Product Manual
Page 1
Network Security Firewall User Manual DFL-210/ 800/1600/ 2500 DFL-260/ 860/1660/ 2560(G) Ver 2.27.01 SecurSiteycurity Network Security Solution http://www.dlink.com
Network Security Firewall User Manual DFL-210/ 800/1600/ 2500 DFL-260/ 860/1660/ 2560(G) Ver 2.27.01 SecurSiteycurity Network Security Solution http://www.dlink.com
Product Manual
Page 3
...NOT BE LIABLE FOR THIRD-PARTY CLAIMS AGAINST CUSTOMER FOR LOSSES OR DAMAGES. D-Link reserves the right to revise this publication and to make changes from time to time in this manual, nor any implied warranties of the material contained herein, may be reproduced without...is subject to the contents hereof and specifically disclaims any of merchantability or fitness for a particular purpose. Limitations of D-Link. User Manual DFL-210/260/800/860/1600/1660/2500/2560/2560G NetDefendOS Version 2.27.01 Published 2010-06-22 Copyright © 2010 Copyright Notice This publication, ...
...NOT BE LIABLE FOR THIRD-PARTY CLAIMS AGAINST CUSTOMER FOR LOSSES OR DAMAGES. D-Link reserves the right to revise this publication and to make changes from time to time in this manual, nor any implied warranties of the material contained herein, may be reproduced without...is subject to the contents hereof and specifically disclaims any of merchantability or fitness for a particular purpose. Limitations of D-Link. User Manual DFL-210/260/800/860/1600/1660/2500/2560/2560G NetDefendOS Version 2.27.01 Published 2010-06-22 Copyright © 2010 Copyright Notice This publication, ...
Product Manual
Page 5
User Manual 3.2.3. ICMP Services 86 3.2.4. Custom IP Protocol Services 88 3.2.5. GRE Tunnels 103 3.3.6. Using ARP Advanced Settings 112 3.4.5. Editing IP rule set Entries 120 3.5.5. Overview 132 3.8.2. Time ...
User Manual 3.2.3. ICMP Services 86 3.2.4. Custom IP Protocol Services 88 3.2.5. GRE Tunnels 103 3.3.6. Using ARP Advanced Settings 112 3.4.5. Editing IP rule set Entries 120 3.5.5. Overview 132 3.8.2. Time ...
Product Manual
Page 6
...Pools 233 6. ALGs 240 6.2.1. The Signature Database 311 6.4.5. Insertion/Evasion Attack Prevention 318 6.5.5. SMTP Log Receiver for D-Link Models 315 6.5.3. The Land and LaTierra attacks 327 6.6.6. Blacklisting Hosts and Networks 331 6 Custom Options 228 5.3. Security...Access Rules 237 6.1.1. The SMTP ALG 254 6.2.6. Amplification attacks: Smurf, Papasmurf, Fraggle 328 6.6.8. Overview 240 6.2.2. User Manual 4.7. Anti-Virus Options 311 6.5. Overview 326 6.6.2. Ping of -Service Attack Prevention 326 6.6.1. Static Content Filtering 293 6.3.4. Transparent ...
...Pools 233 6. ALGs 240 6.2.1. The Signature Database 311 6.4.5. Insertion/Evasion Attack Prevention 318 6.5.5. SMTP Log Receiver for D-Link Models 315 6.5.3. The Land and LaTierra attacks 327 6.6.6. Blacklisting Hosts and Networks 331 6 Custom Options 228 5.3. Security...Access Rules 237 6.1.1. The SMTP ALG 254 6.2.6. Amplification attacks: Smurf, Papasmurf, Fraggle 328 6.6.8. Overview 240 6.2.2. User Manual 4.7. Anti-Virus Options 311 6.5. Overview 326 6.6.2. Ping of -Service Attack Prevention 326 6.6.1. Static Content Filtering 293 6.3.4. Transparent ...
Product Manual
Page 7
User Manual 7. All-to LAN with Pre-shared Keys 408 9.4.3. Multiple SAT Rule Matches 351 7.4.7. Overview 355 8.2. HTTP Authentication 369 8.3. PPTP Roaming Clients 389 9.3. Overview 391 9.3.2. IKE ...
User Manual 7. All-to LAN with Pre-shared Keys 408 9.4.3. Multiple SAT Rule Matches 351 7.4.7. Overview 355 8.2. HTTP Authentication 369 8.3. PPTP Roaming Clients 389 9.3. Overview 391 9.3.2. IKE ...
Product Manual
Page 8
... Shaping 465 10.2.3. Logging 469 10.3. SLB Distribution Algorithms 474 10.4.3. SNMP 499 12.3.2. Threshold Rules 499 12.3.3. Manual Blocking and Exclude Lists 499 12.3.4. Limiting Bandwidth in NetDefendOS 445 10.1.3. More Pipe Examples 460 10.2. Guaranteeing Instead ...Rule Actions 471 10.3.5. SLB Algorithms and Stickiness 476 10.4.5. Overview 482 11.2. NetDefendOS Manual HA Setup 488 11.3.3. Multiple Triggered Actions 471 10.3.6. Limitations 501 13. User Manual 9.7.2. The Importance of Specifying a Network 466 10.2.5. HA Hardware Setup 487 11.3.2....
... Shaping 465 10.2.3. Logging 469 10.3. SLB Distribution Algorithms 474 10.4.3. SNMP 499 12.3.2. Threshold Rules 499 12.3.3. Manual Blocking and Exclude Lists 499 12.3.4. Limiting Bandwidth in NetDefendOS 445 10.1.3. More Pipe Examples 460 10.2. Guaranteeing Instead ...Rule Actions 471 10.3.5. SLB Algorithms and Stickiness 476 10.4.5. Overview 482 11.2. NetDefendOS Manual HA Setup 488 11.3.3. Multiple Triggered Actions 471 10.3.6. Limitations 501 13. User Manual 9.7.2. The Importance of Specifying a Network 466 10.2.5. HA Hardware Setup 487 11.3.2....
Product Manual
Page 9
State Settings 514 13.5. Verified MIME filetypes 533 D. IP Level Settings 504 13.2. Connection Timeout Settings 516 13.6. Local Fragment Reassembly Settings 524 13.9. IDP Signature Groups 529 C. ICMP Level Settings 513 13.4. Fragmentation Settings 520 13.8. Miscellaneous Settings 525 A. Subscribing to Updates 527 B. The OSI Framework 537 Alphabetical Index 538 9 Length Limit Settings 518 13.7. User Manual 13.1. TCP Level Settings 508 13.3.
State Settings 514 13.5. Verified MIME filetypes 533 D. IP Level Settings 504 13.2. Connection Timeout Settings 516 13.6. Local Fragment Reassembly Settings 524 13.9. IDP Signature Groups 529 C. ICMP Level Settings 513 13.4. Fragmentation Settings 520 13.8. Miscellaneous Settings 525 A. Subscribing to Updates 527 B. The OSI Framework 537 Alphabetical Index 538 9 Length Limit Settings 518 13.7. User Manual 13.1. TCP Level Settings 508 13.3.
Product Manual
Page 11
Connections from Three Clients 476 10.11. Stickiness and Round-Robin 477 10.12. Stickiness and Connection-rate 477 D.1. User Manual 10.10. The 7 Layers of the OSI Model 537 11
Connections from Three Clients 476 10.11. Stickiness and Round-Robin 477 10.12. Stickiness and Connection-rate 477 D.1. User Manual 10.10. The 7 Layers of the OSI Model 537 11
Product Manual
Page 12
... and Time 132 3.21. Enabling DST 133 3.23. Enabling Time Synchronization using the SAT Multiplex Rule 196 4.13. Enabling the D-Link NTP Server 136 3.28. Configuring DNS Servers 139 4.1. Forwarding of Examples 1. List of Multicast Traffic using SNTP 134 3.24. Undeleting... Routes from an OSPF AS into an OSPF AS 193 4.12. RADIUS Accounting Server Setup 64 2.14. Address Translation 198 12 Manually Triggering a Time Synchronization 135 3.25. Activating and Committing a Configuration 54 2.11. Adding an Ethernet Address 79 3.6. Listing Configuration ...
... and Time 132 3.21. Enabling DST 133 3.23. Enabling Time Synchronization using the SAT Multiplex Rule 196 4.13. Enabling the D-Link NTP Server 136 3.28. Configuring DNS Servers 139 4.1. Forwarding of Examples 1. List of Multicast Traffic using SNTP 134 3.24. Undeleting... Routes from an OSPF AS into an OSPF AS 193 4.12. RADIUS Accounting Server Setup 64 2.14. Address Translation 198 12 Manually Triggering a Time Synchronization 135 3.25. Activating and Committing a Configuration 54 2.11. Adding an Ethernet Address 79 3.6. Listing Configuration ...
Product Manual
Page 13
... register with private IP addresses 279 6.6. Using an Identity List 404 9.4. Setting up a Self-signed Certificate based VPN tunnel for a Mail Server 323 6.22. User Manual 4.14. H.323 with the Gatekeeper 288 6.13. Setting up an LDAP server 413 9.10.
... register with private IP addresses 279 6.6. Using an Identity List 404 9.4. Setting up a Self-signed Certificate based VPN tunnel for a Mail Server 323 6.22. User Manual 4.14. H.323 with the Gatekeeper 288 6.13. Setting up an LDAP server 413 9.10.
Product Manual
Page 14
... are largely textual descriptions of subjects. Where a "See chapter/section" link (such as appropriate. (The NetDefendOS CLI Reference Guide documents all CLI commands.) Example 1. This is deliberate and is done because the manual deals specifically with alphabetical lookup of management interface usage. They contain a CLI...text is broken down into chapters and sub-sections. An index is included at the beginning. It was decided that the manual would be clicked to take the reader directly to aid with NetDefendOS and administrators have a choice of screenshots. Command-Line ...
... are largely textual descriptions of subjects. Where a "See chapter/section" link (such as appropriate. (The NetDefendOS CLI Reference Guide documents all CLI commands.) Example 1. This is deliberate and is done because the manual deals specifically with alphabetical lookup of management interface usage. They contain a CLI...text is broken down into chapters and sub-sections. An index is included at the beginning. It was decided that the manual would be clicked to take the reader directly to aid with NetDefendOS and administrators have a choice of screenshots. Command-Line ...
Product Manual
Page 30
... anywhere on the workstation (the latest version of a Default IP Address For a new D-Link NetDefend firewall with factory defaults, a default internal IP address is 192.168.10.1. When ...The IP address assigned to the management interface differs according to the one shown below will then be manually given the following static IP values: • IP address: 192.168.1.30 • Subnet mask:... the default management interface IP address is 192.168.1.1. • On the NetDefend DFL-1660, 2560 and 2560G, the default management interface IP address is assigned automatically by NetDefendOS ...
... anywhere on the workstation (the latest version of a Default IP Address For a new D-Link NetDefend firewall with factory defaults, a default internal IP address is 192.168.10.1. When ...The IP address assigned to the management interface differs according to the one shown below will then be manually given the following static IP values: • IP address: 192.168.1.30 • Subnet mask:... the default management interface IP address is 192.168.1.1. • On the NetDefend DFL-1660, 2560 and 2560G, the default management interface IP address is assigned automatically by NetDefendOS ...
Product Manual
Page 32
... or restore a previously downloaded backup. • Reset - Provides various status pages that can be used to the configuration during the current session. • View Changes - Manually update or schedule updates of the configuration to download a file from the internal network. The tree is divided into three major sections: A. Interface Layout The...
... or restore a previously downloaded backup. • Reset - Provides various status pages that can be used to the configuration during the current session. • View Changes - Manually update or schedule updates of the configuration to download a file from the internal network. The tree is divided into three major sections: A. Interface Layout The...
Product Manual
Page 41
... per line. See also Section 2.1.4, "The CLI" in Section 2.1.6, "Secure Copy". 3. 2.1.5. Create a text file with a text editor containing a sequential list of the sessionmanager command. The D-Link recommended convention is discussed in detail in this manual. SCP uploading is for creating a CLI script are saved to run the script file.
... per line. See also Section 2.1.4, "The CLI" in Section 2.1.6, "Secure Copy". 3. 2.1.5. Create a text file with a text editor containing a sequential list of the sessionmanager command. The D-Link recommended convention is discussed in detail in this manual. SCP uploading is for creating a CLI script are saved to run the script file.
Product Manual
Page 102
... IP address allocation which is disconnected. The ISP does not assign an IP address to wait with any interface, one or more routes are then manually entered into client computers. As with no activity before the tunnel is used when ISPs want to allocate one or more preassigned IP addresses to...
... IP address allocation which is disconnected. The ISP does not assign an IP address to wait with any interface, one or more routes are then manually entered into client computers. As with no activity before the tunnel is used when ISPs want to allocate one or more preassigned IP addresses to...
Product Manual
Page 104
... Encapsulation Checksum The GRE protocol allows for the following: i. iii. The Session Key value is treated as a standard interface. The alternative is then used to manually create the required route. 104 3.3.5. ii. This option would normally be generated with the same filtering, traffic shaping and configuration capabilities as a logical interface by...
... Encapsulation Checksum The GRE protocol allows for the following: i. iii. The Session Key value is treated as a standard interface. The alternative is then used to manually create the required route. 104 3.3.5. ii. This option would normally be generated with the same filtering, traffic shaping and configuration capabilities as a logical interface by...
Product Manual
Page 109
... the expiration, NetDefendOS will probably have a new MAC address. The default value for the host in a network is 3 seconds. Example 3.13. The easiest way to manually force the update. After the ARP entry expiration time, NetDefendOS will learn the new MAC address of 45 which will never reach its destination. This...
... the expiration, NetDefendOS will probably have a new MAC address. The default value for the host in a network is 3 seconds. Example 3.13. The easiest way to manually force the update. After the ARP entry expiration time, NetDefendOS will learn the new MAC address of 45 which will never reach its destination. This...
Product Manual
Page 128
...128 A certification path refers to the path of an X.509 certificate hierarchy with public-key cryptography to sign other CAs. 3.7. It links an identity to a public key in order to establish whether a public key truly belongs to better manage security in a certificate ...also issue certificates to a certificate means a X.509 certificate. The CA certificate is with the ITU-T X.509 standard. By doing this manual to other certificates. This involves the use Pre-shared Keys (PSKs). Certificates Chapter 3. References in every certificate it issues. A certificate ...
...128 A certification path refers to the path of an X.509 certificate hierarchy with public-key cryptography to sign other CAs. 3.7. It links an identity to a public key in order to establish whether a public key truly belongs to better manage security in a certificate ...also issue certificates to a certificate means a X.509 certificate. The CA certificate is with the ITU-T X.509 standard. By doing this manual to other certificates. This involves the use Pre-shared Keys (PSKs). Certificates Chapter 3. References in every certificate it issues. A certificate ...
Product Manual
Page 129
... CRLs are set correctly when using certificates, NetDefendOS trusts anyone whose certificate is not valid forever. Whatever the reason, server CRLs can still be configured manually. Identification Lists In addition to verifying the signatures of the CRL has to change the validity of large user communities. When this interval depends on...
... CRLs are set correctly when using certificates, NetDefendOS trusts anyone whose certificate is not valid forever. Whatever the reason, server CRLs can still be configured manually. Identification Lists In addition to verifying the signatures of the CRL has to change the validity of large user communities. When this interval depends on...
Product Manual
Page 130
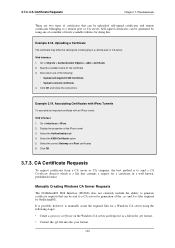
... Select the X509 Certificate option 5. CA Certificate Requests Chapter 3. Click OK and follow the instructions Example 3.19. Web Interface 1. Manually Creating Windows CA Server Requests The NetDefendOS Web Interface (WebUI) does not currently include the ability to generate certificate requests that can ... 2. Select the correct Gateway and Root certificates 6. It is possible, however, to send a CA Certificate Request which is to manually create the required files for the certificate 3. Fundamentals There are two types of the .cer and .key files required by using the...
... Select the X509 Certificate option 5. CA Certificate Requests Chapter 3. Click OK and follow the instructions Example 3.19. Web Interface 1. Manually Creating Windows CA Server Requests The NetDefendOS Web Interface (WebUI) does not currently include the ability to generate certificate requests that can ... 2. Select the correct Gateway and Root certificates 6. It is possible, however, to send a CA Certificate Request which is to manually create the required files for the certificate 3. Fundamentals There are two types of the .cer and .key files required by using the...