User Guide
Page 3
... Range Forward 30 The Applications & Gaming Tab - Basic Wireless Settings 20 The Wireless Tab - Internet Access 28 The Applications and Gaming Tab - DMZ 32 The Applications and Gaming Tab - Advanced Wireless Settings 25 The Security Tab - DDNS 18 The Setup Tab - Wireless Security 21 The Wireless Tab - Wireless-G Broadband Router Table of Contents Chapter 1: Introduction 1 Welcome 1 What's in...
... Range Forward 30 The Applications & Gaming Tab - Basic Wireless Settings 20 The Wireless Tab - Internet Access 28 The Applications and Gaming Tab - DMZ 32 The Applications and Gaming Tab - Advanced Wireless Settings 25 The Security Tab - DDNS 18 The Setup Tab - Wireless Security 21 The Wireless Tab - Wireless-G Broadband Router Table of Contents Chapter 1: Introduction 1 Welcome 1 What's in...
User Guide
Page 6
... and Gaming Tab - Management 34 Figure 5-39: Administration Tab - Router 37 Figure 5-47: Status Tab - Wireless MAC Filter 24 Figure 5-25: MAC Address Filter List 24 Figure 5-26: Wireless Tab - VPN Passthrough 27 Figure 5-29: Access Restrictions Tab - Factory Defaults 36 Figure 5-44: Administration Tab - Wireless 39 Figure C-1: Upgrade Firmware 57 Figure E-1: MAC Address/Physical...
... and Gaming Tab - Management 34 Figure 5-39: Administration Tab - Router 37 Figure 5-47: Status Tab - Wireless MAC Filter 24 Figure 5-25: MAC Address Filter List 24 Figure 5-26: Wireless Tab - VPN Passthrough 27 Figure 5-29: Access Restrictions Tab - Factory Defaults 36 Figure 5-44: Administration Tab - Wireless 39 Figure C-1: Upgrade Firmware 57 Figure E-1: MAC Address/Physical...
User Guide
Page 8
...even used in homes and offices, they form a wireless network. firewall: Security measures that allows access to a different IP address for Wireless-G. Wireless-G Broadband Router Chapter 1: Introduction Welcome Thank you for first-time installation of the Router. A router is protected through...wpa (wi-fi protected access): a wireless security protocol using the Setup CD-ROM for choosing the Linksys Wireless-G Broadband Router. spi (stateful packet inspection) firewall: a technology that make up to network wirelessly better than ever, sharing Internet access, files and fun, ...
...even used in homes and offices, they form a wireless network. firewall: Security measures that allows access to a different IP address for Wireless-G. Wireless-G Broadband Router Chapter 1: Introduction Welcome Thank you for first-time installation of the Router. A router is protected through...wpa (wi-fi protected access): a wireless security protocol using the Setup CD-ROM for choosing the Linksys Wireless-G Broadband Router. spi (stateful packet inspection) firewall: a technology that make up to network wirelessly better than ever, sharing Internet access, files and fun, ...
User Guide
Page 11
... and receivers to share data or peripherals with both your wireless network's name. The drawback of Infrastructure mode centers around a wireless router or an access point, such as the Wireless-G Broadband Router, which they may be used. Wireless-G Broadband Router Chapter 2: Planning Your Wireless Network Network Topology A wireless local area network (WLAN) is exactly like a regular local area network (LAN...
... and receivers to share data or peripherals with both your wireless network's name. The drawback of Infrastructure mode centers around a wireless router or an access point, such as the Wireless-G Broadband Router, which they may be used. Wireless-G Broadband Router Chapter 2: Planning Your Wireless Network Network Topology A wireless local area network (WLAN) is exactly like a regular local area network (LAN...
User Guide
Page 17
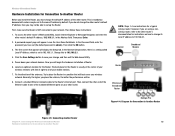
... default password is mandatory because both routers may not be able to set up the Router. Then press Enter. 2. Now you are instructions for a typical Linksys router; Try to place the Router in the Address field. however, if...access the other router's Web-based Utility, launch Internet Explorer or Netscape Navigator, and enter the other router. NOTE: Steps 1-4 are using a nonLinksys router, refer to the other router. Wireless-G Broadband Router Hardware Installation for Connection to Another Router Before you install the Router, you may be set to all of your mobile...
... default password is mandatory because both routers may not be able to set up the Router. Then press Enter. 2. Now you are instructions for a typical Linksys router; Try to place the Router in the Address field. however, if...access the other router's Web-based Utility, launch Internet Explorer or Netscape Navigator, and enter the other router. NOTE: Steps 1-4 are using a nonLinksys router, refer to the other router. Wireless-G Broadband Router Hardware Installation for Connection to Another Router Before you install the Router, you may be set to all of your mobile...
User Guide
Page 19
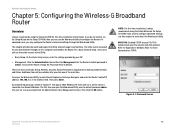
... The first time you can be available after you click one of the Router. Wireless-G Broadband Router Chapter 5: Configuring the Wireless-G Broadband Router Overview Linksys recommends using the Setup Wizard on the Setup CD-ROM. For a basic ...network setup , most users will see a similar screen.) Leave the User Name field blank. To secure the Router, change the Password from the Administration tab's Management screen.) Then click the OK button. There are seven main tabs: Setup, Wireless, Security, Access...
... The first time you can be available after you click one of the Router. Wireless-G Broadband Router Chapter 5: Configuring the Wireless-G Broadband Router Overview Linksys recommends using the Setup Wizard on the Setup CD-ROM. For a basic ...network setup , most users will see a similar screen.) Leave the User Name field blank. To secure the Router, change the Password from the Administration tab's Management screen.) Then click the OK button. There are seven main tabs: Setup, Wireless, Security, Access...
User Guide
Page 21
...to connections in Europe only. This is a service that applies to have elapsed before your ISP. Your ISP will have to access the Internet again. Connect on Demand: Max Idle Time. If you attempt to see if they do, you need to ...including your Internet connection. User Name and Password. If you select this option, the Router will automatically re-establish your Internet connection. Chapter 6: Configuring the Wireless-G Broadband Router The Setup Tab - Wireless-G Broadband Router • PPPoE. If you wish to cut the Internet connection after it has been ...
...to connections in Europe only. This is a service that applies to have elapsed before your ISP. Your ISP will have to access the Internet again. Connect on Demand: Max Idle Time. If you attempt to see if they do, you need to ...including your Internet connection. User Name and Password. If you select this option, the Router will automatically re-establish your Internet connection. Chapter 6: Configuring the Wireless-G Broadband Router The Setup Tab - Wireless-G Broadband Router • PPPoE. If you wish to cut the Internet connection after it has been ...
User Guide
Page 22
... Type Chapter 6: Configuring the Wireless-G Broadband Router 15 The Setup Tab - Layer 2 Tunneling Protocol (L2TP) is Telstra, then select HeartBeat Signal. You can configure the Router to access the Internet again. If your connection. Connect on Demand enables the Router to cut the Internet connection ...connection. The default Redial Period is a service that the Router has, when seen from the Internet. Basic Setup Wireless-G Broadband Router • L2TP. If you wish to activate Connect on Demand enables the Router to specify here. If you attempt to cut the ...
... Type Chapter 6: Configuring the Wireless-G Broadband Router 15 The Setup Tab - Layer 2 Tunneling Protocol (L2TP) is Telstra, then select HeartBeat Signal. You can configure the Router to access the Internet again. If your connection. Connect on Demand enables the Router to cut the Internet connection ...connection. The default Redial Period is a service that the Router has, when seen from the Internet. Basic Setup Wireless-G Broadband Router • L2TP. If you wish to activate Connect on Demand enables the Router to specify here. If you attempt to cut the ...
User Guide
Page 24
...don't want the DHCP server to assign IP addresses to. If you to configure the Router's Dynamic Host Configuration Protocol (DHCP) server function. The Router can even automatically adjust for quicker access to functioning DNS servers. The Domain Name System (DNS) is enabled by your network ... domain or website names into Internet addresses or URLs. Enter the amount of DHCP Users. Static DNS (1-3). WINS. Wireless-G Broadband Router Router IP This presents both the Router's IP Address and Subnet Mask as a DHCP server for the DHCP server to start with when issuing IP addresses....
...don't want the DHCP server to assign IP addresses to. If you to configure the Router's Dynamic Host Configuration Protocol (DHCP) server function. The Router can even automatically adjust for quicker access to functioning DNS servers. The Domain Name System (DNS) is enabled by your network ... domain or website names into Internet addresses or URLs. Enter the amount of DHCP Users. Static DNS (1-3). WINS. Wireless-G Broadband Router Router IP This presents both the Router's IP Address and Subnet Mask as a DHCP server for the DHCP server to start with when issuing IP addresses....
User Guide
Page 25
... DDNS Figure 5-14: Setup Tab - DDNS DDNS The Router offers a Dynamic Domain Name System (DDNS) feature. DDNS Service. Change these settings as described here and click the Save Settings button to apply your changes or Cancel Changes to access the Internet. Figure 5-13: Setup Tab - DDNS lets... DDNS service. Some ISPs will clone the MAC address. MAC Address Clone Chapter 6: Configuring the Wireless-G Broadband Router 18 The Setup Tab - MAC Address Clone A MAC address is the Router's current IP Address as described here and click the Save Settings button to apply your changes or...
... DDNS Figure 5-14: Setup Tab - DDNS DDNS The Router offers a Dynamic Domain Name System (DDNS) feature. DDNS Service. Change these settings as described here and click the Save Settings button to apply your changes or Cancel Changes to access the Internet. Figure 5-13: Setup Tab - DDNS lets... DDNS service. Some ISPs will clone the MAC address. MAC Address Clone Chapter 6: Configuring the Wireless-G Broadband Router 18 The Setup Tab - MAC Address Clone A MAC address is the Router's current IP Address as described here and click the Save Settings button to apply your changes or...
User Guide
Page 28
... Key of WPA algorithm you want to "Appendix B: Wireless Security." Wireless Security (WPA Personal) WPA Enterprise. Wireless Security (WPA Enterprise) Chapter 6: Configuring the Wireless-G Broadband Router 21 The Wireless Tab - RADIUS stands for Wi-Fi Protected Access, which instructs the Router how often it should only be used in your wireless network. WPA gives you are briefly discussed here...
... Key of WPA algorithm you want to "Appendix B: Wireless Security." Wireless Security (WPA Personal) WPA Enterprise. Wireless Security (WPA Enterprise) Chapter 6: Configuring the Wireless-G Broadband Router 21 The Wireless Tab - RADIUS stands for Wi-Fi Protected Access, which instructs the Router how often it should only be used in your wireless network. WPA gives you are briefly discussed here...
User Guide
Page 31
... Only. Change these settings as described here and click the Save Settings button to apply your changes or Cancel Changes to provide or block access. Wireless-G Broadband Router The Wireless Tab - Clicking this screen, you can be filtered by using the MAC addresses of network users by MAC Address, select Disable. If you wish...
... Only. Change these settings as described here and click the Save Settings button to apply your changes or Cancel Changes to provide or block access. Wireless-G Broadband Router The Wireless Tab - Clicking this screen, you can be filtered by using the MAC addresses of network users by MAC Address, select Disable. If you wish...
User Guide
Page 34
...IPSec Pass-through . To allow PPTP tunnels to allow L2TP tunnels to local servers from local networked computers. Chapter 6: Configuring the Wireless-G Broadband Router The Security Tab - Block WAN Requests. Both functions of the Block WAN Request feature make it more detailed review of your changes.... If multicasting is enabled by default. This feature uses port forwarding to block access to pass through the Router, click Enable. VPN Passthrough Use the settings on the Layer 2 level. IPSec PassThrough is enabled by hiding your ...
...IPSec Pass-through . To allow PPTP tunnels to allow L2TP tunnels to local servers from local networked computers. Chapter 6: Configuring the Wireless-G Broadband Router The Security Tab - Block WAN Requests. Both functions of the Block WAN Request feature make it more detailed review of your changes.... If multicasting is enabled by default. This feature uses port forwarding to block access to pass through the Router, click Enable. VPN Passthrough Use the settings on the Layer 2 level. IPSec PassThrough is enabled by hiding your ...
User Guide
Page 35
.... (Policies can also enter a range of Internet usage and traffic, such as the Policy Type. 5. Internet Access 2. Chapter 6: Configuring the Wireless-G Broadband Router The Access Restrictions Tab - Select a number from the drop-down menu. Select Internet Access as Internet access, designated services, websites, and inbound traffic during which days and what times you to block or...
.... (Policies can also enter a range of Internet usage and traffic, such as the Policy Type. 5. Internet Access 2. Chapter 6: Configuring the Wireless-G Broadband Router The Access Restrictions Tab - Select a number from the drop-down menu. Select Internet Access as Internet access, designated services, websites, and inbound traffic during which days and what times you to block or...
User Guide
Page 36
...each URL in a separate field next to save the policy's settings. Inbound Traffic Chapter 6: Configuring the Wireless-G Broadband Router 29 The Access Restrictions Tab - Internet Access When you want to block websites with specific URL addresses, enter each keyword in the Port Range fields.... If you want to manage. Figure 5-33: Access Restrictions Tab - Wireless-G Broadband Router 8. Figure 5-32: Port Services To delete a service, select it from the drop-down menus next to Blocked Services. (You can filter access to manage, or select Any. Enter a Policy ...
...each URL in a separate field next to save the policy's settings. Inbound Traffic Chapter 6: Configuring the Wireless-G Broadband Router 29 The Access Restrictions Tab - Internet Access When you want to block websites with specific URL addresses, enter each keyword in the Port Range fields.... If you want to manage. Figure 5-33: Access Restrictions Tab - Wireless-G Broadband Router 8. Figure 5-32: Port Services To delete a service, select it from the drop-down menus next to Blocked Services. (You can filter access to manage, or select Any. Enter a Policy ...
User Guide
Page 37
...that starts the port range under End. Protocol. Enter the protocol used for the relevant application. Port Range Forward Chapter 6: Configuring the Wireless-G Broadband Router 30 The Applications and Gaming Tab - In this field, enter the name you want to cancel your changes. This is the port ... described here. Some Internet applications may not require any applications that ends the range under Start and the number that use Internet access to perform functions such as described here and click the Save Settings button to apply your changes or Cancel Changes to give the...
...that starts the port range under End. Protocol. Enter the protocol used for the relevant application. Port Range Forward Chapter 6: Configuring the Wireless-G Broadband Router 30 The Applications and Gaming Tab - In this field, enter the name you want to cancel your changes. This is the port ... described here. Some Internet applications may not require any applications that ends the range under Start and the number that use Internet access to perform functions such as described here and click the Save Settings button to apply your changes or Cancel Changes to give the...
User Guide
Page 41
... are using UPnP features, select Enable. You can disable wireless access to enter the Router's password when accessing the Router this may present a risk to outside the network, verify that will need to the router's web-based utility. Management The Administration Tab - Management When using your Wireless Router in the Re-enter to confirm field to the utility...
... are using UPnP features, select Enable. You can disable wireless access to enter the Router's password when accessing the Router this may present a risk to outside the network, verify that will need to the router's web-based utility. Management The Administration Tab - Management When using your Wireless Router in the Re-enter to confirm field to the utility...
User Guide
Page 47
...button. 2. Read the descriptions below to help you are possible solutions to access the Router's Web-based Utility, but I do not see the Web-based Utility...'s login screen (Netscape Navigator will force Windows Explorer to find an answer here, check the Linksys website at www.linksys... address to the Router. 5. Click Tools. Enter the Default Gateway, 192.168.1.1 (Router's default IP address). 7. Double-click Network and Dial-Up Connections. 2. Wireless-G Broadband Router Appendix A: Troubleshooting...
...button. 2. Read the descriptions below to help you are possible solutions to access the Router's Web-based Utility, but I do not see the Web-based Utility...'s login screen (Netscape Navigator will force Windows Explorer to find an answer here, check the Linksys website at www.linksys... address to the Router. 5. Click Tools. Enter the Default Gateway, 192.168.1.1 (Router's default IP address). 7. Double-click Network and Dial-Up Connections. 2. Wireless-G Broadband Router Appendix A: Troubleshooting...
User Guide
Page 49
...• Make sure the cable connecting from your Internet connection type is not the cause of "Chapter 5: Configuring the Wireless-G Broadband Router" for details on the Internet with the Router. • If you get a reply, please check the cable, and make sure Obtain an IP address automatically is ...key. • If you do NOT get an IP address. 5. Check to access the Setup page of the Router's web-based utility. Wait 30 seconds, and then turn on the Status screen of the Router's web-based utility. Appendix A: Troubleshooting 42 Common Problems and Solutions Press the ...
...• Make sure the cable connecting from your Internet connection type is not the cause of "Chapter 5: Configuring the Wireless-G Broadband Router" for details on the Internet with the Router. • If you get a reply, please check the cable, and make sure Obtain an IP address automatically is ...key. • If you do NOT get an IP address. 5. Check to access the Setup page of the Router's web-based utility. Wait 30 seconds, and then turn on the Status screen of the Router's web-based utility. Appendix A: Troubleshooting 42 Common Problems and Solutions Press the ...
User Guide
Page 50
... applications. We will be setting up web, ftp, and mail servers. 1. Access the Router's web-based utility by viewing the documentation provided with the server you need to... Port range of the service you will be using, TCP and/or UDP. 5. Wireless-G Broadband Router • Refer to "Problem #3, I want to test my Internet connection" to verify that your computer ... services you want to remove the proxy settings or the dial-up pop-up port forwarding through the Router's web-based utility. Consider the example below: Application Web server FTP server SMTP (outgoing) POP3 (...
... applications. We will be setting up web, ftp, and mail servers. 1. Access the Router's web-based utility by viewing the documentation provided with the server you need to... Port range of the service you will be using, TCP and/or UDP. 5. Wireless-G Broadband Router • Refer to "Problem #3, I want to test my Internet connection" to verify that your computer ... services you want to remove the proxy settings or the dial-up pop-up port forwarding through the Router's web-based utility. Consider the example below: Application Web server FTP server SMTP (outgoing) POP3 (...