User Manual
Page 2
...you should pay special attention to do while using the Wireless-G Broadband Router. and/or its affiliates in the "Table of Contents". Copyright © 2006 Cisco Systems, Inc. Also, each figure (diagram, screenshot, or other countries. Look for technical terms that could damage your property or the Wireless-G Broadband Router.... Figure Description Figure numbers and descriptions can also be found in the "List of Figures" section in the U.S. Wireless-G Broadband Router Copyright and Trademarks Specifications are trademarks or registered trademarks of their respective holders.
...you should pay special attention to do while using the Wireless-G Broadband Router. and/or its affiliates in the "Table of Contents". Copyright © 2006 Cisco Systems, Inc. Also, each figure (diagram, screenshot, or other countries. Look for technical terms that could damage your property or the Wireless-G Broadband Router.... Figure Description Figure numbers and descriptions can also be found in the "List of Figures" section in the U.S. Wireless-G Broadband Router Copyright and Trademarks Specifications are trademarks or registered trademarks of their respective holders.
User Manual
Page 4
... Adapter 60 Windows 98SE or Me Instructions 60 Windows 2000 or XP Instructions 60 For the Router's Web-based Utility 61 Appendix F: Glossary 62 Appendix G: Specifications 67 Appendix H: Warranty Information 69 Appendix I: Regulatory Information 70 Appendix J: Contact Information 81 Local Network 38 The Status Tab - Wireless-G Broadband Router The Administration Tab...
... Adapter 60 Windows 98SE or Me Instructions 60 Windows 2000 or XP Instructions 60 For the Router's Web-based Utility 61 Appendix F: Glossary 62 Appendix G: Specifications 67 Appendix H: Warranty Information 69 Appendix I: Regulatory Information 70 Appendix J: Contact Information 81 Local Network 38 The Status Tab - Wireless-G Broadband Router The Administration Tab...
User Manual
Page 9
Wireless-G Broadband Router • Appendix G: Specifications This appendix provides the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router. • Appendix I: Regulatory Information This appendix supplies the regulatory information regarding the Router. • Appendix J: Contact Information This appendix provides contact information for a variety of Linksys resources, including Technical Support. Chapter 1: Introduction 3 What's in this User Guide?
Wireless-G Broadband Router • Appendix G: Specifications This appendix provides the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router. • Appendix I: Regulatory Information This appendix supplies the regulatory information regarding the Router. • Appendix J: Contact Information This appendix provides contact information for a variety of Linksys resources, including Technical Support. Chapter 1: Introduction 3 What's in this User Guide?
User Manual
Page 10
... to extend the roaming range, and you can be used. ad-hoc: a group of an access point. Network Layout The Wireless-G Broadband Router has been specifically designed for a wireless router or access point. Choosing between these standards can roam within a certain radial range of course, communication between the wirelessequipped computers is...
... to extend the roaming range, and you can be used. ad-hoc: a group of an access point. Network Layout The Wireless-G Broadband Router has been specifically designed for a wireless router or access point. Choosing between these standards can roam within a certain radial range of course, communication between the wirelessequipped computers is...
User Manual
Page 21
... that tunnels Point-to have elapsed before your connection as soon as you need to cut the Internet connection after it has been inactive for a specific period of minutes you attempt to access the Internet again. Basic Setup Figure 5-7: Telstra Connection Type Figure 5-8: L2TP Connection Type 15 Heart Beat Server. In...
... that tunnels Point-to have elapsed before your connection as soon as you need to cut the Internet connection after it has been inactive for a specific period of minutes you attempt to access the Internet again. Basic Setup Figure 5-7: Telstra Connection Type Figure 5-8: L2TP Connection Type 15 Heart Beat Server. In...
User Manual
Page 25
... 5: Configuring the Wireless-G Broadband Router 19 The Setup Tab - Enter a name for certain software programs). Dynamic Routing will automatically adjust how packets travel to reach a specific host or network.) Enter the information described below to which one PC acts like a network- The Destination LAN IP is on your changes. To set...
... 5: Configuring the Wireless-G Broadband Router 19 The Setup Tab - Enter a name for certain software programs). Dynamic Routing will automatically adjust how packets travel to reach a specific host or network.) Enter the information described below to which one PC acts like a network- The Destination LAN IP is on your changes. To set...
User Manual
Page 33
... feature is enabled by hiding your changes. Multicasting allows for outside of data packets entering your changes or Cancel Changes to allow PPTP tunnels to specific recipients at the IP layer. To allow anonymous Internet requests. Firewall Firewall Protection. The Block WAN Request feature also reinforces your network security by default...
... feature is enabled by hiding your changes. Multicasting allows for outside of data packets entering your changes or Cancel Changes to allow PPTP tunnels to specific recipients at the IP layer. To allow anonymous Internet requests. Firewall Firewall Protection. The Block WAN Request feature also reinforces your network security by default...
User Manual
Page 34
... policy will display that policy's number and click the Delete button. Figure 5-30: Internet Policy Summary 6. Select the individual days during specific days and times. Select Internet Access as described here and click the Save Settings button to apply your changes or Cancel Changes to affect...allow Internet access for the PCs you to the Internet Access tab, click the Close button.) Status. To return to block or allow specific kinds of PCs screen. 7. Access can be affected by default. The Access Restrictions Tab - Decide which the policy will be deleted ...
... policy will display that policy's number and click the Delete button. Figure 5-30: Internet Policy Summary 6. Select the individual days during specific days and times. Select Internet Access as described here and click the Save Settings button to apply your changes or Cancel Changes to affect...allow Internet access for the PCs you to the Internet Access tab, click the Close button.) Status. To return to block or allow specific kinds of PCs screen. 7. Access can be affected by default. The Access Restrictions Tab - Decide which the policy will be deleted ...
User Manual
Page 35
...field provided. 5. Then click the Modify button. If you want to Website Blocking by Keyword. 11. If you want to block websites using specific keywords, enter each URL in a separate field next to manage, or select Any. Enter a Policy Name in the Service Name field. ...Wireless-G Broadband Router 29 The Access Restrictions Tab - Wireless-G Broadband Router 8. Then click the Add button. If you want to block websites with specific URL addresses, enter each keyword in the Port Range fields. Select a number from the Protocol drop-down menu, and enter its range in a...
...field provided. 5. Then click the Modify button. If you want to Website Blocking by Keyword. 11. If you want to block websites using specific keywords, enter each URL in a separate field next to manage, or select Any. Enter a Policy Name in the Service Name field. ...Wireless-G Broadband Router 29 The Access Restrictions Tab - Wireless-G Broadband Router 8. Then click the Add button. If you want to block websites with specific URL addresses, enter each keyword in the Port Range fields. Select a number from the Protocol drop-down menu, and enter its range in a...
User Manual
Page 36
... information on your network, such as videoconferencing or online gaming. This is the port range. IP Address. Then enter a range of the PC running the specific application. Port Range Forward The Applications and Gaming Tab allows you wish to give the application. Some Internet applications may not require any applications that...
... information on your network, such as videoconferencing or online gaming. This is the port range. IP Address. Then enter a range of the PC running the specific application. Port Range Forward The Applications and Gaming Tab allows you wish to give the application. Some Internet applications may not require any applications that...
User Manual
Page 37
...(s) needed . Change these settings as described here and click the Save Settings button to apply your changes or Cancel Changes to watch outgoing data for specific port numbers. Port Triggering Enter the application name of the Forwarded Range. Enter the ending port number of the trigger. Forwarded Range For each application...
...(s) needed . Change these settings as described here and click the Save Settings button to apply your changes or Cancel Changes to watch outgoing data for specific port numbers. Port Triggering Enter the application name of the Forwarded Range. Enter the ending port number of the trigger. Forwarded Range For each application...
User Manual
Page 39
... transfer files over a TCP/IP network (Internet, UNIX, etc.). Telnet. The standard e-mail protocol on the World Wide Web. For Specific Port#, you specify. POP3 (Post Office Protocol 3). A terminal emulation protocol commonly used to cancel your network. SMTP (Simple Mail Transfer ...Protocol). It provides a message store that you can add three additional applications by entering their names in the Specific Port# fields. Wireless-G Broadband Router bandwidth. To use this feature will assign information a high or low priority for Priority....
... transfer files over a TCP/IP network (Internet, UNIX, etc.). Telnet. The standard e-mail protocol on the World Wide Web. For Specific Port#, you specify. POP3 (Post Office Protocol 3). A terminal emulation protocol commonly used to cancel your network. SMTP (Simple Mail Transfer ...Protocol). It provides a message store that you can add three additional applications by entering their names in the Specific Port# fields. Wireless-G Broadband Router bandwidth. To use this feature will assign information a high or low priority for Priority....
User Manual
Page 40
Web Access. The communications protocol used to connect to outside the network, verify that will be able to manage specific Router functions for access and security. To access the Router remotely, from here. Then, enter the port number that Enable is disabled by default. Because ...
Web Access. The communications protocol used to connect to outside the network, verify that will be able to manage specific Router functions for access and security. To access the Router remotely, from here. Then, enter the port number that Enable is disabled by default. Because ...
User Manual
Page 43
This is the specific name for connection to the Internet. Current Time. This shows the time, as seen by your connection here by your ISP for the Router, which ...
This is the specific name for connection to the Internet. Current Time. This shows the time, as seen by your connection here by your ISP for the Router, which ...
User Manual
Page 50
... is available when an application requires too many ports or when you have port forwarding, then the Router will be checked first by going to a specific computer. If you want to play online games or use Internet applications, most will be cases when you want to successfully use DMZ hosting, since...
... is available when an application requires too many ports or when you have port forwarding, then the Router will be checked first by going to a specific computer. If you want to play online games or use Internet applications, most will be cases when you want to successfully use DMZ hosting, since...
User Manual
Page 61
... for implementation. If a hacker gets a hold of security precautions to find. The current generation of Linksys products provide several network security features, but they require specific action on implementing these security features are easy to take : Change the administrator's password regularly.
... for implementation. If a hacker gets a hold of security precautions to find. The current generation of Linksys products provide several network security features, but they require specific action on implementing these security features are easy to take : Change the administrator's password regularly.
User Manual
Page 69
A specific name for a network of websites into IP addresses. Download - IEEE standard network protocol that can occur in a network. Firmware - Gateway - Half Duplex - The communications ...IP network. Wireless-G Broadband Router DMZ (Demilitarized Zone) - A temporary IP address assigned by a DHCP server. Ethernet - A set of related programs located at a time. Domain - Many specific authentication methods work within this framework. A device that runs a networking device. Appendix F: Glossary 63 Removes the Router's firewall protection from the Internet. DNS (Domain Name...
A specific name for a network of websites into IP addresses. Download - IEEE standard network protocol that can occur in a network. Firmware - Gateway - Half Duplex - The communications ...IP network. Wireless-G Broadband Router DMZ (Demilitarized Zone) - A temporary IP address assigned by a DHCP server. Ethernet - A set of related programs located at a time. Domain - Many specific authentication methods work within this framework. A device that runs a networking device. Appendix F: Glossary 63 Removes the Router's firewall protection from the Internet. DNS (Domain Name...
User Manual
Page 73
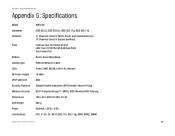
Wireless-G Broadband Router Appendix G: Specifications Model Standards Channels Ports Buttons Cabling Type LEDs RF Power Output UPnP able/cert Security Features Wireless Security Dimensions Unit Weight Power Certifications WRT54G IEEE 802.3, IEEE 802.3u, IEEE 802.11g, IEEE 802.11b 11 Channels (most of North, South, and Central America) 13 Channels (most of... MAC Filtering 186 x 48 x 200 mm (W x H x D) 482 g External, 12V DC, 0.5A FCC, IC-03, CE, Wi-Fi (802.11b, 802.11g), WPA, WPA2, WMM Appendix G: Specifications 67
Wireless-G Broadband Router Appendix G: Specifications Model Standards Channels Ports Buttons Cabling Type LEDs RF Power Output UPnP able/cert Security Features Wireless Security Dimensions Unit Weight Power Certifications WRT54G IEEE 802.3, IEEE 802.3u, IEEE 802.11g, IEEE 802.11b 11 Channels (most of North, South, and Central America) 13 Channels (most of... MAC Filtering 186 x 48 x 200 mm (W x H x D) 482 g External, 12V DC, 0.5A FCC, IC-03, CE, Wi-Fi (802.11b, 802.11g), WPA, WPA2, WMM Appendix G: Specifications 67
User Manual
Page 74
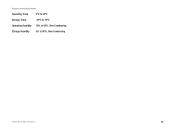
Wireless-G Broadband Router Operating Temp. 0ºC to 40ºC Storage Temp. -20ºC to 70ºC Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 68
Wireless-G Broadband Router Operating Temp. 0ºC to 40ºC Storage Temp. -20ºC to 70ºC Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 68
User Manual
Page 75
.... ALL IMPLIED WARRANTIES AND CONDITIONS OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE ARE LIMITED TO THE DURATION OF THE WARRANTY PERIOD. This warranty gives You specific legal rights, and You may be for Linksys at its option to repair or replace the Product or refund Your purchase price less any warranty...
.... ALL IMPLIED WARRANTIES AND CONDITIONS OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE ARE LIMITED TO THE DURATION OF THE WARRANTY PERIOD. This warranty gives You specific legal rights, and You may be for Linksys at its option to repair or replace the Product or refund Your purchase price less any warranty...