Brochure
Page 1
...Internet Safe and secure wireless and Internet connections Linksys EasyLink Advisor (LELA) Get up and running wires The Linksys Wireless-G Broadband Router is a snap with up to 128-bit industrial-strength encryption. Surf, work, or play without running in the house. ...cable or DSL Internet connection. Utilize extra free space on a shared printer connected anywhere in minutes Wireless-G Broadband Router Model: WRT54G2 With the Linksys Wireless-G Broadband Router at 11Mbps) devices to fill up. Connect four PCs directly, or attach more hubs and switches to create as...
...Internet Safe and secure wireless and Internet connections Linksys EasyLink Advisor (LELA) Get up and running wires The Linksys Wireless-G Broadband Router is a snap with up to 128-bit industrial-strength encryption. Surf, work, or play without running in the house. ...cable or DSL Internet connection. Utilize extra free space on a shared printer connected anywhere in minutes Wireless-G Broadband Router Model: WRT54G2 With the Linksys Wireless-G Broadband Router at 11Mbps) devices to fill up. Connect four PCs directly, or attach more hubs and switches to create as...
Brochure
Page 2
...OS X 10.4 or Higher • Wired or Wireless Network Adapter Linksys A Division of Cisco Systems, Inc. 121 Theory Irvine, CA 92617 USA E-mail: [email protected] Web: ... their respective holders. 8062310A-JL Model: WRT54G2 and/or its affiliates in dBm UPnP able/cert Security Features Wireless Security Security Key Bits WRT54G2 IEEE 802.3, IEEE 802.3u, IEEE.... All rights reserved. Specifications are subject to 90%, Noncondensing Package Contents • Wireless-G Broadband Router • Setup Software and User Guide on many factors, conditions and variables, including distance from ...
...OS X 10.4 or Higher • Wired or Wireless Network Adapter Linksys A Division of Cisco Systems, Inc. 121 Theory Irvine, CA 92617 USA E-mail: [email protected] Web: ... their respective holders. 8062310A-JL Model: WRT54G2 and/or its affiliates in dBm UPnP able/cert Security Features Wireless Security Security Key Bits WRT54G2 IEEE 802.3, IEEE 802.3u, IEEE.... All rights reserved. Specifications are subject to 90%, Noncondensing Package Contents • Wireless-G Broadband Router • Setup Software and User Guide on many factors, conditions and variables, including distance from ...
User Manual
Page 2
Copyright © 2008 Cisco Systems, Inc. All rights reserved. WARNING: This exclamation point indicates that there is something that you should pay special attention to websites without adding the ... or registered trademarks of their respective holders. Online Resources Most web browsers allow you to add it is a registered trademark or trademark of Cisco Systems, Inc. Wireless-G Broadband Router About This Guide i Resource Website Linksys www.linksys.com Linksys International www.linksys.com/international Glossary www.linksys.com/glossary Network Security www...
Copyright © 2008 Cisco Systems, Inc. All rights reserved. WARNING: This exclamation point indicates that there is something that you should pay special attention to websites without adding the ... or registered trademarks of their respective holders. Online Resources Most web browsers allow you to add it is a registered trademark or trademark of Cisco Systems, Inc. Wireless-G Broadband Router About This Guide i Resource Website Linksys www.linksys.com Linksys International www.linksys.com/international Glossary www.linksys.com/glossary Network Security www...
User Manual
Page 3
... Gaming > QoS 18 Administration > Management 19 Administration > Log 20 Administration > Diagnostics 20 Administration > Factory Defaults 21 Administration > Upgrade Firmware 21 Administration > Config Management 21 Status > Router 22 Status > Local Network 22 Status > Wireless 23 Appendix A: Troubleshooting 24 Appendix B: Specifications 25 Appendix C: Warranty Information 26 Limited Warranty 26 Wireless-G Broadband...
... Gaming > QoS 18 Administration > Management 19 Administration > Log 20 Administration > Diagnostics 20 Administration > Factory Defaults 21 Administration > Upgrade Firmware 21 Administration > Config Management 21 Status > Router 22 Status > Local Network 22 Status > Wireless 23 Appendix A: Troubleshooting 24 Appendix B: Specifications 25 Appendix C: Warranty Information 26 Limited Warranty 26 Wireless-G Broadband...
User Manual
Page 4
Table of Contents Appendix D: Regulatory Information 28 FCC Statement 28 FCC Radiation Exposure Statement 28 Safety Notices 28 Industry Canada Statement 28 Avis d'Industrie Canada 29 Wireless Disclaimer 29 Avis de non-responsabilité concernant les appareils sans fil 29 User Information for Consumer Products Covered by EU Directive 2002/96/EC on Waste Electric and Electronic Equipment (WEEE 30 Appendix E: Software License Agreement 34 Software in Linksys Products 34 Software Licenses 34 Wireless-G Broadband Router iii
Table of Contents Appendix D: Regulatory Information 28 FCC Statement 28 FCC Radiation Exposure Statement 28 Safety Notices 28 Industry Canada Statement 28 Avis d'Industrie Canada 29 Wireless Disclaimer 29 Avis de non-responsabilité concernant les appareils sans fil 29 User Information for Consumer Products Covered by EU Directive 2002/96/EC on Waste Electric and Electronic Equipment (WEEE 30 Appendix E: Software License Agreement 34 Software in Linksys Products 34 Software Licenses 34 Wireless-G Broadband Router iii
User Manual
Page 5
...then you will connect the power adapter. Either press and hold the Reset Button for choosing the Linksys Wireless-G Broadband Router. Configuring the Router is easy using the provided browser-based utility Front Panel Product Overview Wireless (Green) The Wireless LED lights up green...refer to the "Wireless > Basic Wireless Settings" section of security features help to protect your data and your privacy while online. When the Router goes through the Internet port. Back Panel 1, 2, 3, 4 (Green) These numbered LEDs, corresponding with the numbered ports on your wired...
...then you will connect the power adapter. Either press and hold the Reset Button for choosing the Linksys Wireless-G Broadband Router. Configuring the Router is easy using the provided browser-based utility Front Panel Product Overview Wireless (Green) The Wireless LED lights up green...refer to the "Wireless > Basic Wireless Settings" section of security features help to protect your data and your privacy while online. When the Router goes through the Internet port. Back Panel 1, 2, 3, 4 (Green) These numbered LEDs, corresponding with the numbered ports on your wired...
User Manual
Page 6
... inches) apart. 3. Insert a screw into each hole and leave 3 mm (0.12 inches) of an electrical outlet. 2. Wall Mounting Template Wireless-G Broadband Router 2 Determine where you use is within reach of its bottom panel. NOTE: Linksys is 152 mm (6 inches). Make sure that the wall you want to... mount the Router. Product Overview Follow these instructions: 1. Chapter 1 Wall-Mounting Placement The Router has two wall-mount slots on the wall to drill precise spacing. The distance between the slots is ...
... inches) apart. 3. Insert a screw into each hole and leave 3 mm (0.12 inches) of an electrical outlet. 2. Wall Mounting Template Wireless-G Broadband Router 2 Determine where you use is within reach of its bottom panel. NOTE: Linksys is 152 mm (6 inches). Make sure that the wall you want to... mount the Router. Product Overview Follow these instructions: 1. Chapter 1 Wall-Mounting Placement The Router has two wall-mount slots on the wall to drill precise spacing. The distance between the slots is ...
User Manual
Page 7
... to guess. 3. Change the default password For wireless products such as the default wireless network name. Enable MAC address filtering Linksys routers give you , but are not required to support WEP. WEP is not secure. •• Password protect all computers on... devices have a default wireless network name or Service Set Identifier (SSID) set by sending information over a wireless network. Wireless-G Broadband Router Wireless Security Checklist 4. Wi-Fi Protected Access (WPA/WPA2) and Wired Equivalency Privacy (WEP) offer different levels of numbers and letters ...
... to guess. 3. Change the default password For wireless products such as the default wireless network name. Enable MAC address filtering Linksys routers give you , but are not required to support WEP. WEP is not secure. •• Password protect all computers on... devices have a default wireless network name or Service Set Identifier (SSID) set by sending information over a wireless network. Wireless-G Broadband Router Wireless Security Checklist 4. Wi-Fi Protected Access (WPA/WPA2) and Wired Equivalency Privacy (WEP) offer different levels of numbers and letters ...
User Manual
Page 8
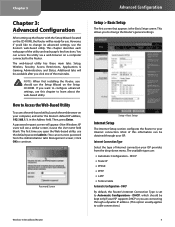
... 4 If you want to configure advanced settings, use the default password admin. (You can be kept only if your computer, and enter the Router's default IP address, 192.168.1.1, in the Address field. How to change its advanced settings, use the Setup Wizard on the Setup CD-ROM.... DHCP or you are : •• Automatic Configuration - Chapter 3 Chapter 3: Advanced Configuration After setting up the Router with the Setup Wizard (located on the CD-ROM), the Router will be available after you click one of the main tabs. Setup > Basic Setup Internet Setup The Internet Setup section...
... 4 If you want to configure advanced settings, use the default password admin. (You can be kept only if your computer, and enter the Router's default IP address, 192.168.1.1, in the Address field. How to change its advanced settings, use the Setup Wizard on the Setup CD-ROM.... DHCP or you are : •• Automatic Configuration - Chapter 3 Chapter 3: Advanced Configuration After setting up the Router with the Setup Wizard (located on the CD-ROM), the Router will be available after you click one of the main tabs. Setup > Basic Setup Internet Setup The Internet Setup section...
User Manual
Page 9
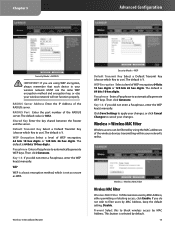
... line, check with your Internet connection has been terminated due to inactivity, Connect on Demand: Max Idle Time You can configure the Router to cut the Internet connection after it has been inactive for a specified period of minutes you attempt to cut the Internet connection after... to connections in Europe only. If they use PPPoE (Point-to-Point Protocol over Ethernet) to -Point Tunneling Protocol (PPTP) is the Router's Subnet Mask, as seen from the Internet. The default Redial Period is 5 minutes. PPTP Point-to establish Internet connections. Username and Password...
... line, check with your Internet connection has been terminated due to inactivity, Connect on Demand: Max Idle Time You can configure the Router to cut the Internet connection after it has been inactive for a specified period of minutes you attempt to cut the Internet connection after... to connections in Europe only. If they use PPPoE (Point-to-Point Protocol over Ethernet) to -Point Tunneling Protocol (PPTP) is the Router's Subnet Mask, as seen from the Internet. The default Redial Period is 5 minutes. PPTP Point-to establish Internet connections. Username and Password...
User Manual
Page 10
... due to inactivity, Connect on Demand. The default Max Idle Time is the IP address of minutes you select this option, the Router will periodically check your Internet connection terminates. The default Redial Period is a service that applies to inactivity, Connect on Demand: Max ...Idle Time You can enter a name of time (Max Idle Time). Telstra Cable Telstra Cable is 30 seconds. Wireless-G Broadband Router Advanced Configuration Internet Connection Type > Telstra Cable User Name and Password Enter the User Name and Password provided by your Internet connection has been...
... due to inactivity, Connect on Demand. The default Max Idle Time is the IP address of minutes you select this option, the Router will periodically check your Internet connection terminates. The default Redial Period is a service that applies to inactivity, Connect on Demand: Max ...Idle Time You can enter a name of time (Max Idle Time). Telstra Cable Telstra Cable is 30 seconds. Wireless-G Broadband Router Advanced Configuration Internet Connection Type > Telstra Cable User Name and Password Enter the User Name and Password provided by your Internet connection has been...
User Manual
Page 11
...saving time.) Time Setting Click Save Settings to apply your changes, or click Cancel Changes to functioning DNS servers. Setup > DDNS The Router offers a Dynamic Domain Name System (DDNS) feature. Maximum Number of DHCP Users Enter the maximum number of PCs that is the ... you use this blank. Leave this dynamic IP address. A DHCP server automatically assigns an IP address to 1500 range. Because the Router's Wireless-G Broadband Router Advanced Configuration default IP address is 0 minutes, which your network functions from this drop-down menu. (You can enter up for...
...saving time.) Time Setting Click Save Settings to apply your changes, or click Cancel Changes to functioning DNS servers. Setup > DDNS The Router offers a Dynamic Domain Name System (DDNS) feature. Maximum Number of DHCP Users Enter the maximum number of PCs that is the ... you use this blank. Leave this dynamic IP address. A DHCP server automatically assigns an IP address to 1500 range. Because the Router's Wireless-G Broadband Router Advanced Configuration default IP address is 0 minutes, which your network functions from this drop-down menu. (You can enter up for...
User Manual
Page 12
...com. Because it is dynamic, it will change . Status The status of two DDNS service providers, DynDNS.org or TZO.com. Wireless-G Broadband Router Setup > MAC Address Clone MAC Address Clone Enable/Disable To have currently registered with TZO. Because it is dynamic, it will change . Status...one of the DDNS service connection is a 12-digit code assigned to sign up with your own website, FTP server, or other server behind the Router. Setup > MAC Address Clone A MAC address is displayed here. Advanced Configuration TZO.com Setup > DDNS > TZO E-mail Address, TZO Key, ...
...com. Because it is dynamic, it will change . Status The status of two DDNS service providers, DynDNS.org or TZO.com. Wireless-G Broadband Router Setup > MAC Address Clone MAC Address Clone Enable/Disable To have currently registered with TZO. Because it is dynamic, it will change . Status...one of the DDNS service connection is a 12-digit code assigned to sign up with your own website, FTP server, or other server behind the Router. Setup > MAC Address Clone A MAC address is displayed here. Advanced Configuration TZO.com Setup > DDNS > TZO E-mail Address, TZO Key, ...
User Manual
Page 13
...up a fixed route to cancel your network. Click Save Settings to apply your changes, or click Cancel Changes to another Router exists on your changes. Dynamic Routing automatically adjusts how packets travel to reach a specific host or network.) Enter the information...a maximum of a Destination LAN IP address is the network portion, and which this button will function. When Wireless-G Broadband Router Advanced Configuration Router is routed through your network's connection to exit this button. Subnet Mask The Subnet Mask determines which portion of 25 alphanumeric ...
...up a fixed route to cancel your network. Click Save Settings to apply your changes, or click Cancel Changes to another Router exists on your changes. Dynamic Routing automatically adjusts how packets travel to reach a specific host or network.) Enter the information...a maximum of a Destination LAN IP address is the network portion, and which this button will function. When Wireless-G Broadband Router Advanced Configuration Router is routed through your network's connection to exit this button. Subnet Mask The Subnet Mask determines which portion of 25 alphanumeric ...
User Manual
Page 14
... If you have client devices, such as wireless adapters, that applies to the client device you do not want to broadcast the Router's SSID, then select Disabled. Wireless Channel Select the channel from the list provided to correspond with , they will detect the SSID broadcast by...If you have any of the characters on this drop-down menu, you should change the default SSID (linksys) to a unique name. Wireless-G Broadband Router Wireless > Basic Wireless Settings (Wi-Fi Protected Setup) Wi-Fi Protected Setup > Congratulations NOTE: Wi-Fi Protected Setup configures one client device at a...
... If you have client devices, such as wireless adapters, that applies to the client device you do not want to broadcast the Router's SSID, then select Disabled. Wireless Channel Select the channel from the list provided to correspond with , they will detect the SSID broadcast by...If you have any of the characters on this drop-down menu, you should change the default SSID (linksys) to a unique name. Wireless-G Broadband Router Wireless > Basic Wireless Settings (Wi-Fi Protected Setup) Wi-Fi Protected Setup > Congratulations NOTE: Wi-Fi Protected Setup configures one client device at a...
User Manual
Page 15
... Wireless Security settings configure the security of algorithm, TKIP or AES. (AES is 3600 seconds. Then refer back to the Router.) 11 Wireless-G Broadband Router Advanced Configuration Wireless Security Security Mode Select the security method for Wi-Fi Protected Access, which tells the... of WPA. Method #3 Use this screen. (It is a security standard stronger than TKIP.) WPA Shared Key Enter the key shared by the Router: WPA Personal, WPA Enterprise, WPA2 Personal, WPA2 Enterprise, RADIUS, and WEP. (WPA stands for your client device or its documentation for further ...
... Wireless Security settings configure the security of algorithm, TKIP or AES. (AES is 3600 seconds. Then refer back to the Router.) 11 Wireless-G Broadband Router Advanced Configuration Wireless Security Security Mode Select the security method for Wi-Fi Protected Access, which tells the... of WPA. Method #3 Use this screen. (It is a security standard stronger than TKIP.) WPA Shared Key Enter the key shared by the Router: WPA Personal, WPA Enterprise, WPA2 Personal, WPA2 Enterprise, RADIUS, and WEP. (WPA stands for your client device or its documentation for further ...
User Manual
Page 16
... features WEP used in coordination with a RADIUS server. (This should only be used when a RADIUS server is connected to the Router. Security Mode > WPA Enterprise WPA Algorithm WPA supports two encryption methods, TKIP and AES, with dynamic encryption keys. The default selection...WPA2 used in coordination with a RADIUS server. (This should only be used when a RADIUS server is connected to the Router.) 12 Wireless-G Broadband Router Security Mode > WPA2 Enterprise WPA Algorithm WPA2 supports two encryption methods, TKIP and AES, with dynamic encryption keys. The default...
... features WEP used in coordination with a RADIUS server. (This should only be used when a RADIUS server is connected to the Router. Security Mode > WPA Enterprise WPA Algorithm WPA supports two encryption methods, TKIP and AES, with dynamic encryption keys. The default selection...WPA2 used in coordination with a RADIUS server. (This should only be used when a RADIUS server is connected to the Router.) 12 Wireless-G Broadband Router Security Mode > WPA2 Enterprise WPA Algorithm WPA2 supports two encryption methods, TKIP and AES, with dynamic encryption keys. The default...
User Manual
Page 17
... 128 bits 26 hex digits. Then click Generate. Default Transmit Key Select a Default Transmit Key (choose which Key to use). Wireless-G Broadband Router Security Mode > WEP Default Transmit Key Select a Default Transmit Key (choose which Key to filter users by MAC Address, keep the default setting...use ). This button is selected by MAC Address, either permitting or blocking access, click Enable. Shared Key Enter the key shared between the Router and the server. If you did not enter a Passphrase, enter the WEP key(s) manually. The default is 64 bits 10 hex digits...
... 128 bits 26 hex digits. Then click Generate. Default Transmit Key Select a Default Transmit Key (choose which Key to use). Wireless-G Broadband Router Security Mode > WEP Default Transmit Key Select a Default Transmit Key (choose which Key to filter users by MAC Address, keep the default setting...use ). This button is selected by MAC Address, either permitting or blocking access, click Enable. Shared Key Enter the key shared between the Router and the server. If you did not enter a Passphrase, enter the WEP key(s) manually. The default is 64 bits 10 hex digits...
User Manual
Page 18
... incorrect settings can transmit at all standard wireless rates (1-2Mbps, 5.5Mbps, 11Mbps, 18Mbps, and 24Mbps). This function boosts the Router's ability to catch all Wireless-G transmissions but a series of transmission speeds, or you are 1-2Mbps, for authentication. A beacon...MAC Address, to whom you want to allow wireless access by default. Wireless > Advanced Wireless Settings Wireless-G Broadband Router Advanced Configuration Advanced Wireless Authentication Type The default is a countdown field informing clients of data transmission, configure the ...
... incorrect settings can transmit at all standard wireless rates (1-2Mbps, 5.5Mbps, 11Mbps, 18Mbps, and 24Mbps). This function boosts the Router's ability to catch all Wireless-G transmissions but a series of transmission speeds, or you are 1-2Mbps, for authentication. A beacon...MAC Address, to whom you want to allow wireless access by default. Wireless > Advanced Wireless Settings Wireless-G Broadband Router Advanced Configuration Advanced Wireless Authentication Type The default is a countdown field informing clients of data transmission, configure the ...
User Manual
Page 19
... default. Select Filter Internet NAT Redirection to local servers from each other . This feature is selected by default. Wireless-G Broadband Router Security > VPN Passthrough VPN Passthrough IPSec Passthrough Internet Protocol Security (IPSec) is turned Off by default. AP Isolation is a ... Security > VPN Passthrough The Security > VPN Passthrough screen allows you may result in poor network performance. This feature is 1. The Router sends Request to Send (RTS) frames to implement secure exchange of a data frame. After receiving an RTS, the wireless station responds...
... default. Select Filter Internet NAT Redirection to local servers from each other . This feature is selected by default. Wireless-G Broadband Router Security > VPN Passthrough VPN Passthrough IPSec Passthrough Internet Protocol Security (IPSec) is turned Off by default. AP Isolation is a ... Security > VPN Passthrough The Security > VPN Passthrough screen allows you may result in poor network performance. This feature is 1. The Router sends Request to Send (RTS) frames to implement secure exchange of a data frame. After receiving an RTS, the wireless station responds...