Software Guide
Page 8
... Up the Switch to Run SSH 8-35 Configuring the SSH Server 8-36 Displaying the SSH Configuration and Status 8-37 Configuring the Switch for Secure Socket Layer HTTP 8-37 Understanding Secure HTTP Servers and Clients 8-37 Certificate Authority Trustpoints 8-38 CipherSuites 8-39 Configuring Secure HTTP Servers and Clients 8-40 Default SSL Configuration...
... Up the Switch to Run SSH 8-35 Configuring the SSH Server 8-36 Displaying the SSH Configuration and Status 8-37 Configuring the Switch for Secure Socket Layer HTTP 8-37 Understanding Secure HTTP Servers and Clients 8-37 Certificate Authority Trustpoints 8-38 CipherSuites 8-39 Configuring Secure HTTP Servers and Clients 8-40 Default SSL Configuration...
Software Guide
Page 9
... 9-14 Using IEEE 802.1x Authentication with Wake-on-LAN 9-15 Using IEEE 802.1x Authentication with MAC Authentication Bypass 9-16 Using Network Admission Control Layer 2 IEEE 802.1x Validation 9-17 Using Web Authentication 9-17 Web Authentication with Automatic MAC Check 9-18 Configuring IEEE 802.1x Authentication 9-18 Default IEEE 802...
... 9-14 Using IEEE 802.1x Authentication with Wake-on-LAN 9-15 Using IEEE 802.1x Authentication with MAC Authentication Bypass 9-16 Using Network Admission Control Layer 2 IEEE 802.1x Validation 9-17 Using Web Authentication 9-17 Web Authentication with Automatic MAC Check 9-18 Configuring IEEE 802.1x Authentication 9-18 Default IEEE 802...
Software Guide
Page 10
Contents Configuring the Inaccessible Authentication Bypass Feature 9-33 Configuring IEEE 802.1x Authentication with WoL 9-35 Configuring MAC Authentication Bypass 9-36 Configuring NAC Layer 2 IEEE 802.1x Validation 9-37 Configuring Web Authentication 9-38 Disabling IEEE 802.1x Authentication on the Port 9-40 Resetting the IEEE 802.1x Authentication Configuration ...
Contents Configuring the Inaccessible Authentication Bypass Feature 9-33 Configuring IEEE 802.1x Authentication with WoL 9-35 Configuring MAC Authentication Bypass 9-36 Configuring NAC Layer 2 IEEE 802.1x Validation 9-37 Configuring Web Authentication 9-38 Disabling IEEE 802.1x Authentication on the Port 9-40 Resetting the IEEE 802.1x Authentication Configuration ...
Software Guide
Page 11
...11-2 Default Smartports Macro Configuration 11-2 Smartports Macro Configuration Guidelines 11-2 Creating Smartports Macros 11-4 Applying Smartports Macros 11-5 Applying Cisco-Default Smartports Macros 11-6 Displaying Smartports Macros 11-8 Configuring VLANs 12-1 Understanding VLANs 12-1 Supported VLANs 12-2 VLAN Port Membership...Displaying VLANs 12-13 Configuring VLAN Trunks 12-14 Trunking Overview 12-14 IEEE 802.1Q Configuration Considerations 12-15 Default Layer 2 Ethernet Interface VLAN Configuration 12-16 Configuring an Ethernet Interface as a Trunk Port 12-16 Interaction with Other Features...
...11-2 Default Smartports Macro Configuration 11-2 Smartports Macro Configuration Guidelines 11-2 Creating Smartports Macros 11-4 Applying Smartports Macros 11-5 Applying Cisco-Default Smartports Macros 11-6 Displaying Smartports Macros 11-8 Configuring VLANs 12-1 Understanding VLANs 12-1 Supported VLANs 12-2 VLAN Port Membership...Displaying VLANs 12-13 Configuring VLAN Trunks 12-14 Trunking Overview 12-14 IEEE 802.1Q Configuration Considerations 12-15 Default Layer 2 Ethernet Interface VLAN Configuration 12-16 Configuring an Ethernet Interface as a Trunk Port 12-16 Interaction with Other Features...
Software Guide
Page 23
... Other Features 31-6 EtherChannel On Mode 31-6 Load Balancing and Forwarding Methods 31-6 Configuring EtherChannels 31-8 Default EtherChannel Configuration 31-9 EtherChannel Configuration Guidelines 31-9 Configuring Layer 2 EtherChannels 31-10 Configuring EtherChannel Load Balancing 31-12 Configuring the PAgP Learn Method and Priority 31-13 Configuring LACP Hot-Standby Ports 31-14...
... Other Features 31-6 EtherChannel On Mode 31-6 Load Balancing and Forwarding Methods 31-6 Configuring EtherChannels 31-8 Default EtherChannel Configuration 31-9 EtherChannel Configuration Guidelines 31-9 Configuring Layer 2 EtherChannels 31-10 Configuring EtherChannel Load Balancing 31-12 Configuring the PAgP Learn Method and Priority 31-13 Configuring LACP Hot-Standby Ports 31-14...
Software Guide
Page 24
... and Identification 32-12 Monitoring SFP Module Status 32-12 Using Ping 32-12 Understanding Ping 32-13 Executing Ping 32-13 Using Layer 2 Traceroute 32-14 Understanding Layer 2 Traceroute 32-14 Usage Guidelines 32-14 Displaying the Physical Path 32-15 Using IP Traceroute 32-15 Understanding IP Traceroute 32-15...
... and Identification 32-12 Monitoring SFP Module Status 32-12 Using Ping 32-12 Understanding Ping 32-13 Executing Ping 32-13 Using Layer 2 Traceroute 32-14 Understanding Layer 2 Traceroute 32-14 Usage Guidelines 32-14 Displaying the Physical Path 32-15 Using IP Traceroute 32-15 Understanding IP Traceroute 32-15...
Software Guide
Page 35
... Port Aggregation Protocol (PAgP) and Link Aggregation Control Protocol (LACP) for automatic creation of EtherChannel links • Forwarding of Layer 2 packets at Gigabit line rate • Per-port storm control for preventing broadcast, multicast, and unicast storms • Port blocking on... system resources to maximize support for user-selected features • Cisco IOS IP Service Level Agreements (SLAs), a part of Cisco IOS software that uses active traffic monitoring for measuring network performance Support for Cisco IOS IP Service Level Agreements (SLAs) responder that is a ...
... Port Aggregation Protocol (PAgP) and Link Aggregation Control Protocol (LACP) for automatic creation of EtherChannel links • Forwarding of Layer 2 packets at Gigabit line rate • Per-port storm control for preventing broadcast, multicast, and unicast storms • Port blocking on... system resources to maximize support for user-selected features • Cisco IOS IP Service Level Agreements (SLAs), a part of Cisco IOS software that uses active traffic monitoring for measuring network performance Support for Cisco IOS IP Service Level Agreements (SLAs) responder that is a ...
Software Guide
Page 36
... mapping between the switch and other Cisco devices on Cisco.com. • CLI-The Cisco IOS software supports desktop- For more information about the CLI, see Getting Started with Cisco Network Assistant, available on the network • Link Layer Discovery Protocol (LLDP) and LLDP ...Media Endpoint Discovery (LLDP-MED) for interoperability with specific source or destination MAC addresses • Cisco Discovery Protocol (CDP) Versions 1 and ...
... mapping between the switch and other Cisco devices on Cisco.com. • CLI-The Cisco IOS software supports desktop- For more information about the CLI, see Getting Started with Cisco Network Assistant, available on the network • Link Layer Discovery Protocol (LLDP) and LLDP ...Media Endpoint Discovery (LLDP-MED) for interoperability with specific source or destination MAC addresses • Cisco Discovery Protocol (CDP) Versions 1 and ...
Software Guide
Page 38
... Tree Protocol (RSTP) for preventing switches outside the network core from becoming designated ports because of a failure that leads to a unidirectional link • Flex Link Layer 2 interfaces to back up one another as an alternative to 128 spanning-tree instances supported - Loop guard for preventing alternate or root ports from becoming...
... Tree Protocol (RSTP) for preventing switches outside the network core from becoming designated ports because of a failure that leads to a unidirectional link • Flex Link Layer 2 interfaces to back up one another as an alternative to 128 spanning-tree instances supported - Loop guard for preventing alternate or root ports from becoming...
Software Guide
Page 39
... traffic • Voice VLAN for creating subnets for voice traffic from connected hosts and servers, and to allow a supplicant (client) that carry upstream traffic from Cisco IP Phones • VLAN 1 minimization for reducing the risk of spanning-tree loops or storms by the IEEE 802.1Q standard • VLAN Query Protocol...) for negotiating trunking on a link between two devices and for limiting and identifying MAC addresses of interfaces configured as allowed by allowing VLAN 1 to provide Layer 2 redundancy without requiring Spanning Tree Protocol (STP).
... traffic • Voice VLAN for creating subnets for voice traffic from connected hosts and servers, and to allow a supplicant (client) that carry upstream traffic from Cisco IP Phones • VLAN 1 minimization for reducing the risk of spanning-tree loops or storms by the IEEE 802.1Q standard • VLAN Query Protocol...) for negotiating trunking on a link between two devices and for limiting and identifying MAC addresses of interfaces configured as allowed by allowing VLAN 1 to provide Layer 2 redundancy without requiring Spanning Tree Protocol (STP).
Software Guide
Page 40
... lists for defining security policies in the inbound direction on Layer 2 interfaces • Source and destination MAC-based ACLs for MDA to allow a dynamic voice VLAN on an MDA-enabled port - IEEE 802.1x accounting to detect and recognize a Cisco IP phone. - IEEE 802.1x with wake-on-LAN... to allow dormant PCs to be powered on based on the receipt of a specific Ethernet frame • MAC authentication bypass to authorize clients based on the client MAC address. • Network Admission Control (NAC) Layer 2 IEEE 802...
... lists for defining security policies in the inbound direction on Layer 2 interfaces • Source and destination MAC-based ACLs for MDA to allow a dynamic voice VLAN on an MDA-enabled port - IEEE 802.1x accounting to detect and recognize a Cisco IP phone. - IEEE 802.1x with wake-on-LAN... to allow dormant PCs to be powered on based on the receipt of a specific Ethernet frame • MAC authentication bypass to authorize clients based on the client MAC address. • Network Admission Control (NAC) Layer 2 IEEE 802...
Software Guide
Page 42
... enabled). If you have specific network needs, you do not configure the switch at all, the switch operates with Cisco Network Assistant, available on a network by using the CLI-based setup program, see the getting started guide. For...settings: • Default switch IP address, subnet mask, and default gateway is designed for tracking users on Cisco.com. 1-10 Catalyst 2960 Switch Software Configuration Guide OL-8603-04 If you can change the interface-specific...authorization errors, resource issues, and time-out events • Layer 2 traceroute to the other devices in your network.
... enabled). If you have specific network needs, you do not configure the switch at all, the switch operates with Cisco Network Assistant, available on a network by using the CLI-based setup program, see the getting started guide. For...settings: • Default switch IP address, subnet mask, and default gateway is designed for tracking users on Cisco.com. 1-10 Catalyst 2960 Switch Software Configuration Guide OL-8603-04 If you can change the interface-specific...authorization errors, resource issues, and time-out events • Layer 2 traceroute to the other devices in your network.
Software Guide
Page 43
... Chapter 6, "Administering the Switch." • DNS is enabled. For more information, see Chapter 8, "Configuring Switch-Based Authentication." • The standard HTTP server and Secure Socket Layer (SSL) HTTPS server are defined. Interface speed and duplex mode is server. For more information, see Chapter 10, "Configuring Interface Characteristics." • No Smartports macros...
... Chapter 6, "Administering the Switch." • DNS is enabled. For more information, see Chapter 8, "Configuring Switch-Based Authentication." • The standard HTTP server and Secure Socket Layer (SSL) HTTPS server are defined. Interface speed and duplex mode is server. For more information, see Chapter 10, "Configuring Interface Characteristics." • No Smartports macros...
Software Guide
Page 46
... Use switches that support at least two queues per port. • Use voice VLAN IDs (VVIDs) to a router in the distribution layer. The first illustration is of IP connectivity over existing infrastructure, such as either high- You can use QoS DSCP marking priorities on IEEE 802...data traffic as existing telephone lines. See the documentation sets specific to the desktop. To prevent congestion, use the Cisco Catalyst 2960 switches in the distribution layer. Using SFP modules also provides flexibility in the Catalyst 2900 LRE XL and Catalyst 2950 LRE switches. The switch ...
... Use switches that support at least two queues per port. • Use voice VLAN IDs (VVIDs) to a router in the distribution layer. The first illustration is of IP connectivity over existing infrastructure, such as either high- You can use QoS DSCP marking priorities on IEEE 802...data traffic as existing telephone lines. See the documentation sets specific to the desktop. To prevent congestion, use the Cisco Catalyst 2960 switches in the distribution layer. Using SFP modules also provides flexibility in the Catalyst 2900 LRE XL and Catalyst 2950 LRE switches. The switch ...
Software Guide
Page 47
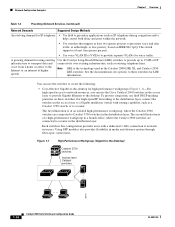
...OL-8603-04 Catalyst 2960 Switch Software Configuration Guide 1-15 For high-speed IP forwarding at the distribution layer, connect the switches in the access layer to interconnect groups of servers, centralizing physical security and administration of servers connected to the network core.... SFP module uplinks from the server racks to the core is achieved through fiber-optic connections. Chapter 1 Overview WAN Cisco 2600 router Access-layer Catalyst switches Network Configuration Examples 89374 • Server aggregation (Figure 1-2)-You can use the switches to multilayer switches with...
...OL-8603-04 Catalyst 2960 Switch Software Configuration Guide 1-15 For high-speed IP forwarding at the distribution layer, connect the switches in the access layer to interconnect groups of servers, centralizing physical security and administration of servers connected to the network core.... SFP module uplinks from the server racks to the core is achieved through fiber-optic connections. Chapter 1 Overview WAN Cisco 2600 router Access-layer Catalyst switches Network Configuration Examples 89374 • Server aggregation (Figure 1-2)-You can use the switches to multilayer switches with...
Software Guide
Page 48
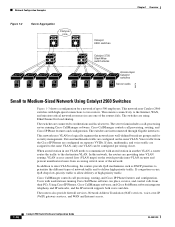
...interfaces. VLAN access control lists (VLAN maps) on separate VVIDs. Users with workstations running Cisco CallManager software. Using Cisco IP Phones, Cisco CallManager software, and Cisco SoftPhone software integrates telephony and IP networks, and the IP network supports both voice and ... StackWise switch stacks Access-layer Catalyst switches Server racks 89376 Small to Medium-Sized Network Using Catalyst 2960 Switches Figure 1-3 shows a configuration for a network of the routers fails. Cisco CallManager controls call processing, routing, and Cisco IP Phone features and ...
...interfaces. VLAN access control lists (VLAN maps) on separate VVIDs. Users with workstations running Cisco CallManager software. Using Cisco IP Phones, Cisco CallManager software, and Cisco SoftPhone software integrates telephony and IP networks, and the IP network supports both voice and ... StackWise switch stacks Access-layer Catalyst switches Server racks 89376 Small to Medium-Sized Network Using Catalyst 2960 Switches Figure 1-3 shows a configuration for a network of the routers fails. Cisco CallManager controls call processing, routing, and Cisco IP Phone features and ...
Software Guide
Page 50
Where to Go Next Chapter 1 Overview Figure 1-4 Long-Distance, High-Bandwidth Transport Configuration Access layer Aggregation layer 8 Gbps Catalyst switches CWDM OADM modules Eight 1-Gbps connections CWDM OADM modules Catalyst 4500 multilayer switches Where to Go Next Before configuring the switch, review these sections for startup information: • Chapter 2, "Using the Command-Line Interface" • Chapter 3, "Assigning the Switch IP Address and Default Gateway" 95750 1-18 Catalyst 2960 Switch Software Configuration Guide OL-8603-04
Where to Go Next Chapter 1 Overview Figure 1-4 Long-Distance, High-Bandwidth Transport Configuration Access layer Aggregation layer 8 Gbps Catalyst switches CWDM OADM modules Eight 1-Gbps connections CWDM OADM modules Catalyst 4500 multilayer switches Where to Go Next Before configuring the switch, review these sections for startup information: • Chapter 2, "Using the Command-Line Interface" • Chapter 3, "Assigning the Switch IP Address and Default Gateway" 95750 1-18 Catalyst 2960 Switch Software Configuration Guide OL-8603-04
Software Guide
Page 83
...Cisco IOS agent. Assuming there is no DHCP server on interface VLAN 1 (the default) and downloads the bootstrap configuration file from the TFTP server. Figure 4-2 Initial Configuration Overview Configuration Engine V WAN TFTP server DHCP server Distribution layer DHCP relay agent default gateway Access layer...assigns an IP address to the new switch and includes the TFTP server IP address, the path to the DHCP relay agent. The Cisco IOS agent feature supports the switch by providing these features: • Initial Configuration, page 4-5 • Incremental (Partial) Configuration, page...
...Cisco IOS agent. Assuming there is no DHCP server on interface VLAN 1 (the default) and downloads the bootstrap configuration file from the TFTP server. Figure 4-2 Initial Configuration Overview Configuration Engine V WAN TFTP server DHCP server Distribution layer DHCP relay agent default gateway Access layer...assigns an IP address to the new switch and includes the TFTP server IP address, the path to the DHCP relay agent. The Cisco IOS agent feature supports the switch by providing these features: • Initial Configuration, page 4-5 • Incremental (Partial) Configuration, page...
Software Guide
Page 92
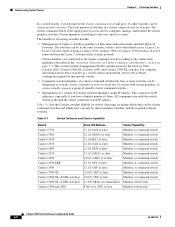
... clustering, including which ones can be cluster command switches and which ones can be cluster member switches. Cluster members can be designated as a Layer 3 router between the Layer 2 switches in the cluster) network. One or more switches can belong to configure, manage, and monitor the cluster member switches. Table 5-1...2950 Catalyst 2950 LRE Catalyst 2940 Catalyst 3500 XL Catalyst 2900 XL (8-MB switches) Catalyst 2900 XL (4-MB switches) Catalyst 1900 and 2820 Cisco IOS Release 12.1(11)AX or later 12.1(19)EA1b or later 12.1(4)EA1 or later 12.1(11)AX or later 12.2(25)FX ...
... clustering, including which ones can be cluster command switches and which ones can be cluster member switches. Cluster members can be designated as a Layer 3 router between the Layer 2 switches in the cluster) network. One or more switches can belong to configure, manage, and monitor the cluster member switches. Table 5-1...2950 Catalyst 2950 LRE Catalyst 2940 Catalyst 3500 XL Catalyst 2900 XL (8-MB switches) Catalyst 2900 XL (4-MB switches) Catalyst 1900 and 2820 Cisco IOS Release 12.1(11)AX or later 12.1(19)EA1b or later 12.1(4)EA1 or later 12.1(11)AX or later 12.2(25)FX ...
Software Guide
Page 98
... its default VLAN changes to the VLAN of the immediately upstream neighbor. Planning a Switch Cluster Chapter 5 Clustering Switches Figure 5-4 Discovery Through Different Management VLANs with a Layer 3 Cluster Command Switch Command device Standby command device VLAN 9 VLAN 16 Device 3 (management VLAN 16) VLAN 16 VLAN 62 Device 5 (management VLAN 62) VLAN trunk...
... its default VLAN changes to the VLAN of the immediately upstream neighbor. Planning a Switch Cluster Chapter 5 Clustering Switches Figure 5-4 Discovery Through Different Management VLANs with a Layer 3 Cluster Command Switch Command device Standby command device VLAN 9 VLAN 16 Device 3 (management VLAN 16) VLAN 16 VLAN 62 Device 5 (management VLAN 62) VLAN trunk...