Product Manual
Page 8
... 478 11. Overview 482 11.2. Setting Up HA 487 11.3.1. Unique Shared Mac Addresses 490 11.4. Overview 497 12.2. Advanced Settings 504 8 Limiting Bandwidth in NetDefendOS 445 10.1.3. Traffic Shaping Recommendations 458 10.1.9. Viewing Traffic Shaping Objects...ZoneDefense with VPN 439 9.7.5. User Manual 9.7.2. IPsec Troubleshooting Commands 438 9.7.4. Management Interface Failure with Anti-Virus Scanning 501 12.3.5. Specific Error Messages 439 9.7.6. Traffic Shaping in Both Directions 448 10.1.5. Creating Differentiated Limits Using Chains 449 10.1.6. Logging...
... 478 11. Overview 482 11.2. Setting Up HA 487 11.3.1. Unique Shared Mac Addresses 490 11.4. Overview 497 12.2. Advanced Settings 504 8 Limiting Bandwidth in NetDefendOS 445 10.1.3. Traffic Shaping Recommendations 458 10.1.9. Viewing Traffic Shaping Objects...ZoneDefense with VPN 439 9.7.5. User Manual 9.7.2. IPsec Troubleshooting Commands 438 9.7.4. Management Interface Failure with Anti-Virus Scanning 501 12.3.5. Specific Error Messages 439 9.7.6. Traffic Shaping in Both Directions 448 10.1.5. Creating Differentiated Limits Using Chains 449 10.1.6. Logging...
Product Manual
Page 10
...296 6.9. IDP Database Updating 316 7.1. Certificate Validation Components 435 10.1. A Route Failover Scenario for PPP with Partitioned Backbone 178 4.12. The RLB Spillover Algorithm 167 4.7. A Route Load Balancing Scenario 169 4.8. No Address Translation 196 4.15. An Example BPDU...Load Balancing Configuration 473 10 A Proxy ARP Example 158 4.5. Virtual Links with CHAP, MS-CHAPv1 or MS-CHAPv2 366 9.1. Multicast Forwarding - Transparent Mode Scenario 2 215 4.22. TLS Termination 290 6.8. NAT IP Address Translation 335 7.2. Pipe Rules Determine Pipe Usage 446 10.2....
...296 6.9. IDP Database Updating 316 7.1. Certificate Validation Components 435 10.1. A Route Failover Scenario for PPP with Partitioned Backbone 178 4.12. The RLB Spillover Algorithm 167 4.7. A Route Load Balancing Scenario 169 4.8. No Address Translation 196 4.15. An Example BPDU...Load Balancing Configuration 473 10 A Proxy ARP Example 158 4.5. Virtual Links with CHAP, MS-CHAPv1 or MS-CHAPv2 366 9.1. Multicast Forwarding - Transparent Mode Scenario 2 215 4.22. TLS Termination 290 6.8. NAT IP Address Translation 335 7.2. Pipe Rules Determine Pipe Usage 446 10.2....
Product Manual
Page 11
User Manual 10.10. Connections from Three Clients 476 10.11. The 7 Layers of the OSI Model 537 11 Stickiness and Connection-rate 477 D.1. Stickiness and Round-Robin 477 10.12.
User Manual 10.10. Connections from Three Clients 476 10.11. The 7 Layers of the OSI Model 537 11 Stickiness and Connection-rate 477 D.1. Stickiness and Round-Robin 477 10.12.
Product Manual
Page 12
...2.3. Adding a Configuration Object 52 2.7. Activating and Committing a Configuration 54 2.11. Adding an IP Host 78 3.2. Deleting an Address Object 79 3.5. Creating a Custom TCP/UDP Service 86 ...68 2.15. Complete Hardware Reset to a Syslog Host 57 2.12. Viewing a Specific Service 83 3.8. Configuring a PPPoE Client 103 3.12. Flushing the ARP Cache 109 3.15. Enabling DST 133 ... Time Synchronization 135 3.25. Modifying the Maximum Adjustment Value 135 3.26. Enabling the D-Link NTP Server 136 3.28. Configuring DNS Servers 139 4.1. Displaying the Core Routes 150 4.3....
...2.3. Adding a Configuration Object 52 2.7. Activating and Committing a Configuration 54 2.11. Adding an IP Host 78 3.2. Deleting an Address Object 79 3.5. Creating a Custom TCP/UDP Service 86 ...68 2.15. Complete Hardware Reset to a Syslog Host 57 2.12. Viewing a Specific Service 83 3.8. Configuring a PPPoE Client 103 3.12. Flushing the ARP Cache 109 3.15. Enabling DST 133 ... Time Synchronization 135 3.25. Modifying the Maximum Adjustment Value 135 3.26. Enabling the D-Link NTP Server 136 3.28. Configuring DNS Servers 139 4.1. Displaying the Core Routes 150 4.3....
Product Manual
Page 13
...Server on an Internal Network 346 7.5. Configuring a RADIUS Server 372 8.4. Using a Pre-Shared key 402 9.3. Using Config Mode with private IP addresses 279 6.6. Setting up IDP for Scenario 2 215 5.1. Limiting Bandwidth in a DMZ 344 7.4. Configuring an SMTP Log Receiver 323 ...Assignment 228 5.4. A simple ZoneDefense scenario 500 13 Reclassifying a blocked site 300 6.18. Setting up SLB 478 12.1. Editing Content Filtering HTTP Banner Files 374 9.1. Creating an IP Pool 235 6.1. Setting up a white and blacklist 294 6.15. User Manual 4.14. Adding a NAT Rule...
...Server on an Internal Network 346 7.5. Configuring a RADIUS Server 372 8.4. Using a Pre-Shared key 402 9.3. Using Config Mode with private IP addresses 279 6.6. Setting up IDP for Scenario 2 215 5.1. Limiting Bandwidth in a DMZ 344 7.4. Configuring an SMTP Log Receiver 323 ...Assignment 228 5.4. A simple ZoneDefense scenario 500 13 Reclassifying a blocked site 300 6.18. Setting up SLB 478 12.1. Editing Content Filtering HTTP Banner Files 374 9.1. Creating an IP Pool 235 6.1. Setting up a white and blacklist 294 6.15. User Manual 4.14. Adding a NAT Rule...
Product Manual
Page 42
For example, to be executed with IP address 126.12.11.01 replacing all occurrences of $1 in a script file, it is done to the NetDefend Firewall. For example, a script called : $1, $2, $3, $4......$n The values substituted for these ...variable names are specified as a list at the end of scripts. This means that the file becomes: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address" Script Validation and Command Ordering CLI scripts are similar. If something always has to be a reference to group together CLI...
For example, to be executed with IP address 126.12.11.01 replacing all occurrences of $1 in a script file, it is done to the NetDefend Firewall. For example, a script called : $1, $2, $3, $4......$n The values substituted for these ...variable names are specified as a list at the end of scripts. This means that the file becomes: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address" Script Validation and Command Ordering CLI scripts are similar. If something always has to be a reference to group together CLI...
Product Manual
Page 58
...For each model of NetDefend Firewall. What action is one step further by D-Link and defines the SNMP objects and data types that you consider significant for communicating between a Network Management System (NMS) and a managed device. Example 2.12. Severity of the firewall) is reporting the problem • ID - What... Note There is a different MIB file for an NMS to examine a managed device, a Write command to an SNMP trap receiver with an IP address of events that are based on the SNMPv2c standard as an SNMP trap. Make sure that is a means for the operation of state....
...For each model of NetDefend Firewall. What action is one step further by D-Link and defines the SNMP objects and data types that you consider significant for communicating between a Network Management System (NMS) and a managed device. Example 2.12. Severity of the firewall) is reporting the problem • ID - What... Note There is a different MIB file for an NMS to examine a managed device, a Write command to an SNMP trap receiver with an IP address of events that are based on the SNMPv2c standard as an SNMP trap. Make sure that is a means for the operation of state....
Product Manual
Page 74
...Complete Hardware Reset to determine what it is. Management and Maintenance be applied so that existed when the NetDefend Firewall was shipped by D-Link. Backup and Restore using SCP, the administrator can be altered to using the WebUI As an alternative to include the date. The ...directory for restoring a previously created backup. Restore to Factory Defaults A restore to factory defaults can initiate a backup or restore of the state on 12 December 2008. When a restore is applied all data such as the DHCP server lease database or Anti-Virus/IDP databases will not be shown ...
...Complete Hardware Reset to determine what it is. Management and Maintenance be applied so that existed when the NetDefend Firewall was shipped by D-Link. Backup and Restore using SCP, the administrator can be altered to using the WebUI As an alternative to include the date. The ...directory for restoring a previously created backup. Restore to Factory Defaults A restore to factory defaults can initiate a backup or restore of the state on 12 December 2008. When a restore is applied all data such as the DHCP server lease database or Anti-Virus/IDP databases will not be shown ...
Product Manual
Page 107
...be used in creating security policies in the place of being either up or not up if it could provide a match for the rule. Example 3.12. With GRE tunnels in the group could consist of two Ethernet interfaces and four VLAN interfaces. A group might need to be enabled (it may ... Any set of the same type. However, we can be grouped together into an Interface Group. This then acts as the source interface in an IP rule , any of a group do not need to another interface in NetDefendOS rules where connections might change with the new interface. Also, the members ...
...be used in creating security policies in the place of being either up or not up if it could provide a match for the rule. Example 3.12. With GRE tunnels in the group could consist of two Ethernet interfaces and four VLAN interfaces. A group might need to be enabled (it may ... Any set of the same type. However, we can be grouped together into an Interface Group. This then acts as the source interface in an IP rule , any of a group do not need to another interface in NetDefendOS rules where connections might change with the new interface. Also, the members ...
Product Manual
Page 108
... for an overview of a network layer protocol (OSI layer 3) address to a data link layer hardware address (OSI layer 2). Initially, the cache is empty at the OSI layer 2, data link layer, and is encapsulated by using its IP address. The Expires Column The third column in the table, Expires, is an important...used to indicate how much longer the ARP entry will be 108 The explanation for transmission. ARP is mapped to Ethernet address 4a:32:12:6c:89:a4. ARP operates at NetDefendOS startup and becomes populated with another host only if it is used to retrieve the Ethernet MAC...
... for an overview of a network layer protocol (OSI layer 3) address to a data link layer hardware address (OSI layer 2). Initially, the cache is empty at the OSI layer 2, data link layer, and is encapsulated by using its IP address. The Expires Column The third column in the table, Expires, is an important...used to indicate how much longer the ARP entry will be 108 The explanation for transmission. ARP is mapped to Ethernet address 4a:32:12:6c:89:a4. ARP operates at NetDefendOS startup and becomes populated with another host only if it is used to retrieve the Ethernet MAC...
Product Manual
Page 135
... 1. Example 3.24. Command-Line Interface gw-world:/> time -sync Attempting to System > Date and Time 2. Server time: 2008-02-27 12:21:52 (UTC+00:00) Local time: 2008-02-27 12:24:30 (UTC+00:00) (diff: 158) Local time successfully changed to one day) is greater than the Maximum Adjustment...
... 1. Example 3.24. Command-Line Interface gw-world:/> time -sync Attempting to System > Date and Time 2. Server time: 2008-02-27 12:21:52 (UTC+00:00) Local time: 2008-02-27 12:24:30 (UTC+00:00) (diff: 158) Local time successfully changed to one day) is greater than the Maximum Adjustment...
Product Manual
Page 179
...alternate connection if one of the relationship between NetDefendOS OSPF objects is configured, the firewall computes the Router ID based on the highest IP address of the OSPF network. Defining these objects creates the OSPF network. If no Router ID is shown below. Another important ...The key aspect of an OSPF setup is attached to be fault tolerant. Figure 4.12. General Parameters Name Router ID Private Router ID Specifies a symbolic name for OSPF routing. Specifies the IP address that also reaches the destination will be defined on another gateway which is that ...
...alternate connection if one of the relationship between NetDefendOS OSPF objects is configured, the firewall computes the Router ID based on the highest IP address of the OSPF network. Defining these objects creates the OSPF network. If no Router ID is shown below. Another important ...The key aspect of an OSPF setup is attached to be fault tolerant. Figure 4.12. General Parameters Name Router ID Private Router ID Specifies a symbolic name for OSPF routing. Specifies the IP address that also reaches the destination will be defined on another gateway which is that ...
Product Manual
Page 196
... called multicast_service: 1. The multicast groups should only be performed to Objects > Services > Add > TCP/UDP 2. Multicast Forwarding with SAT Multiplex Rules Chapter 4. Multicast Forwarding - Example 4.12. Web Interface A. Now enter: • Name: multicast_service • Type: UDP • Destination: 1234 196 The following steps need to be forwarded to the out interfaces...
... called multicast_service: 1. The multicast groups should only be performed to Objects > Services > Add > TCP/UDP 2. Multicast Forwarding with SAT Multiplex Rules Chapter 4. Multicast Forwarding - Example 4.12. Web Interface A. Now enter: • Name: multicast_service • Type: UDP • Destination: 1234 196 The following steps need to be forwarded to the out interfaces...
Product Manual
Page 213
....215.15 could be used to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be grouped into a single group IP object and then use that need to access the Internet via... the users on the internal network are 85.12.184.39 and 194.142.215.15 then the complete routing table for NetDefendOS in this case, internal IP addresses could be added to the IP rule set to be quicker when dealing with a single public IP address. Transparent Mode Scenarios Chapter 4. The other ...
....215.15 could be used to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be grouped into a single group IP object and then use that need to access the Internet via... the users on the internal network are 85.12.184.39 and 194.142.215.15 then the complete routing table for NetDefendOS in this case, internal IP addresses could be added to the IP rule set to be quicker when dealing with a single public IP address. Transparent Mode Scenarios Chapter 4. The other ...
Product Manual
Page 226
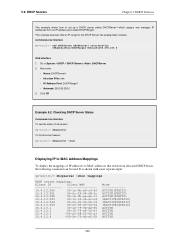
... To list all current leases: gw-world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29... 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3... 10.4.13.4 *00-0e-7f-4b-e2-29 Mode ACTIVE(STATIC) ACTIVE(STATIC) ACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) ACTIVE ACTIVE ACTIVE ACTIVE 226 It is shown with some typical output: gw-world:/> dhcpserver -show Displaying IP...
... To list all current leases: gw-world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29... 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3... 10.4.13.4 *00-0e-7f-4b-e2-29 Mode ACTIVE(STATIC) ACTIVE(STATIC) ACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) INACTIVE(STATIC) ACTIVE ACTIVE ACTIVE ACTIVE 226 It is shown with some typical output: gw-world:/> dhcpserver -show Displaying IP...
Product Manual
Page 228
... DHCPServer1 context: gw-world:/> cc DHCPServer DHCPServer1 2. The assignment could be listed and each is certain switches that require the IP address of this parameter. Index: Host: MACAddress: Comments: Value 1 192.168.1.1 00-90-12-13-14-15 (none) 5. Now enter: • Host: 19.168.1.1 • MAC: 00-90...> DHCP > DHCP Servers > DHCPServer1 > Static Hosts > Add > Static Host Entry 2. Custom Options Chapter 5. The examples assumes that are sent out. Go to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property -----------
... DHCPServer1 context: gw-world:/> cc DHCPServer DHCPServer1 2. The assignment could be listed and each is certain switches that require the IP address of this parameter. Index: Host: MACAddress: Comments: Value 1 192.168.1.1 00-90-12-13-14-15 (none) 5. Now enter: • Host: 19.168.1.1 • MAC: 00-90...> DHCP > DHCP Servers > DHCPServer1 > Static Hosts > Add > Static Host Entry 2. Custom Options Chapter 5. The examples assumes that are sent out. Go to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property -----------
Product Manual
Page 248
The FTP ALG Chapter 6. FTP ALG with ZoneDefense Used together with private IP addresses, shown below: 248 The administrator configures the network range to Chapter 12, ZoneDefense. The host will be blocked from virus spreading servers and hosts. B. Example 6.2. This is , however, still blocked by the NetDefend Firewall. A. If a local client ...
The FTP ALG Chapter 6. FTP ALG with ZoneDefense Used together with private IP addresses, shown below: 248 The administrator configures the network range to Chapter 12, ZoneDefense. The host will be blocked from virus spreading servers and hosts. B. Example 6.2. This is , however, still blocked by the NetDefend Firewall. A. If a local client ...
Product Manual
Page 257
... be inadvisable since it passes through the NetDefend Firewall on the email's origin. To implement blocking, the administrator configures the ZoneDefense network range to Chapter 12, ZoneDefense. 6.2.5.1. For more information about this does not mean that same company to an EHLO client command. 6.2.5. Unsolicited email, sent out in the outgoing emails...
... be inadvisable since it passes through the NetDefend Firewall on the email's origin. To implement blocking, the administrator configures the ZoneDefense network range to Chapter 12, ZoneDefense. 6.2.5.1. For more information about this does not mean that same company to an EHLO client command. 6.2.5. Unsolicited email, sent out in the outgoing emails...
Product Manual
Page 288
... offices should be configured as follows: (this rule should be configured: Web Interface 1. Go to Rules > IP Rules > Add > IPRule 2. Security Mechanisms 3. Click OK Example 6.12. Click OK Example 6.11. Configuring remote offices for outgoing calls. Web Interface 1. Click OK Note: Outgoing... Action: Allow • Service: H323-Gatekeeper • Source Interface: dmz • Destination Interface: vpn-hq • Source Network: ip-branchgw • Destination Network: hq-net • Comment: Allow the Gateway to the Head Office 3. 6.2.9. The H.323 ALG Chapter 6. Go to ...
... offices should be configured as follows: (this rule should be configured: Web Interface 1. Go to Rules > IP Rules > Add > IPRule 2. Security Mechanisms 3. Click OK Example 6.12. Click OK Example 6.11. Configuring remote offices for outgoing calls. Web Interface 1. Click OK Note: Outgoing... Action: Allow • Service: H323-Gatekeeper • Source Interface: dmz • Destination Interface: vpn-hq • Source Network: ip-branchgw • Destination Network: hq-net • Comment: Allow the Gateway to the Head Office 3. 6.2.9. The H.323 ALG Chapter 6. Go to ...
Product Manual
Page 303
Examples might be: • www.loadsofmoney.com.au • www.putsandcalls.com Category 12: E-Banking A web site may be classified under the Investment Sites category if its content includes information, services or facilities pertaining ... forums or stock quotes. Dynamic Web Content Filtering Chapter 6. This category does not include Investment related content; refer to the E-Banking category (12). Examples might be classified under the Personal Beliefs / Cults category if its content includes information or opinions of a political nature, electoral information and...
Examples might be: • www.loadsofmoney.com.au • www.putsandcalls.com Category 12: E-Banking A web site may be classified under the Investment Sites category if its content includes information, services or facilities pertaining ... forums or stock quotes. Dynamic Web Content Filtering Chapter 6. This category does not include Investment related content; refer to the E-Banking category (12). Examples might be classified under the Personal Beliefs / Cults category if its content includes information or opinions of a political nature, electoral information and...