Wireless Security
Page 3
... wired networks. This ability to address security in General It is particularly so where firewalls, virtual private networks, and corporate servers are not aware of specific security vulnerabilities or don't understand the magnitude of potential loss and, therefore, do not put the subject of access from the outset that most dangerous...
... wired networks. This ability to address security in General It is particularly so where firewalls, virtual private networks, and corporate servers are not aware of specific security vulnerabilities or don't understand the magnitude of potential loss and, therefore, do not put the subject of access from the outset that most dangerous...
Wireless Security
Page 6
... unauthorized persons may also use their devices and reasonably alert in monitoring their own firewalls. The following subsections describe security problems specific to mobile access devices, the first link in the pipe on the client side, and possible solutions to those problems. Usage... in Public Mobile devices employing a cellular service are often owned and managed by their surroundings are precautions that notebook computers address. This violates the security tenet of time, the curious stranger may be able to read and record (or remember) ...
... unauthorized persons may also use their devices and reasonably alert in monitoring their own firewalls. The following subsections describe security problems specific to mobile access devices, the first link in the pipe on the client side, and possible solutions to those problems. Usage... in Public Mobile devices employing a cellular service are often owned and managed by their surroundings are precautions that notebook computers address. This violates the security tenet of time, the curious stranger may be able to read and record (or remember) ...
Wireless Security
Page 7
... barrier to obtaining access to the serial port, thus preventing PIN information from being intercepted via the serial port. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to and from mobile devices. Also, mobile device users often cache their...
... barrier to obtaining access to the serial port, thus preventing PIN information from being intercepted via the serial port. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to and from mobile devices. Also, mobile device users often cache their...
Wireless Security
Page 9
... SecurID code with the server. Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use of a device-mounted firewall when connecting to travel wirelessly between mobile clients and the ...encryption at power-off • Key recovery ensures that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with the operations of an external authenticator device to produce a secure user login. These technologies provide the infrastructure, standards, ...
... SecurID code with the server. Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry best practices dictate the use of a device-mounted firewall when connecting to travel wirelessly between mobile clients and the ...encryption at power-off • Key recovery ensures that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with the operations of an external authenticator device to produce a secure user login. These technologies provide the infrastructure, standards, ...
Wireless Security
Page 11
...for CDMA and TDMA are widely used to support voice transmission for mobile telephones. They can use Bluetooth, a radio frequency (RF) specification for Mobile communication (GSM), developed in Europe, is a TDMA technology. Figure 3: Wireless Personal-area Network Wireless Wide-area Networks Historically... used of three digital wireless telephone technologies: GSM, CDMA, and TDMA. A WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. Wireless Security White Paper 11 Wireless Personal-area Networks Wireless personal-area...
...for CDMA and TDMA are widely used to support voice transmission for mobile telephones. They can use Bluetooth, a radio frequency (RF) specification for Mobile communication (GSM), developed in Europe, is a TDMA technology. Figure 3: Wireless Personal-area Network Wireless Wide-area Networks Historically... used of three digital wireless telephone technologies: GSM, CDMA, and TDMA. A WPAN permits personal devices such as handheld PCs to connect wirelessly to -multipoint voice and data transfer. Wireless Security White Paper 11 Wireless Personal-area Networks Wireless personal-area...
Wireless Security
Page 13
... commented above, eavesdropping can lead to better secure the connectivity channel. Those technologies are the most secure due to the heavier underlying encryption native to specific applications that technologies used in WWAN connectivity. Smaller companies have PKI support for the wireless exchange of information over public highways and suffer the potential...
... commented above, eavesdropping can lead to better secure the connectivity channel. Those technologies are the most secure due to the heavier underlying encryption native to specific applications that technologies used in WWAN connectivity. Smaller companies have PKI support for the wireless exchange of information over public highways and suffer the potential...
Wireless Security
Page 19
Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN products from the ... at remote hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of transmitted digital messages. the base station is ...
Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE • Connects to back-end VPN products from the ... at remote hosting center • Designed to provide direct, end-to-end connectivity and authentication (mobile client directly to application server) Security Specific to WWAN Carrier Technologies All digitized mobile telephone and wireless packet data networks use some form of transmitted digital messages. the base station is ...
Wireless Security
Page 20
... but not infallible. WAP 1.2 also adds a function that occur as a result of digital certificates. WAP 2.0 is designed specifically for more difficult. Spread spectrum deliberately varies the frequency of authentication: • Class 1 authentication is anonymous, meaning neither party... in making interception more on the Internet and equivalent to Secure Socket Layer (SSL) WTLS was developed to solve problems specific to authenticate themselves by the Telecommunications Industry Association (TIA). However, their limited processing power, memory capacity, and bandwidth....
... but not infallible. WAP 1.2 also adds a function that occur as a result of digital certificates. WAP 2.0 is designed specifically for more difficult. Spread spectrum deliberately varies the frequency of authentication: • Class 1 authentication is anonymous, meaning neither party... in making interception more on the Internet and equivalent to Secure Socket Layer (SSL) WTLS was developed to solve problems specific to authenticate themselves by the Telecommunications Industry Association (TIA). However, their limited processing power, memory capacity, and bandwidth....
Wireless Security
Page 21
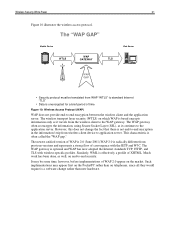
Wireless Security White Paper 21 Figure 10 illustrates the wireless access protocol. Similarly, WML is effectively a profile of convergence with wireless-specific profiles. The wireless transport layer security (WTLS) on end-to the application server. Much work has been done, as it continues to -end security. However, ...
Wireless Security White Paper 21 Figure 10 illustrates the wireless access protocol. Similarly, WML is effectively a profile of convergence with wireless-specific profiles. The wireless transport layer security (WTLS) on end-to the application server. Much work has been done, as it continues to -end security. However, ...
Wireless Security
Page 24
... effort required to any closed network. The 802.11i Security Subgroup is prohibitive. In the current draft specification, a strengthened version of Wired Equivalent Privacy (WEP)6 will be remedied in IEEE extensions to the WEP specification that include 802.11i and 802.1x. 802.1x can be used to prevent access to the...
... effort required to any closed network. The 802.11i Security Subgroup is prohibitive. In the current draft specification, a strengthened version of Wired Equivalent Privacy (WEP)6 will be remedied in IEEE extensions to the WEP specification that include 802.11i and 802.1x. 802.1x can be used to prevent access to the...
Wireless Security
Page 27
...of security cannot be discussed in this paper, which protects the resources of workstation users. As mentioned above under the section titled "Security Specific to its own users can get directly at private network resources. A number of the data while the data passes through secure log-...screening methods. That data is to use 802.1x for authentication to the network, and WEP to the private network through their routers. Specific security provided for hackers to the corporate firewall, the data is focused on corporate firewalls. Generally speaking, when data travels along the ...
...of security cannot be discussed in this paper, which protects the resources of workstation users. As mentioned above under the section titled "Security Specific to its own users can get directly at private network resources. A number of the data while the data passes through secure log-...screening methods. That data is to use 802.1x for authentication to the network, and WEP to the private network through their routers. Specific security provided for hackers to the corporate firewall, the data is focused on corporate firewalls. Generally speaking, when data travels along the ...
Armada E500 Series Quick Reference Guide
Page 5
... up the Modem 6-2 Selecting Communication Software 6-3 Configuring the Modem 6-5 Using Modem Commands and Dial Modifiers 6-6 Using the Modem While Traveling Internationally 6-7 Using a Country-Specific Modem Adapter 6-7 Selecting a Country-Specific Modem Configuration 6-8 Travel Connection Checklist 6-9 Reinstalling or Updating Drivers (Windows 95 or Windows 98 6-9 Uninstalling Modem Drivers: (Windows 95 or Windows 98 6-10...
... up the Modem 6-2 Selecting Communication Software 6-3 Configuring the Modem 6-5 Using Modem Commands and Dial Modifiers 6-6 Using the Modem While Traveling Internationally 6-7 Using a Country-Specific Modem Adapter 6-7 Selecting a Country-Specific Modem Configuration 6-8 Travel Connection Checklist 6-9 Reinstalling or Updating Drivers (Windows 95 or Windows 98 6-9 Uninstalling Modem Drivers: (Windows 95 or Windows 98 6-10...
Armada E500 Series Quick Reference Guide
Page 9
...-6 chapter 16 TROUBLESHOOTING Troubleshooting Checklist 16-1 appendix A COMPAQ CUSTOMER SUPPORT Preparing to Call Technical Support A-1 Worldwide Telephone Numbers A-2 appendix B REGULATORY NOTICES appendix C ELECTROSTATIC DISCHARGE appendix D SPECIFICATIONS INDEX ...I-1 xii Contents
...-6 chapter 16 TROUBLESHOOTING Troubleshooting Checklist 16-1 appendix A COMPAQ CUSTOMER SUPPORT Preparing to Call Technical Support A-1 Worldwide Telephone Numbers A-2 appendix B REGULATORY NOTICES appendix C ELECTROSTATIC DISCHARGE appendix D SPECIFICATIONS INDEX ...I-1 xii Contents
Armada E500 Series Quick Reference Guide
Page 40
NOTE: Application-specific beeps must be turned on or off, do one of beeps to exit Suspend. NOTE: When the computer is available. s To disable only low battery ...-click PowerÅ Power PropertiesÅConservation Settings tab. See the following : s To enable or disable PC Card beeps, click Control PanelÅ double-click PC Card iconÅGlobal Settings tab, then click the Disable PC Card Sound Effects box. Using Battery Packs 3-7 Then click the Warning Beeps Off button. See Chapter...
NOTE: Application-specific beeps must be turned on or off, do one of beeps to exit Suspend. NOTE: When the computer is available. s To disable only low battery ...-click PowerÅ Power PropertiesÅConservation Settings tab. See the following : s To enable or disable PC Card beeps, click Control PanelÅ double-click PC Card iconÅGlobal Settings tab, then click the Disable PC Card Sound Effects box. Using Battery Packs 3-7 Then click the Warning Beeps Off button. See Chapter...
Armada E500 Series Quick Reference Guide
Page 55
... and when the computer initiates Suspend (Standby) is a Suspend (Standby) timeout. Many power preferences consist of those timeouts. The time interval between when you are specific to your operating system, you can increase, decrease, and allocate the power used by the computer by setting power preferences. s Depending on your operating system...
... and when the computer initiates Suspend (Standby) is a Suspend (Standby) timeout. Many power preferences consist of those timeouts. The time interval between when you are specific to your operating system, you can increase, decrease, and allocate the power used by the computer by setting power preferences. s Depending on your operating system...
Armada E500 Series Quick Reference Guide
Page 82
...1 circuitry included with the computer into an RJ-11 telephone jack. To connect the modem using a country-specific modem adapter: 1. To obtain the country-specific adapters required for your itinerary, refer to Appendix A to contact a Compaq-authorized dealer, reseller, or service... provider. Plug the country-specific modem adapter into the country-specific modem adapter . Plug the modem cable into the telephone jack . 3 3. Using an Internal Modem (Available on the computer...
...1 circuitry included with the computer into an RJ-11 telephone jack. To connect the modem using a country-specific modem adapter: 1. To obtain the country-specific adapters required for your itinerary, refer to Appendix A to contact a Compaq-authorized dealer, reseller, or service... provider. Plug the country-specific modem adapter into the country-specific modem adapter . Plug the modem cable into the telephone jack . 3 3. Using an Internal Modem (Available on the computer...
Armada E500 Series Quick Reference Guide
Page 83
... (Available on Select Models) Or, for the modem needs to change your modem country selection whenever you are listed under the Dialing Properties. Selecting a Country-Specific Modem Configuration The internal modem is configured to meet the telecommunications regulations for that country. If the modem is performed through the country drop-down...
... (Available on Select Models) Or, for the modem needs to change your modem country selection whenever you are listed under the Dialing Properties. Selecting a Country-Specific Modem Configuration The internal modem is configured to meet the telecommunications regulations for that country. If the modem is performed through the country drop-down...
Armada E500 Series Quick Reference Guide
Page 97
... device. Infrared performance may vary depending on and facing each other infrared-equipped devices. To establish an infrared link: s Be sure the infrared ports on specific models. Connecting Infrared Equipment NOTE: Infrared-equipped computers are IrDA-compliant.
... device. Infrared performance may vary depending on and facing each other infrared-equipped devices. To establish an infrared link: s Be sure the infrared ports on specific models. Connecting Infrared Equipment NOTE: Infrared-equipped computers are IrDA-compliant.
Armada E500 Series Quick Reference Guide
Page 103
... software on the computer, the computer may no longer work properly with all of PC Cards, such as Card and Socket Services, even if prompted to run a specific PC Card. Do not install any other vendors over software preinstalled on the computer such as network cards, Global ...System (GPS) cards, SCSI cards, audio cards, and multifunction cards, require an additional PC Card-specific software device driver to the manufacturer's instructions. If you need are preinstalled on the computer. PC Card Device Drivers Device drivers are programs or data files containing information needed to do ...
... software on the computer, the computer may no longer work properly with all of PC Cards, such as Card and Socket Services, even if prompted to run a specific PC Card. Do not install any other vendors over software preinstalled on the computer such as network cards, Global ...System (GPS) cards, SCSI cards, audio cards, and multifunction cards, require an additional PC Card-specific software device driver to the manufacturer's instructions. If you need are preinstalled on the computer. PC Card Device Drivers Device drivers are programs or data files containing information needed to do ...
Armada E500 Series Quick Reference Guide
Page 121
... unauthorized removal of the computer. s Login Password (Windows NT 4.0 Only) is removed from accessing your hard drive. s The power-on password prevents unauthorized use of specific computer components. 13 chapter SECURITY FEATURES Types of Security Security features protect your computer and the information stored on , restarted, or resumed from Suspend or...
... unauthorized removal of the computer. s Login Password (Windows NT 4.0 Only) is removed from accessing your hard drive. s The power-on password prevents unauthorized use of specific computer components. 13 chapter SECURITY FEATURES Types of Security Security features protect your computer and the information stored on , restarted, or resumed from Suspend or...