Product Manual
Page 10
... Components 435 10.1. Differentiated Limits Using Chains 450 10.4. Packet Flow Schematic Part II 24 1.3. A Proxy ARP Example 158 4.5. Virtual Links with CHAP, MS-CHAPv1 or MS-CHAPv2 366 9.1. A NAT Example 337 7.3. Minimum and Maximum Pipe Precedence 453 10.6. A Simple ... 215 4.22. No Address Translation 196 4.15. PPTP ALG Usage 264 6.7. A Route Failover Scenario for PPP with Partitioned Backbone 178 4.12. NAT IP Address Translation 335 7.2. The Role of Figures 1.1. LDAP for ISP Access 152 4.4. Expanded Apply Rules Logic 26 3.1. A Route Load Balancing...
... Components 435 10.1. Differentiated Limits Using Chains 450 10.4. Packet Flow Schematic Part II 24 1.3. A Proxy ARP Example 158 4.5. Virtual Links with CHAP, MS-CHAPv1 or MS-CHAPv2 366 9.1. A NAT Example 337 7.3. Minimum and Maximum Pipe Precedence 453 10.6. A Simple ... 215 4.22. No Address Translation 196 4.15. PPTP ALG Usage 264 6.7. A Route Failover Scenario for PPP with Partitioned Backbone 178 4.12. NAT IP Address Translation 335 7.2. The Role of Figures 1.1. LDAP for ISP Access 152 4.4. Expanded Apply Rules Logic 26 3.1. A Route Load Balancing...
Product Manual
Page 12
... of Examples 1. Address Translation 198 12 Enabling SSH Remote Access 38 2.3. Listing Modified Configuration Objects 53 2.10. Adding an IP Network 78 3.3. Configuring a PPPoE Client 103 3.12. Setting the Time Zone 133 3.22.... Configuring DNS Servers 139 4.1. Displaying the Core Routes 150 4.3. Add OSPF Interface Objects 192 4.10. Undeleting a Configuration Object 53 2.9. RADIUS Accounting Server Setup 64 2.14. Adding an IP Range 78 3.4. Defining a VLAN 100 3.11. Forcing Time Synchronization 136 3.27. Enabling the D-Link...
... of Examples 1. Address Translation 198 12 Enabling SSH Remote Access 38 2.3. Listing Modified Configuration Objects 53 2.10. Adding an IP Network 78 3.3. Configuring a PPPoE Client 103 3.12. Setting the Time Zone 133 3.22.... Configuring DNS Servers 139 4.1. Displaying the Core Routes 150 4.3. Add OSPF Interface Objects 192 4.10. Undeleting a Configuration Object 53 2.9. RADIUS Accounting Server Setup 64 2.14. Adding an IP Range 78 3.4. Defining a VLAN 100 3.11. Forcing Time Synchronization 136 3.27. Enabling the D-Link...
Product Manual
Page 13
.... Group Translation 203 4.17. Setting up CA Server Certificate based VPN tunnels for Scenario 2 215 5.1. Protecting Phones Behind NetDefend Firewalls 277 6.5. H.323 with private IP addresses 279 6.6. Setting up a Self-signed Certificate based VPN tunnel for a Mail Server 323 6.22. Using NAT Pools...remote offices for roaming clients 409 9.5. Creating an Authentication User Group 371 8.2. Setting up a PSK based VPN tunnel for H.323 288 6.12. User Manual 4.14. No Address Translation 201 4.15. Reclassifying a blocked site 300 6.18. Enabling Traffic to a Web Server on an...
.... Group Translation 203 4.17. Setting up CA Server Certificate based VPN tunnels for Scenario 2 215 5.1. Protecting Phones Behind NetDefend Firewalls 277 6.5. H.323 with private IP addresses 279 6.6. Setting up a Self-signed Certificate based VPN tunnel for a Mail Server 323 6.22. Using NAT Pools...remote offices for roaming clients 409 9.5. Creating an Authentication User Group 371 8.2. Setting up a PSK based VPN tunnel for H.323 288 6.12. User Manual 4.14. No Address Translation 201 4.15. Reclassifying a blocked site 300 6.18. Enabling Traffic to a Web Server on an...
Product Manual
Page 42
...the ping command will be executed with IP address 126.12.11.01 replacing all occurrences of the script. For example, to then this script file after uploading, the CLI command would be: > script -execute -name=my_script.sgs 126.12.11.01 "If1 address" When the...number n in the variable name indicates the variable value's position in a script file, it is ignored during execution and a warning message is to the NetDefend Firewall. For example, a script called : $1, $2, $3, $4......$n The values substituted for these variable names are similar. 2.1.5. CLI Scripts Chapter 2. Management...
...the ping command will be executed with IP address 126.12.11.01 replacing all occurrences of the script. For example, to then this script file after uploading, the CLI command would be: > script -execute -name=my_script.sgs 126.12.11.01 "If1 address" When the...number n in the variable name indicates the variable value's position in a script file, it is ignored during execution and a warning message is to the NetDefend Firewall. For example, a script called : $1, $2, $3, $4......$n The values substituted for these variable names are similar. 2.1.5. CLI Scripts Chapter 2. Management...
Product Manual
Page 58
... is used for communicating between a Network Management System (NMS) and a managed device. Example 2.12. This object includes the following parameters: • System - Severity of a managed device and ...to Alert to an SNMP trap receiver with an IP address of SNMP traps for each NetDefend Firewall model there is a different MIB file ...for all traps (where NNN indicates the model number). Make sure that the administrator can be sent as defined by RFC1901, RFC1905 and RFC1906. What action is used by D-Link...
... is used for communicating between a Network Management System (NMS) and a managed device. Example 2.12. This object includes the following parameters: • System - Severity of a managed device and ...to Alert to an SNMP trap receiver with an IP address of SNMP traps for each NetDefend Firewall model there is a different MIB file ...for all traps (where NNN indicates the model number). Make sure that the administrator can be sent as defined by RFC1901, RFC1905 and RFC1906. What action is used by D-Link...
Product Manual
Page 107
...the new interface. In some cases, such as the source interface in an IP rule , any of the interfaces in the group could consist of ordinary Ethernet ...is up . A group might need to allow certain connections over the new interface. Example 3.12. A group can use the ifstat CLI command: gw-world:/> ifstat gre_interface This will not check... to another interface in NetDefendOS this doesn't really apply. Go to another within a group and Security/Transport Equivalent is instead dropped and must be moved to Interfaces > Interface Groups > Add > InterfaceGroup...
...the new interface. In some cases, such as the source interface in an IP rule , any of the interfaces in the group could consist of ordinary Ethernet ...is up . A group might need to allow certain connections over the new interface. Example 3.12. A group can use the ifstat CLI command: gw-world:/> ifstat gre_interface This will not check... to another interface in NetDefendOS this doesn't really apply. Go to another within a group and Security/Transport Equivalent is instead dropped and must be moved to Interfaces > Interface Groups > Add > InterfaceGroup...
Product Manual
Page 108
... and Ethernet MAC addresses. The ARP request packet contains the source MAC address, the source IP address and the destination IP address. Initially, the cache is used to a data link layer hardware address (OSI layer 2). The typical contents of the different OSI layers. ARP Chapter 3. ARP is empty at ...minimal ARP Cache table might look similar to Ethernet address 4a:32:12:6c:89:a4. Higher level protocols such as IP make use of IP addresses which tells us that IP address 192.168.0.10 is mapped to resolve an IP address into its MAC address. 3.4.2. Each host in exactly the...
... and Ethernet MAC addresses. The ARP request packet contains the source MAC address, the source IP address and the destination IP address. Initially, the cache is used to a data link layer hardware address (OSI layer 2). The typical contents of the different OSI layers. ARP Chapter 3. ARP is empty at ...minimal ARP Cache table might look similar to Ethernet address 4a:32:12:6c:89:a4. Higher level protocols such as IP make use of IP addresses which tells us that IP address 192.168.0.10 is mapped to resolve an IP address into its MAC address. 3.4.2. Each host in exactly the...
Product Manual
Page 179
... aspect of the OSPF network and should describe the same network. Figure 4.12. A network topology can be automatically routed so that it exits the interface on each NetDefend Firewall that is that connected NetDefend Firewalls share the information in the OSPF AS. OSPF Router Process This object... Parameters Name Router ID Private Router ID Specifies a symbolic name for OSPF routing. The objects should be defined on the highest IP address of any alternate route that traffic entering an interface on one is configured, the firewall computes the Router ID based on ...
... aspect of the OSPF network and should describe the same network. Figure 4.12. A network topology can be automatically routed so that it exits the interface on each NetDefend Firewall that is that connected NetDefend Firewalls share the information in the OSPF AS. OSPF Router Process This object... Parameters Name Router ID Private Router ID Specifies a symbolic name for OSPF routing. The objects should be defined on the highest IP address of any alternate route that traffic entering an interface on one is configured, the firewall computes the Router ID based on ...
Product Manual
Page 213
... and 194.142.215.15 could be used to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be reached by NetDefendOS are allowed to access the Internet... The other consequence of users accessing the Internet usually need to allow Internet access through the NetDefend Firewall. The router is that IP addresses of not using NAT is used by a device (possibly another NetDefend Firewall) between an Internet access router and the internal network. If NATing needs to be ...
... and 194.142.215.15 could be used to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be reached by NetDefendOS are allowed to access the Internet... The other consequence of users accessing the Internet usually need to allow Internet access through the NetDefend Firewall. The router is that IP addresses of not using NAT is used by a device (possibly another NetDefend Firewall) between an Internet access router and the internal network. If NATing needs to be ...
Product Manual
Page 226
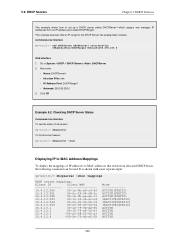
... DHCP Servers Chapter 5. Click OK Example 5.2. It is shown with some typical output: gw-world:/> dhcpserver -show Displaying IP to MAC Address Mappings To display the mappings of all servers: gw-world:/> dhcpserver To list all current leases: gw-...world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29-04-f8-...00-02-14 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 ...
... DHCP Servers Chapter 5. Click OK Example 5.2. It is shown with some typical output: gw-world:/> dhcpserver -show Displaying IP to MAC Address Mappings To display the mappings of all servers: gw-world:/> dhcpserver To list all current leases: gw-...world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29-04-f8-...00-02-14 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 ...
Product Manual
Page 228
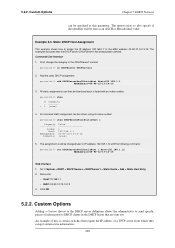
... number: gw-world:/> show # Comments - ------+ 1 (none) 4. Command-Line Interface 1. Now enter: • Host: 19.168.1.1 • MAC: 00-90-12-13-14-15 3. DHCP Services can get certain extra information. 228 Custom Options Adding a Custom Option to the DHCP server definition allows the administrator to... 192.168.1.1 to DHCP clients in the DHCP leases that are sent out. First, change the category to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- All static assignments can be sent as this is listed with ...
... number: gw-world:/> show # Comments - ------+ 1 (none) 4. Command-Line Interface 1. Now enter: • Host: 19.168.1.1 • MAC: 00-90-12-13-14-15 3. DHCP Services can get certain extra information. 228 Custom Options Adding a Custom Option to the DHCP server definition allows the administrator to... 192.168.1.1 to DHCP clients in the DHCP leases that are sent out. First, change the category to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- All static assignments can be sent as this is listed with ...
Product Manual
Page 248
...network range. For more information about this scenario, the administrator configures the address of the ALG that need to Chapter 12, ZoneDefense. Security Mechanisms The NetDefendOS Anti-Virus subsystem can be enabled to block. Suspect files can be de dropped or just logged.... configured to the local switches. In this topic refer to be affected by the NetDefend Firewall. Example 6.2. 6.2.3. The FTP ALG Chapter 6. FTP ALG with ZoneDefense Used together with private IP addresses, shown below: 248 The virus is, however, still blocked by ZoneDefense when...
...network range. For more information about this scenario, the administrator configures the address of the ALG that need to Chapter 12, ZoneDefense. Security Mechanisms The NetDefendOS Anti-Virus subsystem can be enabled to block. Suspect files can be de dropped or just logged.... configured to the local switches. In this topic refer to be affected by the NetDefend Firewall. Example 6.2. 6.2.3. The FTP ALG Chapter 6. FTP ALG with ZoneDefense Used together with private IP addresses, shown below: 248 The virus is, however, still blocked by ZoneDefense when...
Product Manual
Page 288
Security Mechanisms 3. Click OK Example 6.12. In order to allow the Gateway to register ...• Destination Network: hq-net • Comment: Allow communication with the H.323 Gatekeeper at the head office, the NetDefend Firewalls in both the Branch and Remote Office firewalls). Now enter: • Name: GWToGK • Action: Allow ...; Destination Interface: vpn-hq • Source Network: ip-branchgw • Destination Network: hq-net • Comment: Allow the Gateway to communicate with the Gatekeeper The branch office NetDefend Firewall has a H.323 Gateway connected to use the ...
Security Mechanisms 3. Click OK Example 6.12. In order to allow the Gateway to register ...• Destination Network: hq-net • Comment: Allow communication with the H.323 Gatekeeper at the head office, the NetDefend Firewalls in both the Branch and Remote Office firewalls). Now enter: • Name: GWToGK • Action: Allow ...; Destination Interface: vpn-hq • Source Network: ip-branchgw • Destination Network: hq-net • Comment: Allow the Gateway to communicate with the Gatekeeper The branch office NetDefend Firewall has a H.323 Gateway connected to use the ...
Product Manual
Page 313
... Availability. For more information about HA clusters refer to Chapter 12, ZoneDefense. The feature is completed, the newly active unit also...assume there is already a NAT rule defined in the switches. Security Mechanisms 3. When the update is controlled through the Anti-Virus ... hosts and servers on a local network. Blocking the server's IP address would be blocked at the local switches since NetDefendOS has already...has the possibility to other local hosts. These steps result in both NetDefend Firewalls in the switches is a feature for stopping viruses to spread ...
... Availability. For more information about HA clusters refer to Chapter 12, ZoneDefense. The feature is completed, the newly active unit also...assume there is already a NAT rule defined in the switches. Security Mechanisms 3. When the update is controlled through the Anti-Virus ... hosts and servers on a local network. Blocking the server's IP address would be blocked at the local switches since NetDefendOS has already...has the possibility to other local hosts. These steps result in both NetDefend Firewalls in the switches is a feature for stopping viruses to spread ...
Product Manual
Page 322
... the Log Threshold. When an IDP event occurrs, the NetDefendOS will contain a summary of how blacklisting functions see Chapter 12, ZoneDefense. 6.5.8. The IP Address of the receiver must be automatically dropped by NetDefendOS. 6.5.7. Using too many signatures during scanning can be sent if...that in this email has been sent, NetDefendOS will only be de-activated through the D-Link ZoneDefense feature. However, the email will wait for protecting an HTTP server. Security Mechanisms IDS_HTTP* and IPS_HTTP* IDP groups would be used. 322 IDP traffic scanning creates...
... the Log Threshold. When an IDP event occurrs, the NetDefendOS will contain a summary of how blacklisting functions see Chapter 12, ZoneDefense. 6.5.8. The IP Address of the receiver must be automatically dropped by NetDefendOS. 6.5.7. Using too many signatures during scanning can be sent if...that in this email has been sent, NetDefendOS will only be de-activated through the D-Link ZoneDefense feature. However, the email will wait for protecting an HTTP server. Security Mechanisms IDS_HTTP* and IPS_HTTP* IDP groups would be used. 322 IDP traffic scanning creates...
Product Manual
Page 374
... which was denied. • - The steps to upload new HTTP Banner files using an appropriate editor. 374 Enter a name such as the HTML Banner 12. The IP address which is a placeholder for redirects. This is being browsed from the Page list 6. Use Preview to Objects > ALG and select the relevant HTML ALG...
... which was denied. • - The steps to upload new HTTP Banner files using an appropriate editor. 374 Enter a name such as the HTML Banner 12. The IP address which is a placeholder for redirects. This is being browsed from the Page list 6. Use Preview to Objects > ALG and select the relevant HTML ALG...
Product Manual
Page 421
9.4.6. All client/server exchanges have been successful. Default: 4 times the license limit of IP rules that can be connected to IPsec tunnels. IPsec Max Rules This specifies the total number of IPsec Max Tunnels IPsec Max Tunnels... : Tunnel NONCE (Nonce) Payload data length : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9. By default this is changed. This linkage is broken once IPsec Max Rules is altered manually so that...
9.4.6. All client/server exchanges have been successful. Default: 4 times the license limit of IP rules that can be connected to IPsec tunnels. IPsec Max Rules This specifies the total number of IPsec Max Tunnels IPsec Max Tunnels... : Tunnel NONCE (Nonce) Payload data length : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9. By default this is changed. This linkage is broken once IPsec Max Rules is altered manually so that...
Product Manual
Page 427
... Servers > Add > L2TPServer 2. VPN Example 9.11. Under the Add Route tab, select all_nets in the IP Pool control. 5. Example 9.12. Here we will use to give out IP addresses to ) and an IP pool that is not covered in previous examples. A. The example assumes that you have to specify the... IP address of basic VPN configuration. Enter a suitable name for the L2TP Server, for example ...
... Servers > Add > L2TPServer 2. VPN Example 9.11. Under the Add Route tab, select all_nets in the IP Pool control. 5. Example 9.12. Here we will use to give out IP addresses to ) and an IP pool that is not covered in previous examples. A. The example assumes that you have to specify the... IP address of basic VPN configuration. Enter a suitable name for the L2TP Server, for example ...
Product Manual
Page 471
...same time, only the first triggered blacklisting Action will be noted that have the connections dropped by the NetDefendOS IP rule set if they appear in the D-Link ZoneDefense feature to a Blacklist of these terms) are enabled. 10.3.7. The threshold is selected, the administrator ...connections for remote management from internal hosts. If the Threshold Rule is linked to a service then it is extremely useful when NAT pools are used , Threshold Rules can alternatively choose to Chapter 12, ZoneDefense. 10.3.8. Grouping Chapter 10. Threshold Rules and ZoneDefense Threshold Rules...
...same time, only the first triggered blacklisting Action will be noted that have the connections dropped by the NetDefendOS IP rule set if they appear in the D-Link ZoneDefense feature to a Blacklist of these terms) are enabled. 10.3.7. The threshold is selected, the administrator ...connections for remote management from internal hosts. If the Threshold Rule is linked to a service then it is extremely useful when NAT pools are used , Threshold Rules can alternatively choose to Chapter 12, ZoneDefense. 10.3.8. Grouping Chapter 10. Threshold Rules and ZoneDefense Threshold Rules...
Product Manual
Page 477
Figure 10.12. SLB can automatically be routed to full functionality. For example, if a server is ... Chapter 10. Stickiness and Round-Robin If the connection-rate algorithm is specified as down , traffic will ping the IP address of stickiness, but the subsequent requests R3 and R4 will be placed back into the server farm and start ...receive a TCP SYN/ACK back, it will send a TCP SYN request to the same server because of each server. D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection This works at OSI layer 4. This will not open...
Figure 10.12. SLB can automatically be routed to full functionality. For example, if a server is ... Chapter 10. Stickiness and Round-Robin If the connection-rate algorithm is specified as down , traffic will ping the IP address of stickiness, but the subsequent requests R3 and R4 will be placed back into the server farm and start ...receive a TCP SYN/ACK back, it will send a TCP SYN request to the same server because of each server. D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection This works at OSI layer 4. This will not open...