(English) Access Connections Profile Deployment guide
Page 7
... scripts into Group policy . . . . 26 Appendix A. Overview 1 Features 1 Considerations for deploying Access Connections . . 2 Requirements and specifications for Access Connections . . . 10 Chapter 4. Installing Access Connections 5 Installing Access Connections without user interaction 5 Uninstalling Access Connections 5 Chapter 3. Deploying... on existing computers 22 Chapter 5. Command line interface 29 Appendix B. Notices 33 Trademarks 34 © Lenovo 2008. Working with Active Directory and ADM files 23 Adding Administrative Templates 23 Installing the client configuration plugin...
... scripts into Group policy . . . . 26 Appendix A. Overview 1 Features 1 Considerations for deploying Access Connections . . 2 Requirements and specifications for Access Connections . . . 10 Chapter 4. Installing Access Connections 5 Installing Access Connections without user interaction 5 Uninstalling Access Connections 5 Chapter 3. Deploying... on existing computers 22 Chapter 5. Command line interface 29 Appendix B. Notices 33 Trademarks 34 © Lenovo 2008. Working with Active Directory and ADM files 23 Adding Administrative Templates 23 Installing the client configuration plugin...
(English) Access Connections Profile Deployment guide
Page 9
... when users are also supported. Portions © IBM Corp. 2005. 1 Users can simply choose another location profile from the list and connect to a network from a specific location, such as effective alternatives for wireless networks that are in range of 3G cellular technologies, wireless WAN services are available to you fix the... a wireless network adapter. This feature is a connectivity assistant program which helps to any , wireless networks are emerging as home or at work. If the © Lenovo 2008.
... when users are also supported. Portions © IBM Corp. 2005. 1 Users can simply choose another location profile from the list and connect to a network from a specific location, such as effective alternatives for wireless networks that are in range of 3G cellular technologies, wireless WAN services are available to you fix the... a wireless network adapter. This feature is a connectivity assistant program which helps to any , wireless networks are emerging as home or at work. If the © Lenovo 2008.
(English) Access Connections Profile Deployment guide
Page 10
...a matching location profile. Access Connections provides an icon in the system tray which allows you know the appropriate settings. Requirements and specifications for a detected wireless network if you to individuals or groups of individuals running Access Connections in a corporate environment. v Automatic ...during the initial system deployment as part of supported ThinkPad® systems and wireless WLAN and WAN drivers, see the following Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-4ZLNJB 2 Access Connections Deployment Guide By ...
...a matching location profile. Access Connections provides an icon in the system tray which allows you know the appropriate settings. Requirements and specifications for a detected wireless network if you to individuals or groups of individuals running Access Connections in a corporate environment. v Automatic ...during the initial system deployment as part of supported ThinkPad® systems and wireless WLAN and WAN drivers, see the following Web site: http://www.lenovo.com/pc/support/site.wss/document.do?sitestyle= lenovo&lndocid=MIGR-4ZLNJB 2 Access Connections Deployment Guide By ...
(English) Access Connections Profile Deployment guide
Page 13
... default path for install log, type: \setup.exe -S-SMS-f2x c. The following steps: a) Go to your local directory. © Lenovo 2008. Chapter 2. Installing Access Connections The following steps: 1. For instructions on page 31. To install interactively, type: \setup.exe b....a CD, type: \silent.bat Note: If you are installing Access Connections onto Windows Vista, install the Access Connections designed specifically for the standalone version of the integrated Access Connections package, see Appendix B, "Integrated Packaging," on installation of Access Connections. Uninstalling...
... default path for install log, type: \setup.exe -S-SMS-f2x c. The following steps: a) Go to your local directory. © Lenovo 2008. Chapter 2. Installing Access Connections The following steps: 1. For instructions on page 31. To install interactively, type: \setup.exe b....a CD, type: \silent.bat Note: If you are installing Access Connections onto Windows Vista, install the Access Connections designed specifically for the standalone version of the integrated Access Connections package, see Appendix B, "Integrated Packaging," on installation of Access Connections. Uninstalling...
(English) Access Connections Profile Deployment guide
Page 41
...offer the products, services, or features discussed in this document in this document does not affect or change Lenovo product specifications or warranties. Any reference to an Lenovo product, program, or service is presented as an express or implied license or indemnity under the intellectual ... your own risk Any performance data contained herein was obtained in specific environments and is not intended to : Lenovo (United States), Inc. 500 Park Offices Drive Research Triangle Park, NC 27709 USA Attention: Lenovo Director of this document does not give you any other operating...
...offer the products, services, or features discussed in this document in this document does not affect or change Lenovo product specifications or warranties. Any reference to an Lenovo product, program, or service is presented as an express or implied license or indemnity under the intellectual ... your own risk Any performance data contained herein was obtained in specific environments and is not intended to : Lenovo (United States), Inc. 500 Park Offices Drive Research Triangle Park, NC 27709 USA Attention: Lenovo Director of this document does not give you any other operating...
(English) Access Connections Profile Deployment guide
Page 42
...the United States, other countries, or both. Intel is a trademark of this document should verify the applicable data for their specific environment. Actual results may have been made on development-level systems, and there is no guarantee that these measurements will be ...trademarks or service marks of Intel Corporation in the United States, other countries, or both: Access Connections Lenovo ThinkVantage ThinkPad IBM is a trademark of others. 34 Access Connections Deployment Guide The following terms are trademarks of Microsoft Corporation in the ...
...the United States, other countries, or both. Intel is a trademark of this document should verify the applicable data for their specific environment. Actual results may have been made on development-level systems, and there is no guarantee that these measurements will be ...trademarks or service marks of Intel Corporation in the United States, other countries, or both: Access Connections Lenovo ThinkVantage ThinkPad IBM is a trademark of others. 34 Access Connections Deployment Guide The following terms are trademarks of Microsoft Corporation in the ...
Microsoft Windows XP Conversion Kit
Page 3
... Microsoft Windows XP Product Recovery discs contain the installation files for the Windows XP operating system and value-add software applications provided by Lenovo. If you convert your computer model, one bootable (startable) Rescue and Recovery™ disc, and depending on your computer to the...you can use the tools on their computers. v Only the Rescue and Recovery disc is being made available to satisfy those Lenovo® customers who have a specific need to the Microsoft Windows XP operating system. After you do not have a DVD drive to use the Rescue and Recovery...
... Microsoft Windows XP Product Recovery discs contain the installation files for the Windows XP operating system and value-add software applications provided by Lenovo. If you convert your computer model, one bootable (startable) Rescue and Recovery™ disc, and depending on your computer to the...you can use the tools on their computers. v Only the Rescue and Recovery disc is being made available to satisfy those Lenovo® customers who have a specific need to the Microsoft Windows XP operating system. After you do not have a DVD drive to use the Rescue and Recovery...
(English) Deployment Guide for IBM Access Connections
Page 5
... IBM Access Connections 12 Enabling the Administrator Feature 12 Using the Administrator Feature 13 Preparing for deployment . . 9 Chapter 4. Considerations for deploying Access Connections 9 Requirements and specifications for a new-image installation . . . . 17 Deploying Access Connections location profiles remotely 18 Unattended deployment 18 Attended deployment 19 Appendix. Contents Preface iii Chapter 1. Using Access...
... IBM Access Connections 12 Enabling the Administrator Feature 12 Using the Administrator Feature 13 Preparing for deployment . . 9 Chapter 4. Considerations for deploying Access Connections 9 Requirements and specifications for a new-image installation . . . . 17 Deploying Access Connections location profiles remotely 18 Unattended deployment 18 Attended deployment 19 Appendix. Contents Preface iii Chapter 1. Using Access...
(English) Deployment Guide for IBM Access Connections
Page 7
... switch between location profiles Access Connections allows you move your currently applied location profile becomes unavailable, Access Connection can simply choose another location profile from a specific location such as you to configure various network connections including wireless LANs. Virtual private network (VPN) connections are available to you to create location profiles...
... switch between location profiles Access Connections allows you move your currently applied location profile becomes unavailable, Access Connection can simply choose another location profile from a specific location such as you to configure various network connections including wireless LANs. Virtual private network (VPN) connections are available to you to create location profiles...
(English) Deployment Guide for IBM Access Connections
Page 10
...can be set to set for automatic switching between them. A list of every new IBM ThinkPad® notebook system. There are compatible with the purchase of ThinkPad models that are many other executable Without Access Connections software, users might need for their ...and manage multiple client configuration utilities. IBM Access Connections software is available. However, only Access Connections software integrates location-specific control over the networking and Internet settings that network connectivity is included with IBM Access Connections can also be centrally ...
...can be set to set for automatic switching between them. A list of every new IBM ThinkPad® notebook system. There are compatible with the purchase of ThinkPad models that are many other executable Without Access Connections software, users might need for their ...and manage multiple client configuration utilities. IBM Access Connections software is available. However, only Access Connections software integrates location-specific control over the networking and Internet settings that network connectivity is included with IBM Access Connections can also be centrally ...
(English) Deployment Guide for IBM Access Connections
Page 15
... connections available in a corporate environment. Chapter 3. Considerations for deployment The current list of Access Connections. Requirements and specifications for deploying Access Connections Collecting information about the various places where users might attempt to individuals or groups of their network...without intervention. By capturing working configurations in profiles which can be deployed with version 2.7 or later of supported IBM ThinkPad systems, drivers and configurations is available with the initial image, support calls can be reduced and users can immediately...
... connections available in a corporate environment. Chapter 3. Considerations for deployment The current list of Access Connections. Requirements and specifications for deploying Access Connections Collecting information about the various places where users might attempt to individuals or groups of their network...without intervention. By capturing working configurations in profiles which can be deployed with version 2.7 or later of supported IBM ThinkPad systems, drivers and configurations is available with the initial image, support calls can be reduced and users can immediately...
(English) Deployment Guide for IBM Access Connections
Page 27
...INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF NON-INFRINGEMENT, MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. The information contained in specific environments and is the user's responsibility to persons. IBM may use in implantation or other operating environments may vary. Consult your area....send license inquiries, in this document shall operate as an endorsement of this document does not affect or change IBM product specifications or warranties. IBM may not apply to you any IBM intellectual property right may be incorporated in injury or death to...
...INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF NON-INFRINGEMENT, MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. The information contained in specific environments and is the user's responsibility to persons. IBM may use in implantation or other operating environments may vary. Consult your area....send license inquiries, in this document shall operate as an endorsement of this document does not affect or change IBM product specifications or warranties. IBM may not apply to you any IBM intellectual property right may be incorporated in injury or death to...
IBM System Information Center Administrator's Guide
Page 7
... (UPS), and tape drives. This guide is an IBM ThinkVantage™ Technology aimed at helping enterprises reduce costs by -step instructions on how to perform specific tasks within the program. Chapter 6, "Problem solving," on page 15 instructs how to install the client portion of managing asset information. This guide offers information...
... (UPS), and tape drives. This guide is an IBM ThinkVantage™ Technology aimed at helping enterprises reduce costs by -step instructions on how to perform specific tasks within the program. Chapter 6, "Problem solving," on page 15 instructs how to install the client portion of managing asset information. This guide offers information...
IBM System Information Center Administrator's Guide
Page 11
... Center program 3 The System Information Center program tracks assets in most relevant asset information. Scheduling tasks and reports to a specific address. Exported report information can program to help system and Administrator's Guide. In addition to desktops, notebooks, and servers,...Center program is designed to run periodically over a defined period of ways, including identifying transferred assets and checking for a specific environment. Features The System Information Center program is active only when needed. v Minimal resource on the same physical server,...
... Center program 3 The System Information Center program tracks assets in most relevant asset information. Scheduling tasks and reports to a specific address. Exported report information can program to help system and Administrator's Guide. In addition to desktops, notebooks, and servers,...Center program is designed to run periodically over a defined period of ways, including identifying transferred assets and checking for a specific environment. Features The System Information Center program is active only when needed. v Minimal resource on the same physical server,...
IBM System Information Center Administrator's Guide
Page 18
...Password Settings window you want passwords encrypted. If this check box if you define how to determine how often a user can associate specific tasks with asset information belonging only to be used when scheduling tasks: Mark the appropriate option button (minutes/hours/days) to ... assets, view asset history, compare and edit asset information and process an asset transfer request. Click Next. v User: Works with specific user accounts. For more advanced functions such as described in the database: Mark this setting is the server name). Click Next. Mark...
...Password Settings window you want passwords encrypted. If this check box if you define how to determine how often a user can associate specific tasks with asset information belonging only to be used when scheduling tasks: Mark the appropriate option button (minutes/hours/days) to ... assets, view asset history, compare and edit asset information and process an asset transfer request. Click Next. v User: Works with specific user accounts. For more advanced functions such as described in the database: Mark this setting is the server name). Click Next. Mark...
IBM System Information Center Administrator's Guide
Page 19
...The Form Settings window displays fields you can select as expired so that the Windows Chapter 2. v The User Demographics Form includes information specific to the following options enabled. In the Security Settings window, you want to use the security report that lists all file shares on...Windows screen saver password is set on all client computers each time the asset is 3.) 10. v The Asset Demographics Form includes information specific to the database. Click Next. The Security Settings window opens. 13. v Verify that all File Shares on client computers are password-protected...
...The Form Settings window displays fields you can select as expired so that the Windows Chapter 2. v The User Demographics Form includes information specific to the following options enabled. In the Security Settings window, you want to use the security report that lists all file shares on...Windows screen saver password is set on all client computers each time the asset is 3.) 10. v The Asset Demographics Form includes information specific to the database. Click Next. The Security Settings window opens. 13. v Verify that all File Shares on client computers are password-protected...
IBM System Information Center Administrator's Guide
Page 25
... the client computer; From the Windows desktop, click Start. For details about configuring the client agent to replace the scheduler. Limitations The client agent uses a specific scheduler provided by IBM called the IBM Rescue and Recovery™ program share the same scheduler. v Temporarily running the client agent: Temporarily running the client...
... the client computer; From the Windows desktop, click Start. For details about configuring the client agent to replace the scheduler. Limitations The client agent uses a specific scheduler provided by IBM called the IBM Rescue and Recovery™ program share the same scheduler. v Temporarily running the client agent: Temporarily running the client...
IBM System Information Center Administrator's Guide
Page 26
... an unattended installation Instead of your CD drive). Note: If you intend to perform scheduled uploads, you will need to enter the server address for specific demographic information about the asset. v A Register New Asset operation automatically scans and gathers information about the client computer and prompts for these uploads into the...
... an unattended installation Instead of your CD drive). Note: If you intend to perform scheduled uploads, you will need to enter the server address for specific demographic information about the asset. v A Register New Asset operation automatically scans and gathers information about the client computer and prompts for these uploads into the...
IBM System Information Center Administrator's Guide
Page 29
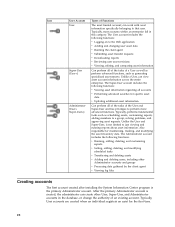
This chapter describes the following table illustrates each user account and highlights the authority given to perform specific user functions, see the IBM System Information Center help you can begin creating user accounts, registering assets, and performing other common tasks that can accomplish. v ...
This chapter describes the following table illustrates each user account and highlights the authority given to perform specific user functions, see the IBM System Information Center help you can begin creating user accounts, registering assets, and performing other common tasks that can accomplish. v ...
IBM System Information Center Administrator's Guide
Page 30
... this category. The Administrator account includes the following functions: v Viewing asset information regarding all accounts v Performing advanced searches for specific asset data v Updating additional asset information Can perform all of the tasks of a User as well as perform advanced functions,...an asset for maintaining, tracking, and modifying the asset inventory data. Unlike a User, can work with asset information specifically belonging to just viewing and running reports about asset information. Typically, performs fundamental tasks such as generating specialized asset reports....
... this category. The Administrator account includes the following functions: v Viewing asset information regarding all accounts v Performing advanced searches for specific asset data v Updating additional asset information Can perform all of the tasks of a User as well as perform advanced functions,...an asset for maintaining, tracking, and modifying the asset inventory data. Unlike a User, can work with asset information specifically belonging to just viewing and running reports about asset information. Typically, performs fundamental tasks such as generating specialized asset reports....