass-through the Router's firewall. Wireless-G Broadband Router with 2 Phone Ports The Security Tab - Select Enabled to filter multicasting, or Disabled to implement secure exchange of...
... transmissions to local servers from being scanned by hiding your network environment. This feature uses port forwarding to block access to specific recipients at the IP layer. This feature keeps port 113 from being "pinged," or detected, by default. Internet Protocol... VPN Passthrough 29 Multicasting allows for outside of the Block WAN Request feature make it . IPSec Pass-through the Router's firewall. Wireless-G Broadband Router with 2 Phone Ports The Security Tab - Select Enabled to filter multicasting, or Disabled to implement secure exchange of...
User Guide
Page 37
... during which the policy will appear. Internet Access Figure 5-30: Internet Policy Summary Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports Change these settings as Internet access, designated services, websites, and inbound traffic during specific days and times. Use the settings on whether you listed on the List of PCs 30 Click...
... during which the policy will appear. Internet Access Figure 5-30: Internet Policy Summary Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports Change these settings as Internet access, designated services, websites, and inbound traffic during specific days and times. Use the settings on whether you listed on the List of PCs 30 Click...
User Guide
Page 38
...Save Settings button to the Access Restrictions screen, click the Close button. 8. If the service you want to block websites with specific URL addresses, enter each keyword in the Service Name field. To delete a service, select it from the Protocol drop-down ...you want to cancel your changes, click the Cancel button. Figure 5-32: Port Services Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports 7. Internet Access Wireless-G Broadband Router with 2 Phone Ports 31 The Access Restrictions Tab - Change these settings as FTP or telnet, by selecting ...
...Save Settings button to the Access Restrictions screen, click the Close button. 8. If the service you want to block websites with specific URL addresses, enter each keyword in the Service Name field. To delete a service, select it from the Protocol drop-down ...you want to cancel your changes, click the Cancel button. Figure 5-32: Port Services Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports 7. Internet Access Wireless-G Broadband Router with 2 Phone Ports 31 The Access Restrictions Tab - Change these settings as FTP or telnet, by selecting ...
User Guide
Page 39
... functions such as described here and click the Save Settings button to apply your changes or Cancel Changes to 12 characters. Wireless-G Broadband Router with 2 Phone Ports 32 The Applications and Gaming Tab - For each line for the criteria required. Figure 5-33: ... Forward Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The Applications and Gaming Tab - The criteria are any forwarding.) To forward a port, enter the information on each application, enter the IP Address of the PC running the specific application. Change these settings as...
... functions such as described here and click the Save Settings button to apply your changes or Cancel Changes to 12 characters. Wireless-G Broadband Router with 2 Phone Ports 32 The Applications and Gaming Tab - For each line for the criteria required. Figure 5-33: ... Forward Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The Applications and Gaming Tab - The criteria are any forwarding.) To forward a port, enter the information on each application, enter the IP Address of the PC running the specific application. Change these settings as...
User Guide
Page 40
...the Triggered Range. Figure 5-34: Applications and Gaming Tab Port Triggering Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The Applications & Gaming Tab - Wireless-G Broadband Router with 2 Phone Ports 33 The Applications & Gaming Tab - Port Triggering The Port Triggering screen...Router to the proper computer by way of the Forwarded Range. Enter the ending port number of the Triggered Range. End Port. Triggered Range For each application, list the forwarded port number range. Check with the Internet application documentation for specific...
...the Triggered Range. Figure 5-34: Applications and Gaming Tab Port Triggering Chapter 5: Configuring the Wireless-G Broadband Router with 2 Phone Ports The Applications & Gaming Tab - Wireless-G Broadband Router with 2 Phone Ports 33 The Applications & Gaming Tab - Port Triggering The Port Triggering screen...Router to the proper computer by way of the Forwarded Range. Enter the ending port number of the Triggered Range. End Port. Triggered Range For each application, list the forwarded port number range. Check with the Internet application documentation for specific...
User Guide
Page 43
...SSL (Secured Socket Layer) to confirm. Wireless Access Web - When using your Wireless Router in the Re-enter to confirm field to encrypt data transmitted for your changes or Cancel Changes to the utility. Figure 5-37: Administration Tab - Log The Router can keep the default setting, Disable. ...connection. The communications protocol used to connect to cancel your guests, you wish to manage specific Router functions for access and security. Select HTTP or HTTPS. To access the Router remotely, from here. When you wish to view the logs, click Incoming Log or...
...SSL (Secured Socket Layer) to confirm. Wireless Access Web - When using your Wireless Router in the Re-enter to confirm field to encrypt data transmitted for your changes or Cancel Changes to the utility. Figure 5-37: Administration Tab - Log The Router can keep the default setting, Disable. ...connection. The communications protocol used to connect to cancel your guests, you wish to manage specific Router functions for access and security. Select HTTP or HTTPS. To access the Router remotely, from here. When you wish to view the logs, click Incoming Log or...
User Guide
Page 46
...This is the specific name for a DHCP connection, click this button to replace the current IP address-of the device connected to the Router's Internet port. Domain Name. Firmware Version. This shows the time, as seen by your ISP. Router Name. Configuration ... Status Tab displays the Router's current status. Router This is the Router's current firmware. DHCP Release. Available for the Router, which you set on the Setup Tab. Router Chapter 5: Configuring the Wireless-G Broadband Router with a new IP address. Host Name. Router The Router screen on the Setup ...
...This is the specific name for a DHCP connection, click this button to replace the current IP address-of the device connected to the Router's Internet port. Domain Name. Firmware Version. This shows the time, as seen by your ISP. Router Name. Configuration ... Status Tab displays the Router's current status. Router This is the Router's current firmware. DHCP Release. Available for the Router, which you set on the Setup Tab. Router Chapter 5: Configuring the Wireless-G Broadband Router with a new IP address. Host Name. Router The Router screen on the Setup ...
User Guide
Page 54
...Zone (DMZ) hosting. Check the Enable option for the Application. 3. This option is to go to use a certain Internet application: 1. Wireless-G Broadband Router with 2 Phone Ports 7. Follow these steps to set up online game hosting or use DMZ hosting, since forwarding has priority over DMZ ...hosting. (In other Internet applications. Enter any Internet game, server, or application to function properly, consider exposing one PC to a specific ...
...Zone (DMZ) hosting. Check the Enable option for the Application. 3. This option is to go to use a certain Internet application: 1. Wireless-G Broadband Router with 2 Phone Ports 7. Follow these steps to set up online game hosting or use DMZ hosting, since forwarding has priority over DMZ ...hosting. (In other Internet applications. Enter any Internet game, server, or application to function properly, consider exposing one PC to a specific ...
User Guide
Page 64
... note that information. Appendix B: Wireless Security Security Precautions NOTE: Some of Linksys products provide several network security features, but they require specific action on implementing these security features are setting up or using your wireless network. Change the default password ... messages can change those settings. The current generation of these security features, refer to "Chapter 5: Configuring the Wireless-G Broadband Router." For information on your network performance. 7. Here are easy to find. Change the administrator's password regularly. Security...
... note that information. Appendix B: Wireless Security Security Precautions NOTE: Some of Linksys products provide several network security features, but they require specific action on implementing these security features are setting up or using your wireless network. Change the default password ... messages can change those settings. The current generation of these security features, refer to "Chapter 5: Configuring the Wireless-G Broadband Router." For information on your network performance. 7. Here are easy to find. Change the administrator's password regularly. Security...
User Guide
Page 72
... 65 A device that connects a computer to the cable television network, which translates the names of websites into IP addresses. A specific name for a limited amount of time, instead of assigning permanent IP addresses. Wireless-G Broadband Router with a redundant bit pattern resulting in a lower probability of information being lost in transit. A method of computers. A signal...
... 65 A device that connects a computer to the cable television network, which translates the names of websites into IP addresses. A specific name for a limited amount of time, instead of assigning permanent IP addresses. Wireless-G Broadband Router with a redundant bit pattern resulting in a lower probability of information being lost in transit. A method of computers. A signal...
User Guide
Page 73
...in the wireless router, EasyKeySetup will use the currently security settings and share those with an e-mail address. If you the name associated with the T-Mobile phone. ...you have enabled security and have not previously enabled security for the wireless router, the default will create a secure wireless connection using encryption. Encryption - A networking protocol that uses digital ... F: Glossary 66 Firewall - A set of related programs located at a time. Wireless-G Broadband Router with different, incompatible communications protocols. A device that can occur in a network. To...
...in the wireless router, EasyKeySetup will use the currently security settings and share those with an e-mail address. If you the name associated with the T-Mobile phone. ...you have enabled security and have not previously enabled security for the wireless router, the default will create a secure wireless connection using encryption. Encryption - A networking protocol that uses digital ... F: Glossary 66 Firewall - A set of related programs located at a time. Wireless-G Broadband Router with different, incompatible communications protocols. A device that can occur in a network. To...
User Guide
Page 78
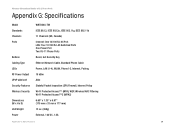
Wireless-G Broadband Router with 2 Phone Ports Appendix G: Specifications Model Standards Channels Ports Buttons Cabling Type LEDs RF Power Output UPnP able/cert Security Features Wireless Security Dimensions (W x H x D) Unit Weight Power WRTU54G-TM IEEE 802.3, IEEE 802.3u, IEEE 802.11g, IEEE 802.11b 11 Channels (US, ..., LAN (1-4), WLAN, Phone1-2, Internet, Pairing 18 dBm Able Stateful Packet Inspection (SPI) Firewall, Internet Policy Wi-Fi Protected Access™ (WPA), WEP, Wireless MAC Filtering Wi-Fi Protected Access™2 (WPA2) 6.69" x 1.30" x 6.97" (170 mm x 33 mm x 177 mm) 13 oz...
Wireless-G Broadband Router with 2 Phone Ports Appendix G: Specifications Model Standards Channels Ports Buttons Cabling Type LEDs RF Power Output UPnP able/cert Security Features Wireless Security Dimensions (W x H x D) Unit Weight Power WRTU54G-TM IEEE 802.3, IEEE 802.3u, IEEE 802.11g, IEEE 802.11b 11 Channels (US, ..., LAN (1-4), WLAN, Phone1-2, Internet, Pairing 18 dBm Able Stateful Packet Inspection (SPI) Firewall, Internet Policy Wi-Fi Protected Access™ (WPA), WEP, Wireless MAC Filtering Wi-Fi Protected Access™2 (WPA2) 6.69" x 1.30" x 6.97" (170 mm x 33 mm x 177 mm) 13 oz...
User Guide
Page 79
Wireless-G Broadband Router with 2 Phone Ports Certifications FCC, IC-03, CE, Wi-Fi (802.11b, 802.11g), WPA, WPA2, WMM Operating Temp. 0ºC to 40ºC (32ºF to 104ºF) Storage Temp. -20ºC to 70ºC (-4ºF to 158ºF) Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 72
Wireless-G Broadband Router with 2 Phone Ports Certifications FCC, IC-03, CE, Wi-Fi (802.11b, 802.11g), WPA, WPA2, WMM Operating Temp. 0ºC to 40ºC (32ºF to 104ºF) Storage Temp. -20ºC to 70ºC (-4ºF to 158ºF) Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 72
User Guide
Page 80
... Appendix H: Warranty Information This warranty gives You specific legal rights, and You may not apply to You. In addition, due to the continual development of new techniques for intruding upon and attacking networks, Linksys does not warrant that , for a period ...the exclusion or limitation of America and Canada are responsible for all inquiries to: Linksys, P.O. You are responsible for shipping defective Products to Linksys. Wireless-G Broadband Router with instructions supplied by Linksys, or (c) has been subjected to abnormal physical or electrical stress, misuse, ...
... Appendix H: Warranty Information This warranty gives You specific legal rights, and You may not apply to You. In addition, due to the continual development of new techniques for intruding upon and attacking networks, Linksys does not warrant that , for a period ...the exclusion or limitation of America and Canada are responsible for all inquiries to: Linksys, P.O. You are responsible for shipping defective Products to Linksys. Wireless-G Broadband Router with instructions supplied by Linksys, or (c) has been subjected to abnormal physical or electrical stress, misuse, ...
User Guide
Page 81
...Increase the separation between the radiator and your body. IEEE 802.11b or 802.11g operation of this product near a swimming pool. Wireless-G Broadband Router with 2 Phone Ports Appendix I : Regulatory Information 74 This transmitter must accept any other than the receiver's • Consult a ... authority to provide reasonable protection against harmful interference in a particular installation. This product has been tested and complies with the specifications for example, in conjunction with Part 15 of electric shock from lightning. Do not use only No.26 AWG or larger...
...Increase the separation between the radiator and your body. IEEE 802.11b or 802.11g operation of this product near a swimming pool. Wireless-G Broadband Router with 2 Phone Ports Appendix I : Regulatory Information 74 This transmitter must accept any other than the receiver's • Consult a ... authority to provide reasonable protection against harmful interference in a particular installation. This product has been tested and complies with the specifications for example, in conjunction with Part 15 of electric shock from lightning. Do not use only No.26 AWG or larger...