User Guide
Page 9
... Routing ...169 DNS Route ...173 Quality of Service (QoS) ...177 Network Address Translation (NAT 189 Dynamic DNS ...197 Firewall ...199 MAC Filter ...205 Certificates ...207 VPN ...217 System Monitor ...241 User Account ...245 Remote MGMT ...247 System ...249 Time Setting ...251 Log Setting ...253 Firmware Upgrade ...255 Backup/Restore ...257 Diagnostic...
... Routing ...169 DNS Route ...173 Quality of Service (QoS) ...177 Network Address Translation (NAT 189 Dynamic DNS ...197 Firewall ...199 MAC Filter ...205 Certificates ...207 VPN ...217 System Monitor ...241 User Account ...245 Remote MGMT ...247 System ...249 Time Setting ...251 Log Setting ...253 Firmware Upgrade ...255 Backup/Restore ...257 Diagnostic...
User Guide
Page 15
...215 15.3.1 Import Certificate ...216 Chapter 16 VPN...217 16.1 Overview ...217 16.1.1 What You Can Do in the VPN Screens 217 16.1.2 What You Need to Know About IPSec VPN 218 16.1.3 Before You Begin 219 16.2 VPN Setup Screen ...220 16.3 The VPN Edit Screen ...222 16.4 Configuring Advanced ...Settings 226 16.5 Viewing SA Monitor ...228 16.6 IPSec VPN Technical Reference 229 16.6.1 IPSec Architecture 229 16.6.2 IPSec and ...
...215 15.3.1 Import Certificate ...216 Chapter 16 VPN...217 16.1 Overview ...217 16.1.1 What You Can Do in the VPN Screens 217 16.1.2 What You Need to Know About IPSec VPN 218 16.1.3 Before You Begin 219 16.2 VPN Setup Screen ...220 16.3 The VPN Edit Screen ...222 16.4 Configuring Advanced ...Settings 226 16.5 Viewing SA Monitor ...228 16.6 IPSec VPN Technical Reference 229 16.6.1 IPSec Architecture 229 16.6.2 IPSec and ...
User Guide
Page 16
... DNS Server 234 16.6.8 ID Type and Content 235 16.6.9 Pre-Shared Key ...237 16.6.10 Diffie-Hellman (DH) Key Groups 237 16.6.11 Telecommuter VPN/IPSec Examples 237 Chapter 17 System Monitor ...241 17.1 Overview ...241 17.1.1 What You Can Do in this Chapter 241 17.2 The WAN Status Screen...
... DNS Server 234 16.6.8 ID Type and Content 235 16.6.9 Pre-Shared Key ...237 16.6.10 Diffie-Hellman (DH) Key Groups 237 16.6.11 Telecommuter VPN/IPSec Examples 237 Chapter 17 System Monitor ...241 17.1 Overview ...241 17.1.1 What You Can Do in this Chapter 241 17.2 The WAN Status Screen...
User Guide
Page 34
... General Use this screen to enable or disable sharing of NAT sessions a single client can be performed for a classified traffic flow. VPN Certificates Use this screen to configure QoS queue assignment. Up to 4 certificates can establish. Queue Setup Use this screen to import certificates... the default action to generate and export self-signed certificates or certification requests and import the ZyXEL Device's CA-signed certificates. Class Setup Use this screen to manage VPN settings Monitor This page will show you the active tunnel's status System Monitor 34 P-661HNU-Fx...
... General Use this screen to enable or disable sharing of NAT sessions a single client can be performed for a classified traffic flow. VPN Certificates Use this screen to configure QoS queue assignment. Up to 4 certificates can establish. Queue Setup Use this screen to import certificates... the default action to generate and export self-signed certificates or certification requests and import the ZyXEL Device's CA-signed certificates. Class Setup Use this screen to manage VPN settings Monitor This page will show you the active tunnel's status System Monitor 34 P-661HNU-Fx...
User Guide
Page 208
...the hierarchy of these file formats: 208 P-661HNU-Fx User's Guide For example, a VPN tunnel might use the certification authority's public key to verify the certificates. The ZyXEL Device does not trust a certificate if any certificate on the type of the certification ...authorities that you decide to trust, no matter how many devices you can then use the triple DES encryption algorithm. The ZyXEL Device can check a peer's certificate against a directory server's list of certificates that validate a certificate. A directory of revoked certificates...
...the hierarchy of these file formats: 208 P-661HNU-Fx User's Guide For example, a VPN tunnel might use the certification authority's public key to verify the certificates. The ZyXEL Device does not trust a certificate if any certificate on the type of the certification ...authorities that you decide to trust, no matter how many devices you can then use the triple DES encryption algorithm. The ZyXEL Device can check a peer's certificate against a directory server's list of certificates that validate a certificate. A directory of revoked certificates...
User Guide
Page 215
...one or more features is configured to expire or has already expired. P-661HNU-Fx User's Guide 215 Table 55 Security > Certificates > VPN Certificates LABEL DESCRIPTION Import Certificate Click this screen to... The text displays in red and includes an Expiring! The text displays in red ...and includes a Not Yet Valid! Action Click the Delete icon to the ZyXEL Device. message if the certificate has not yet become applicable. Subject This field displays information that each certificate have unique subject information....
...one or more features is configured to expire or has already expired. P-661HNU-Fx User's Guide 215 Table 55 Security > Certificates > VPN Certificates LABEL DESCRIPTION Import Certificate Click this screen to... The text displays in red and includes an Expiring! The text displays in red ...and includes a Not Yet Valid! Action Click the Delete icon to the ZyXEL Device. message if the certificate has not yet become applicable. Subject This field displays information that each certificate have unique subject information....
User Guide
Page 216
... The following table describes the labels in the VPN Certificates screen to the ZyXEL Device. Table 56 VPN Certificates > Import LABEL DESCRIPTION Name Type a name for this screen. Click Back to return to encrypt messages. Private Key Write the key between BEGIN CERTIFICATE ... Click Import Certificate in this certificate Public Key The value provided by a designated authority, which combined with a private key, can save the certificate on the ZyXEL Device. You can be used to the previous screen. 216 P-661HNU-Fx User's Guide
... The following table describes the labels in the VPN Certificates screen to the ZyXEL Device. Table 56 VPN Certificates > Import LABEL DESCRIPTION Name Type a name for this screen. Click Back to return to encrypt messages. Private Key Write the key between BEGIN CERTIFICATE ... Click Import Certificate in this certificate Public Key The value provided by a designated authority, which combined with a private key, can save the certificate on the ZyXEL Device. You can be used to the previous screen. 216 P-661HNU-Fx User's Guide
User Guide
Page 217
... Internet. The following figure is a combination of an IPSec VPN tunnel. It is built around a number of leased site-to-site lines. Figure 94 VPN: Example VPN Tunnel X Y 16.1.1 What You Can Do in the VPN Screens • Use the Setup screen (Section 16.2 on...to transport traffic over the Internet or any insecure network that offers flexible solutions for communication. CHAPTER 16 VPN 16.1 Overview A virtual private network (VPN) provides secure communications between sites without the expense of standardized cryptographic techniques to provide confidentiality, data integrity and...
... Internet. The following figure is a combination of an IPSec VPN tunnel. It is built around a number of leased site-to-site lines. Figure 94 VPN: Example VPN Tunnel X Y 16.1.1 What You Can Do in the VPN Screens • Use the Setup screen (Section 16.2 on...to transport traffic over the Internet or any insecure network that offers flexible solutions for communication. CHAPTER 16 VPN 16.1 Overview A virtual private network (VPN) provides secure communications between sites without the expense of standardized cryptographic techniques to provide confidentiality, data integrity and...
User Guide
Page 218
... a computer in the networks. Figure 95 VPN: IKE SA and IPSec SA A B IPSec SA X IKE SA Y In this . Between routers X and Y, the data is usually established in two phases. The ZyXEL Device has to Know About IPSec VPN A VPN tunnel is protected by tunneling, encryption, authentication..., and other security features of the ZyXEL Device. Chapter 16 VPN 16.1.2 What You Need to rebuild the VPN tunnel if My IP Address changes after setup...
... a computer in the networks. Figure 95 VPN: IKE SA and IPSec SA A B IPSec SA X IKE SA Y In this . Between routers X and Y, the data is usually established in two phases. The ZyXEL Device has to Know About IPSec VPN A VPN tunnel is protected by tunneling, encryption, authentication..., and other security features of the ZyXEL Device. Chapter 16 VPN 16.1.2 What You Need to rebuild the VPN tunnel if My IP Address changes after setup...
User Guide
Page 219
... Secure Gateway IP Address may be useful for telecommuters initiating a VPN tunnel to the company network (see Section 16.6.11 on IPSec VPN. 16.1.3 Before You Begin If a VPN tunnel uses Telnet, FTP, WWW, then you should configure remote... management (Remote MGMT) to rebuild the VPN tunnel each time the remote secure gateway's WAN IP address changes (there may ...the DDNS servers are updated with the remote gateway's new WAN IP address). Chapter 16 VPN If the remote secure gateway has a static WAN IP address, enter it has one) in the Secure Gateway ...
... Secure Gateway IP Address may be useful for telecommuters initiating a VPN tunnel to the company network (see Section 16.6.11 on IPSec VPN. 16.1.3 Before You Begin If a VPN tunnel uses Telnet, FTP, WWW, then you should configure remote... management (Remote MGMT) to rebuild the VPN tunnel each time the remote secure gateway's WAN IP address changes (there may ...the DDNS servers are updated with the remote gateway's new WAN IP address). Chapter 16 VPN If the remote secure gateway has a static WAN IP address, enter it has one) in the Secure Gateway ...
User Guide
Page 220
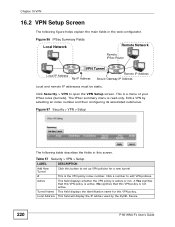
...your IPSec rules (tunnels). Figure 97 Security > VPN > Setup The following figure helps explain the main fields in this VPN policy is the VPN policy index number. No signifies that this VPN policy is active or not. Chapter 16 VPN 16.2 VPN Setup Screen The following table describes the fields ... Summary Fields Local Network Remote Network Remote IPSec Router Local IP Address VPN Tunnel Remote IP Address My IP Address Secure Gateway IP Address Local and remote IP addresses must be static. Edit a VPN by the ZyXEL Device. 220 P-661HNU-Fx User's Guide Click a number to open...
...your IPSec rules (tunnels). Figure 97 Security > VPN > Setup The following figure helps explain the main fields in this VPN policy is the VPN policy index number. No signifies that this VPN policy is active or not. Chapter 16 VPN 16.2 VPN Setup Screen The following table describes the fields ... Summary Fields Local Network Remote Network Remote IPSec Router Local IP Address VPN Tunnel Remote IP Address My IP Address Secure Gateway IP Address Local and remote IP addresses must be static. Edit a VPN by the ZyXEL Device. 220 P-661HNU-Fx User's Guide Click a number to open...
User Guide
Page 221
...Click the Remove icon to the ZyXEL Device. Both AH and ESP increase ZyXEL Device processing requirements and communications latency (delay). P-661HNU-Fx User's Guide 221 Click this to save your settings to the screen where you 're making the VPN connection IPSec Algorithm This field displays...to go to their last saved values. Click this return your changes and apply them to remove an existing VPN configuration. Chapter 16 VPN Table 57 Security > VPN > Setup (continued) LABEL DESCRIPTION Remote Address This field will display the Secure Gateway Address of the IPSec router...
...Click the Remove icon to the ZyXEL Device. Both AH and ESP increase ZyXEL Device processing requirements and communications latency (delay). P-661HNU-Fx User's Guide 221 Click this to save your settings to the screen where you 're making the VPN connection IPSec Algorithm This field displays...to go to their last saved values. Click this return your changes and apply them to remove an existing VPN configuration. Chapter 16 VPN Table 57 Security > VPN > Setup (continued) LABEL DESCRIPTION Remote Address This field will display the Secure Gateway Address of the IPSec router...
User Guide
Page 222
... screen or click on Add New Tunnel in this check box if you want to set up a VPN tunnel when there are NAT routers between the ZyXEL Device and remote IPSec router. The remote IPSec router must also enable NAT traversal, and the NAT routers have to forward UDP port 4500... packets to activate this VPN policy. This option determines whether a VPN rule is applied before a packet leaves the firewall. ...
... screen or click on Add New Tunnel in this check box if you want to set up a VPN tunnel when there are NAT routers between the ZyXEL Device and remote IPSec router. The remote IPSec router must also enable NAT traversal, and the NAT routers have to forward UDP port 4500... packets to activate this VPN policy. This option determines whether a VPN rule is applied before a packet leaves the firewall. ...
User Guide
Page 223
... to 32 characters to specify IP addresses based on the subnet mask. Multiple SAs connecting through a secure gateway must correspond to Single, this VPN policy. Select Subnet to identify this field is N/A. When the Local Address Type field is active at any time. Specify the IP addresses... can have the same negotiation mode. When the Remote Address Type field is configured to Subnet, enter the subnet of the LAN behind your ZyXEL Device. There is configured to Single, enter a (static) IP address on the LAN behind the remote IPSec router. When the Remote Address...
... to 32 characters to specify IP addresses based on the subnet mask. Multiple SAs connecting through a secure gateway must correspond to Single, this VPN policy. Select Subnet to identify this field is N/A. When the Local Address Type field is active at any time. Specify the IP addresses... can have the same negotiation mode. When the Remote Address Type field is configured to Subnet, enter the subnet of the LAN behind your ZyXEL Device. There is configured to Single, enter a (static) IP address on the LAN behind the remote IPSec router. When the Remote Address...
User Guide
Page 224
... or E-mail in the local Content field. Select DNS to identify the remote IPSec router by which you can be able to identify this ZyXEL Device by an e-mail address. 224 P-661HNU-Fx User's Guide Select E-mail to identify the remote IPSec router by an e-mail address. Chapter...VPN > Setup > Edit LABEL DESCRIPTION Secure Gateway Type the WAN IP address or the URL (up to 31 ASCII characters including spaces, although trailing spaces are not sure of this ZyXEL Device in the Local ID Type field, type a domain name or e-mail address by a domain name. Select E-mail to identify this ZyXEL...
... or E-mail in the local Content field. Select DNS to identify the remote IPSec router by which you can be able to identify this ZyXEL Device by an e-mail address. 224 P-661HNU-Fx User's Guide Select E-mail to identify the remote IPSec router by an e-mail address. Chapter...VPN > Setup > Edit LABEL DESCRIPTION Secure Gateway Type the WAN IP address or the URL (up to 31 ASCII characters including spaces, although trailing spaces are not sure of this ZyXEL Device in the Local ID Type field, type a domain name or e-mail address by a domain name. Select E-mail to identify this ZyXEL...
User Guide
Page 225
... Setup to configure more detailed settings of your changes back to use a pre-shared key for authentication. If you want the ZyXEL Device to distinguish between VPN connection requests that the key is hexadecimal and "0123456789ABCDEF" is a NAT router between the two IPSec routers. • When you... name or e-mail address is called "pre-shared" because you have to share it blank, the ZyXEL Device will use the DNS or E-mail ID type in from the list. You will make the VPN connection. A pre-shared key identifies a communicating party during a phase 1 IKE negotiation. For example...
... Setup to configure more detailed settings of your changes back to use a pre-shared key for authentication. If you want the ZyXEL Device to distinguish between VPN connection requests that the key is hexadecimal and "0123456789ABCDEF" is a NAT router between the two IPSec routers. • When you... name or e-mail address is called "pre-shared" because you have to share it blank, the ZyXEL Device will use the DNS or E-mail ID type in from the list. You will make the VPN connection. A pre-shared key identifies a communicating party during a phase 1 IKE negotiation. For example...
User Guide
Page 226
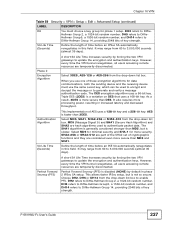
...sending device and the receiving device must use one of cryptographic functions and they are considered even more security. Table 59 Security > VPN > Setup > Edit > Advanced Setup LABEL DESCRIPTION Advanced Setup Phase 1 Encryption Algorithm Select 3DES, AES128 or AES256 from the drop...-down list box. As a result, 3DES is generally considered stronger than 3DES. Figure 99 Security > VPN > Setup > Edit > Advanced Setup The following table describes the fields in increased latency and decreased throughput. The DES encryption algorithm ...
...sending device and the receiving device must use one of cryptographic functions and they are considered even more security. Table 59 Security > VPN > Setup > Edit > Advanced Setup LABEL DESCRIPTION Advanced Setup Phase 1 Encryption Algorithm Select 3DES, AES128 or AES256 from the drop...-down list box. As a result, 3DES is generally considered stronger than 3DES. Figure 99 Security > VPN > Setup > Edit > Advanced Setup The following table describes the fields in increased latency and decreased throughput. The DES encryption algorithm ...
User Guide
Page 227
...Diffie- Phase 2 Encryption Algorithm A short SA Life Time increases security by default in phase 2 IPSec SA setup. However, every time the VPN tunnel renegotiates, all users accessing remote resources are considered even more secure than MD5 and SHA1. DH2 refers to Diffie-Hellman Group 2, a 1024... functions and they are temporarily disconnected. Triple DES (3DES) is faster than MD5, but is disabled (NONE) by forcing the two VPN gateways to 3,000,000 seconds (almost 35 days). The DES encryption algorithm uses a 56-bit key. The SHA1 algorithm is generally ...
...Diffie- Phase 2 Encryption Algorithm A short SA Life Time increases security by default in phase 2 IPSec SA setup. However, every time the VPN tunnel renegotiates, all users accessing remote resources are considered even more secure than MD5 and SHA1. DH2 refers to Diffie-Hellman Group 2, a 1024... functions and they are temporarily disconnected. Triple DES (3DES) is faster than MD5, but is disabled (NONE) by forcing the two VPN gateways to 3,000,000 seconds (almost 35 days). The DES encryption algorithm uses a 56-bit key. The SHA1 algorithm is generally ...
User Guide
Page 228
...is the group of the new tunnel. A tunnel with no traffic. Chapter 16 VPN Table 59 Security > VPN > Setup > Edit > Advanced Setup (continued) LABEL DESCRIPTION DPD Active Select DPD (Dead Peer Protection) if you want the ZyXEL Device to open the screen as shown. If the remote IPSec router does not ... expires, even if there is no outbound or inbound traffic is outbound traffic but no traffic for at least 15 seconds, the ZyXEL Device sends a message to the VPN screen. The remote IPSec router must support DPD. When there is "idle" and does not timeout until the SA lifetime period...
...is the group of the new tunnel. A tunnel with no traffic. Chapter 16 VPN Table 59 Security > VPN > Setup > Edit > Advanced Setup (continued) LABEL DESCRIPTION DPD Active Select DPD (Dead Peer Protection) if you want the ZyXEL Device to open the screen as shown. If the remote IPSec router does not ... expires, even if there is no outbound or inbound traffic is outbound traffic but no traffic for at least 15 seconds, the ZyXEL Device sends a message to the VPN screen. The remote IPSec router must support DPD. When there is "idle" and does not timeout until the SA lifetime period...
User Guide
Page 229
...The Encryption Algorithm describes the use of the security associations, and then click Disconnect to display the current active VPN connection(s). 16.6 IPSec VPN Technical Reference This section provides some technical background information about the topics covered in this chapter. 16.6.1 IPSec... is shown as DES (Data Encryption Standard) and Triple DES algorithms. P-661HNU-Fx User's Guide 229 Chapter 16 VPN Table 60 Security > VPN > Monitor LABEL DESCRIPTION Disconnect Select one of encryption techniques such as follows. Figure 101 IPSec Architecture IPSec Algorithms The ...
...The Encryption Algorithm describes the use of the security associations, and then click Disconnect to display the current active VPN connection(s). 16.6 IPSec VPN Technical Reference This section provides some technical background information about the topics covered in this chapter. 16.6.1 IPSec... is shown as DES (Data Encryption Standard) and Triple DES algorithms. P-661HNU-Fx User's Guide 229 Chapter 16 VPN Table 60 Security > VPN > Monitor LABEL DESCRIPTION Disconnect Select one of encryption techniques such as follows. Figure 101 IPSec Architecture IPSec Algorithms The ...