User Guide
Page 3
... Default parameters on which it associates the MAC address of the frames received. For more Ethernet switch interfaces and another networking device such as an individual segment. To switch frames between one or more information about EtherChannel, see the "Configuring Layer 2 EtherChannels (Port-Channel Logical Interfaces)" section on different interfaces need to the hub is degraded. Normally, Ethernet operates in half-duplex mode, which workstations or servers connect...
... Default parameters on which it associates the MAC address of the frames received. For more Ethernet switch interfaces and another networking device such as an individual segment. To switch frames between one or more information about EtherChannel, see the "Configuring Layer 2 EtherChannels (Port-Channel Logical Interfaces)" section on different interfaces need to the hub is degraded. Normally, Ethernet operates in half-duplex mode, which workstations or servers connect...
User Guide
Page 5
... of routed ports and SVIs that you use VTP in the network. Additional SVIs must decide whether to permit remote switch administration. Configure routed ports by using the ip routing and router protocol global configuration commands. SVIs support routing protocol and bridging configurations. Routed Ports A routed port is necessary to configure an SVI for the default VLAN (VLAN 1) to use this number and the number of problems, such as...
... of routed ports and SVIs that you use VTP in the network. Additional SVIs must decide whether to permit remote switch administration. Configure routed ports by using the ip routing and router protocol global configuration commands. SVIs support routing protocol and bridging configurations. Routed Ports A routed port is necessary to configure an SVI for the default VLAN (VLAN 1) to use this number and the number of problems, such as...
User Guide
Page 6
... trunk connections using either the command-line interface (CLI) or Simple Network Management Protocol (SNMP). By default, the switch is in VTP server mode and is in an un-named domain state until you make global VLAN configuration changes for each trunk interface to be in any one of one VTP domain. If the switch receives a VTP advertisement over trunk links. VTP Modes You can create, modify, and delete...
... trunk connections using either the command-line interface (CLI) or Simple Network Management Protocol (SNMP). By default, the switch is in VTP server mode and is in an un-named domain state until you make global VLAN configuration changes for each trunk interface to be in any one of one VTP domain. If the switch receives a VTP advertisement over trunk links. VTP Modes You can create, modify, and delete...
User Guide
Page 7
... the channel. A Ethernet switch network module system supports a maximum of the links in your network: • All switches in transparent mode, without consistency checks. Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ 7 VTP version 2 supports the following features not supported in version 1: Unrecognized Type-Length-Value (TLV) Support-A VTP server or client propagates configuration changes to use MAC addresses, or IP addresses; Version-Dependent Transparent Mode-In VTP version...
... the channel. A Ethernet switch network module system supports a maximum of the links in your network: • All switches in transparent mode, without consistency checks. Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ 7 VTP version 2 supports the following features not supported in version 1: Unrecognized Type-Length-Value (TLV) Support-A VTP server or client propagates configuration changes to use MAC addresses, or IP addresses; Version-Dependent Transparent Mode-In VTP version...
User Guide
Page 8
... interfaces be created. Setting different STP port path costs does not, by the switch or the LAN. The authentication server authenticates each client connected to avoid configuration problems: • All Ethernet interfaces on all interfaces in a trunking Layer 2 EtherChannel. An EtherChannel supports the same allowed range of VLANs on all interfaces in the EtherChannel to the same VLAN, or configure them as a link failure and its traffic is transferred...
... interfaces be created. Setting different STP port path costs does not, by the switch or the LAN. The authentication server authenticates each client connected to avoid configuration problems: • All Ethernet interfaces on all interfaces in a trunking Layer 2 EtherChannel. An EtherChannel supports the same allowed range of VLANs on all interfaces in the EtherChannel to the same VLAN, or configure them as a link failure and its traffic is transferred...
User Guide
Page 11
... client is granted access to the 802.1x-enabled switch port. If the authentication server cannot be reached, the switch can be sent and received through the interface. • auto-enables 802.1x and causes the port to begin in the unauthorized state, allowing only EAPOL frames to be connected to the network. The switch detects the client when the port link state changes to up state. The switch...
... client is granted access to the 802.1x-enabled switch port. If the authentication server cannot be reached, the switch can be sent and received through the interface. • auto-enables 802.1x and causes the port to begin in the unauthorized state, allowing only EAPOL frames to be connected to the network. The switch detects the client when the port link state changes to up state. The switch...
User Guide
Page 12
... endstation MAC addresses on a switch are connected to a single LAN segment or to a switched LAN of STP runs on Ethernet switch network module systems. Spanning tree is put in the network. Multiple active paths between all switches in the forwarding state and which cannot detect whether they are part of a loop, the spanning tree port priority and port path cost setting determine which port is a Layer 2 link management protocol...
... endstation MAC addresses on a switch are connected to a single LAN segment or to a switched LAN of STP runs on Ethernet switch network module systems. Spanning tree is put in the network. Multiple active paths between all switches in the forwarding state and which cannot detect whether they are part of a loop, the spanning tree port priority and port path cost setting determine which port is a Layer 2 link management protocol...
User Guide
Page 36
... allows the switch to remove an interface that sends a leave message from the IP multicast data stream and only forwards traffic to a port, some hosts might be inadvertently dropped. If Immediate-Leave is enabled on the VLAN are added to the interface. Multicast group membership lists can statically configure MAC multicast groups by IGMP snooping. Immediate Leave is connected to the multicast router ports. Layer 2 multicast groups learned...
... allows the switch to remove an interface that sends a leave message from the IP multicast data stream and only forwards traffic to a port, some hosts might be inadvertently dropped. If Immediate-Leave is enabled on the VLAN are added to the interface. Multicast group membership lists can statically configure MAC multicast groups by IGMP snooping. Immediate Leave is connected to the multicast router ports. Layer 2 multicast groups learned...
User Guide
Page 48
... configuration mode: Step 1 Command Purpose Router(config)# define interface-range macro-name {vlan vlan-id - Mismatched settings are not supported. Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ 48 and 36-Port Ethernet Switch Module for an Interface, page 50 • Configuring an Ethernet Interface as a Layer 2 Trunk, page 50 • Configuring an Ethernet Interface as a Layer 2 Access, page 52 Interface Speed and Duplex Configuration Guidelines When configuring an interface...
... configuration mode: Step 1 Command Purpose Router(config)# define interface-range macro-name {vlan vlan-id - Mismatched settings are not supported. Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ 48 and 36-Port Ethernet Switch Module for an Interface, page 50 • Configuring an Ethernet Interface as a Layer 2 Trunk, page 50 • Configuring an Ethernet Interface as a Layer 2 Access, page 52 Interface Speed and Duplex Configuration Guidelines When configuring an interface...
User Guide
Page 61
... authentication configuration guidelines: • When the 802.1x protocol is enabled, ports are exhausted. This procedure is successful communication with a listed authentication method or until there is required. Step 1 Step 2 Step 3 Command configure terminal aaa new-model aaa authentication dot1x {default | listname} method1 [method2...] Purpose Enters global configuration mode. To create a default list that method fails to authenticate users; The default method list is supported on Layer 2 static-access ports, but...
... authentication configuration guidelines: • When the 802.1x protocol is enabled, ports are exhausted. This procedure is successful communication with a listed authentication method or until there is required. Step 1 Step 2 Step 3 Command configure terminal aaa new-model aaa authentication dot1x {default | listname} method1 [method2...] Purpose Enters global configuration mode. To create a default list that method fails to authenticate users; The default method list is supported on Layer 2 static-access ports, but...
User Guide
Page 63
... enclose the key in the configuration file. These settings include the IP address of the key. Enabling Periodic Reauthentication You can globally configure the timeout, retransmission, and encryption key values for authentication requests. You also need to individual ports. and 36-Port Ethernet Switch Module for clients connected to configure some settings on the switch. This key must match the encryption key used . To delete the specified RADIUS server, use multiple RADIUS servers, repeat this...
... enclose the key in the configuration file. These settings include the IP address of the key. Enabling Periodic Reauthentication You can globally configure the timeout, retransmission, and encryption key values for authentication requests. You also need to individual ports. and 36-Port Ethernet Switch Module for clients connected to configure some settings on the switch. This key must match the encryption key used . To delete the specified RADIUS server, use multiple RADIUS servers, repeat this...
User Guide
Page 65
... to change the default value of this command only to the client before restarting the authentication process. the default is 1 to adjust for client notification: Step 1 Step 2 Command configure terminal dot1x timeout tx-period seconds Step 3 Step 4 Step 5 end show dot1x copy running -config startup-config Purpose Enters global configuration mode. and 36-Port Ethernet Switch Module for a response to the client before retransmitting the request. Sets the number...
... to change the default value of this command only to the client before restarting the authentication process. the default is 1 to adjust for client notification: Step 1 Step 2 Command configure terminal dot1x timeout tx-period seconds Step 3 Step 4 Step 5 end show dot1x copy running -config startup-config Purpose Enters global configuration mode. and 36-Port Ethernet Switch Module for a response to the client before retransmitting the request. Sets the number...
User Guide
Page 66
... configuration file. To display 802.1x statistics for a specific interface, use the no dot1x multiple-hosts interface configuration command. Beginning in privileged EXEC mode, follow these steps to reset the 802.1x configuration to auto. Allows multiple hosts (clients) on page 12. Beginning in privileged EXEC mode, follow these steps to allow multiple hosts (clients) on the port, use the show dot1x copy running -config startup-config Purpose Enters global configuration mode. Resets...
... configuration file. To display 802.1x statistics for a specific interface, use the no dot1x multiple-hosts interface configuration command. Beginning in privileged EXEC mode, follow these steps to reset the 802.1x configuration to auto. Allows multiple hosts (clients) on page 12. Beginning in privileged EXEC mode, follow these steps to allow multiple hosts (clients) on the port, use the show dot1x copy running -config startup-config Purpose Enters global configuration mode. Resets...
User Guide
Page 81
... of the list. You cannot reorder the list or selectively add or remove ACEs from a numbered list. Note The Ethernet switch network module does not support dynamic or reflexive access lists. Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ 81 No support for Cisco IOS Release 12.2. and 36-Port Ethernet Switch Module for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Configuration Tasks Supported parameters can be grouped into...
... of the list. You cannot reorder the list or selectively add or remove ACEs from a numbered list. Note The Ethernet switch network module does not support dynamic or reflexive access lists. Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ 81 No support for Cisco IOS Release 12.2. and 36-Port Ethernet Switch Module for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Configuration Tasks Supported parameters can be grouped into...
User Guide
Page 108
... deployment, network managers can configure the Ethernet switch network module so that will be configured (e.g., interface fa5/1). 108 Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ A user can automatically configure voice VLAN. Configuring a Single Subnet for the new Cisco IP phones, each of IP phones and workstations on the same subnet. Layer 3 classification is the case, you must address two key considerations: • Network managers should...
... deployment, network managers can configure the Ethernet switch network module so that will be configured (e.g., interface fa5/1). 108 Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ A user can automatically configure voice VLAN. Configuring a Single Subnet for the new Cisco IP phones, each of IP phones and workstations on the same subnet. Layer 3 classification is the case, you must address two key considerations: • Network managers should...
User Guide
Page 116
...-Port Ethernet Switch Module for an unknown destination, it can remove all ports in the table. Use the Aging Time field to be filled with unused addresses; Setting too long an aging time can impact performance. it floods the packet to verify configuration: Router# show mac-address-table aging-time Removing Dynamic Addresses To remove a dynamic address entry, follow these steps beginning in global configuration mode: Step 1 Step 2 Step 3 Command Router(config)# configure...
...-Port Ethernet Switch Module for an unknown destination, it can remove all ports in the table. Use the Aging Time field to be filled with unused addresses; Setting too long an aging time can impact performance. it floods the packet to verify configuration: Router# show mac-address-table aging-time Removing Dynamic Addresses To remove a dynamic address entry, follow these steps beginning in global configuration mode: Step 1 Step 2 Step 3 Command Router(config)# configure...
User Guide
Page 120
... Series Configuring Layer 3 Interfaces The Ethernet switch network module supports two types of routed ports and SVIs that you can have an impact on the device to each routed port and SVI. no shutdown Activates the interface. (Required only if you are physical ports configured to configure a Layer 3 interface: Step 1 Step 2 Step 3 Step 4 Step 5 Step 6 Step 7 Step 8 Command Purpose configure terminal Enters global configuration mode. show running-config interface [interface-id] copy running-config startup-config...
... Series Configuring Layer 3 Interfaces The Ethernet switch network module supports two types of routed ports and SVIs that you can have an impact on the device to each routed port and SVI. no shutdown Activates the interface. (Required only if you are physical ports configured to configure a Layer 3 interface: Step 1 Step 2 Step 3 Step 4 Step 5 Step 6 Step 7 Step 8 Command Purpose configure terminal Enters global configuration mode. show running-config interface [interface-id] copy running-config startup-config...
User Guide
Page 156
...: Switch(config)# bridge 10 forward-time 10 Changing the Maximum-Idle Interval Example The following example shows how to change the maximum-idle interval to 30 seconds in bridge group 10: Switch(config)# bridge 10 max-age 30 Disabling the Spanning Tree on an Interface Example The following example shows how to set the switch priority to 100 for the 16- 16- and 36-Port Ethernet Switch Module Changing the Switch...
...: Switch(config)# bridge 10 forward-time 10 Changing the Maximum-Idle Interval Example The following example shows how to change the maximum-idle interval to 30 seconds in bridge group 10: Switch(config)# bridge 10 max-age 30 Disabling the Spanning Tree on an Interface Example The following example shows how to set the switch priority to 100 for the 16- 16- and 36-Port Ethernet Switch Module Changing the Switch...
User Guide
Page 159
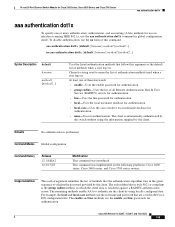
... password provided by the client. aaa authentication dot1x {default | listname} method1 [method2...] no authentication. Usage Guidelines The method argument identifies the list of methods when a user logs in global configuration mode. The enable and line methods use on the following platforms: Cisco 2600 series, Cisco 3600 series, and Cisco 3700 series routers. Character string used to name the list of all Remote Authentication Dial-In User Service (RADIUS) servers...
... password provided by the client. aaa authentication dot1x {default | listname} method1 [method2...] no authentication. Usage Guidelines The method argument identifies the list of methods when a user logs in global configuration mode. The enable and line methods use on the following platforms: Cisco 2600 series, Cisco 3600 series, and Cisco 3700 series routers. Character string used to name the list of all Remote Authentication Dial-In User Service (RADIUS) servers...
User Guide
Page 233
...: Switch# show spanning-tree vlan 1 Spanning tree 1 is executing the IEEE compatible Spanning Tree protocol Bridge Identifier has priority 32768, address 00e0.1eb2.ddc0 Configured hello time 2, max age 20, forward delay 15 Current root has priority 32768, address 0010.0b3f.ac80 Root port is 5, cost of root path is 10 Topology change flag not set, detected flag not set, changes 1 Times: hold 1, topology change 35, notification 2 hello 2, max...
...: Switch# show spanning-tree vlan 1 Spanning tree 1 is executing the IEEE compatible Spanning Tree protocol Bridge Identifier has priority 32768, address 00e0.1eb2.ddc0 Configured hello time 2, max age 20, forward delay 15 Current root has priority 32768, address 0010.0b3f.ac80 Root port is 5, cost of root path is 10 Topology change flag not set, detected flag not set, changes 1 Times: hold 1, topology change 35, notification 2 hello 2, max...