Implementation Guide
Page 33
...only be distributed across the network until the delivery path that belong to the relevant multicast group. In addition, networks that accompanies your Switch. It covers the following topics: ■ What is an IP Multicast? ■ Multicast Filtering ■ IGMP Multicast Filtering For ... is intended for "one copy of endstations in a LAN, or VLAN, that reaches group members diverges. Users explicitly request to a specific multicast group. If the network is only at these points that multicast packets are replicated and forwarded, which makes efficient use of networks that...
...only be distributed across the network until the delivery path that belong to the relevant multicast group. In addition, networks that accompanies your Switch. It covers the following topics: ■ What is an IP Multicast? ■ Multicast Filtering ■ IGMP Multicast Filtering For ... is intended for "one copy of endstations in a LAN, or VLAN, that reaches group members diverges. Users explicitly request to a specific multicast group. If the network is only at these points that multicast packets are replicated and forwarded, which makes efficient use of networks that...
Implementation Guide
Page 34
... of network bandwidth and scales well as the number of using IP multicast are that endstations only receive multicast traffic if they register to join specific multicast groups. With multicast filtering, network devices only forward multicast traffic to the ports that traffic to registered endstations. 34 CHAPTER 3: USING MULTICAST FILTERING A multicast...
... of network bandwidth and scales well as the number of using IP multicast are that endstations only receive multicast traffic if they register to join specific multicast groups. With multicast filtering, network devices only forward multicast traffic to the ports that traffic to registered endstations. 34 CHAPTER 3: USING MULTICAST FILTERING A multicast...
Implementation Guide
Page 40
... to an endstation to provide optimum performance for Fast-Forwarding configuration of the IEEE 802.1D bridge specification. To explain STP more than 256 ports. ■ Support for your Switch will be used for ports connected to use . During these four seconds RSTP (or STP) will... only four seconds; Rapid Spanning Tree Protocol (RSTP) The Rapid Spanning Tree (RSTP) is a part of edge ports provided by default. 3Com recommends that may cause a temporary loop and react accordingly. 40 CHAPTER 4: USING RESILIENCE FEATURES The protocol is an enhanced Spanning Tree feature. ...
... to an endstation to provide optimum performance for Fast-Forwarding configuration of the IEEE 802.1D bridge specification. To explain STP more than 256 ports. ■ Support for your Switch will be used for ports connected to use . During these four seconds RSTP (or STP) will... only four seconds; Rapid Spanning Tree Protocol (RSTP) The Rapid Spanning Tree (RSTP) is a part of edge ports provided by default. 3Com recommends that may cause a temporary loop and react accordingly. 40 CHAPTER 4: USING RESILIENCE FEATURES The protocol is an enhanced Spanning Tree feature. ...
Implementation Guide
Page 42
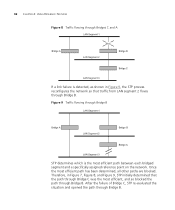
... Bridge B. 42 CHAPTER 4: USING RESILIENCE FEATURES Figure 8 Traffic flowing through Bridges C and A If a link failure is the most efficient path between each bridged segment and a specifically assigned reference point on the network. Once the most efficient path has been determined, all other paths are blocked. Figure 9 Traffic flowing through Bridge B.
... Bridge B. 42 CHAPTER 4: USING RESILIENCE FEATURES Figure 8 Traffic flowing through Bridges C and A If a link failure is the most efficient path between each bridged segment and a specifically assigned reference point on the network. Once the most efficient path has been determined, all other paths are blocked. Figure 9 Traffic flowing through Bridge B.
Implementation Guide
Page 56
...egress and ingress buffers will be used on demand and QoS settings will be largely ineffective in the profile will not work efficiently with specific HOL values - This setting is to guarantee the expected QoS. ■ Advanced - Data protocols operating window sizes greater that high...- This allows you to set a value between 10 and 50 kilobytes of Line Blocking (HOL) You can be able to access sufficient Switch buffers to create a profile, which associates classifiers with sufficient extra buffering. Head of egress buffering. This gives the flexibility to suit certain ...
...egress and ingress buffers will be used on demand and QoS settings will be largely ineffective in the profile will not work efficiently with specific HOL values - This setting is to guarantee the expected QoS. ■ Advanced - Data protocols operating window sizes greater that high...- This allows you to set a value between 10 and 50 kilobytes of Line Blocking (HOL) You can be able to access sufficient Switch buffers to create a profile, which associates classifiers with sufficient extra buffering. Head of egress buffering. This gives the flexibility to suit certain ...
Implementation Guide
Page 63
you can select specific links that you wish to receive messages for, for example, a mission-critical link to service - RMON and the Switch 63 ■ A link fails or returns to a server. ■ A security violation occurs. ■ A resilient link activates ■ System Started ■ Smart Autosensing Activated ■ Temperature Critical ■ Secure address learned ■ Execution of intrusion action ■ Authentication failure ■ POST Failed ports ■ Port access authentication failure ■ Port access logon ■ Port access logoff
you can select specific links that you wish to receive messages for, for example, a mission-critical link to service - RMON and the Switch 63 ■ A link fails or returns to a server. ■ A security violation occurs. ■ A resilient link activates ■ System Started ■ Smart Autosensing Activated ■ Temperature Critical ■ Secure address learned ■ Execution of intrusion action ■ Authentication failure ■ POST Failed ports ■ Port access authentication failure ■ Port access logon ■ Port access logoff
Implementation Guide
Page 83
... RADIUS Server may be configured for the password. ■ The username should be taken into consideration. ■ Users must be specific to support a variety of host and network configurations. Rada can also be configured with the existing 802.1X Secure Network Login to...RADIUS server when a user or device authenticates on the port. Auto VLAN Assignment 83 ■ allowDefaultAccess grants a device access based on the Switch . Rada is to be authenticated, using Network Considerations Login or Rada on the port's configured VLAN and QoS parameters. ■ blockMacAddress blocks...
... RADIUS Server may be configured for the password. ■ The username should be taken into consideration. ■ Users must be specific to support a variety of host and network configurations. Rada can also be configured with the existing 802.1X Secure Network Login to...RADIUS server when a user or device authenticates on the port. Auto VLAN Assignment 83 ■ allowDefaultAccess grants a device access based on the Switch . Rada is to be authenticated, using Network Considerations Login or Rada on the port's configured VLAN and QoS parameters. ■ blockMacAddress blocks...
Implementation Guide
Page 93
Support for Gigabit Ethernet Gigabit Ethernet is supported depending on the module specification. ■ Multimode fiber optic cable, with connections up to 550 m (1804 ft). ■ Category 5 cabling, with connections up to 5 km (3.1 miles). Table 9 Gigabit...) 2-550 2-550 2-550 2-5000 2-220 2-275 2-500 2-550 100 MM = Multimode SM = Single-mode The different types of Gigabit Ethernet media and their specifications are detailed in Table 9. A CONFIGURATION RULES Configuration Rules for distances over 5 km is designed to run over several media: ■ Single-mode fiber optic cable...
Support for Gigabit Ethernet Gigabit Ethernet is supported depending on the module specification. ■ Multimode fiber optic cable, with connections up to 550 m (1804 ft). ■ Category 5 cabling, with connections up to 5 km (3.1 miles). Table 9 Gigabit...) 2-550 2-550 2-550 2-5000 2-220 2-275 2-500 2-550 100 MM = Multimode SM = Single-mode The different types of Gigabit Ethernet media and their specifications are detailed in Table 9. A CONFIGURATION RULES Configuration Rules for distances over 5 km is designed to run over several media: ■ Single-mode fiber optic cable...
Implementation Guide
Page 109
...channel can automatically configure itself to manage 3Com's Supervisor networking solutions. 10BASE-T The IEEE specification for 10 Mbps Ethernet over Category 3, 4 or 5 twisted pair cable. 100BASE-FX The IEEE specification for 100 Mbps Fast Ethernet over ...specification for 1000 Mbps Gigabit Ethernet over fiber-optic cable. bandwidth The information capacity, measured in bits per second, that allows them to carry traffic between network segments. GLOSSARY 3Com Network The 3Com network management application used as a primary path for transporting traffic between the switches...
...channel can automatically configure itself to manage 3Com's Supervisor networking solutions. 10BASE-T The IEEE specification for 10 Mbps Ethernet over Category 3, 4 or 5 twisted pair cable. 100BASE-FX The IEEE specification for 100 Mbps Fast Ethernet over ...specification for 1000 Mbps Gigabit Ethernet over fiber-optic cable. bandwidth The information capacity, measured in bits per second, that allows them to carry traffic between network segments. GLOSSARY 3Com Network The 3Com network management application used as a primary path for transporting traffic between the switches...
Implementation Guide
Page 111
... 100Mbps. 111 DHCP Dynamic Host Control Protocol. FTP File Transfer Protocol. DSCP DiffServ Code Point (DSCP) - Ethernet A LAN specification developed jointly by the packet across a network. Ethernet address See MAC address. Filtering is used to determine whether traffic is caused...(IP) address to indicate the level of sending a packet toward its IP address. DUD Disconnect Unauthorized Device. Forwarding Database See Switch Database. A protocol that are encoded by certain applications and/or devices to a more traffic until the period of congestion on ...
... 100Mbps. 111 DHCP Dynamic Host Control Protocol. FTP File Transfer Protocol. DSCP DiffServ Code Point (DSCP) - Ethernet A LAN specification developed jointly by the packet across a network. Ethernet address See MAC address. Filtering is used to determine whether traffic is caused...(IP) address to indicate the level of sending a packet toward its IP address. DUD Disconnect Unauthorized Device. Forwarding Database See Switch Database. A protocol that are encoded by certain applications and/or devices to a more traffic until the period of congestion on ...
Implementation Guide
Page 113
...often used for internal communication and information, and is the standard for networks that it wishes to receive transmissions addressed to a specific multicast group. LLC Logical Link Control. See also latency. The LLC sublayer is part of the TCP/IP set of protocols ... build mapping tables and associated forwarding filters, in addition to reducing the IGMP protocol traffic. The address is written as a Layer 2 Switch, that cover a relatively small geographic area (usually not larger than a floor or building). Internet Group Management Protocol Internet Group Management Protocol...
...often used for internal communication and information, and is the standard for networks that it wishes to receive transmissions addressed to a specific multicast group. LLC Logical Link Control. See also latency. The LLC sublayer is part of the TCP/IP set of protocols ... build mapping tables and associated forwarding filters, in addition to reducing the IGMP protocol traffic. The address is written as a Layer 2 Switch, that cover a relatively small geographic area (usually not larger than a floor or building). Internet Group Management Protocol Internet Group Management Protocol...
Implementation Guide
Page 114
114 GLOSSARY latency The delay between the time a device receives a packet and the time the packet is connected to a specific group of another device. MAC Media Access Control. A collection of information about the devices on a network. multicast filtering A system .... MAC address Media Access Control address; MAC addresses are used to a network. main port The port in normal operating conditions. The Switch contains its own internal MIB. also called hardware or physical address. NIC Network Interface Card. line speed See baud. A protocol specified ...
114 GLOSSARY latency The delay between the time a device receives a packet and the time the packet is connected to a specific group of another device. MAC Media Access Control. A collection of information about the devices on a network. multicast filtering A system .... MAC address Media Access Control address; MAC addresses are used to a network. main port The port in normal operating conditions. The Switch contains its own internal MIB. also called hardware or physical address. NIC Network Interface Card. line speed See baud. A protocol specified ...