Security Guide
Page 2
... Notice. Table of Contents INTRODUCTION...3 PURPOSE...3 REFERENCES...3 DOCUMENT ORGANIZATION ...3 LEXMARK PRINTCRYPTIONTM 4 OVERVIEW...4 MODULE SPECIFICATION ...4 MODULE INTERFACES...7 ROLES AND SERVICES...9 Crypto Officer Role ...9 User Role...10 PHYSICAL SECURITY ...10 OPERATIONAL ENVIRONMENT ...10 CRYPTOGRAPHIC KEY MANAGEMENT 11 Access Control Policy ...12 Key Generation ...12 Key Storage ...12 Key Entry and Output...12 Key Zerorization...12 SELF-TESTS ...12 DESIGN ASSURANCE...14 MITIGATION OF OTHER ATTACKS 14 OPERATION IN FIPS MODE 15 INITIAL SETUP ...15...
... Notice. Table of Contents INTRODUCTION...3 PURPOSE...3 REFERENCES...3 DOCUMENT ORGANIZATION ...3 LEXMARK PRINTCRYPTIONTM 4 OVERVIEW...4 MODULE SPECIFICATION ...4 MODULE INTERFACES...7 ROLES AND SERVICES...9 Crypto Officer Role ...9 User Role...10 PHYSICAL SECURITY ...10 OPERATIONAL ENVIRONMENT ...10 CRYPTOGRAPHIC KEY MANAGEMENT 11 Access Control Policy ...12 Key Generation ...12 Key Storage ...12 Key Entry and Output...12 Key Zerorization...12 SELF-TESTS ...12 DESIGN ASSURANCE...14 MITIGATION OF OTHER ATTACKS 14 OPERATION IN FIPS MODE 15 INITIAL SETUP ...15...
Security Guide
Page 4
... shown in the printing industry. This document may be printed. Module Specification The version 1.3.2i PrintCryptionTM module is a firmware module composed of encrypted print jobs. The module is enabled in Lexmark printers using a Downloaded Emulator Card (DLE), a PCI interface PCB board that is the first of two binaries (aessd & dkmd) on the IBM750CL processor platform. With the PrintCryption module installed, the printer is capable of 20 ©...
... shown in the printing industry. This document may be printed. Module Specification The version 1.3.2i PrintCryptionTM module is a firmware module composed of encrypted print jobs. The module is enabled in Lexmark printers using a Downloaded Emulator Card (DLE), a PCI interface PCB board that is the first of two binaries (aessd & dkmd) on the IBM750CL processor platform. With the PrintCryption module installed, the printer is capable of 20 ©...
Security Guide
Page 8
... described in log file. This document may be freely reproduced and distributed whole and intact including this Copyright Notice. The status outputs of the module are logically distinct from the module includes X.509 certificate and deciphered data, which provide the only means of accessing the module's services. Control inputs are also data at TCP/IP port, however they are sent via network and...
... described in log file. This document may be freely reproduced and distributed whole and intact including this Copyright Notice. The status outputs of the module are logically distinct from the module includes X.509 certificate and deciphered data, which provide the only means of accessing the module's services. Control inputs are also data at TCP/IP port, however they are sent via network and...
Security Guide
Page 9
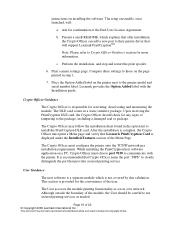
... Interfaces Roles and Services The module supports two roles, a Crypto Officer role and a User role, and an operator on demand Call a show status from the printer status Command Command Command Command Result of activation None Deactivated module Status output Status output None Integrity Check Key None Page 9 of the roles. Crypto Officer Role The Crypto Officer activates and deactivates the PrintCryption module by installing and removing the DLE card. Install...
... Interfaces Roles and Services The module supports two roles, a Crypto Officer role and a User role, and an operator on demand Call a show status from the printer status Command Command Command Command Result of activation None Deactivated module Status output Status output None Integrity Check Key None Page 9 of the roles. Crypto Officer Role The Crypto Officer activates and deactivates the PrintCryption module by installing and removing the DLE card. Install...
Security Guide
Page 10
... module. Encrypted print job at network port 9150. The PrintCryption module runs on Lexmark printers listed in the following table: Service Public Key request Secure Printing Description Input Output CSP Users request for business use). Crypto Officer Services, Descriptions, CSPs Type of Access to the EMI/EMC requirements specified by default. X.509 certificate Status output RSA public key RNG seed AES session key RSA private key Table 5 - The module runs on the Lexmark Linux v2.6 OS, and configured...
... module. Encrypted print job at network port 9150. The PrintCryption module runs on Lexmark printers listed in the following table: Service Public Key request Secure Printing Description Input Output CSP Users request for business use). Crypto Officer Services, Descriptions, CSPs Type of Access to the EMI/EMC requirements specified by default. X.509 certificate Status output RSA public key RNG seed AES session key RSA private key Table 5 - The module runs on the Lexmark Linux v2.6 OS, and configured...
Security Guide
Page 12
.... Self-Tests The PrintCryption module runs power-up self-tests are met. FIPS-Approved PRNG X9.31 Appendix A.2.4 is used to decrypt the data for AES Session key transport. Module startup occurs every time a new network connection is 1024 bits RSA key pair using key generation techniques that are entered into the module transported (encrypted) by Crypto-Officer "Run Self-Test" service. Firmware Integrity Check: The module employs a firmware integrity test in plaintext. Power-up...
.... Self-Tests The PrintCryption module runs power-up self-tests are met. FIPS-Approved PRNG X9.31 Appendix A.2.4 is used to decrypt the data for AES Session key transport. Module startup occurs every time a new network connection is 1024 bits RSA key pair using key generation techniques that are entered into the module transported (encrypted) by Crypto-Officer "Run Self-Test" service. Firmware Integrity Check: The module employs a firmware integrity test in plaintext. Power-up...
Security Guide
Page 14
...; Copyright 2009 Lexmark International Inc. This document may be freely reproduced and distributed whole and intact including this Copyright Notice. MLS is used to mitigate specific attacks. Design Assurance Source code and associated documentation files are always accessible. This software provides access control, versioning, and logging. Page 14 of Other Attacks The PrintCryption module does not employ security mechanisms to provide configuration management for the firmware module's FIPS documentation.
...; Copyright 2009 Lexmark International Inc. This document may be freely reproduced and distributed whole and intact including this Copyright Notice. MLS is used to mitigate specific attacks. Design Assurance Source code and associated documentation files are always accessible. This software provides access control, versioning, and logging. Page 14 of Other Attacks The PrintCryption module does not employ security mechanisms to provide configuration management for the firmware module's FIPS documentation.
Security Guide
Page 15
.... Initial Setup The DLE card containing PrintCryption activation code may be factory installed or user-installed. Installation procedure of the module is behind a firewall, it must allow IP ports 9150 and 9152 to place and keep the module in FIPS mode the Menu Settings Page must list "Lexmark PrintCryption Card" otherwise the FIPS module is not being used." 5. b. Configure the printer onto the TCP/IP network per installation requirements. Turn off the printer and install the card. If "Lexmark PrintCryption Card...
.... Initial Setup The DLE card containing PrintCryption activation code may be factory installed or user-installed. Installation procedure of the module is behind a firewall, it must allow IP ports 9150 and 9152 to place and keep the module in FIPS mode the Menu Settings Page must list "Lexmark PrintCryption Card" otherwise the FIPS module is not being used." 5. b. Configure the printer onto the TCP/IP network per installation requirements. Turn off the printer and install the card. If "Lexmark PrintCryption Card...
Security Guide
Page 16
... clearly distinguish the port that will : a. instructions on the printer next to the printer model and serial number label. This document may follow the installation sheet found in step 1. 7. The DLE card comes in a static sensitive package. Perform the installation, and stop and restart the print spooler. 6. Crypto Officer Guidance The Crypto Officer is not covered by this Copyright Notice. User Guidance The user software is...
... clearly distinguish the port that will : a. instructions on the printer next to the printer model and serial number label. This document may follow the installation sheet found in step 1. 7. The DLE card comes in a static sensitive package. Perform the installation, and stop and restart the print spooler. 6. Crypto Officer Guidance The Crypto Officer is not covered by this Copyright Notice. User Guidance The user software is...
Security Guide
Page 18
FIPS approved key and block sizes, and mode of operation are open. • The printer is installed. • The network path exists, even through a firewall, and when ping command does not work. • The proper IP ports (9150 and 9152) are as part of the install session. Setup.exe also installs the Lexmark PrintCryption Utility (LPCU) program as follows: • Key Length: 128, 192, or 256 bit. • Block Length...
FIPS approved key and block sizes, and mode of operation are open. • The printer is installed. • The network path exists, even through a firewall, and when ping command does not work. • The proper IP ports (9150 and 9152) are as part of the install session. Setup.exe also installs the Lexmark PrintCryption Utility (LPCU) program as follows: • Key Length: 128, 192, or 256 bit. • Block Length...
Security Target
Page 2
Table of Contents INTRODUCTION...3 PURPOSE...3 REFERENCES...3 DOCUMENT ORGANIZATION ...3 LEXMARK PRINTCRYPTIONTM 4 OVERVIEW...4 MODULE SPECIFICATION ...4 MODULE INTERFACES...6 ROLES AND SERVICES...7 Crypto Officer Role ...7 User Role...8 PHYSICAL SECURITY ...8 OPERATIONAL ENVIRONMENT ...9 CRYPTOGRAPHIC KEY MANAGEMENT 9 Access Control Policy ...10 Key Generation ...10 Key Storage ...10 Key Entry and Output...10 Key Zerorization...10 SELF-TESTS ...10 DESIGN ASSURANCE...11 MITIGATION OF OTHER ATTACKS 11 OPERATION IN FIPS MODE 12 INITIAL SETUP ...12 CRYPTO OFFICER GUIDANCE...13 USER GUIDANCE...
Table of Contents INTRODUCTION...3 PURPOSE...3 REFERENCES...3 DOCUMENT ORGANIZATION ...3 LEXMARK PRINTCRYPTIONTM 4 OVERVIEW...4 MODULE SPECIFICATION ...4 MODULE INTERFACES...6 ROLES AND SERVICES...7 Crypto Officer Role ...7 User Role...8 PHYSICAL SECURITY ...8 OPERATIONAL ENVIRONMENT ...9 CRYPTOGRAPHIC KEY MANAGEMENT 9 Access Control Policy ...10 Key Generation ...10 Key Storage ...10 Key Entry and Output...10 Key Zerorization...10 SELF-TESTS ...10 DESIGN ASSURANCE...11 MITIGATION OF OTHER ATTACKS 11 OPERATION IN FIPS MODE 12 INITIAL SETUP ...12 CRYPTO OFFICER GUIDANCE...13 USER GUIDANCE...
Security Target
Page 4
... industry. Module Specification The PrintCryptionTM module (firmware version 1.3.1) is a firmware module composed of its kind in Lexmark printers using a Downloaded Emulator Card (DLE), a serial interface PCB board that plugs into the printer. The module meets overall level 1 FIPS 140-2 requirements, as detailed in Figure 1. The Lexmark PrintCryptionTM analyses the encrypted data stream, determines if the correct key was used to encrypt the data, decrypts the data and allows the confidential document to be...
... industry. Module Specification The PrintCryptionTM module (firmware version 1.3.1) is a firmware module composed of its kind in Lexmark printers using a Downloaded Emulator Card (DLE), a serial interface PCB board that plugs into the printer. The module meets overall level 1 FIPS 140-2 requirements, as detailed in Figure 1. The Lexmark PrintCryptionTM analyses the encrypted data stream, determines if the correct key was used to encrypt the data, decrypts the data and allows the confidential document to be...
Security Target
Page 6
... printer ports include the network port, parallel port, USB port, paper exit port, multipurpose feeder, LED, and LCD display. All of these physical ports are logically distinct from the module includes X.509 certificate and deciphered data, which provide the only means of accessing the module's services. Control inputs are also data at TCP/IP port, however they are separated into logical interfaces defined by the hardware platforms listed above...
... printer ports include the network port, parallel port, USB port, paper exit port, multipurpose feeder, LED, and LCD display. All of these physical ports are logically distinct from the module includes X.509 certificate and deciphered data, which provide the only means of accessing the module's services. Control inputs are also data at TCP/IP port, however they are separated into logical interfaces defined by the hardware platforms listed above...
Security Target
Page 7
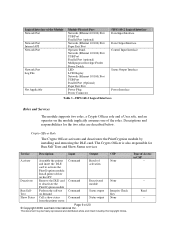
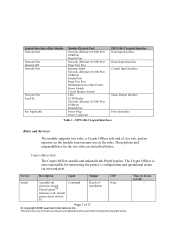
...(s); Type of the roles. Power Plug Power Connector FIPS 140-2 Logical Interface Data Input Interface Data Output Interface Control Input Interface Status Output Interface Power Interface Table 2 - FIPS 140-2 Logical Interfaces Roles and Services The module supports two roles, a Crypto Officer role and a User role, and an operator on host PC Command Result of installation None Page 7 of the Module Network Port Network Port Internal API Network Port Network Port Log File Not Applicable Module Physical Port Network (Ethernet 10/100) Port USB Port Parallel Port Network (Ethernet 10...
...(s); Type of the roles. Power Plug Power Connector FIPS 140-2 Logical Interface Data Input Interface Data Output Interface Control Input Interface Status Output Interface Power Interface Table 2 - FIPS 140-2 Logical Interfaces Roles and Services The module supports two roles, a Crypto Officer role and a User role, and an operator on host PC Command Result of installation None Page 7 of the Module Network Port Network Port Internal API Network Port Network Port Log File Not Applicable Module Physical Port Network (Ethernet 10/100) Port USB Port Parallel Port Network (Ethernet 10...
Security Target
Page 8
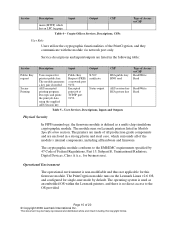
... log page Command Command Command Uninstalled None module Module setting None Status output Status output Integrity Check Key None Table 3 - Read -- The module generates a key pair if needed AES encrypted printing program; The printers are listed in the following table: Service Public Key request Secure Printing Role Input Output CSP Users request for business use as a multi-chip standalone cryptographic module. Encrypted print job at network port 9150. User Services, Descriptions, Inputs and Outputs Type of Access to CSP -- -- User...
... log page Command Command Command Uninstalled None module Module setting None Status output Status output Integrity Check Key None Table 3 - Read -- The module generates a key pair if needed AES encrypted printing program; The printers are listed in the following table: Service Public Key request Secure Printing Role Input Output CSP Users request for business use as a multi-chip standalone cryptographic module. Encrypted print job at network port 9150. User Services, Descriptions, Inputs and Outputs Type of Access to CSP -- -- User...
Security Target
Page 10
... entered into the module transported (encrypted) by overwriting the flash image with a new image. Page 10 of the module and imported via RSA key transport. Listing of Key and Critical Security Parameters Key transport Firmware Integrity test RNG Access Control Policy User functionalities have read by overwriting the flash image. RSA public key is 1024 bits RSA key pair using PKCS#1 key generation mechanism Externally generated, hard coded in the module 2-key TDES keys, 8 bytes of seed...
... entered into the module transported (encrypted) by overwriting the flash image with a new image. Page 10 of the module and imported via RSA key transport. Listing of Key and Critical Security Parameters Key transport Firmware Integrity test RNG Access Control Policy User functionalities have read by overwriting the flash image. RSA public key is 1024 bits RSA key pair using PKCS#1 key generation mechanism Externally generated, hard coded in the module 2-key TDES keys, 8 bytes of seed...
Security Target
Page 11
... history and older revisions are always accessible. Mitigation of HMAC SHA-1 over the three module binaries. Firmware Integrity Check: The module employs a firmware integrity test in the form of Other Attacks The PrintCryption module does not employ security mechanisms to provide configuration management for the firmware module's FIPS documentation. MLS is used to mitigate specific attacks. This software provides access control, versioning, and logging. This document may be freely reproduced and...
... history and older revisions are always accessible. Mitigation of HMAC SHA-1 over the three module binaries. Firmware Integrity Check: The module employs a firmware integrity test in the form of Other Attacks The PrintCryption module does not employ security mechanisms to provide configuration management for the firmware module's FIPS documentation. MLS is used to mitigate specific attacks. This software provides access control, versioning, and logging. This document may be freely reproduced and...
Security Target
Page 12
... and install the card. Page 12 of the module is behind a firewall, it must allow IP ports 9150 and 9152 to pass through . 2. Print a menu settings page from a printer: a. Configure the printer onto the TCP/IP network per installation requirements. This document may be freely reproduced and distributed whole and intact including this Copyright Notice. Lexmark provides an Installation sheet, a driver CD with publications, and license...
... and install the card. Page 12 of the module is behind a firewall, it must allow IP ports 9150 and 9152 to pass through . 2. Print a menu settings page from a printer: a. Configure the printer onto the TCP/IP network per installation requirements. This document may be freely reproduced and distributed whole and intact including this Copyright Notice. Lexmark provides an Installation sheet, a driver CD with publications, and license...
Security Target
Page 13
... the Installation guide. Upon receiving the PrintCryption card, the Crypto Officer should check for longer than 45 seconds, turn off the printer and reinstall the card. 4. The Crypto Officer must choose port 9150 to install the PrintCryption module. Page 13 of NVRAM for any signs of the End-User License Agreement. Print a menu settings page. Please refer to their printer driver that provides secured printing service. c. b. The...
... the Installation guide. Upon receiving the PrintCryption card, the Crypto Officer should check for longer than 45 seconds, turn off the printer and reinstall the card. 4. The Crypto Officer must choose port 9150 to install the PrintCryption module. Page 13 of NVRAM for any signs of the End-User License Agreement. Print a menu settings page. Please refer to their printer driver that provides secured printing service. c. b. The...
Security Target
Page 16
... can help Users to determine: • The Lexmark PrintCryption Card is installed. • The network path exists, even through a firewall, and when ping command does not work. • The proper IP ports (9150 and 9152) are open. • The printer is capable of returning an X.509 security certificate. • The printer can successfully decode an encrypted packet. Page 16 of the install session. PrintCryption Log Viewer Users can be...
... can help Users to determine: • The Lexmark PrintCryption Card is installed. • The network path exists, even through a firewall, and when ping command does not work. • The proper IP ports (9150 and 9152) are open. • The printer is capable of returning an X.509 security certificate. • The printer can successfully decode an encrypted packet. Page 16 of the install session. PrintCryption Log Viewer Users can be...