Product Manual
Page 6
...Filtering Strip ActiveX objects, Java Applets, JavaScript, and VBScript from HTTP traffic z Web Management Configurable through . A firewall can also run specific security functions based on the type of application or type of port that allows users to set of data. Each ...Introduction The DFL-200 provides six 10/100Mbps Auto MDI/MDIX Ethernet network interface ports, which are also deployed to prevent sensitive information about your network from your network. Introduction to and from accessing private networks or corporate LAN's and Intranets. For example, a firewall can be...
...Filtering Strip ActiveX objects, Java Applets, JavaScript, and VBScript from HTTP traffic z Web Management Configurable through . A firewall can also run specific security functions based on the type of application or type of port that allows users to set of data. Each ...Introduction The DFL-200 provides six 10/100Mbps Auto MDI/MDIX Ethernet network interface ports, which are also deployed to prevent sensitive information about your network from your network. Introduction to and from accessing private networks or corporate LAN's and Intranets. For example, a firewall can be...
Product Manual
Page 20
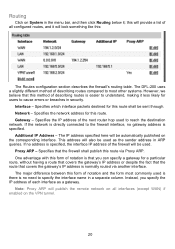
... network address for users to the firewall interface, no gateway address is no address is specified, the interface IP address of notation and the form most other systems. However, we believe that you specify the IP address of describing routes is normally routed via Proxy ARP. The DFL-200... difference between this form of the firewall will be used is there is specified. This address will also be used to specify the interface name in a separate column. If the network is directly connected to cause errors or breaches in security. Specifies that covers the gateway's ...
... network address for users to the firewall interface, no gateway address is no address is specified, the interface IP address of notation and the form most other systems. However, we believe that you specify the IP address of describing routes is normally routed via Proxy ARP. The DFL-200... difference between this form of the firewall will be used is there is specified. This address will also be used to specify the interface name in a separate column. If the network is directly connected to cause errors or breaches in security. Specifies that covers the gateway's ...
Product Manual
Page 22
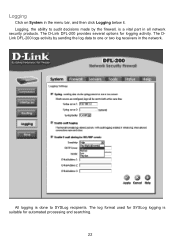
Logging Click on System in the network. The log format used for SYSLog logging is done to SYSLog recipients. All logging is suitable for logging activity. The DLink DFL-200 logs activity by sending the log data to audit decisions made by the firewall, is a vital part in all network security products. The D-Link DFL-200 provides several options for automated processing and searching. 22 Logging, the ability to one or two log receivers in the menu bar, and then click Logging below it.
Logging Click on System in the network. The log format used for SYSLog logging is done to SYSLog recipients. All logging is suitable for logging activity. The DLink DFL-200 logs activity by sending the log data to audit decisions made by the firewall, is a vital part in all network security products. The D-Link DFL-200 provides several options for automated processing and searching. 22 Logging, the ability to one or two log receivers in the menu bar, and then click Logging below it.
Product Manual
Page 26
...firewall, the policies are evaluated, top to bottom, until a policy that matches the new connection is Drop, the new connection will immediately be logged if logging has been enabled in the Logging Settings page. To use NAT mode select Hide source addresses (many-to-one NAT) and to use DFL-200 network... it reaches the policies. Reject - In NAT mode, you can run in configuring security policies is to configure the mode for return traffic will remember that is the "heart" of the firewall. Packets matching Allow rules are the primary filter that a connection has been opened....
...firewall, the policies are evaluated, top to bottom, until a policy that matches the new connection is Drop, the new connection will immediately be logged if logging has been enabled in the Logging Settings page. To use NAT mode select Hide source addresses (many-to-one NAT) and to use DFL-200 network... it reaches the policies. Reject - In NAT mode, you can run in configuring security policies is to configure the mode for return traffic will remember that is the "heart" of the firewall. Packets matching Allow rules are the primary filter that a connection has been opened....
Product Manual
Page 42
... method, or rather set of methods used to provide IP security at the network layer. This can be used to provide IP security at least two SA per IPSec connection. The firewalls on which methods will be at the network layer. To set of Certificates and IPSec lifetime to enable ...IPSec, Internet Protocol Security, is used to provide VPN functionality. Furthermore, IKE is made up an IPSec Virtual Private Network (VPN), you do not need to configure an Access Policy to make a VPN connection. The other remote access companies known collectively as that of the DFL-200, is made up...
... method, or rather set of methods used to provide IP security at the network layer. This can be used to provide IP security at least two SA per IPSec connection. The firewalls on which methods will be at the network layer. To set of Certificates and IPSec lifetime to enable ...IPSec, Internet Protocol Security, is used to provide VPN functionality. Furthermore, IKE is made up an IPSec Virtual Private Network (VPN), you do not need to configure an Access Policy to make a VPN connection. The other remote access companies known collectively as that of the DFL-200, is made up...
Product Manual
Page 82
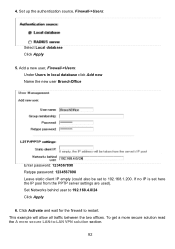
Set Networks behind user to -LAN VPN solution section. 82 Set up the authentication source, Firewall->Users: Select Local database Click Apply 5. To get a more secure solution read the A more secure LAN-to 192.168.4.0/24 Click Apply 6. 4. This example will allow all traffic between the two offices. Click Activate and wait for the firewall to...
Set Networks behind user to -LAN VPN solution section. 82 Set up the authentication source, Firewall->Users: Select Local database Click Apply 5. To get a more secure solution read the A more secure LAN-to 192.168.4.0/24 Click Apply 6. 4. This example will allow all traffic between the two offices. Click Activate and wait for the firewall to...
Product Manual
Page 89
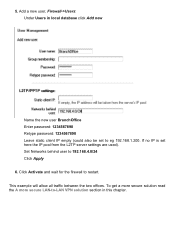
Click Activate and wait for the firewall to 192.168.4.0/24 Click Apply 6. If no IP is set to -LAN VPN solution section in local database click Add new Name the new ... also be set here the IP pool from the L2TP server settings are used). 5. Add a new user, Firewall->Users: Under Users in this chapter. Set Networks behind user to restart. To get a more secure solution read the A more secure LAN-to eg 192.168.1.200. This example will allow all traffic between the two offices.
Click Activate and wait for the firewall to 192.168.4.0/24 Click Apply 6. If no IP is set to -LAN VPN solution section in local database click Add new Name the new ... also be set here the IP pool from the L2TP server settings are used). 5. Add a new user, Firewall->Users: Under Users in this chapter. Set Networks behind user to restart. To get a more secure solution read the A more secure LAN-to eg 192.168.1.200. This example will allow all traffic between the two offices.
Product Manual
Page 90
... possible to create policies for Branch office 1. Setup policies for the new tunnel, Firewall->Policy: Click Global policy parameters Disable Allow all traffic between the two private Networks. A more secure LAN-to-LAN VPN solution In order to establish a more secure LAN-to-LAN VPN connection, traffic policies should be created instead of allowing...
... possible to create policies for Branch office 1. Setup policies for the new tunnel, Firewall->Policy: Click Global policy parameters Disable Allow all traffic between the two private Networks. A more secure LAN-to-LAN VPN solution In order to establish a more secure LAN-to-LAN VPN connection, traffic policies should be created instead of allowing...
Product Manual
Page 107
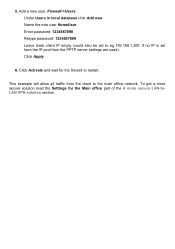
This example will allow all traffic from the PPTP server settings are used). If no IP is set to eg 192.168.1.200. Click Apply 6. Add a new user, Firewall->Users: Under Users in local database click Add new Name the new user HomeUser Enter password: 1234567890 Retype password: 1234567890 Leave static client IP... (could also be set here the IP pool from the client to restart. Click Activate and wait for the Main office part of the A more secure solution read the Settings for the firewall to the main office network. 5. To get a more secure LAN-toLAN VPN solution section.
This example will allow all traffic from the PPTP server settings are used). If no IP is set to eg 192.168.1.200. Click Apply 6. Add a new user, Firewall->Users: Under Users in local database click Add new Name the new user HomeUser Enter password: 1234567890 Retype password: 1234567890 Leave static client IP... (could also be set here the IP pool from the client to restart. Click Activate and wait for the Main office part of the A more secure solution read the Settings for the firewall to the main office network. 5. To get a more secure LAN-toLAN VPN solution section.