W1 Manual for English Edition
Page 5
... software support may vary depending on this problem. Due to correct this Notebook PC may be the (D:) drive or (E:) drive on your built-in "My Computer" (may produce different results than the preloaded one, the following are the actual driver names displayed in the provided user's manuals. If the autorun menu...
... software support may vary depending on this problem. Due to correct this Notebook PC may be the (D:) drive or (E:) drive on your built-in "My Computer" (may produce different results than the preloaded one, the following are the actual driver names displayed in the provided user's manuals. If the autorun menu...
W1 Manual for English Edition
Page 10
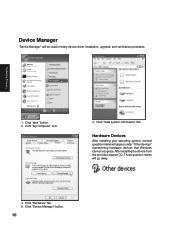
Click "My Computer" icon. 3. Click "Hardware" tab. 5. Click "Device Manager" button. 10 Those question marks will appear under "Other devices" representing hardware devices that Windows cannot recognize. After installing the drivers from the provided support CD. Click "View system information" link. Hardware Devices After installing your operating system, several question marks will go away. 4. Software Drivers 1. Click "start" button. 2. Device Manager "Device Manager" will be used in many device driver installation, upgrade, and verification processes.
Click "My Computer" icon. 3. Click "Hardware" tab. 5. Click "Device Manager" button. 10 Those question marks will appear under "Other devices" representing hardware devices that Windows cannot recognize. After installing the drivers from the provided support CD. Click "View system information" link. Hardware Devices After installing your operating system, several question marks will go away. 4. Software Drivers 1. Click "start" button. 2. Device Manager "Device Manager" will be used in many device driver installation, upgrade, and verification processes.
W1 Manual for English Edition
Page 31
In the example here, a warning is shown here. Click Change to use spaces or symbols in the computer name. You cannot use "Notebook PC". You can use the single word "Notebook" instead. 31 Configuring your LAN Joining a Domain or Workgroup (Windows XP) Software Drivers (1) Click Start and My Computer. (2) Click View system information. (3) Your computer name, workgroup or domain information is given when trying to view options.
In the example here, a warning is shown here. Click Change to use spaces or symbols in the computer name. You cannot use "Notebook PC". You can use the single word "Notebook" instead. 31 Configuring your LAN Joining a Domain or Workgroup (Windows XP) Software Drivers (1) Click Start and My Computer. (2) Click View system information. (3) Your computer name, workgroup or domain information is given when trying to view options.
W1 Manual for English Edition
Page 32
... in the Control Panel. 32 Joining a Domain or Workgroup (Cont') Software Drivers (4a) Domain: The primary server in the domain will be asked for your computer.
... in the Control Panel. 32 Joining a Domain or Workgroup (Cont') Software Drivers (4a) Domain: The primary server in the domain will be asked for your computer.
W1 Manual for English Edition
Page 33
Viewing Your Network (6) Clicking on "My Network Places" will display all the servers available under that protocol. 33 Software Drivers Joining a Domain or Workgroup (Cont') (5) After you restart your computer, you have installed protocols for. Clicking a network protocol such as "MS Windows Network" will display networks which you should see some contents through Entire Network.
Viewing Your Network (6) Clicking on "My Network Places" will display all the servers available under that protocol. 33 Software Drivers Joining a Domain or Workgroup (Cont') (5) After you restart your computer, you have installed protocols for. Clicking a network protocol such as "MS Windows Network" will display networks which you should see some contents through Entire Network.
W1 Manual for English Edition
Page 48
...to the Internet. However, the program behind the interface uses the latest technology and provides you with protection from Windows Explorer or My Computer by right-clicking the file icon • Scan floppy disks and clean any file from the nastiest viruses, sneakiest Trojans, and the ...for macro viruses • Scan your email attachments as they are being downloaded from an Internet (POP3) mail server • Protect your computer against malicious Java applets and Microsoft ActiveX controls while surfing the Web • Detects and cleans live Trojans installed on your system • ...
...to the Internet. However, the program behind the interface uses the latest technology and provides you with protection from Windows Explorer or My Computer by right-clicking the file icon • Scan floppy disks and clean any file from the nastiest viruses, sneakiest Trojans, and the ...for macro viruses • Scan your email attachments as they are being downloaded from an Internet (POP3) mail server • Protect your computer against malicious Java applets and Microsoft ActiveX controls while surfing the Web • Detects and cleans live Trojans installed on your system • ...
W1 Manual for English Edition
Page 49
...filtering network traffic, the firewall prevents malicious programs or files from being traced, the hacker can still wreak havoc on both your computer from malicious code like NetBIOS browsing, port scanning, or ICMP packet special processing will be filtered. The Trojan Backdoor Blocking function ...PC-cillin 2002 providing you know are still vulnerable to the Internet for Wireless is ideal for computers using techniques like spyware and Trojan horses. Even computers that you with its new Personal Firewall feature. This barrier examines and filters network traffic coming into...
...filtering network traffic, the firewall prevents malicious programs or files from being traced, the hacker can still wreak havoc on both your computer from malicious code like NetBIOS browsing, port scanning, or ICMP packet special processing will be filtered. The Trojan Backdoor Blocking function ...PC-cillin 2002 providing you know are still vulnerable to the Internet for Wireless is ideal for computers using techniques like spyware and Trojan horses. Even computers that you with its new Personal Firewall feature. This barrier examines and filters network traffic coming into...
W1 Manual for English Edition
Page 50
... harmful known script-based viruses ("I Love You" and "Anna Kournikova"), but can also update and register your software. In addition, you can also protect your computer. The TSC uses patterns to define how to determine the meaning of Trojan horse programs, recovers system files which are kept up-to and from...
... harmful known script-based viruses ("I Love You" and "Anna Kournikova"), but can also update and register your software. In addition, you can also protect your computer. The TSC uses patterns to define how to determine the meaning of Trojan horse programs, recovers system files which are kept up-to and from...
W1 Manual for English Edition
Page 51
... updates for example, .exe, .com, .dll) and execute whenever the host program executes. About viruses A computer virus is worth bearing in the appropriate fields, receive your computer is online, PC-cillin automatically connects to the Trend Micro server to check if the latest update is often buggy... not to start downloading. If you want to download immediately, the pop-up window reappears in your system can lead to register your computer is harmful or not, its components updated; Beyond simple replication, a virus almost always seeks to fulfill another purpose: to just taunting ...
... updates for example, .exe, .com, .dll) and execute whenever the host program executes. About viruses A computer virus is worth bearing in the appropriate fields, receive your computer is online, PC-cillin automatically connects to the Trend Micro server to check if the latest update is often buggy... not to start downloading. If you want to download immediately, the pop-up window reappears in your system can lead to register your computer is harmful or not, its components updated; Beyond simple replication, a virus almost always seeks to fulfill another purpose: to just taunting ...
W1 Manual for English Edition
Page 52
... which uses Trend's award-winning, 32-bit, multi-threading scan engine, is not wasted hunting down (and cleaning up on hacker's computers. Software Utilities How viruses are known to make certain your company is not victimized, that data you can view updated Security Alerts and ...the Real-time top ten viruses. Why? Usually, though, misguided individuals who writes a virus program and then introduces it to computers create viruses. Use it onto a single computer, network server, or the Internet. Viewing the Trend Micro Virus list The Virus Information Center contains a list of...
... which uses Trend's award-winning, 32-bit, multi-threading scan engine, is not wasted hunting down (and cleaning up on hacker's computers. Software Utilities How viruses are known to make certain your company is not victimized, that data you can view updated Security Alerts and ...the Real-time top ten viruses. Why? Usually, though, misguided individuals who writes a virus program and then introduces it to computers create viruses. Use it onto a single computer, network server, or the Internet. Viewing the Trend Micro Virus list The Virus Information Center contains a list of...
W1 Manual for English Edition
Page 54
... and network activity. All incoming and outgoing Internet traffic is currently under attack. Stop Network Activity Click the large button with a computer and broken network cable to stop all network activity if you suspect harmful activities are being made to protect you from the network. ...54 Or right click and select "Configuration". Your computer is halted. The real-time scanning function is activated. The Emergency Lock is enabled. Real-time Status Select "Real-time Status" ...
... and network activity. All incoming and outgoing Internet traffic is currently under attack. Stop Network Activity Click the large button with a computer and broken network cable to stop all network activity if you suspect harmful activities are being made to protect you from the network. ...54 Or right click and select "Configuration". Your computer is halted. The real-time scanning function is activated. The Emergency Lock is enabled. Real-time Status Select "Real-time Status" ...
W1 Manual for English Edition
Page 63
... indicating that lets you open the Probe2 interface. It also has a utility that Probe2 is a convenient utility to Programs, and then ASUS Utility, and then click Probe VX.XX. Software Utilities Probe2 Reference Probe2 is running services. 63 When Probe2 starts, a splash screen appears... allowing you to select whether to show the screen again when you review useful information about your computer system's vital components, such as hard disk space, memory usage, and CPU type, CPU speed, and internal/ external frequencies through the...
... indicating that lets you open the Probe2 interface. It also has a utility that Probe2 is a convenient utility to Programs, and then ASUS Utility, and then click Probe VX.XX. Software Utilities Probe2 Reference Probe2 is running services. 63 When Probe2 starts, a splash screen appears... allowing you to select whether to show the screen again when you review useful information about your computer system's vital components, such as hard disk space, memory usage, and CPU type, CPU speed, and internal/ external frequencies through the...
W1 Manual for English Edition
Page 88
... and tailor your Notebook PC to allow BIOS updating without using the BIOS setup program so that the computer can recognize these changes and record them in the CMOS RAM. A battery backed-up the computer, press [F2] to "Run Setup" during bootup. The Setup program has been designed to reconfigure your BIOS...
... and tailor your Notebook PC to allow BIOS updating without using the BIOS setup program so that the computer can recognize these changes and record them in the CMOS RAM. A battery backed-up the computer, press [F2] to "Run Setup" during bootup. The Setup program has been designed to reconfigure your BIOS...
W1 Manual for English Edition
Page 94
... [Both] (shows enabled item) This item allows you to edit device information. (Editing device information is only used for troubleshooting by technical computer experts and should never be edited by users.) [Not Detected] If "Not Detected" is shown here, it means that there is only ...used for troubleshooting by technical computer experts and should never be edited by users.) [ATAPI CDROM] This item automatically detects any IDE device connected here. BIOS Setup Advanced (sub...
... [Both] (shows enabled item) This item allows you to edit device information. (Editing device information is only used for troubleshooting by technical computer experts and should never be edited by users.) [Not Detected] If "Not Detected" is shown here, it means that there is only ...used for troubleshooting by technical computer experts and should never be edited by users.) [ATAPI CDROM] This item automatically detects any IDE device connected here. BIOS Setup Advanced (sub...
W1 Manual for English Edition
Page 96
... : [Auto] [Disabled] [Enabled] 32Bit Data Transfer [Enabled] Enables or disables 32-bit data transfers for the remaining fields on this option speeds up communication between a computer's BIOS and hard disk. Disabled - The configuration options are : [Auto] [0] [1] [2] [3] [4] DMA Mode [Auto] When enabled, this sub-menu. The configuration options are : [Disabled] [Auto] PIO...
... : [Auto] [Disabled] [Enabled] 32Bit Data Transfer [Enabled] Enables or disables 32-bit data transfers for the remaining fields on this option speeds up communication between a computer's BIOS and hard disk. Disabled - The configuration options are : [Auto] [0] [1] [2] [3] [4] DMA Mode [Auto] When enabled, this sub-menu. The configuration options are : [Disabled] [Auto] PIO...
W1 Manual for English Edition
Page 99
... Password A hard disk password places a protection on the hard disk drive so that a password is necessary in order to modify hidden bootup files on another computer. • The protected hard disk drive cannot be used as a master or slave drive on your hard disk drive. Symbols and other keys are : [Disabled...
... Password A hard disk password places a protection on the hard disk drive so that a password is necessary in order to modify hidden bootup files on another computer. • The protected hard disk drive cannot be used as a master or slave drive on your hard disk drive. Symbols and other keys are : [Disabled...
W1 Manual for English Edition
Page 109
... INDIRECT DAMAGES OR FOR ANY ECONOMIC CONSEQUENTIAL DAMAGES (INCLUDING LOST PROFITS OR SAVINGS), EVEN IF ASUS, ITS SUPPLIERS OR YOUR RESELLER IS INFORMED OF THEIR POSSIBILITY. or (2) the serial number of ASUSTeK COMPUTER INC. ("ASUS"). Copyright © 2004 ASUSTeK COMPUTER INC. Limitation of Liability Circumstances may not be extended if: (1) the product is repaired...
... INDIRECT DAMAGES OR FOR ANY ECONOMIC CONSEQUENTIAL DAMAGES (INCLUDING LOST PROFITS OR SAVINGS), EVEN IF ASUS, ITS SUPPLIERS OR YOUR RESELLER IS INFORMED OF THEIR POSSIBILITY. or (2) the serial number of ASUSTeK COMPUTER INC. ("ASUS"). Copyright © 2004 ASUSTeK COMPUTER INC. Limitation of Liability Circumstances may not be extended if: (1) the product is repaired...
W1 Manual for English Edition
Page 1
... be responsible for or indemnify you for identification or explanation and to the owners' benefit, without the express written permission of ASUSTeK COMPUTER INC. ("ASUS"). Copyright © 2003 ASUSTeK COMPUTER INC. ASUS will not be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any other liability, you are entitled to the listed...
... be responsible for or indemnify you for identification or explanation and to the owners' benefit, without the express written permission of ASUSTeK COMPUTER INC. ("ASUS"). Copyright © 2003 ASUSTeK COMPUTER INC. ASUS will not be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any other liability, you are entitled to the listed...
W1 Manual for English Edition
Page 6
.... Use the provided support CD to install another operating system other than the preloaded one, the following are the actual driver names displayed in "My Computer" (may not be many hardware devices without drivers. The following pages will bring up the autorun menu. Variations may be found for Windows The Notebook...
.... Use the provided support CD to install another operating system other than the preloaded one, the following are the actual driver names displayed in "My Computer" (may not be many hardware devices without drivers. The following pages will bring up the autorun menu. Variations may be found for Windows The Notebook...
W1 Manual for English Edition
Page 10
... operating system. PCMCIA "R5C593" (Already supported in its Windows XP operating system. The processors can dynamically switch clock frequency and voltage, depending on whether the computer is running on batteries or is provided by Microsoft in Windows XP) This driver is plugged into AC power. Support CD Drivers Provided in its...
... operating system. PCMCIA "R5C593" (Already supported in its Windows XP operating system. The processors can dynamically switch clock frequency and voltage, depending on whether the computer is running on batteries or is provided by Microsoft in Windows XP) This driver is plugged into AC power. Support CD Drivers Provided in its...